Microsoft’s MSRC advisory that “Azure Linux includes this open‑source library and is therefore potentially affected” is an important, actionable attestation — but it is not a categorical guarantee that Azure Linux is the only Microsoft product that could include the vulnerable SQLite code referenced by CVE‑2025‑29087.
CVE‑2025‑29087 is a memory safety vulnerability in certain SQLite releases where the concat_ws() SQL function can cause a heap write beyond an allocated buffer when an attacker‑controlled separator string is extremely large. The practical trigger is an integer overflow during result size calculation, which can leave malloc returning a buffer too small for the data copied into it (the user’s summary described versions 3.44.0 through 3.49.0 prior to the 3.49.1 fix). That makes the vulnerability dangerous in environments that execute untrusted SQL or accept large attacker‑controlled inputs. Microsoft’s public advisory specifically calls out Azure Linux as a Microsoft‑maintained distribution that includes the affected upstream library and should be treated as potentially affected.
What matters operationally is what that MSRC sentence actually means. Microsoft’s wording is a product‑level inventory attestation: it confirms that Microsoft inspected the Azure Linux distribution, found the implicated upstream component, and therefore marks that product in‑scope for follow‑up and remediation. It does not assert that every other Microsoft product has been exhaustively scanned and found clean. Multiple independent analyses and community guidance emphasize this distinction: an attestation for one product is not an exclusivity guarantee for the entire vendor portfolio.
By prioritizing Azure Linux remediation while simultaneously running an aggressive inventory, SBOM and rebuild program across all Microsoft and third‑party artifacts you consume, you’ll convert a single‑product attestation into a comprehensive risk reduction program — the only practical way to stay ahead of library‑level CVEs that can appear in many places at once.
Conclusion: Treat the MSRC attestation as the authoritative signal for Azure Linux, but do not stop there — hunt, patch, rebuild, and verify across your entire estate until you can demonstrate that no other artifacts you run contain the vulnerable SQLite code.
Source: MSRC Security Update Guide - Microsoft Security Response Center
 Background / Overview
Background / Overview
CVE‑2025‑29087 is a memory safety vulnerability in certain SQLite releases where the concat_ws() SQL function can cause a heap write beyond an allocated buffer when an attacker‑controlled separator string is extremely large. The practical trigger is an integer overflow during result size calculation, which can leave malloc returning a buffer too small for the data copied into it (the user’s summary described versions 3.44.0 through 3.49.0 prior to the 3.49.1 fix). That makes the vulnerability dangerous in environments that execute untrusted SQL or accept large attacker‑controlled inputs. Microsoft’s public advisory specifically calls out Azure Linux as a Microsoft‑maintained distribution that includes the affected upstream library and should be treated as potentially affected.What matters operationally is what that MSRC sentence actually means. Microsoft’s wording is a product‑level inventory attestation: it confirms that Microsoft inspected the Azure Linux distribution, found the implicated upstream component, and therefore marks that product in‑scope for follow‑up and remediation. It does not assert that every other Microsoft product has been exhaustively scanned and found clean. Multiple independent analyses and community guidance emphasize this distinction: an attestation for one product is not an exclusivity guarantee for the entire vendor portfolio.
Why the MSRC wording is useful — and why it’s limited
What the attestation gives you
- Immediate focus: If you run Azure Linux images (IaaS VMs, AKS node pools that use Azure Linux images, or appliances built on that distro), you have a clear, authoritative signal to prioritize patching and validation. Microsoft’s public mapping gives Azure Linux customers a direct, actionable next step.
- Transparency baseline: The attestation is part of Microsoft’s broader VEX/CSAF effort to provide machine‑readable product impact data; this enables automation of triage in large environments. Microsoft has committed to expanding these attestations over time.
