Microsoft’s short MSRC note that “Azure Linux includes this open‑source library and is therefore potentially affected” is an authoritative inventory attestation for the Azure Linux family — but it is not evidence that no other Microsoft product could carry the same upstream code; operators must treat un‑attested Microsoft artifacts as potentially affected until those artifacts are explicitly inventoried or the vendor updates its CSAF/VEX mappings.
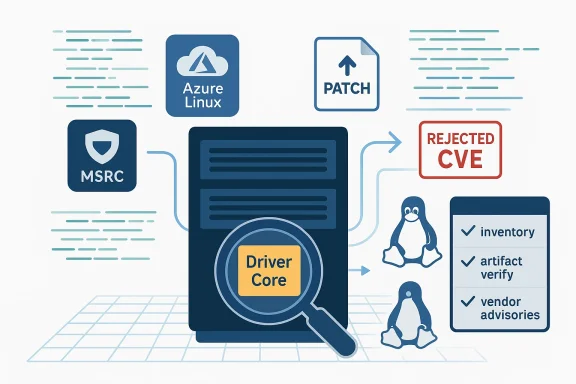
CVE‑2024‑44952 was recorded in public vulnerability trackers but later marked Rejected by its CVE Numbering Authority; NVD and several distributions’ trackers show the CVE entry as withdrawn or rejected. The short technical story in upstream places this fix in the Linux kernel’s driver‑core area (the uevent_show() vs driver detach race), and multiple distributions shipped kernel patches for the underlying locking/deadlock issue.
At the same time Microsoft’s Security Response Center (MSRC) has been publishing product‑scoped attestations that name Azure Linux (the distribution descended from CBL‑Mariner) as a product that “includes this open‑source library and is therefore potentially affected.” Those attestations are part of a broader transparency program: Microsoft began publishing machine‑readable CSAF/VEX attestations in October 2025 and explains the attestation approach in its MSRC blog. Microsoft’s public guidance also says it will update the CVE/VEX records if additional Microsoft products are found to be carriers.
Putting those two facts together — a CNA rejection of the CVE and a Microsoft product attestation naming Azure Linux — produces a practical question for security teams: Does Microsoftnux mean Azure Linux is the only Microsoft product that could contain the vulnerable code? The clear operational answer is: No — but the nuance matters, and it’s the nuance that determines what operators should do next.
That distinction is critical because Linux kernel source code is upstream and reusable: the same driver files or subsystems can be built into many different kernel artifacts depending on configuration, target archig choices. A product‑level attestation is precise about what Microsoft has inventory‑checked; it is not a comprehensive statement covering every possible Microsoft binary or image.
Source: MSRC Security Update Guide - Microsoft Security Response Center
 Background / Overview
Background / Overview
CVE‑2024‑44952 was recorded in public vulnerability trackers but later marked Rejected by its CVE Numbering Authority; NVD and several distributions’ trackers show the CVE entry as withdrawn or rejected. The short technical story in upstream places this fix in the Linux kernel’s driver‑core area (the uevent_show() vs driver detach race), and multiple distributions shipped kernel patches for the underlying locking/deadlock issue.At the same time Microsoft’s Security Response Center (MSRC) has been publishing product‑scoped attestations that name Azure Linux (the distribution descended from CBL‑Mariner) as a product that “includes this open‑source library and is therefore potentially affected.” Those attestations are part of a broader transparency program: Microsoft began publishing machine‑readable CSAF/VEX attestations in October 2025 and explains the attestation approach in its MSRC blog. Microsoft’s public guidance also says it will update the CVE/VEX records if additional Microsoft products are found to be carriers.
Putting those two facts together — a CNA rejection of the CVE and a Microsoft product attestation naming Azure Linux — produces a practical question for security teams: Does Microsoftnux mean Azure Linux is the only Microsoft product that could contain the vulnerable code? The clear operational answer is: No — but the nuance matters, and it’s the nuance that determines what operators should do next.
What “product‑scoped attestation” actually means
Azure Linux = a confirmed carrier, not a universal exclusion
When MSRC says “Azure Linux includes this open‑source library and is therefore potentially affected,” that is an inventory statement about the product family Microsoft has inspected. It confirms Azure Linux images were found to include the implicated upstream component, and that those images therefore require attention from customers running them. It does not provt artifacts or products — WSL2 kernels, linux‑azure kernels used for VM families, Marketplace images, container images, device firmware, or internal builds — cannot also include the same upstream source.That distinction is critical because Linux kernel source code is upstream and reusable: the same driver files or subsystems can be built into many different kernel artifacts depending on configuration, target archig choices. A product‑level attestation is precise about what Microsoft has inventory‑checked; it is not a comprehensive statement covering every possible Microsoft binary or image.
Why vendors publish product‑level attestations first
Vendors typically start with a limited scope for machine‑readable VEX/CSAF disclosures for operational reasons:- Inventorying every internal and derivative artifact is time‑consuming and error‑prone.
- An iterative approach allows a vendor to publish high‑confidence attestations first (the artifacts they have already checked), then expand coverage as additional scans and build‑tree analyses complete.
