Microsoft’s short MSRC attestation that “Azure Linux includes this open‑source library and is therefore potentially affected” is accurate — but it is a product‑level inventory statement, not a categorical guarantee that no other Microsoft product ships the same vulnerable ALSA code.
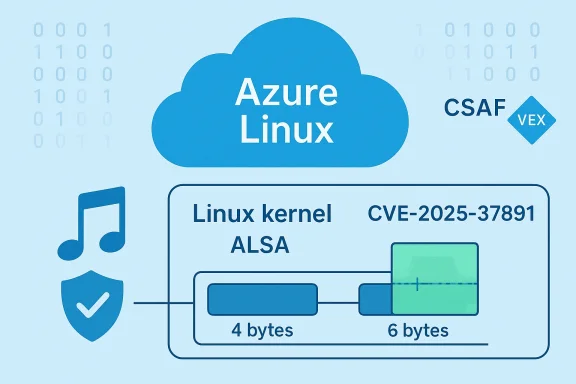
CVE‑2025‑37891 is a Linux kernel vulnerability in the ALSA (Advanced Linux Sound Architecture) subsystem’s UMP (Universal MIDI Packet) conversion path. The defect arises because the MIDI‑to‑UMP conversion routine maintained an internal temporary buffer sized to four bytes while certain SysEx (system exclusive) UMP messages can require up to six bytes; this mismatch can produce a buffer overflow and potential memory corruption when a longer SysEx message is processed. Upstream maintainers fixed the defect by increasing the temporary buffer to six bytes. The issue and its patch are documented in mainstream vulnerability trackers and distributor advisories.
Microsoft’s published vulnerability record for this CVE names Azure Linux (the distro Microsoft maintains for cloud images and related artifacts) as a product that includes the implicated open‑source library and is therefore potentially affected. Microsoft also announced that it began publishing machine‑readable CSAF/VEX attestations with the Azure Linux pilot in October 2025 and will update those records if additional Microsoft products are found to ship the affected upstream component. That procedural commitment is material when interpreting the single‑line MSRC notice.
From an operational perspective, the right posture is straightforward:
Source: MSRC Security Update Guide - Microsoft Security Response Center
 Background / Overview
Background / Overview
CVE‑2025‑37891 is a Linux kernel vulnerability in the ALSA (Advanced Linux Sound Architecture) subsystem’s UMP (Universal MIDI Packet) conversion path. The defect arises because the MIDI‑to‑UMP conversion routine maintained an internal temporary buffer sized to four bytes while certain SysEx (system exclusive) UMP messages can require up to six bytes; this mismatch can produce a buffer overflow and potential memory corruption when a longer SysEx message is processed. Upstream maintainers fixed the defect by increasing the temporary buffer to six bytes. The issue and its patch are documented in mainstream vulnerability trackers and distributor advisories.Microsoft’s published vulnerability record for this CVE names Azure Linux (the distro Microsoft maintains for cloud images and related artifacts) as a product that includes the implicated open‑source library and is therefore potentially affected. Microsoft also announced that it began publishing machine‑readable CSAF/VEX attestations with the Azure Linux pilot in October 2025 and will update those records if additional Microsoft products are found to ship the affected upstream component. That procedural commitment is material when interpreting the single‑line MSRC notice.
What Microsoft’s statement actually means
Attestation versus exclusivity
Microsoft’s wording is intentionally narrow: it communicates the results of Microsoft’s inventory of one product family. An attestation that “Azure Linux includes the library” is an authoritative, actionable statement for customers who run Azure Linux images — they should treat those images as in scope and apply recommended updates. However, the statement does not technically prove that other Microsoft products do not include the same upstream code. Microsoft has said it will expand its machine‑readable VEX/CSAF mappings as it completes inventories of additional product families.Why vendors publish product‑scoped attestations first
- Practicality: large vendors manage thousands of artifacts and can’t instantly inventory every binary and image. Starting with a single product family (Azure Linux) lets Microsoft publish verified attestations quickly and expand coverage systematically.
- Precision: a product attestation reduces “noise” for customers who run that product, allowing them to prioritize remediation.
- Process: VEX/CSAF allow vendors to say “Known Affected” for one product, “Not Affected” for another, or “Under Investigation” while inventory continues.