What the attestation does not give you
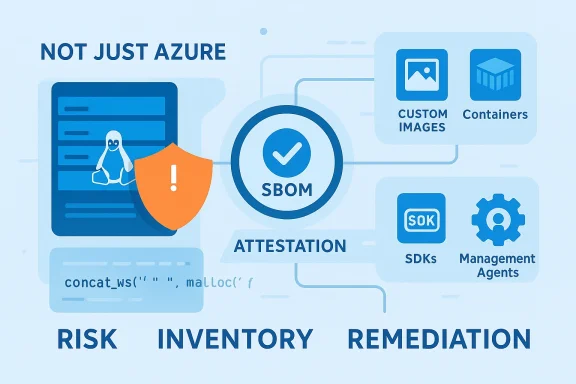
- Not a global exclusion: The statement does not prove that other Microsoft‑branded images, SDKs, management agents, containers, or services cannot contain the same vulnerable SQLite code. Product‑level attestations reflect the scope of the audit performed, not the absence of the component elsewhere. Large vendors ship thousands of artifacts; libraries can be copied or vendor‑pinned into many of them.
- No exhaustive internal visibility for customers: External observers cannot independently validate every internal Microsoft image, build job, or transient container unless Microsoft publishes those attestations or the customer inspects their own consumed artifacts. Accordingly, treat MSRC’s attestation as starting point, not the final answer.
Short answer to the user’s question
No — Azure Linux is the Microsoft product Microsoft has publicly attested to include the implicated SQLite library for CVE‑2025‑29087, and therefore it is explicitly potentially affected. However, Microsoft’s phrasing does not mean Azure Linux is the only Microsoft product that could include that library. Other Microsoft artifacts — custom images, management agents, container images published by Microsoft, or product components that statically link or vendor SQLite — could contain the vulnerable code until those artifacts are explicitly inventoried and declared “Not Affected” or “Fixed.” Customers should therefore assume a conservative posture: prioritize Azure Linux remediation but also hunt for the library across your Microsoft‑supplied artifacts.Technical reasoning: how the same library can appear across products
- Static linking and vendoring: Many applications include SQLite by copying the amalgamation (sqlite3.c / sqlite3.h) into their source tree and compiling it into the final binary. That means the presence of a vulnerable SQLite in a product is a function of the built artifact, not only the base OS package. A Microsoft service, SDK sample, or appliance that compiled SQLite into its binaries could carry the bug even if the underlying OS image is patched. This reality makes a single OS attestation insufficient to guarantee global coverage.
- Container and image reuse: Microsoft publishes numerous base images, management images, sample containers, and Marketplace items. If any of those images came from a distribution snapshot or a third‑party layer that included the vulnerable SQLite, consumers who pull those images could receive an affected copy. The same applies to partner marketplace images built from Microsoft artifacts.
- Third‑party dependencies inside Microsoft products: Complex products bundle third‑party components in many languages (C, C++, Python wheels, Node modules). A transitive dependency can bring SQLite into an artifact where it wasn’t obvious at first glance. Until Microsoft enumerates all artifacts and their SBOMs, you cannot assume absence elsewhere.
Practical impact scenarios
High‑priority scenarios
- Azure VMs or AKS nodes running Azure Linux images that have not been updated: these are explicitly in the MSRC attestation and should be patched first.
- Applications that execute SQL against a bundled SQLite engine and accept untrusted input (for example, management consoles or custom server agents): arbitrary SQL execution or upload of malicious SQL that exercises concat_ws() could trigger the bug.
- Containers and Marketplace images that include system packages or static SQLite copies: these are common carriers if the image maintainer used an older base image.
Medium‑priority scenarios
- Microsoft sample images, SDK containers, or developer VMs that bundle older libraries: these are not necessarily customer production assets but can seed vulnerable dependencies if copied into production workflows.
Lower‑priority (but non‑zero) scenarios
- Azure PaaS managed services that do not ship a user‑facing SQLite binary but may host customer containers: risk depends on whether the runtime executes untrusted SQL or uses a bundled SQLite. Microsoft’s attestation does not prove these are unaffected; it only confirms Azure Linux was scanned. Customers should verify their own artifacts.
