Microsoft’s short public notice that “Azure Linux includes this open‑source library and is therefore potentially affected” is accurate for the Azure Linux images that Microsoft has inventory‑checked — but it is not a technical guarantee that no other Microsoft product contains the same vulnerable kernel code.
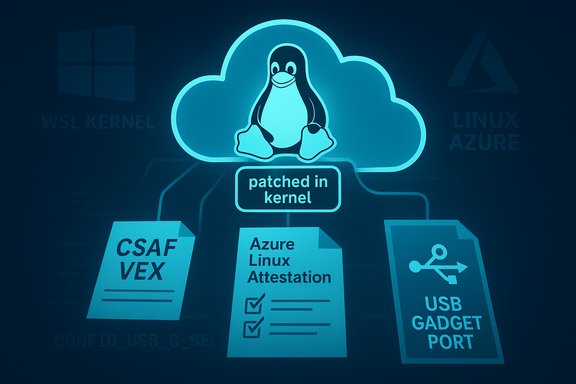
The vulnerability tracked as CVE‑2025‑38448 is a kernel race in the USB gadget serial function (u_serial) that can lead to a NULL‑pointer dereference when the gadget’s TTY wakeup path races with disconnect/close operations. Upstream maintainers fixed the bug by switching to a null‑safe TTY port helper when waking the TTY, removing the window where a wakeup could dereference a cleared pointer. Public vulnerability trackers and distro advisories describe the issue in identical terms. Microsoft’s MSRC advisory for this and other Linux‑component CVEs has used a product‑attestation model: Microsoft published a machine‑readable CSAF/VEX attestation saying Azure Linux images were inspected and that Azure Linux “includes this open‑source library and is therefore potentially affected.” Microsoft also announced it began publishing CSAF/VEX attestations in October 2025 and said it will update CVE entries if additional Microsoft products are later found to ship the same component. That attestation is authoritative for Azure Linux, but it is intentionally scoped and phased.
Why that measured answer is correct:
There is also a communications risk: short product‑attestation phrasing can be misread by non‑technical readers as a sweeping “only Azure Linux is affected” declaration. That misunderstanding can delay discovery and remediation in other artifacts. The correct operational posture is to assume possible exposure for any image that ships a Linux kernel with gadget support until verified otherwise.
Source: MSRC Security Update Guide - Microsoft Security Response Center
 Background / Overview
Background / Overview
The vulnerability tracked as CVE‑2025‑38448 is a kernel race in the USB gadget serial function (u_serial) that can lead to a NULL‑pointer dereference when the gadget’s TTY wakeup path races with disconnect/close operations. Upstream maintainers fixed the bug by switching to a null‑safe TTY port helper when waking the TTY, removing the window where a wakeup could dereference a cleared pointer. Public vulnerability trackers and distro advisories describe the issue in identical terms. Microsoft’s MSRC advisory for this and other Linux‑component CVEs has used a product‑attestation model: Microsoft published a machine‑readable CSAF/VEX attestation saying Azure Linux images were inspected and that Azure Linux “includes this open‑source library and is therefore potentially affected.” Microsoft also announced it began publishing CSAF/VEX attestations in October 2025 and said it will update CVE entries if additional Microsoft products are later found to ship the same component. That attestation is authoritative for Azure Linux, but it is intentionally scoped and phased.What CVE‑2025‑38448 is — concise technical anatomy
- Vulnerable component: Linux kernel — USB gadget: u_serial (the gadget serial function driver).
- Root cause: a race between functions that briefly drop a port lock (usb_ep_queue path) and cleanup/disconnect paths that clear the port’s tty pointers. If a wakeup runs while the port’s tty was cleared, it can dereference a NULL pointer and trigger a kernel oops.
- Observed symptom: kernel oops / stability failure (Null pointer dereference) — primarily an availability/stability problem rather than direct remote code execution.
- Attack vector: local or local‑adjacent — the code path is exercised when gadget endpoints are active; risk increases where untrusted devices or USB passthrough are permitted.
What Microsoft actually said — reading the attestation
Microsoft’s wording is procedural and carefully scoped:- The company published a VEX/CSAF attestation for the Azure Linux distribution documenting which upstream components are present in those images.
- The specific phrasing — “Azure Linux includes this open‑source library and is therefore potentially affected” — means Microsoft inspected Azure Linux and found the component mapped to the CVE. It is an attestation for that product family, not a company‑wide inventory statement.
Is Azure Linux the only Microsoft product that could be affected?
