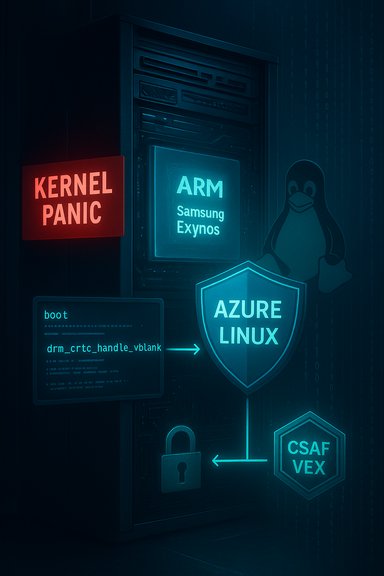
Microsoft’s own advisory for CVE-2025-38467 confirms that the vulnerability exists in the Linux kernel’s Exynos DRM driver — specifically the exynos7_drm_decon IRQ handling path — and that Azure Linux (Microsoft’s managed Linux distribution and kernel builds for Azure) is explicitly listed as a product that contains the affected code; Microsoft also states it will update the CVE and its public CSAF/VEX entry if additional Microsoft products are later found to include the vulnerable component.
CVE-2025-38467 describes a race-condition/null-pointer dereference in the Linux kernel’s Exynos DRM display controller code (the exynos7_drm_decon driver). Under certain boot-time configurations — for example when another console device like a serial TTY is present — the driver may call drm_crtc_handle_vblank without confirming the DRM device is in a state able to service vertical-blank (vblank) handling. That call can lead to a NULL-pointer dereference and a kernel panic during boot. Upstream kernel maintainers fixed the issue by adding a guard that verifies vblank handling is valid before calling into drm_crtc_handle_vblank.
Important clarifications and caveats:
That said, the nature of Linux kernel reuse means other Microsoft-delivered kernels could conceivably include the same code in some builds or variants; Microsoft’s promise to update the CVE if additional products are identified is important but does not absolve customers from verifying the kernel configurations of other Microsoft-provided images they run.
Operationally, the vulnerability is a local kernel panic/race condition limited to systems where the Exynos DECON driver is present. For most cloud and server customers running x86_64 infrastructure, the risk is low because the Exynos DECON driver targets SoC/mobilestyle hardware. For device manufacturers, embedded system operators, and any Azure customers who leverage Microsoft’s Azure Linux kernels on ARM-based appliances or devices that could include Exynos support, the correct action is to apply the vendor patch promptly or use available mitigations until a patched kernel is deployed.
Finally: Microsoft’s transparency and CSAF/VEX publishing represent a positive step for enterprise vulnerability management; the prudent path for defenders is to combine vendor advisories with local kernel-level verification (module checks and config audits) to ensure comprehensive coverage beyond vendor-issued product mappings.
Source: MSRC Security Update Guide - Microsoft Security Response Center
 Background / Overview
Background / Overview
CVE-2025-38467 describes a race-condition/null-pointer dereference in the Linux kernel’s Exynos DRM display controller code (the exynos7_drm_decon driver). Under certain boot-time configurations — for example when another console device like a serial TTY is present — the driver may call drm_crtc_handle_vblank without confirming the DRM device is in a state able to service vertical-blank (vblank) handling. That call can lead to a NULL-pointer dereference and a kernel panic during boot. Upstream kernel maintainers fixed the issue by adding a guard that verifies vblank handling is valid before calling into drm_crtc_handle_vblank.- Affected component (concise): drivers/gpu/drm/exynos/exynos7_drm_decon (IRQ path / decon_irq_handler).
- Symptom: intermittent kernel panic during early boot (NULL pointer dereference in drm_crtc_handle_vblank).
- Patch strategy: add a vblank-capable check before invoking drm_crtc_handle_vblank to avoid racing into an unready DRM device.
