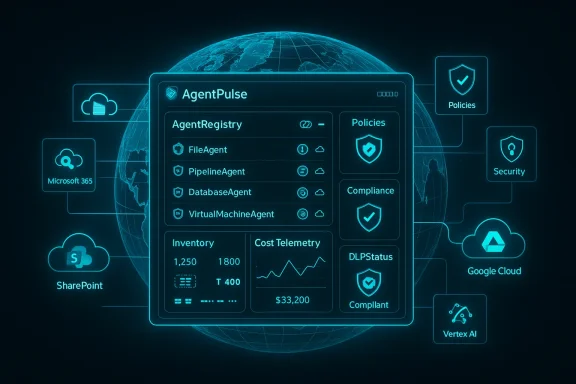
AvePoint has moved AgentPulse Command Center out of preview and into general availability, offering enterprises a single-pane view and lifecycle controls for AI agents across Microsoft 365 and Google Cloud — a direct response to the rising operational, security, and cost risks posed by unmanaged “agentic” AI in the workplace.
The enterprise shift from experimentation to production for AI agents — small, task-focused autonomous systems that act on behalf of users — has accelerated. As organizations stitch agents into workflows, they inherit a new class of operational risks: runaway pay-per-use bills, uncontrolled access to sensitive content, scattered agent inventories across multiple clouds, and compliance blind spots. AvePoint’s AgentPulse Command Center is designed to be a centralized control plane for those challenges, integrating agent discovery, observability, lifecycle management, and data protection into the AvePoint Confidence Platform.
AgentPulse’s general availability release explicitly extends observability to both Microsoft 365 ecosystems (including Copilot Studio, Microsoft Foundry, SharePoint-based agents) and Google Cloud (including Vertex AI and Google Drive). The product positions itself as a multicloud agent registry and governance layer that claims to stop “shadow AI” before it becomes a financial, security, or compliance problem.
Enterprises have three urgent needs that AgentPulse is pitching itself to solve:
However, organizations should view AgentPulse as a necessary but not sufficient part of an agent governance strategy. The platform appears strongest at discovery, inventory, and centralized visibility; buyers must validate enforcement depth (especially runtime DLP), integration specifics with native agent toolchains, and how easily telemetry can feed into broader security operations. AgentPulse can significantly reduce the friction of governance, but operational discipline, IAM rigor, and developer processes remain the critical determinants of whether agentic AI delivers value without becoming a liability.
For enterprises already wrestling with shadow AI, spiky cloud bills, and the messy reality of cross‑tenant data sprawl, AgentPulse is worth a proof-of-concept as part of a broader governance program. For others, the product is a valuable signal that the market is maturing: multicloud, agent-aware governance tools are moving from concept to production, and the next 12–24 months will likely decide which organizations can realize scalable, safe, and cost-effective agentic AI at enterprise scale.
Conclusion
As agentic AI shifts from experimentation to everyday workflows, the need for centralized, multicloud governance is non-negotiable. AvePoint’s AgentPulse Command Center addresses many of the immediate visibility and control problems enterprises face, notably by combining agent inventory, cost telemetry, and data protection into a single interface. The product’s general availability and Google Cloud expansion are timely responses to a landscape where agents and data move freely across platforms. Still, technical teams should treat AgentPulse as a platform piece within a broader program of process change, identity hygiene, runtime enforcement, and cost governance — not as a silver bullet. Agents will continue to reshape how work gets done; the real winners will be organizations that pair powerful agent capabilities with disciplined, multicloud governance.
Source: The AI Journal AvePoint Announces General Availability of AgentPulse Command Center, with Multicloud Agentic AI Governance | The AI Journal
 Background / Overview
Background / Overview
The enterprise shift from experimentation to production for AI agents — small, task-focused autonomous systems that act on behalf of users — has accelerated. As organizations stitch agents into workflows, they inherit a new class of operational risks: runaway pay-per-use bills, uncontrolled access to sensitive content, scattered agent inventories across multiple clouds, and compliance blind spots. AvePoint’s AgentPulse Command Center is designed to be a centralized control plane for those challenges, integrating agent discovery, observability, lifecycle management, and data protection into the AvePoint Confidence Platform.AgentPulse’s general availability release explicitly extends observability to both Microsoft 365 ecosystems (including Copilot Studio, Microsoft Foundry, SharePoint-based agents) and Google Cloud (including Vertex AI and Google Drive). The product positions itself as a multicloud agent registry and governance layer that claims to stop “shadow AI” before it becomes a financial, security, or compliance problem.