Short answer: No — not necessarily. Azure Linux is the only Microsoft product Microsoft has publicly attested to include the vulnerable component so far, but absence of a published attestation is not proof of absence elsewhere. Any Microsoft product that ships a Linux kernel build (or a distribution image, guest kernel, or appliance image) could conceivably include the same upstream code until it is inventory‑checked.Why that measured answer is correct:
- Presence in source control is not the same as active exposure. A product may carry the upstream file but the kernel build might not enable the module or compile the helper into the image (CONFIG options, disabled drivers, or module blacklists matter).
- Even when the code is compiled in, whether it is used depends on the target hardware and drivers enabled for that image (USB gadget support, gadget functions enabled, or specific SoC drivers).
- Microsoft maintains multiple Linux artifacts: Azure Linux images, linux‑azure kernel builds for some VM families, the WSL2 kernel image that ships with Windows, curated Marketplace images, AKS node images, and other prebuilt or appliance-style images. Any of these could theoretically include the same code until an attestation or vendor advisory says otherwise.
How to verify whether your Microsoft‑supplied artifact is affected
Operators and engineers should not assume “not mentioned = safe.” Perform artifact‑level checks and follow a prioritized verification path:- Inventory: identify which Microsoft artifacts you run that include a Linux kernel image.
- Azure VM images, Marketplace distributions, AKS node images.
- Windows hosts running WSL2 (the WSL kernel image is a Microsoft‑built Linux kernel).
- Appliance images, IoT or prebuilt virtual appliances obtained from Microsoft or the Marketplace.
- Azure Linux (CBL‑Mariner lineage) images are already attested — treat them as in‑scope until patched.
- Inspect the kernel build in the artifact:
- Check uname -r and match the kernel package to vendor advisories.
- Examine kernel config for whether gadget serial support and the relevant helper are enabled (search for CONFIG_USB_G_SERIAL or similar gadget options in the kernel config — exact config names vary by kernel series and vendor packaging).
- On a booted system, check loaded modules: lsmod | grep gserial or similar; inspect /sys/modules and dmesg for gadget function messages.
- Map to vendor/distro advisories:
- Use the distro’s security tracker (Ubuntu, Debian, Oracle, etc. or the NVD entry for CVE‑2025‑38448 to see which kernel packages include the upstream patch.
- If you rely on Microsoft‑provided images and cannot confirm via public advisories:
- Query Microsoft’s CSAF/VEX artifacts for that CVE and those product SKUs (Microsoft has published machine‑readable attestations for Azure Linux and plans to expand coverage).
- Open a support ticket to ask Microsoft to confirm whether a particular image SKU or kernel build is inventory‑checked or will be updated. Microsoft has said it will update CVE pages if additional products are found to carry the component.
- Prioritize based on exposure:
- Hosts that accept USB gadgets, allow USB passthrough, or run untrusted workloads near gadget device nodes are highest priority.
- Embedded or appliance images that are seldom updated and rely on vendor‑forked kernels are high risk.
Practical mitigations until you can patch
- Patch: the definitive fix is a kernel update that includes the upstream commit. Deploy vendor/distribution kernel updates and reboot affected hosts. Upstream patches are already in stable trees and distributions are producing packages.
- Limit device exposure:
- Disable USB passthrough on VMs unless required.
- Enforce USB device allowlists or udev rules to block gadget attachments on sensitive hosts.
- For WSL2 hosts, consider restricting which Windows features allow device passthrough into WSL instances (where applicable).
- Compensating controls:
- Restrict /dev/tty* and gadget device nodes to trusted users.
- For appliances where kernel updates are not available, contact vendor support for backported images.
- Detection:
- Monitor kernel logs (dmesg, journalctl -k) for oops or stack traces referencing gserial, u_serial, or tty_wakeup patterns.
- Add SIEM rules to flag kernel oops and USB gadget-related warnings so you can detect attempted triggers while unpatched.
Why Microsoft’s attestation approach is useful — and where it falls short
Strengths- Actionable signal: the VEX/CSAF attestation for Azure Linux is machine‑readable and gives customers a direct, authoritative input for automated triage and patch pipelines. That reduces guesswork for Azure Linux users.
- Phased transparency: by starting with Azure Linux and promising to expand attestations, Microsoft provides a path to vendor-provided SBOMs/VEX artifacts that security automation can consume.
- Phased rollout = gaps: until Microsoft completes inventory across all product families, customers still need to perform artifact‑level checks for other Microsoft images (WSL, Marketplace, AKS, linux‑azure, appliance images).
