Microsoft’s short answer — that “Azure Linux includes this open‑source library and is therefore potentially affected” — is correct and actionable for Azure Linux customers, but it is deliberately scoped: it confirms an inventory result for Azure Linux and does not prove that no other Microsoft product can include the same upstream code. Treat the Azure Linux attestation as an authoritative “yes” for that product, and treat every other Microsoft image, kernel build, or appliance as unverified until it has been inventoried or otherwise inspected.
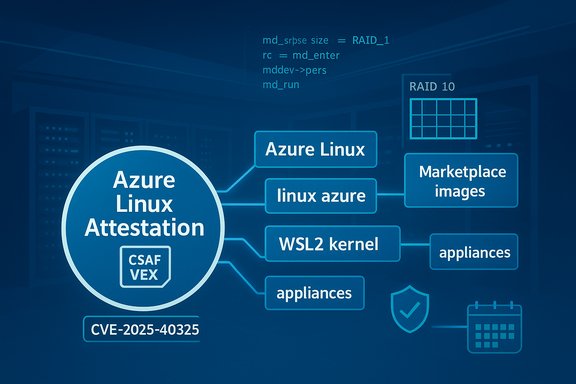
In April 2025 the Linux kernel community and multiple distributor trackers catalogued a bug identified as CVE‑2025‑40325 — a correctness issue in the md/raid10 path where the RAID code must wait a barrier before returning discard requests that carry the REQ_NOWAIT flag. The public technical descriptions treat this as an availability/logging correctness bug rather than a remote code‑execution or confidentiality issue; distributions and vulnerability feeds have mapped the fix to kernel stable commits and distributor package updates. Microsoft’s MSRC entry for the CVE includes a succinct product-level attestation that Azure Linux contains the implicated upstream component and is therefore potentially affected — and Microsoft has publicly committed to publishing machine‑readable CSAF/VEX attestations (a phased rollout beginning with Azure Linux) and to update CVE mappings if additional Microsoft products are later found to carry the component. That policy-level commitment is intended to improve transparency and automation of triage for customers who consume Microsoft’s VEX/CSAF outputs. This article examines what that attestation means, explains the technical and operational implications of CVE‑2025‑40325, and provides practical guidance for operators who must determine whether other Microsoft‑supplied artifacts in their environment may also be carriers and therefore require remediation.
Long answer (the important nuance): Microsoft’s public attestation that Azure Linux includes the implicated code is authoritative for Azure Linux — customers who run Azure Linux images must treat those artifacts as in‑scope and remediate per vendor guidance. But that attestation is a snapshot of Microsoft’s inventory for that product family at the time of publication; it does not exclude the possibility that other Microsoft artifacts include the same upstream md/raid code. Until Microsoft publishes a VEX/CSAF attestation for another Microsoft product, or until you verify the artifact yourself, you should treat other Microsoft artifacts as unverified rather than as safe. Why this matters operationally:
Operators should therefore:
Source: MSRC Security Update Guide - Microsoft Security Response Center
 Background / Overview
Background / Overview
In April 2025 the Linux kernel community and multiple distributor trackers catalogued a bug identified as CVE‑2025‑40325 — a correctness issue in the md/raid10 path where the RAID code must wait a barrier before returning discard requests that carry the REQ_NOWAIT flag. The public technical descriptions treat this as an availability/logging correctness bug rather than a remote code‑execution or confidentiality issue; distributions and vulnerability feeds have mapped the fix to kernel stable commits and distributor package updates. Microsoft’s MSRC entry for the CVE includes a succinct product-level attestation that Azure Linux contains the implicated upstream component and is therefore potentially affected — and Microsoft has publicly committed to publishing machine‑readable CSAF/VEX attestations (a phased rollout beginning with Azure Linux) and to update CVE mappings if additional Microsoft products are later found to carry the component. That policy-level commitment is intended to improve transparency and automation of triage for customers who consume Microsoft’s VEX/CSAF outputs. This article examines what that attestation means, explains the technical and operational implications of CVE‑2025‑40325, and provides practical guidance for operators who must determine whether other Microsoft‑supplied artifacts in their environment may also be carriers and therefore require remediation.What Microsoft’s attestation actually says — and what it does not
The plain reading
- Microsoft’s statement that “Azure Linux includes this open‑source library and is therefore potentially affected” is a product‑scoped inventory result. It confirms Microsoft completed an artifact‑level check for the Azure Linux family and found the vulnerable code there. For anyone running official Azure Linux images or kernels from Microsoft, the attestation is an authoritative, machine‑readable indicator that remediation is needed.
- Microsoft’s publication of CSAF and VEX files — which began in a phased fashion starting in October 2025 — is designed precisely to make these per‑product attestations machine‑actionable. These attestations enumerate whether a product is “Known Affected”, “Not Affected”, “Under Investigation”, or “Fixed” for a given CVE. Microsoft’s blog post describing the VEX rollout documents this phased approach.