Is Azure Linux the only Microsoft product that includes the vulnerable ALSA code?
Short answer: No — Azure Linux is the only Microsoft product Microsoft has publicly attested so far to include the specific upstream ALSA code implicated in CVE‑2025‑37891, but absence of an attestation is not proof that other Microsoft artifacts are free of the same code. Treat the Azure Linux attestation as authoritative for Azure Linux images and perform per‑artifact verification on other Microsoft binaries, kernels, and images.Technical reasons why other Microsoft products could also contain the vulnerable code
- Upstream code distribution: the Linux kernel and its subsystems (including ALSA) are shared upstream. The same source files or commits can appear in multiple downstream kernels depending on the version and patchset used.
- Kernel build variability: whether a particular kernel binary includes the affected ALSA UMP code depends on the kernel version and the kernel configuration flags used when that binary was built. One Microsoft product may ship a kernel with a particular set of CONFIG_* options, while another product ships a different build; those differences determine whether a given subsystem is compiled in.
- Multiple Microsoft artifacts: Microsoft ships a variety of Linux artifacts — Azure Linux images, Marketplace images, managed VM images, node images for Kubernetes hosts, WSL2 kernel binaries, and Linux kernels used in specialized services or appliances. Any of these artifacts that contain the same kernel version/commit and have ALSA/UMP enabled could, in principle, include the same vulnerable code until explicitly inventoried.
Attack surface and exploitability — what administrators should understand
- Attack vector: this CVE is a kernel‑level buffer overflow in an ALSA MIDI conversion helper. In most environments the vulnerability surface is local: it requires delivery of specially crafted SysEx messages to the ALSA UMP conversion routine, typically via a connected MIDI device or an emulated device in a VM or container.
- Remote possibilities: remote exploitation is plausible only when untrusted MIDI data can be supplied remotely (for example, through a user‑level service that accepts remote MIDI streams, a guest VM that exposes emulated MIDI devices to a host, or a container environment that forwards raw device traffic). Those are not the default high‑risk paths for most servers.
- Severity: public trackers assigned a moderate‑to‑high impact rating based on potential memory corruption and the fact the issue exists in kernel space;xploitability depends on the environment and available attack vectors.
Practical validation steps (how to confirm whether your Microsoft artifacts are affected)
If you manage Microsoft‑supplied Linux artifacts or any systems that could include Microsoft kernels, follow these verification steps.- Check Microsoft’s VEX/CSAF mapping first
- Review the MSRC CVE entry and the machine‑readable VEX/CSAF documents Microsoft has published; they explicitly list which product families Microsoft has con which are under investigation. If you run Azure Linux, treat the attestation as definitive and remediate immediately.
- Inventory the kernels and images you run
- Collect kernel version strings and the exact kernel packages in each image or VM.
- Where possible, obtain SBOMs or package manifests for the artifact. If Microsoft provides SBOM metadata for an artifact, reconcile that with your deployed images.
- Per‑artifact verification (recommended for “unknown” Microsoft products you run)
- For each kernel image, check whether the ALSA UMP code or related file exists in the build: search for relevant source identifiers, symbols, or object files (for example, grep for function names such as do_convert_to_ump in kernel source trees or check the kernel’s sound subsystem object files). If you cannot access source, check the kernel config and modules for ALSA/UMP support.
- If you operate WSL2 or custom linux‑azure kernels, examine those kernels’ version and config; they may differ from Azure Linux images.
- Apply vendor patches where available
- If Microsoft has published a patched Azure Linux kernel package, install it for Azure Linux instances. For other artifacts, apply the upstream kernel patches or vendor-supplied updates once you’ve confirmed the artifact includes the affected code. Upstream fixes increase the temporary buffer from four to six to accommodate SysEx messages.
- Compensating controls until you can patch
- Disable or restrict access to MIDI devices on hosts where they are not required.
- Avoid forwarding raw MIDI or emulated device streams between privileged host and untrusted guests.
- Apply kernel‑level hardening (e.g., KASLR, strict dmesg restrictions, exploit mitigation sysctls) and monitor for abnormal kernel oops or crashes. These do not fix the bug but can raise the bar for exploitation.