- Product‑scoped VEX entries reduce false positives for customers who run those specific products, while the vendor’s iterative update promise provides a path to broader coverage.
Why Azure Linux being named does not imply exclusivity
There are three technical and process reasons to avoid equating MSRC’s attestation with a guarantee that no other Microsoft product is affected.- Upstream code is shared, and kernel builds vary.
The kernel is built differently for distinct targets and distributions. A driver or subsystem can be compiled in, compiled as a module, or left out entirely depending on build configuration (CONFIG_* flags). If a Microsoft product ships a kernel build that includes the same driver or subsystem, it is functionally the same upstream code and may be affected. Evidence across multiple disclosures shows the same upstream fix can appear in a range of vendor advisories where only a subset of vendor products have been inspected and attested. - Vendor attestations are artifact‑level, not exhaustive.
Microsoft’s VEX/CSAF program explicitly began with Azure Linux as a first product. The company’s public guidance says it will update the CVE/VEX mapping when additional Microsoft products are identified as carriers. That wording is a promise to expand coverage, not a blanket guarantee that such expansion is unnecessary. Until Microsoft publishes attestations for other artifacts, those artifacts remain in a “not yet mapped” state and must be treated as potentially exposed. - Operational environments multiply risk surfaces.
Many customers run hybrid combinations of Microsoft‑provided artifacts: an Azure VM image with an Azure‑provided kernel, a Marketplace image for a vendor solution, worker nodes with custom kernels, or WSL2 instances on Windows endpoints. Any of these artifacts might, depending on build choices, contain the same upstream driver or library. Treating Azure Linux alone as the only possible carrier risks blind spots.
The CVE status: ‘Rejected’ is not the same as ‘no issue’
CVE‑2024‑44952’s public record shows a “Rejected” status from the assigned CNA, and NVD entries reflect that rejection. Several distributor trackers and vulnerability databases carry the “Rejected” annotation while also listing the upstream fix and shipping patches in distribution kernels. In practice this means:- The CVE identifier was withdrawn or rejected under the CVE assignment process (process reasons vary: duplicate tracking, incorrect assignment, or canonicalization under another CVE number).
- The underlying upstream bug and its patch still exist in kernel trees and distribution kernels; vendors have implemented fixes in their kernels even though the CVE identifier was rejected. That is why you will see kernel patch references and distribution errata alongside a “Rejected” CVE label.
Technical anatomy: where this particular fix lives and why it matters
CVE‑2024‑44952 (as originally described in public trackers) concerned a race between uevent_show() and driver detach in the kernel’s driver core. The class of issue is deadlock or improper locking that could surface as kernel warnings, circular lock dependencies, or in the worst case kernel hangs in pathological sequences.- Upstream patches were applied to the kernel tree to ensure attributes do not dereference a driver pointer while concurrent detach paths can run, and to remove risky device_lock() usage in attribute handlers. Those patches are visible in the stable kernel commits referenced by distribution advisories and security trackers.
- Distributions that ship kernels with the driver‑core code will absorb the upstream fix through standard kernel merges. Because the driver core is a central kernel subsystem, distributions’ kernels often include it; only kernel variants that deliberately disable the affected code would be immune. That means many Linux distributions — and any Microsoft product that reuses or ships a distribution kernel build with the driver core enabled — will find the fix in their kernel errata.
Practical verification: how to determine whether your Microsoft‑provided artifact is affected
Security teams must not rely on product‑level statements alone. Here is a prioritized, actionable checklist you can run in your environment. These steps are pr and targeted at the exact uncertainty introduced by product‑scoped attestations.- Verify Microsoft’s published VEX/CSAF attestation for the CVE (or the VEX product list).
- Check Microsoft’s CSAF/VEX repository entries for the CVE and see which product artifacts are explicitly flagged as “known_affected” vs “component_not_present.” Microsoft has published an explanatory blog and its initial VEX files beginning October 2025.
- Inventory the Microsoft artifacts you run.
- Produce a list of kernels, Marketplace images, WSL2 kernel binaries, and custom images in use. Don’t forget ephemeral or auto‑scaled images. This is an asset management exercise that precedes technical checks.
- On running Linux instances, check the kernel configuration and installed modules. U
- uname -a (kernel version)
- zgrep -i 'CONFIG_DRIVER_CORE' /boot/config-$(uname -r) or equivalent CONFIG flags for the implicated subsystem
- lsmod | grep <module-name> or find /lib/modules/$(uname -r) -type f -name 'drivercore' (replace with the actual driver name when known)
- Search for the specific symbol or file in /lib/modules and /boot to confirm presence. Windows Ftional guidance document these exact commands for artifact verification.
- If your environment uses WSL2 or vendor kernels (linux‑azure, WSL2 kernel binary): validate those kernels the same way. Microsoft distributes WSL2 kernels and linux‑azure kernels separately; they may be configured differx images. Do not assume WSL2 or linux‑azure are unaffected just because Azure Linux is attested.
- For images/containers: extract the kernel or check the image’s package manifest and SBOM (if provided). Container images often avoid shipping their own kernel, but Marketplace VM images or appliances may include kernels built from vendor sources. Use package metadata or SBOMs to find the kernel package and confirm whether the upstream fix appears in the distributed kernel package version.