What AgentPulse Command Center claims to deliver
Unified, multicloud agent observability
- Agent inventory and discovery across tenant boundaries and cloud platforms, giving IT teams a consolidated view of who created agents, where they run, and what resources they access.
- Usage and cost telemetry to surface pay-per-use trends and prevent surprise billing from unmanaged agent activity.
- Creation and inventory trends so teams can spot spikes in agent deployment or unusual agent proliferation.
Deep data interaction visibility
- Agent-to-data mapping that shows which agents access particular files, drives, or data stores.
- Google Drive security posture management, including identification of sensitive files, sharing-analysis, and external access audits.
- Data hygiene analysis that flags inactive, redundant, obsolete, or trivial data (commonly called IROTD) to improve the quality of inputs feeding agent decision-making.
Lifecycle controls and protection
- Agent lifecycle management, from registry and approval to retirement and removal, to reduce unmanaged (shadow) deployments.
- Granular Data Loss Prevention (DLP) tied to agent behavior so that agents can be prevented from exfiltrating or oversharing sensitive information.
- Policy enforcement and remediation workflows that let administrators remediate oversharing or misconfiguration from the same platform.
Platform integrations advertised
- Microsoft: Copilot Studio, Microsoft Foundry, SharePoint agents, and broader Microsoft 365.
- Google: Vertex AI, Google Drive, and broader Google Cloud resources.
Why this matters now: the enterprise context
AI agents are no longer fringe experiments. Market analysis and analyst warnings show two concurrent trends: rapid adoption and high operational risk if governance is missing. Independent analyst findings cited broadly across the industry warned that a large share of agentic AI projects will fail or be canceled if enterprises cannot demonstrate value and manage risk. That backdrop creates both urgency and an opportunity for tooling that can scale governance.Enterprises have three urgent needs that AgentPulse is pitching itself to solve:
- Prevent runaway costs from pay-per-use agent invocations and model calls.
- Stop data leakage and remediate accidental oversharing that can occur when agents access shared drives or external connectors.
- Maintain consistent policy enforcement across SaaS tenants and cloud providers as agents are created by diverse teams with different privileges.
What’s new with Google Cloud support — and why it’s important
AgentPulse’s GA release specifically calls out expanded observability into Google Cloud, with several concrete angles:- Drive security posture monitoring: identifying files that contain sensitive data, mapping sharing permissions, and auditing external access. This targets the frequent weak point where collaborative files are used as training inputs for models or as lookups by agents.
- Data quality controls: spotting stale, duplicate, or low-value content that can degrade AI outputs — the “garbage in, garbage out” problem made more consequential with autonomous decision-making.
- Infrastructure protection: monitoring the cloud resources (compute, storage) that underlie agent workloads so teams can detect misconfigurations or unusual consumption patterns.
Notable strengths and what AvePoint has gotten right
- Single-pane multicloud visibility — The key operational win here is consolidation. Organizations often rely on multiple point products or manual inventories; a central registry for agents simplifies auditability and incident response.
- Practical focus on cost and DLP — By combining cost telemetry with DLP tied to agents, the platform hits two CIO pain points at once: finance and security.
- Integration with SaaS-native agent tooling — Support for Copilot Studio, Microsoft Foundry, SharePoint agents, Vertex AI, and Google Drive is meaningful because those are primary places agents are built and consume data.
- Lifecycle governance — Registry plus lifecycle controls (approval, retirement) are essential to prevent agent sprawl, and the product’s emphasis here aligns with enterprise governance maturity models.
- Addressing data quality — Calling out IROTD (inactive, redundant, obsolete, trivial data) as a first-class problem for agent outputs is a practical addition that many governance tools ignore.
Important limitations and potential blind spots
While the product’s scope is compelling, several practical and strategic caveats matter for buyers and practitioners.- Surface-level observability vs. deep policy enforcement: Visibility is the first step; enforcement across third-party models, external APIs, and bespoke in-house agents will require additional controls. Detecting access is easier than preventing exfiltration through complex agent workflows that may call multiple downstream services.
