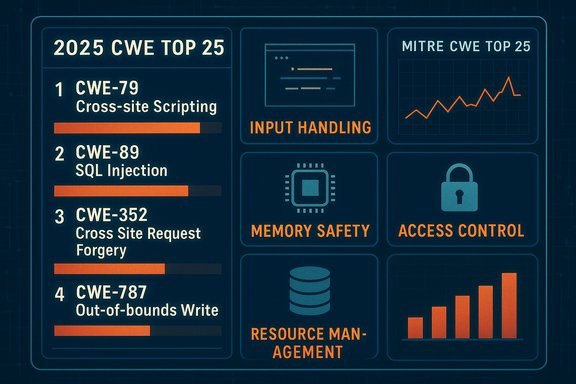
The 2025 CWE Top 25 Most Dangerous Software Weaknesses arrives as a clear, data-driven wake-up call for developers, security teams, and procurement managers: adversaries continue to exploit a concentrated set of weakness classes, and addressing those root causes is the fastest way to reduce high-impact risk across products and services. The list — compiled and published through the CWE program managed by MITRE and endorsed in collaboration with DHS/CISA — ranks the weakness families attackers most often weaponize and maps trends across the vulnerability landscape for the year. The 2025 table highlights familiar offenders (cross-site scripting, SQL injection, command and memory-safety errors) while showing a continued rise in access-control and resource-management failures that make large-scale compromise and data theft easier.
Conclusion: The 2025 Top 25 is both a mirror and a map — it reflects what attackers continue to exploit and directs defenders toward the most effective, long-term reductions in software risk. Implement it thoughtfully, verify mappings and vendor claims, and embed the resulting practices into your development lifecycle to see the largest security ROI.
Source: CISA 2025 CWE Top 25 Most Dangerous Software Weaknesses | CISA
 Background / Overview
Background / Overview
What is the CWE Top 25 and why it matters
The CWE Top 25 is a community-driven, empirical ranking of software weakness classes (not individual CVEs) that are most frequently the root causes of severe vulnerabilities. The ranking is produced by analyzing public vulnerability data, weighting both severity and prevalence, and incorporating signals such as known exploited vulnerabilities. The result is a prioritized, practical list organizations can adopt to shape secure development, testing, and procurement efforts. The 2025 edition was assembled from a dataset of 39,080 CVE records and is presented as a tool for vulnerability reduction across the entire software lifecycle.High-level findings in 2025
- Top-of-list continuance: Cross-site scripting (CWE‑79) remains the #1 weakness, demonstrating that web content generation and output encoding problems continue to be a primary attack vector.
- Access control climbs: Weaknesses related to missing authorization and improper access control rose substantially in ranking, reflecting an increased operational focus on identity/context failures.
- Memory safety still critical: Several memory-safety CWEs (out-of-bounds write/read, use-after-free, classic buffer overflows) remain highly ranked, underscoring persistent risk in native-code ecosystems.
- New and reemerging entries: 2025’s list includes both long-standing categories (SQL injection, buffer overflows) and items that have bounced back in prevalence or moved up due to exploit activity. Coverage across independent security outlets confirms the same trends reported by MITRE.
The 2025 Top 25 at a glance
The definitive list published by the CWE program shows the ranking and relative scores for each weakness family. The most important top entries for operational prioritization are:- CWE‑79 — Improper Neutralization of Input During Web Page Generation (Cross-site Scripting) — Rank 1.
- CWE‑89 — SQL Injection — Rank 2.
- CWE‑352 — Cross‑Site Request Forgery — Rank 3.
- CWE‑862 — Missing Authorization — Rank 4.
- CWE‑787 — Out‑of‑bounds Write — Rank 5.
What changed in 2025 — trends and interpretation
Access control and authorization moved up
The most notable shift in 2025 is the rise of access-control-related weaknesses (Missing Authorization, Incorrect Authorization, Improper Access Control). These are not exotic bugs; they are often design or logic flaws where the system fails to check whether a caller is allowed to perform an operation. That kind of mistake yields high-impact outcomes because it bypasses the very mechanisms intended to limit damage across an environment. MITRE’s ranking shows Missing Authorization jumping several places — a signal that organizations must treat authorization as a first-class engineering requirement.Memory safety remains a dominant attack surface
Native-memory weaknesses (out-of-bounds write/read, use-after-free, and classic buffer overflows) still command substantial presence and severity on the list. These weaknesses enable remote code execution in many contexts and therefore remain the single biggest avenue to full system compromise for software written in languages like C and C++. The list’s persistence of memory-related CWEs underscores the urgency of combining safer language choices, compiler/hardening options, sanitizers, and fuzzing in development pipelines.Input-handling and injection persist
Injection classes — XSS, SQLi, command/code injection, file-upload abuse — continue to dominate because they are straightforward to introduce and, in many systems, straightforward for attackers to trigger. The 2025 Top 25 again emphasizes that working with untrusted input remains the most common root cause behind critical vulnerabilities. Independent press coverage and industry analysis echo this, noting that input-processing errors account for a meaningful portion of high-severity flaws.Resource management and availability concerns
Allocation-of-resources-without-limits (CWE‑770) appears on the 2025 list, reflecting real-world exploitation and denial-of-service styles that take advantage of unbounded resources. This is a reminder that security is not only about confidentiality and integrity — availability is an equal first-class concern that must be tested and bounded.Practical implications by stakeholder
For developers and product teams
- Prioritize defense-in-depth for input handling. Treat input validation, canonicalization, and output encoding as mandatory. Implement whitelists where feasible; for web output, use robust templating libraries and CSP (Content Security Policy) to constrain script execution.
