Microsoft’s public advisory for CVE-2025-37943 confirms that the Azure Linux distribution has been identified as a carrier of the vulnerable upstream code, but that attestation does not mean Azure Linux is the only Microsoft product that could include the affected ath12k driver; it is the only product Microsoft has publicly attested so far. In other words, treat Azure Linux images as confirmed in‑scope and act on Microsoft’s guidance immediately — but do not assume other Microsoft‑published Linux artifacts are safe until you verify them artifact‑by‑artifact.
CVE-2025-37943 is a memory‑corruption vulnerability in the Linux kernel’s ath12k wireless driver. The flaw is rooted in how the driver decapsulates certain receive (RX) packets when the decapsulation type is DP_RX_DECAP_TYPE_NATIVE_WIFI: hardware can present a packet whose length exceeds the maximum native Wi‑Fi header length, and the driver previously lacked a proper sanity check before accessing header fields. That shortfall can lead to invalid data access and potentially memory corruption in kernel context.
The ath12k driver implements support for Qualcomm Atheros Wi‑Fi 7 and related chipsets (for example, QCN9274 and WCN7850 family devices). Upstream maintainers fixed the issue by adding a sanity check on the socket buffer (skb) length before the code attempts to read or modify header fields. Kernel vendors and major distributions pushed patches or kernel updates shortly after the CVE was disclosed; multiple vendor advisories classify the issue as Important / High due to the possibility of confidentiality/integrity/availability impact when exploited.
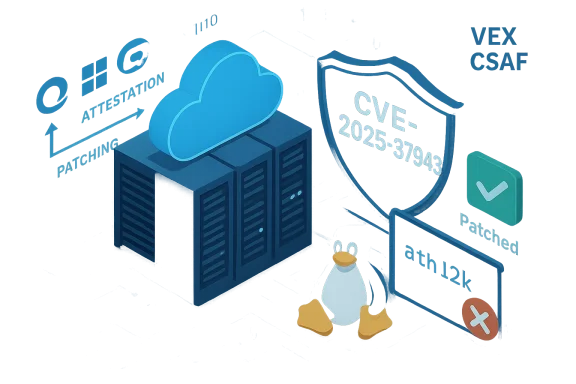
Why this matters to Microsoft customers: Microsoft publishes VEX/CSAF attestations for Azure Linux and has used that mechanism to declare which of its published artifacts include given upstream components. For defenders and admins, that attestation is a trusted, machine‑readable signal — but it is product-scoped and therefore not a global proof that no other Microsoft artifact contains the same code.
Simple checks (run on the target system):
Conclusion
CVE‑2025‑37943 was fixed upstream by adding a safety check in the ath12k RX processing path. Microsoft’s published attestation confirms Azure Linux includes the vulnerable upstream code and is therefore potentially affected; that attestation should be treated as authoritative for Azure Linux. However, it does not guarantee that other Microsoft products are unaffected — those other products must be verified artifact‑by‑artifact. Administrators should prioritize patching Azure Linux, inventory Microsoft‑distributed images they run, apply kernel updates from their distro vendors, and use temporary mitigations where patching is delayed. Follow Microsoft’s VEX/CSAF attestations for updates, but retain active, artifact‑level verification across your environment to ensure full coverage against this and future kernel driver vulnerabilities.
Source: MSRC Security Update Guide - Microsoft Security Response Center
 Background / Overview
Background / Overview
CVE-2025-37943 is a memory‑corruption vulnerability in the Linux kernel’s ath12k wireless driver. The flaw is rooted in how the driver decapsulates certain receive (RX) packets when the decapsulation type is DP_RX_DECAP_TYPE_NATIVE_WIFI: hardware can present a packet whose length exceeds the maximum native Wi‑Fi header length, and the driver previously lacked a proper sanity check before accessing header fields. That shortfall can lead to invalid data access and potentially memory corruption in kernel context.The ath12k driver implements support for Qualcomm Atheros Wi‑Fi 7 and related chipsets (for example, QCN9274 and WCN7850 family devices). Upstream maintainers fixed the issue by adding a sanity check on the socket buffer (skb) length before the code attempts to read or modify header fields. Kernel vendors and major distributions pushed patches or kernel updates shortly after the CVE was disclosed; multiple vendor advisories classify the issue as Important / High due to the possibility of confidentiality/integrity/availability impact when exploited.
