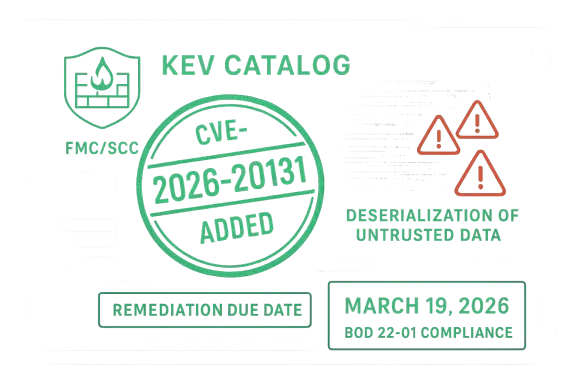
The latest CISA KEV update is a reminder that some of the most dangerous vulnerabilities are not necessarily the most complicated—they are the ones that security teams already know how to classify, but still struggle to contain quickly. On March 19, 2026, CISA added CVE-2026-20131 to its Known Exploited Vulnerabilities Catalog after determining there was evidence of active exploitation, and the affected products are Cisco Secure Firewall Management Center (FMC) Software and Cisco Security Cloud Control (SCC) Firewall Management. Cisco’s advisory describes the issue as an insecure deserialization flaw that can let an unauthenticated remote attacker execute arbitrary Java code as root on an affected device, making it a high-impact exposure for organizations running those management platforms. (cisco.com)
Background — full context
CISA’s KEV Catalog exists for one practical reason: if attackers are already using a vulnerability in the wild, defenders need to treat it as an urgent operational problem rather than a theoretical risk. That is why the agency keeps the catalog live and why Binding Operational Directive 22-01 requires Federal Civilian Executive Branch agencies to remediate listed vulnerabilities by the stated deadline. The policy is not limited to federal agencies in spirit, however; CISA repeatedly encourages all organizations to use the catalog as a prioritization tool because “known exploited” should be a very different category from “maybe someday.” (cisa.gov)CVE-2026-20131 is especially notable because it affects network security management infrastructure, not merely an endpoint or a single exposed application. Cisco says the vulnerability is present in the web-based management interface of Secure Firewall Management Center and in Security Cloud Control Firewall Management, regardless of device configuration. That means the attack surface is tied to administrative control planes that often have broad reach over policy, logging, and deployment across firewall estates. (cisco.com)
Cisco’s advisory is blunt about the impact. The flaw stems from insecure deserialization of a user-supplied Java byte stream, and the company says a crafted serialized object sent to the management interface can result in arbitrary Java code execution as root. In practical terms, that is the kind of issue that can turn a management appliance into a beachhead for lateral movement, policy tampering, credential harvesting, or complete loss of trust in the firewall control environment. (cisco.com)
The other important detail is timing. Cisco published its advisory on March 4, 2026, and CISA added the CVE to KEV on March 19, 2026. That two-week gap suggests the vulnerability moved quickly from vendor disclosure to national prioritization, which is usually a sign that exploitation risk is either already visible or sufficiently credible to justify immediate action. When a control-plane product lands in KEV that fast, it typically means defenders should assume adversaries are looking at it already. (cisco.com)
What makes this even more relevant is the broader pattern. Deserialization flaws have long been a favorite attack vector because they can bypass assumptions about trusted data boundaries and often lead directly to code execution. CISA explicitly called out that this type of vulnerability is a frequent attack vector for malicious cyber actors, and that statement is not just boilerplate—it reflects years of real-world exploitation across enterprise software, remote access tools, and security management products. (cisa.gov)
Why this vulnerability matters
A management-plane compromise is not a normal compromise
A firewall management platform is not just another server. It is the system that defines and distributes policy, collects telemetry, and often serves as the authoritative administrative interface for a much wider security perimeter. If an attacker owns that layer, they may be able to change what traffic is allowed, disable protections, alter logging, or shape incident response visibility. That makes this more than a point-in-time exploit; it is potentially an enterprise-wide trust event. (cisco.com)Deserialization is a classic path to code execution
The core issue here is insecure deserialization of a user-supplied Java byte stream. In enterprise software, deserialization vulnerabilities are dangerous because the application assumes incoming data is benign enough to reconstruct into live objects. If attackers can control that data, they may steer the application into executing malicious logic. Cisco’s own summary says the result can be arbitrary code execution as root, which is about as severe as this class gets. (cisco.com)“Unauthenticated” changes the defensive math