- If the library/driver is not required at runtime and you can enforce a safider disabling the module or rebuilding the kernel with the driver disabled as a temporary mitigation until vendors publish fixes or attestations. This is environment‑specific and requires testing.
- Track vendor advisories and distribution errata for the concrete kernel package versions that provide the upstream fixes. A rejected CVE ID does not remove the distribution or vendor erratum. Use vendor package hotfixes or kernel updates as the authoritative fix mechanism.
Recommended incident and patching playbook (for security teams)
- Triage: Treat Azure Linux artifacts named in MSRC as confirmed in‑scope. Immediately identify any Azure Linux instances and apply vendor kernel updates where available. (High priority.)
- Inventory sweep: Execute the verification checklist across your fleet and itemize artifacts whose kernel builds include the implicated subsystem. This includes WSL2 endpoints, Azure Marketplace VM images, Bastion or appliance images, and any custom images derived from vendor kernel builds.
- Patch plan: Where the upstream fix has been packaged, prioritize kernel updates according to exposure, criticality, and ease of update. For environments where kernel updates require maintenance windows, schedule them following normal change‑control procedures.
- Temporary mitigations: If a kernel update is not immediately available, consider disabling the kernel module (where safe), restricting access to affected workloads, and increasing monitoring for kernel oopses or hangs.
- Communication: Explain to stakeholders the difference between “attested product carrier” and “exclusive carrier.” Microsoft’s public guidance and VEX files are authoritative for mapped artifacts, but they commit to expanding VEX mappings — meaning the list can grow. Keep stakeholders informed as vendor attestations evolve.
- Automation: Integrate CSAF/VEX feeds into your vulnerability management tooling so that new vendor attestations automatically adjust your remediation priorities. Microsoft’s machine‑readable VEX publishing is intended to support this automation.
Risk analysis: strengths and residual hazards
Notable strengths of Microsoft’s approach
- Transparency via CSAF/VEX: Publishing machine‑readable attestations is a major positive. It reduces ambiguity and enables automation for those customers who consume VEX/CSAF. Microsoft’s public blog committing to VEX shows a clear, modern direction. ([microsoft.com](Toward greater transparency: Introducing Machine-readable Vulnerability Exploitability Xchange (VEX) for Azure Linux and beyond attestation reduces noise**: By naming the product family Microsoft has validated, customers running those products can act quickly without wading through uncertain data.
Residual risks and unresolved gaps
- Incomplete coverage initially: The VEX program’s phased approach means other Microsoft artifacts may remain unmapped for some period. During that window, customers must do additional verification work.
- CVE metadata mismatch: A rejected CVE ID creates a metadata gap that can confuse automated scanners and compliance processes. Some scanners or ticketing systems will treat a rejected CVE differently or suppress it; that can lead to missed patching if teams rely solely on CVE presence. Treat distribution errata and upstream commits as the real technical indicators of risk.
- Supply‑chain complexity: Microsoft’s product ecosystem is lar Without explicit attestations for WSL2 kernels, linux‑azure kernels, Marketplace images, and device images, customers must perform artifact‑level scanning themselves. This is especially true for mixed environments with both Windows hosts running WSL2 and cloud VMs using different kernels.
When can you assume ‘not affected’?
You may safely treat an artifact as “not affected” only when at least one of these is true:- The vendor’s machine‑readable VEX/CSAF file explicitly marks that specific artifact or package as component_not_present or not_affected for the given vulnerability.
- Your artifact‑level verification proves the implicated source file or compiled module itime image or kernel (for example, kernel config shows the driver is disabled and no module binaries are present).
- Vendor errata or distribution package versions clearly document that the fix was not necessary bever included the upstream code.
Final assessment and recommended next steps
- Microsoft’s public wording that “Azure Linux includes this open‑source library and is therefore potentially affected” is accurate and useful for customers who run Azure Linux — it is an authoritative attestation for that product family.
- However, that wording is not an exclusivity guarantee. Given the shared nature of upstream Linux kernel code and the diversity of Microsoft’s Linux artifacts, other Microsoft products could include the same upstream component depending on their kernel configuration and build provenance. Customers should not assume Azure Linux is the only Microsoft artifact that could be a carrier.
- The CVE‑2024‑44952 identifier being marked rejected by CNAs changes the CVE metadata but does not erase the underlying upstream bug or the distribution fixes; operational teams must follow kernel errata and vendor advisories, not CVE presence alone.
- Treat Azure Linux artifacts named by MSRC as in‑scope and apply the vendor’s kernel updates where available.
- Inventory and scan all Microsoft‑provided artifacts in your estate — especially WSL2 endpoints, linux‑azure kernels, Marketplace images, and container hosts — using the artifact‑level verification steps above.
- Integrate MSRC’s CSAF/VEX feeds into your vulnerability management pipeline so future product mappings adjust your priorities automatically.
- Treat rejected CVE IDs as potential housekeeping signals and rely on upstream commits and distribution errata for technical remediation evidence.
Source: MSRC Security Update Guide - Microsoft Security Response Center