Why this matters to Microsoft customers: Microsoft publishes VEX/CSAF attestations for Azure Linux and has used that mechanism to declare which of its published artifacts include given upstream components. For defenders and admins, that attestation is a trusted, machine‑readable signal — but it is product-scoped and therefore not a global proof that no other Microsoft artifact contains the same code.
What Microsoft actually said (and what that wording means)
- Microsoft’s advisory language states that Azure Linux is included in the set of Microsoft products that ship the implicated open‑source component and therefore is potentially affected.
- That wording is intentionally scoped: Microsoft has begun publishing machine‑readable CSAF/VEX attestations, starting with Azure Linux. The company has committed to updating those attestations if additional Microsoft products are later identified as carriers.
- The practical takeaway: Azure Linux = confirmed attested product; other Microsoft artifacts = unattested for now, not proven unaffected.
Why Azure Linux’s attestation does not imply exclusivity
There are several technical and operational reasons that make product‑level attestations limited by design:- Kernel artifacts are built per image and per product. Two kernels can come from the same upstream branch but differ in:
- the exact upstream commit or commit range used,
- the set of vendor backports applied,
- the kernel configuration flags (CONFIG_*) that decide which drivers are built or built as modules,
- distribution packaging choices (which files and modules are included).
- Microsoft publishes multiple kernel artifacts and Linux images: Azure Linux (the attested distribution), WSL2 kernel images, curated Marketplace images, Azure Marketplace partner images, and specialized kernels used for specific Azure services or device/edge products. Each of these is an independent build artifact and must be inspected individually.
- Presence of the driver source in a product’s sources or the presence of the compiled module in an image is the operational definition of whether that artifact is affected. Microsoft’s VEX output shows the artifacts the company has inspected; it does not automatically enumerate all Microsoft artifacts at once.
- Some Microsoft Linux artifacts may intentionally omit wireless drivers (for example, minimal server kernels), while others (desktop images, full distributions, or WSL kernel builds that include module support) can include wireless drivers by default.
Which Microsoft artifacts could plausibly include the ath12k driver?
Think of the presence of ath12k as an artifact‑by‑artifact property. The following Microsoft-distributed artifacts are plausible carriers if they were built with kernels that include ath12k:- Azure Linux (attested) — confirmed in Microsoft’s mapping.
- The WSL2 kernel Microsoft distributes for Windows hosts. Microsoft publishes the WSL2 kernel source and releases; whether a given WSL kernel build includes ath12k depends on the kernel configuration and the set of loadable modules the WSL team built into the image.
- Azure Marketplace VM images and partner images that ship a full distribution kernel (depending on how the image was built).
- Specialized Azure kernels (linux‑azure, linux‑azure‑tuned) or kernel variants used for specific VM SKUs, where wireless driver support was enabled.
- AKS node images, IoT/edge images, and other Microsoft‑curated images that ship kernels with wireless drivers enabled.
- Any Microsoft appliance or product that embeds a Linux kernel (edge or IoT offerings).
How to verify whether a Microsoft artifact in your environment is affected
Here are practical, concrete steps you can run to determine whether a given Linux image or kernel includes the ath12k driver or the vulnerable code path.Simple checks (run on the target system):
- Check whether the ath12k module exists or is loaded:
- lsmod | grep ath12k
- modinfo ath12k
- find /lib/modules/$(uname -r) -type f -name 'ath12k*'
- Check for the driver files on disk:
- ls /lib/modules/$(uname -r)/kernel/drivers/net/wireless/ath/ath12k
- grep -R "ath12k" /lib/modules/$(uname -r) 2>/dev/null
- Inspect the kernel configuration used to build the running kernel (if available):
- zcat /proc/config.gz | grep ATH12K
- zcat /proc/config.gz | grep CONFIG_ATH12K
If /proc/config.gz is not present, check /boot/config-$(uname -r) or your distro’s packaged kernel config. - Identify hardware that could use the ath12k driver:
- lspci -nn | grep -i wireless
- lsusb | grep -i wireless
- dmesg | grep -i ath12k
If the host has no wireless hardware and is a cloud VM, the attack surface is smaller but not necessarily zero. - For WSL2: check the WSL kernel version and whether the shipped kernel image includes the module (WSL kernels can include loadable modules as part of the shipped image). Update WSL via Windows Update if Microsoft has released a fixed WSL kernel.
