Microsoft’s short MSRC note — that “Azure Linux includes this open‑source library and is therefore potentially affected” — is accurate for the Azure Linux inventory Microsoft has completed, but it is not a categorical guarantee that no other Microsoft product can include the same vulnerable Linux source code. view
CVE‑2025‑37833 is a Linux‑kernel vulnerability in the net/niu driver family that was disclosed in May 2025. The defect is operational and hardware‑interaction centric: on affected systems (notably SPARC platforms in the public reports) the driver’s msix handling can cause a fatal trap when the kernel reads certain MSIX vector registers before the vector’s ENTRY_DATA register has been written. The practical symptom is a non‑resumable kernel error (panic) under very specific device initialization sequences. This description is reflected in public vulnerability databases and vendor trackers.
Microsoft’s public advisory for the CVE includes a concise product attestation: Microsoft has determined that the Azure Linux distribution includes the implicated upstream component and is therefore “potentially affected.” Microsoft also announced it has begun publishing machine‑readable CSAF/VEX attestations (a wider transparency initiative) and committed to updating CVE mappings if additional Microsoft products are later confirmed to ship the same open‑source source files.
That one‑sentence MSRC mapping is the immediate cause of the question we address here: does Microsoft’s wording mean Azure Linux is the only Microsoft product that includes the vulnerable library? The short answer is: No — not necessarily. The longer, operationally useful answer follows.
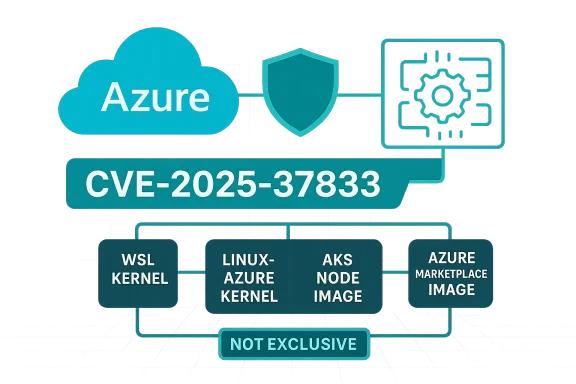
Why this matters: Microsoft distributes many distinct artifacts that may, at build time, contain Linux kernel code or compiled modules originating from the same upstream sources. Each artifact (for example, a kernel image used in WSL, a linux‑azure kernel build, an AKS node image, or Azure Marketplace ISOs) is an independent build-time snapshot. Unless Microsoft explicitly attests those other artifacts as carriers of the same upstream code (via VEX/CSAF entries or advisory text), their status remains unverified.
The practical, defensible guidance for system administrators is straightforward: patch Azure Linux hosts now; treat other Microsoft artifacts as unverified until you confirm otherwise; use VEX/CSAF outputs as they arrive to automate follow‑up; and when in doubt, contact Microsoft support for explicit artifact attestations. The MSRC attestation you quoted is accurate for Azure Linux — but it was never intended to be read as an exclusive warranty that only that product could include the implicated open‑source library.
Source: MSRC Security Update Guide - Microsoft Security Response Center
CVE‑2025‑37833 is a Linux‑kernel vulnerability in the net/niu driver family that was disclosed in May 2025. The defect is operational and hardware‑interaction centric: on affected systems (notably SPARC platforms in the public reports) the driver’s msix handling can cause a fatal trap when the kernel reads certain MSIX vector registers before the vector’s ENTRY_DATA register has been written. The practical symptom is a non‑resumable kernel error (panic) under very specific device initialization sequences. This description is reflected in public vulnerability databases and vendor trackers.
Microsoft’s public advisory for the CVE includes a concise product attestation: Microsoft has determined that the Azure Linux distribution includes the implicated upstream component and is therefore “potentially affected.” Microsoft also announced it has begun publishing machine‑readable CSAF/VEX attestations (a wider transparency initiative) and committed to updating CVE mappings if additional Microsoft products are later confirmed to ship the same open‑source source files.
