Microsoft’s MSRC entry naming Azure Linux as a product that “includes this open‑source library and is therefore potentially affected” is an authoritative, product‑level attestation — but it is not a categorical guarantee that no other Microsoft artifact or product can include the same vulnerable ksmbd code; operators must treat Azure Linux as a confirmed priority while performing artifact‑level discovery across other Microsoft images, kernels, and WSL artifacts.
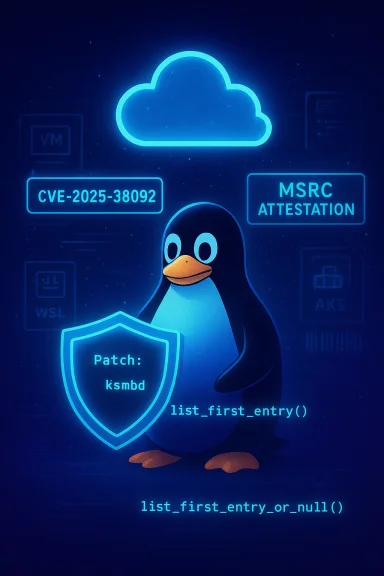
In early July 2025 the Linux kernel community and multiple vulnerability trackers recorded CVE‑2025‑38092, a defect in the in‑kernel SMB server implementation, ksmbd, where an unsafe use of the list traversal helper (list_first_entry()) in opinfo_get_list() could return an invalid pointer if the list became empty; the fix replaces that call with list_first_entry_or_null() to avoid dereferencing an empty list.
Microsoft’s public advisory for the CVE — the short MSRC FAQ line quoted by the user — states that Azure Linux includes the implicated open‑source library and is therefore potentially affected and notes Microsoft’s phased rollout of machine‑readable CSAF/VEX attestations (a program Microsofer 2025). That wording deliberately signals an authoritative inventory result for Azure Linux while promising to update CVE product mappings if additional Microsoft products are later found to ship the same upstream component.
This article explains what that MSRC wording means in practical, operational terms, walks through the technical fix and why it matters, lists the Microsoft artifacts you must check beyond Azure Linux, and gives a prioritized, pragmatic checklist for defenders responsible for mixed estates.
Why this matters practically: a bad pointer dereference in kernel code typically results in an OOPS or panic — i.e., a denial‑of‑service for the host — and in corner cases a memory corruption could be abused in more advanced exploit chains. Most trackers and vendors classify this as an availability‑first issue, but kernel bugs always deserve careful handling because kernels run at the highest privilege level.
Takeaway in one sentence: Azure Linux is the Microsoft product Microsoft has confirmed contains the relevant ksmbd code for CVE‑2025‑38092, but do not assume it is the only Microsoft artifact that could be affected — inventory, verify, and patch your environment promptly.
Source: MSRC Security Update Guide - Microsoft Security Response Center
 Background / Overview
Background / Overview
In early July 2025 the Linux kernel community and multiple vulnerability trackers recorded CVE‑2025‑38092, a defect in the in‑kernel SMB server implementation, ksmbd, where an unsafe use of the list traversal helper (list_first_entry()) in opinfo_get_list() could return an invalid pointer if the list became empty; the fix replaces that call with list_first_entry_or_null() to avoid dereferencing an empty list.Microsoft’s public advisory for the CVE — the short MSRC FAQ line quoted by the user — states that Azure Linux includes the implicated open‑source library and is therefore potentially affected and notes Microsoft’s phased rollout of machine‑readable CSAF/VEX attestations (a program Microsofer 2025). That wording deliberately signals an authoritative inventory result for Azure Linux while promising to update CVE product mappings if additional Microsoft products are later found to ship the same upstream component.
This article explains what that MSRC wording means in practical, operational terms, walks through the technical fix and why it matters, lists the Microsoft artifacts you must check beyond Azure Linux, and gives a prioritized, pragmatic checklist for defenders responsible for mixed estates.
What the code bug is — a concise technical summary
The problem tracked as CVE‑2025‑38092 is straightforward and localized: a function in the ksmbd code used list_first_entry() to obtain the first element of a list without a robust check for an empty list under the list’s locking semantics. The macro list_first_entry() never returns NULL when the list is empty; instead it yields an invalid pointer that, if used, can cause a kernel NULL/dereference or memory corruption. The correct defensive helper is list_first_entry_or_null(), which returns NULL for empty lists and prevents accidental dereferences. The upstream kernel patch switches to the _or_null helper to ensure safe behavior under concurrent conditions.Why this matters practically: a bad pointer dereference in kernel code typically results in an OOPS or panic — i.e., a denial‑of‑service for the host — and in corner cases a memory corruption could be abused in more advanced exploit chains. Most trackers and vendors classify this as an availability‑first issue, but kernel bugs always deserve careful handling because kernels run at the highest privilege level.