Many enterprise vulns are serious but require credentials or local access. Cisco says this one can be exploited by an unauthenticated, remote attacker. That changes triage priorities dramatically because perimeter assumptions, VPN segmentation, and administrative privilege separation no longer provide the usual barrier. If the vulnerable interface is reachable, it is exposed to internet-scale scanning and opportunistic exploitation. (cisco.com)KEV inclusion is a signal, not a suggestion
CISA does not place a CVE in KEV simply because it is technically severe. The agency adds vulnerabilities because it has evidence of active exploitation, which is a much stronger signal than a high CVSS score alone. Here, Cisco rates the issue at 10.0, and CISA’s decision reinforces that the problem is not theoretical. Organizations should treat the KEV listing as a forcing function for patching, exposure review, and compensating controls. (cisco.com)What Cisco disclosed
Scope of the affected products
Cisco says the flaw affects both Cisco Secure Firewall Management Center Software and Cisco Security Cloud Control Firewall Management. The company specifically notes that the vulnerability applies regardless of device configuration, which reduces the possibility that a simple feature toggle or environment hardening measure would neutralize the risk. (cisco.com)Severity and classification
Cisco assigns CVE-2026-20131 a CVSS base score of 10.0 and maps it to CWE-502, the common weakness category for deserialization of untrusted data. That pairing matters because it confirms the issue is both exploit-prone and fundamentally architectural. When the weakness is in how the software handles data trust, the fix often requires code changes rather than a simple rule update. (cisco.com)Exploit path described by Cisco
According to Cisco, an attacker can exploit the problem by sending a crafted serialized Java object to the web-based management interface. If successful, the attacker can execute arbitrary code on the device and elevate privileges to root. Cisco’s language indicates that the exploit path is straightforward enough to be described at a high level, even if weaponization details remain undisclosed. (cisco.com)Workaround status
Cisco lists no workarounds. That is one of the most important operational details in the advisory because it means defenders cannot rely on configuration-only mitigation as a durable substitute for fixing the software. When no workaround exists, patching, isolation, or service removal become the primary response options. (cisco.com)The security message from Cisco
Cisco’s advisory is part of the March 2026 release of the Cisco Secure Firewall ASA, Secure FMC, and Secure FTD Software Security Advisory Bundled Publication. That bundling matters because it shows the vendor is managing a broader security maintenance cycle across firewall products, and administrators need to review adjacent advisories rather than focus on a single CVE in isolation. (cisco.com)Why CISA KEV listings change the playbook
Federal deadlines are only the starting point
Under BOD 22-01, federal civilian agencies must remediate KEV-listed vulnerabilities by the due date. But even organizations outside government should view that directive as a benchmark for urgency, not a compliance niche. The difference between “patched this quarter” and “patched this week” can be the difference between surviving a scanning campaign and dealing with a breach. (cisa.gov)The KEV catalog is a prioritization engine
Most enterprises cannot patch everything immediately. The KEV Catalog helps security teams decide what to move to the front of the line because those issues have already crossed the threshold from potential to actual abuse. In a world of limited staff and constantly expanding attack surfaces, that kind of prioritization is essential. (cisa.gov)Active exploitation changes incident assumptions
Once a vulnerability is known to be under active exploitation, defenders should assume the attacker community has already invested in reconnaissance, proof-of-concept testing, and likely payload refinement. That does not mean every exposed system is already compromised, but it does mean the window for safe delay is effectively closed. (cisa.gov)KEV also affects vendor communications
When a product lands in KEV, the surrounding ecosystem shifts. MSPs, MSSPs, and internal SOCs should expect more urgent customer questions, more help-desk tickets, and more pressure to provide proof of remediation. KEV entries often become the trigger for emergency patch windows, asset inventory checks, and executive reporting. (cisa.gov)Operational implications for defenders
Inventory comes first
If you do not know whether FMC or Security Cloud Control Firewall Management is deployed, you cannot prioritize the vulnerability correctly. The first response should be a targeted inventory sweep for any Cisco Secure Firewall management platforms, including cloud-managed variants that may be hidden behind service-provider abstractions.- Confirm where FMC is deployed.