That one‑sentence MSRC mapping is the immediate cause of the question we address here: does Microsoft’s wording mean Azure Linux is the only Microsoft product that includes the vulnerable library? The short answer is: No — not necessarily. The longer, operationally useful answer follows.
 What the MSRC attestation actually says — and what it doesn’t
What the MSRC attestation actually says — and what it doesn’t
Product‑scoped attestation, not exclusivity
Microsoft’s language — “Azure Linux includes this open‑source library and is therefore potentially affected” — is a product‑inventory statement: it confirms Microsoft inspected the specified product family (Azure Linux) and found the upstream component implicated by the CVE. That is authoritative for Azure Linux customers: treat those images as in‑scope and apply vendor patches. However, this narrow attestation does not prove exclusivity — it does not assert that no other Microsoft product ships the same upstream code. Multiple independent analyses of Microsoft's CVE attestation practice and community commentary emphasize this exact distinction.Why this matters: Microsoft distributes many distinct artifacts that may, at build time, contain Linux kernel code or compiled modules originating from the same upstream sources. Each artifact (for example, a kernel image used in WSL, a linux‑azure kernel build, an AKS node image, or Azure Marketplace ISOs) is an independent build-time snapshot. Unless Microsoft explicitly attests those other artifacts as carriers of the same upstream code (via VEX/CSAF entries or advisory text), their status remains unverified.
Microsoft’s transparency commitments change the game — but inventory is iterative
Microsoft’s rollout of machine‑readable VEX/CSAF attestations improves clarity: these formats allow Microsoft to declare, for each CVE, product‑by‑product status (Not Affected / Under Investigation / Known Affected / Fixed). That capability means Microsoft can and will expand the attestation set over time. But until a product is explicitly listed as “Known Affected,” defenders should not assume either safe or unsafe status for other Microsoft artifacts; they should treat un‑attested artifacts as unverified and perform additional checks if those artifacts are in scope for their environment.Technical summary of CVE‑2025‑37833
- The vulnerability resides in the Linux kernel’s net/niu driver: the code path that interacts with certain NIU (network interface unit) chips and sets up MSI‑X vectors. Public trackers and vendor advisories record the same root cause: reading MSIX vector registers before the ENTRY_DATA register has been initialized can provoke a hardware fault that the kernel cannot recover from.
- The practical effect observed in public reports is a non‑resumable error / kernel panic on SPARC-based systems when the driver encounters specific device and firmware behaviors during MSIX setup. That condition can occur once after power‑up and persist across reboots unless the kernel is patched to set the appropriate driver/hardware flags during initialization.
- The upstream fix implemented in kernel tree(s) applies a defensive measure: mark the PCI device with the flag PCI_DEV_FLAGS_MSIX_TOUCH_ENTRY_DATA_FIRST (or otherwise ensure the driver writes ENTRY_DATA first) so hardware won’t trip when other registers are read. Distribution vendors have back‑ported or patched their kernel packages accordingly. Public advisories (Debian, SUSE, Amazon Linux, etc.) track the distribution updates and the kernel versions that contain the fix.
- Severity and exploitability: This is primarily a local hardware initialization / denial‑of‑service condition; public severity metrics reported a moderately high score (for impact to availability and potential device stability) but it is not described as an elevation‑of‑privilege or remote‑code‑execution vulnerability under typical threat models. That said, any kernel panic on production infrastructure demands prompt remediation.
Is Azure Linux the only Microsoft product that could include the vulnerable code?
The canonical answer for defenders
- Azure Linux is the only Microsoft product Microsoft has publicly attested (so far) to include the specific upstream code referenced by CVE‑2025‑37833. That attestation is meaningful and actionable for anyone running Azure Linux images: apply the vendor update.
- However, Azure Linux is not guaranteed to be the only Microsoft artifact that contains the same Linux kernel source files. Microsoft distributes multiple Linux‑based artifacts (WSL kernels, linux‑azure kernels, CBL‑Mariner derivative images, Azure Marketplace images, AKS node images, appliance images used by specific cloud services), and any of those could — depending on the exact kernel version and build configuration — include the same net/niu driver and thus be susceptible. Absence of an attestation for another product is not proof of absence of exposure.