Why Microsoft’s statement matters
Microsoft’s advisory language does three important things for customers:- Confirms that Azure Linux — the Microsoft-maintained Linux kernel and distro packaging used for Azure images — includes the vulnerable code path.
- Reaffirms Microsoft’s commitment to publish CSAF/VEX data for their Linux-based product components so customers can programmatically ingest impact/mitigation data.
- Leaves the door open: if Microsoft discovers that other Microsoft products contain the same vulnerable code, they will update the CVE/product listing.
Is Azure Linux the only Microsoft product potentially affected?
Short answer: Yes — currently. Microsoft’s publicly published product tree for this CVE lists Azure Linux kernel builds as the Microsoft product that contains the vulnerable code. Microsoft has not listed any additional Microsoft product (for example, WSL kernel releases, Windows components, Azure-managed appliances, or device-specific Microsoft kernels) as containing the vulnerable driver for CVE-2025-38467.Important clarifications and caveats:
- The vulnerability resides in Linux kernel source for an SoC-specific driver (Samsung Exynos DECON). That driver is generally built into kernels that target Exynos-based devices (ARM SoC phones, some embedded platforms), not typical x86_64 server kernels.
- Microsoft’s cloud-oriented Linux kernel builds (the Azure Linux kernels) do include a broad set of drivers for multiple architectures and scenarios; that is why Azure Linux appears in Microsoft’s CSAF product listing. Because Microsoft maintains and ships kernel packages under its “azl / Azure Linux” nomenclature, it is correct for them to list Azure Linux where their kernel builds contain the affected code.
- Other Microsoft projects that consume or ship Linux kernels — for example, the WSL2 kernel that Microsoft publishes for Windows — maintain their own kernel sources and configurations. In practice, WSL kernel builds are configured for the specific host environment and typically do not include SoC-specific drivers that are irrelevant to desktop/server hardware. However, kernel configurations vary by branch, architecture and maintainer choices; therefore the presence or absence of the Exynos driver in every Microsoft-published kernel build cannot be assumed without direct configuration checking.
- Microsoft’s advisory is definitive for what they have currently identified; it is not an exhaustive guarantee that no other Microsoft product ever contains the code. The vendor explicitly promised updates if other Microsoft products are found to include it.
Technical analysis — what the bug is, and why it matters
What component is involved
- Targeted file: the Exynos DRM display controller driver implementation (the exynos7_drm_decon code path in the Linux kernel’s DRM subsystem).
- The issue occurs in the IRQ handler for the DECON display controller (the CPU/SoC-specific display interrupt path).
- The problematic call sequence leads to drm_crtc_handle_vblank being invoked when the associated DRM structures have not been fully initialized or are in a state where vblank handling is not valid — producing a NULL dereference.
Root cause and fix
This is a classic race-condition / state-check problem in kernel interrupt handling:- Race: the IRQ may arrive while console/drm initialization is still incomplete, or when an alternate console device is active, leading to a path where drm_crtc_handle_vblank is unsafe to call.
- Fix: add a fast, defensive check in the IRQ handler to confirm the DRM crtc (display) is capable of handling vblanks before calling drm_crtc_handle_vblank. That prevents the NULL dereference and avoids the kernel panic.
Impact severity
- Direct impact: local denial-of-service (kernel panic / failed boot) on systems where the affected driver is present and the boot-time conditions occur.
- Exploitability: not reported as a remote code-execution vector. It is a crash (DoS) triggered by an interrupt handled while the device is in an unexpected state.
- Likelihood: low on most server/cloud hardware (x86_64 cloud instances) because Exynos drivers are SoC/mobile-specific and unusual in datacenter servers. Higher on devices using Samsung Exynos SoCs and kernels compiled with that driver present.
Practical guidance for Microsoft customers and administrators
Below is a prescriptive checklist administrators can follow to determine exposure and remediate systems under their control.1. Confirm whether your Microsoft-supplied systems are affected
- Check the Microsoft CSAF/VEX for CVE-2025-38467 (Microsoft’s advisory explicitly lists Azure Linux kernel builds). If your subscription uses Azure Linux kernel packages (azl/azl3 kernels indicated in Microsoft product metadata), treat the system as potentially affected.