What Microsoft’s one‑line advisory actually says — and what it does not
- What Microsoft said (short): “Azure Linux includes this open‑source library and is therefore potentially affected.” That statement is a product‑level inventory attestation: Microsoft checked the Azure Linux build outputs (kernel packages/images) and found the upstream ksmbd component mapped to this CVE. Treat this as an authoritative call to action for Azure Linux customers.
- What Microsoft did not say (and why that matters): the wording is not an exclusivity or global proof‑of‑absence statement for all Microsoft products. Microsoft’s VEX/CSAF rollout is product‑by‑product: an attestation naming Azure Linux confirms inventory work for that product, not an exhaustive rosoft kernel image, WSL build, AKS node image, Marketplace image, or internal binary. Microsoft has stated it will update CVE mappings should additional products be found to include the same upstream code — i.e., the company will expand attestation coverage over time. Until that happens, other artifacts that ship or run kernel images must be treated as unverified, not necessarily safe.
Is Azure Linux the only Microsoft product that could be affected? — Short, evidence‑backed answer
- Short answer: No — not necessarily. Azure Linux is the only Microsoft product Microsoft has publicly attested (so far) to include the vulnerable ksmbd component for CVE‑2025‑38092, ands Azure Linux a confirmed remediation priority. However, the same upstream ksmbd code can and does appear in many different Linux kernel artifacts; any Microsoft artifact that ships or runs a kernel built from a tree containing the vulnerable commit range and configured with ksmbd enabled (built‑in or as a module) could be a carrier until patched. Examples include WSL2 kernels Microsoft distributes, linux‑azure kernels used in some VM SKUs, AKS node images, curated Marketplace images, and custom VM/container base images derived from Microsoft images.
- Why that distinction matters: MSRC’s mapping gives Azure Linux customers an actionable priority (patch Azure Linux), but it does not prove other Microsoft artifacts are free of ksmbd. Absent a Not Affected attestation or independent verification, treat those artifacts as unverified and inspect themrify whether your Microsoft artifacts include ksmbd (practical steps)
On a running Linux host (quick reconnaissance)
- Identify the running kernel: uname -r and uname kernel config for ksmbd flags:
- cat /boot/config-$(uname -r) | grep -i ksmbd
- zgrep -i KSMBD /proc/config.gz (where /proc/config.gz exists)
- Check loaded modules and symbols:
- lsmod | grep ksmbd
- grep -i ksmbd /proc/modules
- dmesg | grep -i ksmbd
- Search kernel symbols and build info: gresyms (requires privileges).
For images or offline kernels
- Inspect the /boot/config-* file inside the image for CONFIG_KSMBD.
- Search image build recipes or kernel packaging metadata for CONFIG_KSMBD or references to fs/smb/server files.
- Compare the kernel version and commit hashes used to build the m kernel commits that fixed CVE‑2025‑38092. Kernel git commit references and stable backports are available in the kernel stable trees.
For Windows endpoints using WSL2
- Treat WSL2 kernels as distinct artifacts. Microsoft publishes the WSL2 kernel source and build configs; inspect the kernel config us or examine the binary’s embedded config when possible. Until Microsoft attests WSL2 as Not Affected, verify it.
For AKS, Marketplace images, and Marketplace contmages labeled “linux‑azure,” “Azure Linux,” or Microsoft‑curated Marketplace images.
- Remember that Marketplace images can be third‑party — each vendor’s packaging choices matter. Do not assume a Marketplace label means “not affegations and remediation — immediate to long term
Immediate (while you patch)
- If in‑kernel SMB functionality is not required, blacklist the ksc/modprobe.d/blacklist-ksmbd.conf containing “blacklist ksmbd” and rebuild initramfs if needed. This prevents the module from auto‑loading.
- Restrict access to SMB ports (TCP 445 and related) via host firewall rules, host network policies, or segmentation to reduce the attack surface for unpatched hosts.
Short/medium term
- Apply vendor kernel updates and livepatches where provided. For Azure Linux, apply Microsoft’s kernel updates as a priority (MSRC’s attestation makes Azure Linux the highesrtifact).
- For custom images and CI/CD pipelines, rebuild and reissue base images with the patched kernel. Update SBOMs and CI manifests to reflect the fixed kernel commit or vendor package version.