- Adopt memory-safety practices. Where possible, prefer memory-managed languages, or isolate native modules; integrate AddressSanitizer/MemorySanitizer, ASLR, and modern compiler hardening. Fuzz untrusted parsing code aggressively.
- Make authorization explicit, testable, and centralized. Use policy frameworks that separate authentication from authorization, and add automated tests that assert correct permission checks across API endpoints. Authorization regression testing must be part of CI.
- Treat file handling as code execution risk. Enforce file-type checks, store uploads outside the web root, and sanitize metadata. Use virus/behavioral scanning for uploaded content in internet-facing flows.
- Instrument secure-by-design in the SDLC. Shift left: integrate SAST, dependency-supply-chain scanning, and threat-model-informed test cases into the pipeline. The Top 25 is designed to be an input into Secure by Design decisions.
For application security and operations teams
- Map findings to the Top 25 categories. When triaging vulnerability scan output, use the CWE Top 25 as a filter to prioritize fixes that cut the most risk per remediation dollar. The Top 25 identifies classes that, once fixed at the source, prevent many downstream CVEs.
- Integrate layered testing. Combine SAST (detect injection patterns), DAST/IAST (runtime logic and auth checks), and fuzzing (file parsers, protocol handlers) to surface weaknesses mapped to CWEs. Ensure test harnesses exercise authorization boundaries with negative tests.
- Monitor and respond to KEV signals. CVEs mapped to the KEV (Known Exploited Vulnerabilities) catalog indicate active exploitation; prioritize these fixes and hunt proactively for indicators tied to the CWE families most associated with KEV entries.
For procurement and risk managers
- Use the Top 25 as procurement guardrails. Require vendor attestations, SBOMs, and documentation showing how candidate products address the Top 25 weaknesses (e.g., memory-safe components, authorization architecture, input sanitization). Insist on secure-by-default configurations.
- Ask for test evidence. Vendors should demonstrate SAST/DAST/fuzzing coverage mapped to CWE categories relevant to their product. If they cannot produce evidence, plan compensating controls or higher risk ratings. Independent coverage and guidance from security industry press recommend similar procurement pressure tactics.
Concrete mitigation patterns mapped to the Top 25 (engineer-friendly)
- Cross-site scripting (CWE‑79): use contextual output encoding, templating that auto-escapes, strict Content Security Policy, and input canonicalization.
- SQL Injection (CWE‑89): parameterized queries, stored procedures with properly bound inputs, ORMs that use safe query builders, and DB-layer least-privilege accounts.
- Missing/incorrect authorization (CWE‑862/CWE‑863/CWE‑284): centralize authorization checks, implement role-based or attribute-based access control, and include unit/integration tests asserting failure modes for unauthorized operations.
- Out-of-bounds and use-after-free (CWE‑787/CWE‑125/CWE‑416): prefer memory-safe languages, apply compiler sanitizers (ASan/UBSan), enable static analyzers focused on native memory, and employ fuzzing on parsing code.
- Unrestricted upload (CWE‑434): restrict file types, store outside web roots, scan and sandbox uploads, use dedicated processing services with least privilege.
- Code/command injection (CWE‑94/CWE‑78/CWE‑77): avoid dynamic code generation; if required, strictly validate inputs with allowlists and use isolated execution environments (sandboxes, process boundaries).
- Resource exhaustion (CWE‑770): implement rate-limiting, quotas, and bounded buffers; fail gracefully and include admission/control policies.
Prioritization framework — where you should start (step-by-step)
- Map: Inventory your attack surface and map each component to CWEs from the Top 25 where applicable (web stacks → XSS/CSRF/SQLi; native parsers → memory-safety).
- Measure: Use SAST/DAST/fuzzing outputs to quantify occurrences of Top‑25-related weaknesses and estimate remediation effort.
- Triage: Prioritize fixes that (a) map to Top‑25 families with high score/KEV counts, or (b) enable privilege escalation or chain into broad impact.
- Fix at source: Where feasible, eliminate the weakness in design or code (e.g., replace unsafe parser with a memory-safe library).