What defenders and operators should do now — prioritized playbook
1. Treat Azure Linux as in‑scope immediately
- Identify Azure Linux image versions in use (VM images, custom images built on Azure Linux, AKS node images). Apply Microsoft’s updates or rebuild images against patched SQLite. Microsoft’s attestation makes Azure Linux an immediate remediation priority.
2. Inventory and hunt for SQLite instances across your estate
- Search for known SQLite artifacts:
- Filenames: sqlite3, sqlite3.dll, libsqlite3.so, sqlite3.c, sqlite3.h
- Package managers: dpkg/rpm output (dpkg -l | grep sqlite; rpm -qa | grep sqlite)
- Container images: use SBOM tools to list packages and contents.
- Use binary inspection:
- strings / grep for "SQLite" or "concat_ws" in binaries and libraries.
- ldd to detect dynamically linked libsqlite3.so in Linux binaries.
- Use automated scanners:
- Generate or collect SBOMs (syft), then scan with vulnerability scanners (grype, trivy, or your enterprise scanners).
- For Windows workloads, search application folders and installer payloads for sqlite3.dll or embedded SQLite amalgamation files.
3. Patch, rebuild, and redeploy
- If you find system packages providing SQLite, upgrade using your distribution package manager (apply vendor updates).
- If you find statically linked SQLite in proprietary binaries, update the source to the fixed upstream SQLite release and rebuild. Rebuild all images and containers that include the vulnerable library.
- For containerized workloads, rebuild the container images from patched base images and redeploy.
4. Test and verify
- Run unit and integration tests that exercise SQL paths, especially code that uses concat_ws() or allows large separator strings.
- Validate deployments by checking the SQLite runtime version in the running containers/binaries (runtime metadata, strings output, or version APIs).
- Re‑create SBOMs after rebuild and retain them for future VEX/CSAF alignment.
5. Reduce attack surface where immediate patching isn’t possible
- Temporarily restrict interfaces that accept arbitrary SQL (disable or limit user‑supplied SQL execution).
- Enforce input validation and size limits on separator strings or any user‑supplied string before passing to SQL functions.
- Consider runtime mitigations: sandbox the process, apply strict memory limits, and enable application crash monitoring and auto‑restart policies until patches are applied.
Hunting queries and detection recipes (copy‑paste friendly)
- Find SQLite binaries in Linux images:
- dpkg-based: dpkg -l | grep -i sqlite
- rpm-based: rpm -qa | grep -i sqlite
- Find embedded sqlite in source trees or bundles:
- grep -R --include="*.c" -n "sqlite3" .
- grep -R --include="*.h" -n "sqlite3.h" .
- Find concat_ws usage in your codebase:
- grep -R -n "concat_ws(" .
- Inspect containers without running them:
- syft <image> -o json | jq '.artifacts[] | select(.name|test("sqlite"))'
- trivy image --severity HIGH,CRITICAL <image> (or your enterprise scanner)
- For Windows: search for sqlite3.dll in deployed directories:
- Get-ChildItem -Path C:\ -Filter sqlite3.dll -Recurse -ErrorAction SilentlyContinue
Why you should not rely solely on vendor CVE wording
Multiple independent security analyses reiterate the same caution: a vendor statement that a named distribution or product includes a vulnerable upstream library is valuable, but it does not create a universal safety declaration for everything the vendor ships. Microsoft explicitly said it will update CVE entries if more products are found to include the component — which is the responsible behavior — but until those attestations exist, customers must do their own discovery and verification. Treat vendor attestations as authoritative for what they say, but incomplete for everything they don't explicitly cover.Risk assessment: real‑world severity and exploitation considerations
- The SQLite concat_ws integer overflow is a memory corruption class bug. Memory corruption can lead to denial of service (application crash) and, in some execution environments and with specific memory layouts, could plausibly be escalated to remote code execution. However, publicly documented vendor advisories often conservatively identify DoS as the primary confirmed impact, while more serious exploitation outcomes require additional conditions or proof‑of‑concepts. Treat RCE speculation cautiously until verified.