Recommended remediation playbook (step‑by‑step)
- Identify all hosts and images that run Microsoft‑supplied Linux artifacts (Azure Linux, Marketplace images, WSL kernels, managed nodes).
- Check Microsoft MSRC VEX/CSAF for the CVE; apply Azure Linux updates immediately if you run Azure Linux products.
- For non‑Azure Linux Microsoft artifacts: perform per‑artifact verification (see previous section). If the artifact contains the vulnerablthe kernel with an upstream‑backported fix or vendor patch.
- If you cannot patch immediately, implement the compensating controls listed above and schedule a patch window.
- Validate remediation: reboot into the updated kernel and monitor for regressions. Confirm the kernel package/build includes the fix (kernel changelog or package metadata will often list the CVE).
- Document the change in your asset inventory and SBOMs; update incident response and chanyou should not assume “only Azure Linux” equals “only Microsoft product at risk”
- Microsoft’s advisory practice is incremental. By design they started VEX/CSAF with Azure Linux and will extend attestations to other products over time; this makes Azure Linux a definite “yes” but leaves other product families temporarily unverified.
- Kernel artifacts vary. Different product families may ship different kernel versions and configurations; presence of an upstream source file in one artifact does not automatically exclude it from another.
- Distribution timelines differ. Even if Microsoft discovers the issue in multiple af patches and updates across product families can diverge — which means the operational exposure window may be different for Azure Linux instances versus other Microsoft i assessment: who should be most worried
- Operators of cloud or on‑prem systems that accept or forward raw MIDI input from untrusted sources (for example, multimedia servers exposed to end user devices) should prioritize investigation.
- Teams that run custom kernels, WSL2 distributions, or Microsoft Marketplace images shouldfacts are safe simply because only Azure Linux is named in MSRC — they must verify.
- Desktop systems with attached MIDI hardware or sound servers may be exposed if they run vulnerable kernels, but the default enterprise server footprint often lacks the physical input path. Still, virtualization and device emulation can create surprising attack paths.
Strengths and caveats of Microsoft’s VEX/CSAF approach
Strengths
- Clarity for customers who run Azure Linux: the attestation allows those customers to move quickly from detection to remediation without guesswork.
- Machine‑readable metadata: VEX/CSAF enables automation in vulnerability management tools and reduces false positives for product owners.
Caveats and risks
- **Phased coverage creates temporary unkft completes product inventories, some Microsoft artifacts will be “unattested” and must be verified by customers.
Assumptions about exclusivity are dangerous: interpreting the Azure Linux attestation as proof that other Microsoft products are clean is an
What to tell your security and ops teams (short briefing)
- Azure Linux: treat the MSRC attestation as authoritative and apply the patched kernel release as soon as possible.
- Other Microsoft artifacts: do not assume safety — query SBOMs, check kernel versions/configs, and if necessary, open a ticket with your Microsoft support channel to request VEX/CSAF coverage for those products.
- Where you cannot patch immediately: restrict MIDI device access, discontinue forwarding raw MIDI from untrusted sources, and increase kernel monitoring for oops/panic indicators.
Closing analysis and takeaways
Microsoft’s single‑line MSRC advisory correctly communicates an authoritative inventory result for Azure Linux: Microsoft has confirmed the affected ALSA UMP code is present in that product and therefore Azure Linux instances are in scope for CVE‑2025‑37891. That attestation is valuable and actionable for customers who run Azure Linux images. However, the attestation is product‑scoped and procedural — it is not a technical proof that no other Microsoft product carries the same upstream code. Until Microsoft expands its VEX/CSAF coverage, customers must perform per‑artifact verification for any Microsoft kernels, images, or appliances they run.From an operational perspective, the right posture is straightforward:
- Assume Azure Linux is affected and patch it immediately.
- Do not assume any other Microsoft product is automatically safe — verify and patch where necessary.
- If you need help determining whether a specific Microsoft artifact contains the vulnerable code, collect the kernel build details (version and CONFIG), request SBOM/VEX data from the vendor, and treat un‑attested artifacts as “unknown” until proven otherwise.
Source: MSRC Security Update Guide - Microsoft Security Response Center