Examples of Microsoft artifacts that deserve inspectio for Linux (WSL) kernel images shipped with Windows releases and WSL updates occasionally track or rebase upstream kernel commits; historically, WSL kernels have included a mix of upstream code and Microsoft‑specific patches. If a WSL‑distributed kernel version matches or predates the upstream find includes the net/niu driver compiled in that build configuration, the artifact could be affected. This is an artifact‑by‑artifact question, not a blanket “WSL is/aren’t affected” answer.
- linux‑azure or other Microsoft kernel builds used for virtual machine images upstream subsystems depending on kernel version and configuration. Azure Marketplace images, AKS host images, and other distribution pipelines should be considered in scope for inventory checks.
- Any Microsoft service or product that ships an embedded Linux-based appliance, a custom Linux image, or third‑party virtual appliance may likewise incorporate the same upstream source. Again, the only authoritative way to know is inspection or explicit attestation.
How organisations should treat Microsoft’s Azure Linux attestation operationally
- Treat the Azure Linux attestation as authoritative for Azure Linux. Apply vendor-supplied updates for Azure Linux images and kernels immediately if you run them. Microsoft published the Azure Linux mapping intentionally so customers could act on it.
- Do not assume un‑attested Microsoft artifacts are safe. For each Microsoft‑distributed Linux artifact in your environment (WSL kernels, linux‑azure images, custom Marketplace images, appliances, AKS node images), perform one of these actions:
-F/VEX outputs for updated attestations (Microsoft committed to publishing VEX/CSAF and to update CVE records when additional products are found to include the component). - Inspect the artifact directly: query the kernel version, module lists, and the compiled configuration (CONFIG_* flags) to determine whether net/niu is present and whether the kernel revision includes the upstream fix.
- Contact Microsoft support or your Microsoft account team to request explicit attestation for artifacts you rely on if those artifacts are not listed in the MSRC outputs.
- Apply patches where available. Distribution vendors and kernel maintatches or updated kernels; the public trackers (NVD, vendor advisories) list affected kernel versions and available package updates. For environments where a distribution‑level update is not immediately feasible, consider compensating controls (e.g., avoid running workloads on known‑affected images until patched, or disable affected drivers where possible).
For Windows/WSL administrators: what to check and how to triage
- Verify the WSL kernel version shipped with the Windows build or WSL kernel update in use. If the kernel version predates the public fix in upstream trees, inspect whether net/niu is present in that kernel image (lsmod / modinfo, or check /proc/config.gz if available). If so, treat it as unverified and reach out to Microsoft or block the use of that image until clarified.
- If you manage Windows images that bundle WSL or other Linux artifacts for internal developer machines, apply the same artifact inspection and remediation steps as you would for any third‑party or vendor image.
Why Microsoft limits these one‑line attestations and how to interpret them
- Practical constraints: Microsoft ships a very large set of artifacts and images that are rebuilt frequently. Performing a complete, authoritative, product‑by‑product inventory mapping for every CVE in real time is operationally intensive. That’s why Microsoft’s initial MSRC advisory often names the product(s) they have already checked (Azure Linux in this case) and promises to expand the mapping as they verify more artifacts. That iterative approach is transparent and pragmatic — but it also means defenders must not leap from “not listed” to “not affected.”
- The VEX/CSAF rollout (Microsoft’s announced transparency effort) was created precisely tce Microsoft publishes a VEX attestation for a broader set of products, automation tools can triage CVEs against inventories reliably. Until then, treat the Microsoft attestation as a clear “yes” for the named product and treat every other Microsoft artifact as “unknown unless attested.”
Recommended operational checklist (practical, prioritized steps)
- Immediate (0–24 hours)
- Patch any Azure Linux images/hosts you manage using the vendor updates Microsoft points customers to. Azure Linux attestation means you should treat those images as in‑scope now.