- The exploitability depends on two main prerequisites:
- The vulnerable SQLite binary must be present in the runtime environment.
- An attacker must be able to execute SQL that reaches concat_ws() with an attacker‑controlled large separator (e.g., multi‑megabyte string).
- In embedded systems or services that allow arbitrary SQL (or template/SQL execution with untrusted inputs), the window for remote exploitation is larger. In managed PaaS offerings that do not expose such exec contexts, the practical exploitability may be limited — but this is a per‑artifact assessment customers must perform.
Corporate governance and SBOM lessons
This CVE and Microsoft’s attestation practice together highlight two supply‑chain best practices:- Produce and consume SBOMs: Suppliers and consumers must exchange SBOMs to make rapid product‑level attestations meaningful. When vendors publish VEX/CSAF, customers can correlate SBOMs to determine which artifacts are affected.
- Automate artifact scanning: Integrate vulnerability scanning into CI/CD and image build pipelines so images uploaded to registries are pre‑scanned and rebuilt if required.
- Document third‑party binary reuse: Maintain a central artifact inventory and build provenance records so when a new CVE is disclosed, you can quickly determine which artifacts to rebuild.
What to expect from Microsoft going forward
Microsoft has pledged to update CVE mappings when additional products are found to include implicated components; that means Microsoft may expand the list of named products for CVE‑2025‑29087 if further internal inventorying identifies other carriers. Until then, the public record accurately reflects Microsoft’s current audited inventory for that CVE: Azure Linux is known to include the vulnerable library. Customers who rely on other Microsoft artifacts should not wait for vendor attestations before performing their own artifact‑level discovery.Bottom line and operational checklist
- Short answer: No — Azure Linux is not necessarily the only Microsoft product that could include the vulnerable SQLite library. It is the only Microsoft product Microsoft has publicly attested to include it for this CVE so far, so treat Azure Linux as the immediate priority.
- Do this now:
- Patch Azure Linux images and rebuild any custom images based on Azure Linux.
- Run an enterprise search for sqlite binaries, libraries, and static embeds across all Microsoft‑supplied images and your own artifacts.
- Rebuild any artifacts that vendor the vulnerable SQLite amalgamation with the fixed upstream release and redeploy.
- Collect SBOMs and map them against vendor VEX/CSAF attestations as they appear.
- Apply temporary mitigations (input size limits, disable arbitrary SQL execution) where immediate patching isn’t possible.
Final analysis and caution
Microsoft’s public MSRC language for CVE‑2025‑29087 is a responsible, limited inventory disclosure: it tells Azure Linux customers to act. But it is not a universal safety guarantee for every Microsoft product, SDK, image or service. For robust defense you need artifact‑level verification — SBOMs, scanning, rebuilds, and telemetry — not just vendor statements. Microsoft’s commitment to expand CSAF/VEX attestations is a positive step; however, until broader attestations are published, security teams must assume the possibility of vulnerable library copies in other artifacts and act accordingly.By prioritizing Azure Linux remediation while simultaneously running an aggressive inventory, SBOM and rebuild program across all Microsoft and third‑party artifacts you consume, you’ll convert a single‑product attestation into a comprehensive risk reduction program — the only practical way to stay ahead of library‑level CVEs that can appear in many places at once.
Conclusion: Treat the MSRC attestation as the authoritative signal for Azure Linux, but do not stop there — hunt, patch, rebuild, and verify across your entire estate until you can demonstrate that no other artifacts you run contain the vulnerable SQLite code.
Source: MSRC Security Update Guide - Microsoft Security Response Center