Long term (supply chain hygiene)
- Automate SBOM generation for VM images, container base images, and OS artifacts; consume Microsoft’s machine‑readable CSAF/VEX feeds as they become available to reduce manual verificati has said it began publishing these attestations in October 2025 and will expand them over time.
- Integrate image scanning and kernel config checks o future kernel CVEs are flagged before artifacts reach production.
Detection advice — what defenders should look for
Because the likely immediate manifestation of this kind of bug is kernel instability, prioritize log and telemetry checks that reveal OOPSes or panics:- Monitor kernel logs (dmesg, journalctl -k) for stack traces referencing ksmbd, fs/smb/server, oplock, or symbols beginning with ksmbd_.
- Monitor unexpected reboots, repeated crash dumps, and kdump artifacts from hosts that provide SMB services.
- After patching, validate that kernel logs no longer show ksmbd‑related OOPSes and confirm the kernel package matches vendor‑advised fixed versions.
Risk assessment — strengths, limitations, and realistic exposure
- Strengths: The upstream fix is small and surgical (switching to the _or_null helper); it was merged into the stable kernel trees, making vendor backports straightforward. Multiple distributors and trackers cataloged the CVE and fixes, allowing defenders to cross‑check package updates.
- Limitations / residual risk: The key supply‑chain risk is that the same upstream code can be compiled into many different kernel artifacts with different configs. A product‑scoped attestation naming Azure Linux is operationally useful but is not an exhausther Microsoft‑distributed kernels (WSL2, linux‑azure variants, AKS node images, Marketplace images) are free of the same code. Absent an expliciation, treat other Microsoft artifacts as unverified.
- Exploitability: public trackers primarily as an availability/stability problem; widespread, reliable rs unlikely from this particular bug alone, but kernel bugs are high‑impact because they run at ring 0, and on multi‑tenant infrastructure an untrusted tenant can exploit kernel instability to cause denial‑of‑service for co‑tenants.
Practical, prioritized checklist for administrators (quick reference)
- If you run Azure Linux images: apply Microsoft’s published kernel updates now.
- Inventory all Microsoft‑supplied artifacts you run: AKS node pools, VM images (linux‑azure), Marketplace images, WSL2 kernels, and Microsoft‑published container images. Mark any that are Azure Linux‑based as high priority.
- For each artifact, verify ksoot/config-*, lsmod, /proc/modules, and compare kernel commit hashes to upstream fixes.
- If immediate patching is impossible: blacklist ksmbd and restrict SMB network access.
- Rebuild and redeploy images with patched kernels; update SBOMs.
- Subscribe to MSRC VEX/CSAF feeds and distro advisories so your patch automation can consume attestations and package updates automatically.
Why Microsoft’s attestation model is still a net positive — and what to watch for
Microsoft’s move to publish machine‑readable CSAF and VEX attestations is a real improvement in vendor transparency: it enables automation and reduces guesswork when vendors have completed artifact inventories. For Azure Linux customers the attestation provides an immediate, authoritative remediation signal. However, the rollout is phased and product‑by‑pbsence of an attestation for another Microsoft product is an unknown rather than proof of safety. Security teams should embrace the VEX feeds when available, but continue to run artifact‑level verification until attestations fully cover the Microsoft product surface you run.Conclusion — the operational takeaway
Microsoft’s MSRC message that “Azure Linux includes this open‑source library and is therefore potentially affected” is accurate and authoritative for Azure Linux customers — treat it as a high‑priority remediation signal. But it is not an exclusivity guarantee: the same ksmbd code lives in upstream kernel trees and can be included, depending on build choices, in many different Microsoft and non‑Microsoft artifacts. Defenders must therefore treat Azure Linux as the confirmed hit and perform a rapid, artifact‑level inventory across WSL2 kernels, AKS node images, linux‑azure kernels, Marketplace images, and any custom images derived from Microsoft artifacts. Use kernel config checks, module inspections, and SBOM/image scanning as your primary verification tools; blacklist ksmbd and restrict SMB access as an interim mitigation if you cannot patch immediately; and consume Microsoft’s new CSAF/VEX attestations when they become available to automate future verifications.Takeaway in one sentence: Azure Linux is the Microsoft product Microsoft has confirmed contains the relevant ksmbd code for CVE‑2025‑38092, but do not assume it is the only Microsoft artifact that could be affected — inventory, verify, and patch your environment promptly.
Source: MSRC Security Update Guide - Microsoft Security Response Center