- Vendor integration depth varies: “Support” for ecosystems like Copilot Studio, Vertex AI, or SharePoint can mean different things — from API-level read-only discovery to full lifecycle control. Buyers should validate the exact APIs and permissions the product requires for the features they expect.
- Cross-tenant governance complexities: Enterprises with federated tenants, multiple clouds, or subsidiaries with different cloud identities will still face identity and access management (IAM) challenges that a singular console cannot magically resolve.
- Regulatory and data residency constraints: Centralized visibility does not remove the need to respect data residency, privacy laws, and contractual restrictions on where data can be processed. Organizations must map AgentPulse’s telemetry flows to their compliance posture.
- False sense of security: Tools can improve posture, but they are not a replacement for policy, process, and careful development lifecycle practices. Overreliance on tooling without cultural and organizational change will lead to gaps.
- Agent definition ambiguity: Enterprises use many automations that qualify as “agents” in different ways — bots, apps, scheduled jobs, scripts. Classification rules and inventory accuracy will be crucial; mislabeled assets can undermine governance metrics.
Critical security and compliance considerations
- Data access mapping must be precise: Knowing that Agent A touched Drive folder X is useful, but security teams also need to know what content was accessed and whether model calls transmitted entire documents or tokenized snippets. Audit logs should capture context-rich events.
- DLP tied to agents needs runtime enforcement: Static tagging of sensitive data is not enough. Agents that dynamically generate prompts or that are invoked by users in chat contexts require runtime inspection or blocking to prevent accidental leaks.
- Secrets and credentials management: Agents often require API keys or service accounts. Ensuring those credentials are short-lived, monitored, and not embedded in agent code is foundational.
- Supply chain exposure: Agents that call third-party APIs or incorporate external skills pose supply chain risk. The governance layer must track external dependencies and flag agents that use unapproved connectors.
- Cost governance requires model-level telemetry: To truly control spend, tools need breakdowns by model, prompt volume, and latency. Aggregated usage figures will limit the ability to optimize architecturally.
How to evaluate AgentPulse for your environment: a practical checklist
- Define the scope
- Which clouds, tenants, and collaboration platforms must be monitored?
- Which teams are responsible for agent creation and approval?
- Confirm integration depth
- Does AgentPulse support the specific APIs and features you need for Copilot Studio, Vertex AI, and your SharePoint deployment?
- Which permissions are required and are they acceptable under your security policy?
- Validate observability and telemetry
- Can the product show per-agent model calls, data sources accessed, and associated costs?
- Are audit logs exportable to your SIEM or SOAR tools?
- Test lifecycle controls
- Can you approve, quarantine, retire, or delete agents centrally?
- Are remediation actions auditable and reversible where necessary?
- Assess DLP and enforcement
- What DLP rules can be applied to agents? Can they be enforced at runtime?
- How does AgentPulse surface oversharing incidents and what remediation steps are automated?
- Measure operational impact
- What is the onboarding time for a typical tenant?
- How much additional operational overhead will your security and IT teams need to manage AgentPulse itself?
- Plan for cost control
- Does the solution provide model-level cost breakdowns and alerting thresholds?
- Can chargeback or showback be automated for business units?
- Map to compliance controls
- How does the product help with GDPR, CCPA, HIPAA, PCI, or industry-specific standards in terms of logging, retention, and breach detection?
Implementation roadmap: five practical steps for rolling out agent governance
- Inventory and discovery (Weeks 0–2)
- Run an initial discovery pass to find active agents, service accounts, and connectors across Microsoft 365 and Google Cloud.
- Tag and classify assets by risk level.
- Policy definition (Weeks 2–4)
- Establish a baseline agent policy covering approval workflows, allowed data access scopes, acceptable model providers, and cost limits.
- Define DLP rules specific to agent behavior.
- Enforcement pilot (Weeks 4–8)
- Pilot AgentPulse in a single business unit with controlled agent creation and a by-exception remediation workflow.
- Validate telemetry feeds into your SIEM and cost monitoring tools.
- Scale and train (Months 2–4)
- Expand platform enrollment across tenants and cloud projects.
- Train developer and business teams on approved patterns for building agents and the governance process to follow.
- Continuous improvement (Ongoing)
- Iterate policies based on observed agent usage, false positives/negatives in DLP, and cost anomalies.