- For each system, check the kernel package and release:
- On Debian/Ubuntu/RPM-based systems: identify the kernel package name (for Azure Linux this will usually include “azl” or “azure” kernel package names) and the installed kernel version (uname -r).
- On Linux systems where you can run commands, look for the presence of the Exynos DRM driver:
- Check for modules named exynos in /lib/modules/$(uname -r):
- ls /lib/modules/$(uname -r) | grep -i exynos
- Search the kernel config used to build the running kernel for Exynos DRM entries:
- zgrep EXYNOS /proc/config.gz (if /proc/config.gz is present)
- Or examine /boot/config-$(uname -r) for CONFIG_DRM_EXYNOS or related symbols.
- If drivers are built-in (not modules), check whether the kernel binary includes the path drivers/gpu/drm/exynos by searching the kernel build artifacts — this is more advanced but possible.
2. Mitigation options (ordered by recommended priority)
- Install vendor updates (recommended)
- For Azure Linux images or packages, apply the kernel updates Microsoft has published for affected azl kernel versions; reboot systems after kernel upgrades.
- Microsoft’s published vendor fixes (Azure Linux kernel updates) should contain the upstream patch that added the vblank check.
- Temporary workaround: blacklist/remove the module (if module-based)
- If the driver is a loadable module (not built-in), you can prevent it from loading by blacklisting the module:
- Create /etc/modprobe.d/blacklist-exynos.conf containing: blacklist exynos_drm (or the exact module name reported by lsmod).
- Update initramfs and reboot.
- Note: blacklisting may disable display hardware on devices that actually need the Exynos driver.
- For embedded/system builders: recompile your kernel
- If you or your device vendor maintain custom kernels that include Exynos DRM, rebuild with the patched upstream code or remove the driver entirely if unused.
- Operational mitigations
- Avoid connecting serial consoles or enabling alternate consoles on affected hardware while the kernel is unpatched if doing so reliably reproduces the panic. (This is a narrow and situational mitigation and may not be practical for all environments.
3. Monitoring and detection
- Search system logs for early-boot panics mentioning drm_crtc_handle_vblank or decon_irq_handler. Kernel oops/panic messages will identify the call trace.
- Instrument configuration management and inventory systems to detect which images/kernels are deployed and whether they are the Azure Linux packages Microsoft lists as affected.
- Subscribe to Microsoft’s CSAF/VEX feed and the Azure Linux update channels to receive automated notifications when Microsoft revises product impact or publishes patches.
Is WSL or other Microsoft Linux products affected?
- WSL (Windows Subsystem for Linux) ships a Microsoft-maintained Linux kernel for WSL2. That kernel’s configuration is purpose-built for VM/desktop use on Microsoft-hosted Windows installs. Historically, WSL kernel builds omit many SoC-specific drivers that are not relevant to desktop/server-class hardware.
- Therefore, it is unlikely that the standard WSL kernel builds shipped for x86_64 desktops include the Exynos DECON driver. WSL ARM64 kernels are maintained separately, and their config choices can differ.
- However: kernel configuration is ultimately a build-time decision. To be 100% certain, operators who run WSL on ARM64 or any Microsoft-published kernel should:
- Inspect the kernel configuration used by their WSL kernel (config file) for Exynos/DECON entries, and
- Confirm whether the driver exists in the WSL kernel modules or in the built-in tree.
Why this matters to Microsoft’s broader product portfolio
A few strategic takeaways and potential risks for enterprise consumers:- Microsoft’s shift to publish CSAF/VEX data for its Linux kernel components is a notable improvement in transparency. Customers can programmatically parse Microsoft’s advisories and reconcile them against their installed software inventories.