What the attestation does not do
- It does not assert that other Microsoft products (for example, WSL2 kernels, linux‑azure kernel builds used for some VM images, Marketplace images, appliance images, or other Microsoft‑published kernels) are free of the same upstream code. Absence of a VEX/CSAF entry for a Microsoft product is not proof of absence; it simply means Microsoft has not yet completed that product’s inventory and published an attestation.
- It is not a blanket guarantee that only Azure Linux images are impacted. Vendors with many artifacts commonly publish attestations product‑by‑product as inventories complete; starting with Azure Linux is a pragmatic rollout decision, not a technical exclusion. Independent analyses have repeatedly emphasized this distinction.
Technical snapshot — CVE‑2025‑40325 in plain language
What the bug is
- Component: Linux kernel — md (multiple‑device) RAID subsystem, raid10 personality (file context: drivers/md/raid10).
- Symptom: raid10_handle_discard previously returned a discard bio with the REQ_NOWAIT flag without waiting for the required barrier. This could lead to incorrect behavior and unnecessary warnings in kernel logs (dmesg) and may impact the correctness of discard (TRIM) handling in certain timing windows.
Impact and exploitability
- Primary impact: Operational correctness and availability/log noise. Several vendor trackers describe the practical consequence as low‑to‑moderate severity: in some configurations it can create spurious calltraces in dmesg and may affect discard ordering semantics. Public trackers score the issue as medium/low depending on environment, since the attack vector is local and the practical effect is limited in many deployments.
- Attack vector: LOCAL — an attacker or misbehaving process with access to block device operations or md control interfaces could trigger the path. Typical high‑risk environments are multi‑tenant hosts, virtualization hypervisors, CI/image build servers, or any place where untrusted workloads can manipulate block I/O semantics.
Fix and distribution mapping
- Upstream maintainers applied small, surgical fixes in the md stack to ensure the discard path waits appropriately and does not print unnecessary warnings for REQ_NOWAIT paths. The upstream commits were backported or included in stable kernel trees and distributors published patched kernel packages. Operators should consult their distribution security advisories for the exact fixed kernel package and expected package version. Major trackers such as Debian, Ubuntu, SUSE, and others list fixed package mappings.
Is Azure Linux the only Microsoft product that includes the library?
Short answer: No — not necessarily.Long answer (the important nuance): Microsoft’s public attestation that Azure Linux includes the implicated code is authoritative for Azure Linux — customers who run Azure Linux images must treat those artifacts as in‑scope and remediate per vendor guidance. But that attestation is a snapshot of Microsoft’s inventory for that product family at the time of publication; it does not exclude the possibility that other Microsoft artifacts include the same upstream md/raid code. Until Microsoft publishes a VEX/CSAF attestation for another Microsoft product, or until you verify the artifact yourself, you should treat other Microsoft artifacts as unverified rather than as safe. Why this matters operationally:
- Microsoft builds and distributes multiple Linux kernel artifacts and images across product lines:
- Azure Linux images (the product Microsoft attested)
- linux‑azure / kernel‑azure builds used by some VM images
- WSL2 kernel (Microsoft‑maintained source and builds for Windows Subsystem for Linux)
- Marketplace/partner images and appliance binaries that may embed the same or similar kernel modules
- Management agents or custom images where a kernel module could be statically linked or included in an image
How to verify whether other Microsoft artifacts in your environment are affected
Below is a prioritized, actionable checklist that security teams and system administrators can use to determine exposure across Microsoft artifacts.1. Treat Microsoft’s Azure Linux VEX entry as authoritative for Azure Linux
- If you run official Azure Linux images, follow Microsoft’s remediation guidance and the distribution advisories to patch kernels and reboot where required. The VEX attestation is intended to make that step deterministic.
2. Inventory Microsoft‑supplied artifacts you run
- Identify all Microsoft‑provided images and kernels in your environment:
- Azure VM images where the image publisher is Microsoft (check image metadata).
- Marketplace images and appliances (publisher may be Microsoft or third parties).
- Windows hosts running WSL2 (inspect the WSL2 kernel binary version).
- Any Microsoft-supplied embedded appliances or management nodes.
- For each artifact, record the kernel version and the package or build identifier.
3. Check for md/raid presence at runtime
- On Linux instances, run:
- uname -r
- cat /proc/mdstat
- lsmod | grep md_mod
- lsmod | grep raid10
- If md/raid modules are present or arrays are mounted, treat the host as potentially exposed until the kernel package is confirmed patched. Distribution advisories map patched package versions and upstream commit IDs; use those to confirm.
4. For WSL2 and Windows‑hosted kernels
- WSL2 uses a Microsoft‑maintained kernel binary when not using a custom kernel. Inspect WSL2 kernel versions via:
- wsl uname -r
- If the WSL2 kernel build predates the upstream fix or matches a vulnerable kernel series, open a support case or follow Microsoft’s WSL guidance to update the kernel. Treat WSL2 kernels like any other Microsoft‑built kernel: they must be inventoried individually.