- Conduct periodic tabletop exercises to test breach scenarios involving agents.
Recommendations and practical best practices
- Treat agents like code and services: apply CI/CD, code review, secrets scanning, and runtime monitoring.
- Use least privilege for agent identities: adopt short-lived service tokens and scoped service accounts rather than broad privileges.
- Enforce model budgeting: create per-agent or per-project cost limits and alert thresholds tied to financial owner approvals.
- Automate remediation workflows: when an agent violates DLP or exceeds cost thresholds, automate suspension and notification to avoid manual firefighting.
- Integrate governance with developer workflows: gate agent creation through an approval pipeline that requires security signoff and a recorded business justification.
- Document allowable external connectors: maintain an approved connectors list and block unapproved third-party calls at runtime where possible.
- Measure data quality for AI: add a data hygiene review step before allowing agents to use large corpora as training or reference data.
Strategic implications for IT and security leaders
- Operationalizing agentic AI requires cross-functional governance: Security, finance, legal, IT, and business stakeholders must share responsibility for agent policies and remediation playbooks.
- Tooling reduces friction but does not eliminate the need for governance culture: centralized consoles help, but they must be paired with accountability, SLAs, and developer education.
- Multicloud support is necessary, not optional: enterprises that silo governance in a single platform will face blind spots; a multicloud control plane is increasingly table stakes.
- Vendors that combine DLP, cost telemetry, and lifecycle controls will be advantaged: buyers should prefer solutions that reduce the number of disconnected control planes they need to manage.
Where to be cautious: vendor claims to verify during evaluation
- Any claim about the percentage of agentic AI projects that result in data breaches or the exact reduction in costs achieved by customers should be considered vendor-reported until independently validated.
- Confirm which specific events and payloads are captured in audit logs. Some platforms provide only metadata (agent ID, timestamp) while others capture content-level indicators.
- Verify how the product handles encrypted or proprietary data, and whether on-premises data sources require additional connectors or proxies.
- Ensure the product’s remediation actions (suspend, delete, quarantine) align with your legal and operational requirements; automatic deletion may be unacceptable in regulated environments.
Final analysis: who benefits, and where the gaps remain
AvePoint’s AgentPulse Command Center addresses a core and growing pain point for enterprises: the need to discover, monitor, and govern AI agents at scale across cloud providers. Its multicloud focus and integration with Microsoft and Google ecosystems are aligned with how modern enterprises actually deploy agents. The combined emphasis on cost visibility and DLP is pragmatic and likely to appeal to CIOs and security leaders prioritizing fiscal accountability and data protection.However, organizations should view AgentPulse as a necessary but not sufficient part of an agent governance strategy. The platform appears strongest at discovery, inventory, and centralized visibility; buyers must validate enforcement depth (especially runtime DLP), integration specifics with native agent toolchains, and how easily telemetry can feed into broader security operations. AgentPulse can significantly reduce the friction of governance, but operational discipline, IAM rigor, and developer processes remain the critical determinants of whether agentic AI delivers value without becoming a liability.
For enterprises already wrestling with shadow AI, spiky cloud bills, and the messy reality of cross‑tenant data sprawl, AgentPulse is worth a proof-of-concept as part of a broader governance program. For others, the product is a valuable signal that the market is maturing: multicloud, agent-aware governance tools are moving from concept to production, and the next 12–24 months will likely decide which organizations can realize scalable, safe, and cost-effective agentic AI at enterprise scale.
Conclusion
As agentic AI shifts from experimentation to everyday workflows, the need for centralized, multicloud governance is non-negotiable. AvePoint’s AgentPulse Command Center addresses many of the immediate visibility and control problems enterprises face, notably by combining agent inventory, cost telemetry, and data protection into a single interface. The product’s general availability and Google Cloud expansion are timely responses to a landscape where agents and data move freely across platforms. Still, technical teams should treat AgentPulse as a platform piece within a broader program of process change, identity hygiene, runtime enforcement, and cost governance — not as a silver bullet. Agents will continue to reshape how work gets done; the real winners will be organizations that pair powerful agent capabilities with disciplined, multicloud governance.
Source: The AI Journal AvePoint Announces General Availability of AgentPulse Command Center, with Multicloud Agentic AI Governance | The AI Journal