- Inventory Microsoft‑supplied Linux artifacts in your environment (WSL kernels, linux‑azure kernels, Azure Marketplace images, AKS node images, VMs, appliances). Flag any artifact that you cannot verify as “needs review.”
- Short term (1–7 days)
- For each flagged artifact, check kernel version and module inclusion; cross‑reference with public kernel fixes (NVD, distribution advisories). If the artifact includes net/niu and predates the upstream fix, schedule remediation or quarantine.
- Subscribe to Microsoft’s CSAF/VEX outputs and vendor advisories for automatic updates on additional product mappings.
- Medium term (1–3 months)
- Update asset inventory and vulnerability‑management feeds to incorporate VEX outputs when available. Automate correlation between the VEX attestation statuses and your internal inventory to avoid repeated manual checks.
- Where vendor patches are unavailable or impractical, implement compensating controls such as removing affected modules from initramfs, blacklisting drivers, or isolating affected hardware profiles.
Strengths and limitations of Microsoft’s current approach (analysis)
Strengths
- Clarity for Azure Linux: Microsoft’s attestation provides a direct, actionable signal for Azure Linux customers — they know they are in scope and can apply updates. That focused mapping is useful and reduces wasted effort chasing false positives.
- Commitment to machine‑readable attestations: Publishing VEX/CSAF outputs is a step forward for supply‑chain transparency and automation. When broadly applied, VEX will materially reduce ambiguity for defenders across vendor ecosystems.
Limitations / Risks
- Inventory incompleteness is not the same as absence of exposure. Microsoft’s initial mapping is necessarily partial. Many organizations incorrectly interpret the absence of an attestation as a “not affected” guarantee, which is unsafe. The operational risk here is failing to triage other Microsoft artifacts that might carry the same vulnerable source.
- Artifact diversity complicates automation. Microsoft delivers many kernel builds over time; each is a different artifact that must be verified. Until vendors publish comprehensive VEX attestations covering all artifacts, defenders must combine vendor attestations with artifact inspection.
- Potential for late discovery of additional affected products. Microsoft has explicitly said it will update CVE entries when new products are identified as carrying the implicated code. That implies additional artifacts may be discovered as the company completes its inventory work. Relying on a snapshot in time is risky; organizations need to maintain continuous monitoring.
Final assessment and practical takeaways
- Azure Linux is the Microsoft product Microsoft has publicly verified as including the upstream component cited in CVE‑2025‑37833. If you run Azure Linux, treat that attestation as an immediate call to action: apply the distribution kernel updates.
- Azure Linux is not necessarily the only Microsoft product that could include the vulnerable net/niu driver. Any Microsoft‑distributed kernel image or Linux artifact is a potential candidate until it is explicitly attested or inspected. Absence of a VEX/CSAF attestation is not proof of safety.
- Operationally, the right approach is pragmatic: act immediately for Azure Linux, inventory and inspect other Microsoft artifacts in your environment, subscribe to Microsoft’s machine‑readable attestations, and apply vendor patches or compensating controls where necessary. Use an artifact‑centric model: map CVE → upstream file(s) → build artifacts → deployed images, and automate that pipeline where possible.
- From a vendor posture perspective, Microsoft’s VEX/CSAF program is the correct long‑term direction. The community’s immediate ask is for Microsoft (and all large vendors) to accelerate and broaden attestations so defenders can triage with confidence and automation.
The practical, defensible guidance for system administrators is straightforward: patch Azure Linux hosts now; treat other Microsoft artifacts as unverified until you confirm otherwise; use VEX/CSAF outputs as they arrive to automate follow‑up; and when in doubt, contact Microsoft support for explicit artifact attestations. The MSRC attestation you quoted is accurate for Azure Linux — but it was never intended to be read as an exclusive warranty that only that product could include the implicated open‑source library.
Source: MSRC Security Update Guide - Microsoft Security Response Center