- However, the surface area for Linux code reuse is broad: a single upstream open-source component (like a kernel driver) can be present in many vendor kernels, custom device images, cloud images, and appliance firmware. Microsoft’s initial product mapping listing only Azure Linux is correct as of their advisory, but the presence of the same source code in other Microsoft- or partner-built images is not impossible.
- The risk that similar code slips into other product kernels exists when vendors reuse upstream kernel trees or include large sets of drivers for broad hardware support. This is why Microsoft’s promise to update the CVE if additional products are affected is essential — but it also places responsibility on customers to track vendor CSAF feeds and verify their own images.
Strengths and limitations of Microsoft’s response
Strengths
- Explicit identification of a specific product (Azure Linux): customers with Azure Linux images have clear, actionable information.
- CSAF/VEX adoption: Microsoft’s adoption of structured vulnerability exchange formats gives enterprise customers the ability to automate checks and ingestion into vulnerability management pipelines.
- Public commitment to update: Microsoft stated it will update the CVE if additional internal products are found to include the vulnerable code, which reduces ambiguity and demonstrates a willingness to iterate.
Limitations and risks
- Potential for false negatives at first publication: initial mappings often start narrow (a single product) and are broadened later. Until Microsoft completes cross-product discovery, customers running other Microsoft-provided kernels (custom device kernels, ARM builds, appliance images) must verify locally.
- Kernel configuration variance: Microsoft ships multiple kernel variants for different scenarios; some variants may include extra drivers. This complicates automated assessment if configuration metadata is not centrally published for every build variant.
- Operational inertia: Azure customers may have images derived from or pinned to older kernel versions; updating kernels in cloud-scale fleets is non-trivial and must be planned.
Action checklist for CISOs and Linux platform teams
- Inventory your Microsoft-sourced Linux kernels:
- Identify Azure Linux kernel package versions in your Azure subscriptions and deployments.
- Identify WSL kernel versions used by corporate Windows images (particularly on ARM64 endpoints).
- Search for the Exynos driver in deployed kernels:
- Check /lib/modules and kernel config files for exynos/exynos7_decon entries.
- Patch and reboot affected systems:
- Apply Microsoft’s Azure Linux kernel updates (or vendor-supplied updates) that include the upstream patch.
- Reboot controlled maintenance windows; verify boot success.
- If you cannot immediately patch:
- Consider temporary module blacklisting where the driver is modular and unused.
- Isolate or delay deployment of affected images to Exynos-based devices until patched.
- Automate future checks:
- Ingest Microsoft’s CSAF/VEX outputs programmatically into your vulnerability management system to get immediate notification of product-impact updates.
Final assessment and conclusion
Microsoft’s advisory for CVE-2025-38467 is clear: Azure Linux is the Microsoft product that Microsoft has identified as containing the vulnerable Exynos DRM code. That makes Azure Linux the only Microsoft product explicitly mapped to this CVE in Microsoft’s published CSAF data at the time of this report.That said, the nature of Linux kernel reuse means other Microsoft-delivered kernels could conceivably include the same code in some builds or variants; Microsoft’s promise to update the CVE if additional products are identified is important but does not absolve customers from verifying the kernel configurations of other Microsoft-provided images they run.
Operationally, the vulnerability is a local kernel panic/race condition limited to systems where the Exynos DECON driver is present. For most cloud and server customers running x86_64 infrastructure, the risk is low because the Exynos DECON driver targets SoC/mobilestyle hardware. For device manufacturers, embedded system operators, and any Azure customers who leverage Microsoft’s Azure Linux kernels on ARM-based appliances or devices that could include Exynos support, the correct action is to apply the vendor patch promptly or use available mitigations until a patched kernel is deployed.
Finally: Microsoft’s transparency and CSAF/VEX publishing represent a positive step for enterprise vulnerability management; the prudent path for defenders is to combine vendor advisories with local kernel-level verification (module checks and config audits) to ensure comprehensive coverage beyond vendor-issued product mappings.
Source: MSRC Security Update Guide - Microsoft Security Response Center