- Confirm whether Security Cloud Control Firewall Management is in use.
- Identify internet exposure.
- Map administrative access paths.
- Check whether the management interface is reachable from untrusted networks.
Exposure reduction matters immediately
Because Cisco describes the issue as unauthenticated and remote, organizations should assume exposed management interfaces are high-value targets. Even before patching is complete, defenders should restrict access to known administrator networks, VPN-only paths, or tightly controlled jump hosts wherever operationally possible.- Limit management-plane reachability.
- Remove public exposure if any exists.
- Restrict source IPs at firewall and ACL layers.
- Monitor for unexpected access attempts.
- Treat any external access as suspicious.
Patch management has to be decisive
Cisco states there are no workarounds, which leaves software update as the primary durable fix. That means patch teams should accelerate normal change windows, coordinate with network operations, and avoid the common trap of waiting for “the next scheduled maintenance cycle.”- Review Cisco’s “First Fixed” guidance.
- Test updates against your environment.
- Schedule emergency maintenance where needed.
- Validate after patching.
- Reconfirm service reachability and logs.
Logging and alerting should be intensified
Even if there is no confirmed compromise, a KEV-listed management-plane flaw deserves heightened telemetry review. Security teams should inspect authentication logs, web interface access records, anomalous Java process behavior, and unexpected configuration changes.- Review recent admin logins.
- Look for unusual serialized payload indicators.
- Correlate management activity with change windows.
- Check for root-level command execution artifacts.
- Preserve logs for forensic review.
Incident readiness should be assumed, not hoped for
When CISA says a CVE is actively exploited, it is prudent to prepare for the possibility that exploitation may already have occurred before patching. Organizations should stage response steps in case they uncover signs of tampering or unauthorized policy changes.- Validate firewall rules and ACLs.
- Confirm administrator account integrity.
- Rotate credentials if compromise is suspected.
- Check configuration baselines.
- Consider full incident response if anomalies appear.
Broader lessons from this advisory
Security appliances are high-value targets
Threat actors love security products because they sit close to the heart of the enterprise. A compromise in a firewall management tool can yield a higher payoff than a compromise of a single user workstation. That makes vendor advisories involving management planes especially important to treat as strategic threats, not tactical bugs.- Security tools can become attack platforms.
- Administrative control has disproportionate impact.
- One weakness can affect many downstream devices.
- Control-plane compromise is often stealthier than endpoint compromise.
- Recovery can be more complex than simple reimaging.
Java serialization remains a stubborn risk
The recurring presence of deserialization flaws across enterprise software shows that old design choices can continue creating modern risk. Java object serialization was built for convenience and interoperability, but when used with untrusted input it becomes a liability. Cisco’s advisory is another reminder that secure design choices at the application layer matter as much as perimeter defenses.- Serialization boundaries must be trusted explicitly.
- Untrusted byte streams should be rejected.
- Legacy frameworks can preserve hidden danger.
- Code execution bugs often begin as data-handling bugs.
- Modern secure development must anticipate abuse cases.
CVSS is useful, but not sufficient
A score of 10.0 tells you the issue is severe. KEV tells you it is being exploited. The combination matters because a perfect score without exploitation may still be a planning issue, whereas a KEV item becomes an operational emergency. Good defenders use both signals together rather than relying on one metric alone.- CVSS measures technical severity.