- Misinterpretation hazard: terse wording (“Azure Linux includes this library”) can be misread by operators as a blanket denial for every other Microsoft product. The attestation is product‑scoped, so that assumption would be incorrect.
- Vendor‑forked kernels and long tails: many appliances and embedded images run vendor-maintained kernel trees. These often receive fixes on slower schedules; a vendor attestation is required to close that exposure for those products.
Checklist for Windows and Azure administrators (practical, step‑by‑step)
- Identify Microsoft images you run that include Linux kernels: Azure VM images, Marketplace appliances, AKS node images, WSL2 kernel builds.
- For each image:
- Check whether Microsoft has published a CSAF/VEX attestation or CVE update for that SKU.
- If not attested, inspect the image kernel (uname -r, kernel config) or open a support request.
- If gadget serial support is present:
- Apply vendor or distro kernel updates that contain the upstream patch for CVE‑2025‑38448.
- Schedule reboots and validate the image in a pilot ring.
- If patching is delayed:
- Restrict or disable USB passthrough.
- Enforce udev/device access rules.
- Increase kernel log retention and set alerts for gadget/tty oops.
- For WSL2 enterprise deployments:
- Confirm the WSL kernel build in use and check Microsoft attestation or update channels; update the WSL kernel image as advised by Microsoft when a fix is released.
Responsible operator advice and vendor engagement
- Treat Microsoft’s Azure Linux attestation as authoritative and actionable for Azure Linux only until Microsoft expands VEX coverage. Use the attestation to ensure Azure Linux images in your estate are patched promptly.
- Do not assume other Microsoft artifacts are unaffected solely because they are not mentioned; run artifact‑level checks or request explicit confirmation from Microsoft for specific SKUs.
- For third‑party Marketplace appliances or vendor edge devices managed through Azure, query the appliance vendor or the Marketplace publisher about the kernel contents; many Marketplace images are distributed by third parties and may not follow Microsoft’s VEX inventory.
Critical analysis — balancing transparency with operational reality
Microsoft’s decision to publish CSAF/VEX attestations is a clear operational improvement: it gives customers deterministic, machine‑readable data for automated triage. For Azure Linux customers, that reduces uncertainty and helps teams prioritize remediation. The command of upstream kernel fixes is already broad — the u_serial patch is small and widely backported — so the remediation story is straightforward for distributions that actively ship patched kernels. However, the real operational challenge is the long tail: many Microsoft and third‑party artifacts may embed older kernels, vendor forks, or custom builds where the fix has not yet been applied. Those images — particularly appliance‑style or embedded images — require direct vendor engagement to obtain patched images. Microsoft’s attestation does not magically inventory those third‑party or long‑tail images, so customers must remain vigilant.There is also a communications risk: short product‑attestation phrasing can be misread by non‑technical readers as a sweeping “only Azure Linux is affected” declaration. That misunderstanding can delay discovery and remediation in other artifacts. The correct operational posture is to assume possible exposure for any image that ships a Linux kernel with gadget support until verified otherwise.
What to expect next (timeline & signals)
- Upstream: the kernel fix for CVE‑2025‑38448 is merged and present in stable trees; distributions are mapping it into security packages. Watch distro security trackers (Ubuntu, Debian, Oracle Linux, etc. and the NVD for status on package fixes.
- Microsoft: Microsoft will continue to publish CSAF/VEX attestations for other product families over time; when it discovers additional Microsoft products that include the affected library, it will update the CVE/VEX entries. Until then, use Microsoft’s published VEX output as the authoritative inventory for the attested SKUs only.
- Operators: prioritize Azure Linux images first (attested), then verify WSL, linux‑azure kernels, and Marketplace/appliance images.
Final takeaways
- Microsoft’s public statement about Azure Linux is accurate and valuable: it confirms Azure Linux images were inventoried and found to include the vulnerable component. Treat the Microsoft attestation as authoritative for the attested product family.
- That attestation is not a proof that no other Microsoft product is affected. Any Microsoft artifact that ships a Linux kernel or a prebuilt image could include the same upstream code until it is inventory‑checked and attested. Operators should perform artifact‑level checks for WSL2 kernels, linux‑azure, Marketplace images, AKS node images, and any appliance images they rely on.
- Immediate remediation is straightforward where vendor packages exist: install the patched kernel package and reboot. Where vendor updates are not available, enforce device access controls, disable USB passthrough, and centralize kernel logging to detect attempted triggers.
Source: MSRC Security Update Guide - Microsoft Security Response Center