Immediate mitigation and remediation recommendations
Treat Azure Linux images as confirmed in‑scope and apply Microsoft’s updates as a priority. For other Linux artifacts, follow the guidance below.- Patch promptly
- Apply the vendor/kernel updates that include the upstream ath12k fix. Major distributions and kernel vendors published updated kernels shortly after disclosure; apply those distribution or kernel vendor updates as soon as engineering/testing windows allow.
- For Azure Linux VMs, patch via the distro’s package manager or via the image update channels Microsoft provides.
- If you cannot patch immediately, use temporary mitigations
- Unload or blacklist the ath12k kernel module on hosts that do not require Wi‑Fi:
- To unload immediately (non‑persistent): sudo modprobe -r ath12k
- To blacklist persistently: add a line like "blacklist ath12k" in /etc/modprobe.d/blacklist-ath12k.conf and rebuild initramfs if required by your distro.
- Use kernel livepatch services (where supported) to push a targeted fix if your vendor offers a livepatch for this CVE.
- For WSL2 users, ensure Windows Update is applied to pull the latest WSL kernel, or manually replace the WSL kernel VHD if Microsoft publishes a fixed kernel release.
- Block or remove access to affected physical Wi‑Fi hardware where possible in sensitive environments (e.g., do not attach wireless NICs to hosts that are not supposed to have them).
- Inventory and monitoring
- Use configuration management tools (Ansible, SCCM, Chef, Puppet) or asset inventory tooling to find kernels and images that contain ath12k.
- For Azure customers: review Azure Marketplace images and any custom images in use. Check AKS/VM node images for presence of the ath12k module.
- Monitor Microsoft’s VEX/CSAF outputs — Microsoft has committed to updating attestations when it identifies additional artifacts that include the vulnerable code.
- Risk‑based triage
- Prioritize patching for hosts that:
- Have the ath12k module present and loaded;
- Are multi‑tenant or expose untrusted users;
- Run user workloads that can interact with local networking hardware or packet injection paths.
- Lower priority: cloud‑only VMs that have no attached Wi‑Fi hardware and where the kernel was built without wireless drivers. But document and justify any decision to defer remediation.
How to interpret Microsoft’s VEX/CSAF attestation practice going forward
Microsoft’s decision to publish CSAF/VEX attestations starting with Azure Linux improves transparency for customers, but also introduces a new operational habit for defenders:- Treat vendor attestation as a definitive, actionable signal for the attested product. If Microsoft says Azure Linux includes the code, act accordingly and patch those images promptly.
- Treat a lack of attestations for other vendor artifacts as absence of attestation, not proof of absence. For large vendors with many artifacts, the inventory work is often phased; additional attestations may follow as inventories complete.
- Use the vendor’s VEX/CSAF metadata in your automation pipelines for triage and reporting, but keep artifact discovery and verification steps in your own asset inventory and scanning workflows for coverage assurance.
Technical notes on exploitation and attacker model
- Attack vector: The CVE affects kernel code that handles packets from hardware; exploitation typically requires local access to a path that can cause the kernel to process a malicious packet with the problematic decapsulation type. This often implies local or adjacent network access with control over wireless frames or physical access to the wireless interface, or running code that can control packet streams from an attached device.
- Privilege requirements: Many kernel driver vulnerabilities can escalate from low privileges to higher privileges if an exploit achieves arbitrary kernel memory corruption. Because of that risk, any host that exposes the affected driver to untrusted inputs should be treated as high priority for patching.
- Complexity: Kernel memory‑corruption bugs vary by exploitability. Some are straightforward to weaponize; others are hard to exploit in practice. Do not assume low exploitability for a kernel memory corruption: the potential impact is high, and the effort to exploit may be worthwhile for advanced attackers.