5. Marketplace images and appliances
- Marketplace images are often built by third parties; check each image’s manifest and kernel version. If a Marketplace image references a Microsoft kernel build (linux‑azure) or contains md modules, map it back to your distribution advisories. If the publisher is Microsoft and no VEX entry exists for that product family, treat the image as unverified and request an attestation or supply-chain artifact from the publisher.
6. If you cannot immediately patch: short‑term mitigations
- Restrict access: limit local/untrusted users from manipulating md devices or running mdadm operations.
- Isolate: avoid exposing device‑management interfaces to untrusted containers and guests.
- Monitor: add alarm rules for md subsystem stack traces, repeated discard warnings in dmesg, and hangs during array operations. These signals are commonly used in vendor advisories to detect symptomatic behavior.
Practical risk assessment and prioritization
- Prioritize hosts that:
- Run shared storage or multi‑tenant workloads (cloud hypervisors, CI runners).
- Perform automated reshape/resize or other array management (increase chance of hitting the path).
- Run Microsoft‑supplied Azure Linux images (authoritative attestation = immediate patch priority).
- Lower priority (but not zero): single-tenant desktops and hosts with no md usage or where md modules are absent. Use inventory to move hosts between priority tiers.
- Note on exploitability: public advisories classify this as a local availability/correctness bug rather than a remote RCE. That said, on shared infrastructure, even denial‑of‑service primitives are high‑value to attackers aiming to disrupt services, so rapid remediation remains important.
Why vendor VEX/CSAF adoption matters (and its current limits)
- VEX/CSAF is a machine‑readable standard that lets vendors publish precise per‑product attestations about whether a CVE applies to a product artifact. Microsoft’s staged VEX rollout, starting with Azure Linux, greatly reduces triage noise for customers by providing deterministic answers for each attested product. This is a material improvement for vulnerability automation.
- The limitation: large vendors with many artifacts will phase the rollout product‑by‑product. That means short‑term gaps in coverage — and absence of an attestation is not an attestation of absence. Security and operations teams must continue to perform artifact‑level inventory and scanning for Microsoft‑supplied artifacts that are not yet covered by VEX.
Recommended operational playbook (quick checklist)
- Inventory first: list all Microsoft‑published images, kernels, and appliances you run.
- For Azure Linux instances: follow Microsoft’s VEX/CSAF guidance and your distro advisories — patch and reboot as required.
- For other Microsoft artifacts: verify kernel versions and module presence; if md/raid is present and the kernel predates the upstream fix, prioritize those hosts for patching or isolation.
- Use distribution advisories (Debian, Ubuntu, SUSE, Red Hat, etc. to map the upstream fix to your vendor’s kernel package and fixed package version. Do not assume that an upstream kernel version number alone is sufficient — confirm the stable commit or package changelog.
- Apply compensating controls if immediate patching is impossible: limit untrusted access to md controls, constrain container privileges, and monitor kernel logs for symptomatic calltraces.
- If you run WSL2 or other Microsoft‑maintained kernels and cannot confirm status from published attestations, open a support case asking Microsoft for an artifact‑level attestation or the kernel build metadata. Treat the response as the authoritative inventory for that product.
Caveats, unverifiable points, and what to watch for
- Unverifiable claim to flag: Unless Microsoft publishes a VEX/CSAF attestation for another product or you yourself inspect the artifact, no public attestation proves other Microsoft products are free of the md/raid code. That is a negative claim that cannot be proven by silence — the correct operational posture is to treat un‑attested Microsoft artifacts as unknown and verify them.
- Confirm the timeline: CVE‑2025‑40325 was publicly documented in vendor trackers in April 2025 and distributors have published fixed kernel packages since then; Microsoft’s CSAF/VEX rollout for third‑party components began in October 2025. Use these dates when engaging suppliers and scheduling remediation windows.
- If you see any vendor statements that claim a product is “not affected”, verify whether that claim is a) an explicit attestation in a VEX/CSAF file, b) based on a kernel‑level inspection, or c) an assumption — prefer attestation (a) or documented test evidence (b). If only (c) exists, treat it as insufficient.
Conclusion
Microsoft’s MSRC attestation that Azure Linux includes the implicated open‑source component for CVE‑2025‑40325 is an important, machine‑readable signal and is authoritative for Azure Linux customers — act on it promptly. However, the attestation’s narrow scope is the key point: it documents Microsoft’s completed inventory for that product family and commits Microsoft to extend attestations over time. It does not prove that other Microsoft products cannot carry the same kernel code.Operators should therefore:
- Treat Azure Linux attestation as a high‑confidence signal and remediate accordingly.
- Inventory and verify every other Microsoft artifact in their estate (WSL2 kernels, linux‑azure images, Marketplace images, appliances). Do not assume absence of an attestation equals safety.
- Use distro advisories and upstream commit IDs to confirm that installed kernels contain the upstream fixes for CVE‑2025‑40325 before declaring a host remediated.
Source: MSRC Security Update Guide - Microsoft Security Response Center