- KEV measures real-world exploitation.
- The combination drives urgency.
- Neither should be used in isolation.
- Risk management requires both context and reality.
Bundled advisories deserve closer reading
Cisco’s March 2026 publication cycle shows why security teams should not read only the headline CVE. Bundled publications often contain multiple fixes, overlapping risk patterns, or adjacent product exposure. A vulnerability in FMC may coincide with related issues in ASA or FTD families, and that can alter maintenance priorities.- Read the full vendor bundle.
- Check related CVEs.
- Avoid patching in a single-vuln silo.
- Review whether common components are shared.
- Coordinate across firewall teams.
Strengths and Opportunities
Strong visibility from CISA
One clear strength in this case is the fast, public prioritization by CISA. KEV inclusion gives organizations an unambiguous signal that the issue deserves immediate attention. That can help cut through executive confusion and shorten internal approval cycles for emergency remediation.- Clear national-level prioritization.
- Easier executive escalation.
- Better SOC and IT alignment.
- Faster maintenance approvals.
- Reduced ambiguity about urgency.
Vendor disclosure is straightforward
Cisco’s advisory is unusually direct about the exploit mechanism and impact. Security teams do not need to infer the threat model from vague language; the advisory states the flaw, the entry point, the privilege level, and the likely outcome. That clarity helps defenders plan faster and more accurately.- The attack vector is described plainly.
- The root cause is identified.
- The impact is explicit.
- The affected product family is clear.
- The absence of workarounds is stated.
Remediation can be prioritized cleanly
Because the issue is highly severe and now in KEV, defenders have a clean decision path: inventory, restrict exposure, patch, and verify. That is simpler than trying to triage a weakly understood flaw with unclear scope. In other words, the problem is serious, but the response model is relatively well defined.- Inventory affected assets.
- Reduce access immediately.
- Apply vendor fixes.
- Validate post-patch behavior.
- Document remediation for auditors.
Opportunity to improve asset hygiene
Incidents like this often expose how little many organizations know about their management plane topology. That creates a useful if uncomfortable opportunity to improve documentation, ownership, and monitoring for firewall administration systems. If the response to CVE-2026-20131 triggers better asset discipline, the organization may come out stronger.- Better software inventory.
- Clearer ownership of management tools.
- Stronger logging standards.
- Improved emergency change procedures.
- Better segmentation around sensitive platforms.
Risks and Concerns
The biggest risk is delayed patching
The most obvious danger is simply that organizations will move too slowly. Because the vulnerability is remote, unauthenticated, and in a management interface, delay widens the exposure window for opportunistic exploitation. If patching waits on normal quarterly rhythm, the enterprise may already be behind.- Delay increases exploit opportunity.
- Publicly known flaws attract scanning.
- Management interfaces are high-value targets.
- The absence of workarounds leaves little buffer.
- Short maintenance windows matter more than usual.
Internet exposure could be worse than expected
Some firewall management systems are deployed in ways that are more reachable than teams realize, especially in hybrid environments, remote administration setups, or cloud-managed deployments. If the management interface is exposed to broad network ranges, the risk is materially worse than if it is tightly bound to internal admin networks.- Review published exposure.
- Check cloud connectivity paths.
- Audit remote admin tooling.
- Validate ACL enforcement.
- Confirm that “private” really means private.
Compromise could be hard to detect
Control-plane attacks are often stealthy because attackers can abuse legitimate administration mechanisms after initial code execution. A successful compromise might not look like obvious malware; it could appear as configuration drift, log suppression, or policy changes that seem operationally plausible at first glance.- Watch for subtle config changes.
- Compare against golden baselines.
- Validate administrative account activity.
- Examine integrity of logging pipelines.
- Investigate unusual rule changes.