Operational checklist — what to do next (step‑by‑step)
- Confirm presence
- On each Linux host (including Azure VMs and WSL2 instances), run the presence checks listed above to detect ath12k modules and relevant kernel configs.
- Patch confirmed hosts
- For Azure Linux: apply Microsoft’s updates for Azure Linux images immediately.
- For other Linux hosts: apply your distro vendor kernel updates (look for vendor advisories that mention CVE‑2025‑37943 or updated kernel packages).
- For WSL2: ensure Windows Update has been applied to pull the latest WSL kernel or follow Microsoft’s WSL kernel release guidance.
- Apply temporary mitigations if you cannot patch immediately
- Unload/blacklist ath12k on hosts that do not need wireless.
- Isolate or de‑power Wi‑Fi hardware on high‑sensitivity hosts.
- Consider using host hardening policies to reduce the ability of unprivileged code to trigger driver paths.
- Inventory and monitoring
- Use your asset management system to list all images and VM types; query for kernel versions and installed modules.
- Subscribe to vendor VEX/CSAF feeds and Microsoft’s security advisories to receive updates if Microsoft expands the attestation to additional products.
- Post‑patch validation
- After patching, reboot as required and verify the kernel version or module version includes the fix.
- Re‑run the presence checks to ensure the patched kernel is in use and the module exhibits the expected behavior in vendor test notes.
- Document and communicate
- Record which hosts were found affected, which mitigations were applied, and the patch timeline.
- For regulated environments, capture the evidence for compliance auditing.
Strengths and limitations of Microsoft’s attestation approach (critical analysis)
Strengths- Improves signal quality. Publishing machine‑readable VEX/CSAF attestations for Azure Linux reduces ambiguity: enterprises can automate triage for attested product families with confidence.
- Faster decision‑making. A clear “confirmed affected” attestation helps security teams prioritize patching for Azure Linux images without hunting through source code provenance.
- Transparency commitment. Microsoft’s phased rollout and the promise to update attestations when other products are identified shows a commitment to supply‑chain transparency.
- Phased coverage leaves gaps. Rolling out attestations product‑by‑product inevitably creates windows where other vendor artifacts are not yet attested; customers can misinterpret absence of attestation as proof of safety.
- Artifact heterogeneity complicates automation. Different kernel builds, configs, and backports mean that a single upstream CVE maps to many binary artefacts — automation must be artifact‑aware rather than vendor‑attestation‑only.
- Dependence on customer verification. Ultimately, customers must verify artifacts they operate. For large cloud vendors with many image families, expecting a vendor’s attestation to cover every artifact is unrealistic in the short term.
Final assessment and guidance
- Immediate operational truth: Azure Linux — confirmed attested and should be patched without delay.
- Broader operational truth: Azure Linux is not necessarily the only Microsoft product that could contain the vulnerable ath12k driver. Absence of attestation for other Microsoft artifacts is not evidence of absence of the vulnerable code.
- Recommended actions for administrators:
- Treat Azure Linux images as high priority and patch them now.
- Inventory all Microsoft‑published Linux artifacts you run (WSL2, Marketplace images, AKS nodes, linux‑azure kernels) and verify for ath12k presence.
- If you cannot patch quickly, apply mitigations such as blacklisting ath12k, isolating Wi‑Fi hardware, and using livepatch services where available.
- Incorporate Microsoft’s VEX/CSAF feeds into your triage automation, but pair that with artifact‑level checks as part of your vulnerability management pipeline.
Conclusion
CVE‑2025‑37943 was fixed upstream by adding a safety check in the ath12k RX processing path. Microsoft’s published attestation confirms Azure Linux includes the vulnerable upstream code and is therefore potentially affected; that attestation should be treated as authoritative for Azure Linux. However, it does not guarantee that other Microsoft products are unaffected — those other products must be verified artifact‑by‑artifact. Administrators should prioritize patching Azure Linux, inventory Microsoft‑distributed images they run, apply kernel updates from their distro vendors, and use temporary mitigations where patching is delayed. Follow Microsoft’s VEX/CSAF attestations for updates, but retain active, artifact‑level verification across your environment to ensure full coverage against this and future kernel driver vulnerabilities.
Source: MSRC Security Update Guide - Microsoft Security Response Center