- Compensate: When immediate code fixes aren’t possible, apply environment-level compensations — API gateways, WAF rules, network segmentation, stricter auth policies.
- Validate: Add automated tests that cover the regressed weaknesses, and include them in CI gating.
- Repeat: Treat the Top 25 as a continual prioritization signal and integrate it into your release and procurement checklists.
Costs, ROI, and the business case
Addressing the Top 25 early in the SDLC is materially cheaper than emergency remediation and incident response. Investing in secure design, static analysis, and test automation reduces the number of high-impact vulnerabilities that reach production and hence lowers reactive spending (patching, incident handling, regulatory fines, reputational damage). The CWE program explicitly emphasizes that eliminating weakness classes early reduces overall CVE volume and long-term cost exposure. Industry reporting and analysis mirror this recommendation: fix root causes rather than chase every vulnerability symptom.Limitations, caveats, and verification notes
- The Top 25 is a prioritized weakness class list; it is not a replacement for vulnerability scanning or per-product risk assessment. Use it to guide investments, not as a sole triage mechanism.
- The CWE Top 25 is based on public CVE data and mapping heuristics that can be imperfect; teams must still validate individual CVE mapping and exploitability before taking irreversible action. In practice, verification against CVE registries and vendor advisories is recommended as part of the remediation workflow.
- Attempted retrieval of the U.S. government (CISA) advisory page linked externally may be blocked by remote servers in some automated crawls; however the CWE program page and multiple independent news outlets summarize the same Top 25 and provide the detailed ranking and scoring that organizations require. Readers should consult both the official CWE Top 25 page and any CISA guidance available to them for the authoritative phrasing and recommended mitigations. If official agency pages are inaccessible in a particular environment, rely on the published MITRE CWE Top 25 table as the canonical technical source.
Critical analysis — strengths and risks of the 2025 list
Notable strengths
- Actionable prioritization: By ranking weakness classes rather than individual CVEs, the list helps teams make long-term architectural decisions that reduce multiple future CVEs. This strategic emphasis is particularly valuable to product teams deciding on language and library choices.
- Data-driven: The ranking is grounded in tens of thousands of CVE records and includes signals about in-the-wild exploitation, improving its operational relevance.
- Cross-stakeholder utility: The Top 25 provides tangible guidance for developers, security teams, procurement, and policy makers — enabling consistent security requirements backed by empirical data.
Potential risks and blind spots
- Over-focus on categories, not product context: Organizations that apply the Top 25 as a checklist and ignore product-specific context risk mis-prioritizing fixes. For example, a cloud service with strong sandboxing might prioritize authorization defects over certain memory-safety issues because of contextual mitigations.
- Mapping errors and scoping: CWE mappings from CVE records are sometimes noisy; the Top 25’s utility depends on teams validating the mapping and not assuming each CVE-to-CWE assignment is flawless. This technical nuance requires analysts to confirm mappings before acting.
- Not a substitute for threat modeling: The Top 25 signals where to invest broadly, but targeted threat modeling remains necessary to understand attack paths unique to a product or environment.
Checklist: Quick wins in the next 90 days
- Inventory public-facing endpoints and map them to Top‑25 categories.
- Add high-value unit/integration tests for authorization and input validation.
- Deploy or tune SAST rules to flag the Top‑25 CWE patterns and prioritize those findings in your backlog.
- Run focused fuzzing on file parsers and protocol handlers.
- Harden production controls (rate limits, CSP, WAF rules, API gateways) as immediate compensating measures.
- Require vendor attestation that third-party components address Top‑25 weaknesses where applicable.
Final assessment and takeaway
The 2025 CWE Top 25 Most Dangerous Software Weaknesses is a timely, pragmatic roadmap: it reminds the industry that many high-impact attacks exploit the same underlying mistakes. Tackling those root causes — input handling, memory safety, authorization correctness, and bounded resource management — yields outsized security benefits. Organizations that integrate the Top 25 into Secure by Design development practices, application security testing, and procurement rules will reduce long-term exposure and improve resilience. The ranking is not a magic bullet, but when combined with context-aware threat modeling, layered testing, and governance, it becomes a powerful tool to decrease both the frequency and severity of exploitable vulnerabilities. For implementation, prioritize quick, high-impact fixes (auth checks, injection elimination, output encoding) while investing in systemic changes (memory-safe components, CI-integrated testing, fuzzing) to prevent whole classes of future weaknesses. And when remediating, always validate CVE mappings and vendor advisories to ensure fixes address the correct root cause before deploying changes to production.Conclusion: The 2025 Top 25 is both a mirror and a map — it reflects what attackers continue to exploit and directs defenders toward the most effective, long-term reductions in software risk. Implement it thoughtfully, verify mappings and vendor claims, and embed the resulting practices into your development lifecycle to see the largest security ROI.
Source: CISA 2025 CWE Top 25 Most Dangerous Software Weaknesses | CISA