Recovery could involve more than patching
If an attacker has executed code as root on a management appliance, patching alone may not be enough. Teams may need to assume credential theft, persistence, or malicious configuration artifacts. In serious cases, rebuilding trust in the management plane may require deeper validation than a simple package update.- Rotate credentials.
- Reissue certificates if needed.
- Revalidate trust anchors.
- Consider appliance rebuilds in severe cases.
- Treat root compromise as a systemic issue.
The advisory may be a preview of follow-on issues
When a major security platform is in the spotlight, there is often a follow-on phase of more targeted attack activity, opportunistic exploitation, and possibly additional related advisories. Organizations should avoid the trap of treating this as a one-and-done patch item. Instead, they should monitor for subsequent Cisco notices and CISA updates.- Expect follow-on threat interest.
- Monitor vendor updates closely.
- Watch for related CVEs.
- Reassess exposure after patching.
- Keep response plans flexible.
What to Watch Next
Cisco remediation guidance
The first thing to watch is whether Cisco publishes additional technical guidance, revised “first fixed” release information, or follow-on details about exploitation conditions. Cisco’s advisory already gives a strong baseline, but operational teams will want to confirm the exact fixed versions before scheduling broad upgrades.- Fixed release mappings.
- Any advisory revisions.
- Potential impact on specific deployment models.
- Additional hardening recommendations.
- Expanded detection guidance.
CISA catalog growth
CISA continues to add vulnerabilities that meet its criteria, and this event may be a signal of more firewall- and management-plane issues landing in KEV soon. Security teams should watch for related products or similar deserialization-class vulnerabilities being added to the catalog, especially if they affect administrative interfaces.- New KEV additions.
- Other Cisco entries.
- Similar remote code execution flaws.
- Patterns in active exploitation.
- Broader enterprise firewall targeting.
Indicators of exploitation in the wild
If additional reporting emerges on exploitation campaigns, that will sharpen the defensive response even further. Even without public technical indicators, organizations should treat the combination of KEV status and root-level remote code execution as sufficient reason to act now rather than wait for proof of widespread abuse.- Threat intelligence updates.
- Exploitation patterns.
- Internet scan activity.
- Initial access reports.
- Post-exploitation behaviors.
Enterprise exposure audits
Many organizations will likely use this event to revisit how they expose and monitor management infrastructure. That is a positive outcome if it leads to better segmentation and a stricter understanding of what should and should not be reachable from general enterprise networks.- Audit management-plane exposure.
- Improve segmentation.
- Reassess remote admin workflows.
- Tighten access controls.
- Strengthen emergency response drills.
Practical response checklist
- Identify every deployment of Cisco Secure Firewall Management Center and Security Cloud Control Firewall Management.
- Determine whether any instance is reachable from the internet or broad partner networks.
- Review Cisco’s fix guidance for the earliest patched release.
- Expedite patching under emergency change control.
- Block unnecessary access to the management interface immediately.
- Review logs for unusual access, configuration changes, or root-level activity.
- Rotate credentials and validate administrative accounts if compromise is suspected.
- Preserve logs and system images for forensic analysis.
- Notify leadership if the exposed system supports enterprise-wide firewall policy.
- Track CISA and Cisco updates for any revisions or related advisories.
Strategic takeaways for security teams
CVE-2026-20131 is the kind of vulnerability that tests whether an organization really treats security infrastructure as critical infrastructure. It is easy to say that the firewall management plane is important; it is harder to execute the inventory, isolation, patching, and validation work needed to keep it safe under pressure. But that work is exactly what separates a manageable alert from an enterprise incident.The most important lesson is that active exploitation dramatically narrows the room for delay. Cisco has identified a root-level remote code execution flaw, CISA has placed it in KEV, and there are no workarounds. That combination means the correct response is not debate—it is urgent remediation, exposure reduction, and verification. In cybersecurity, the fastest path to better outcomes often starts with accepting that the threat is already in motion.
Source: cisa.gov CISA Adds One Known Exploited Vulnerability to Catalog | CISA
Last edited: