The latest CISA advisory on Automated Logic’s WebCTRL Premium Server is a reminder that building-automation software is no longer a niche OT concern; it is a live security issue with direct implications for commercial facilities worldwide. CISA says successful exploitation could let an attacker read, intercept, modify, or impersonate communications, and the affected product line is WebCTRL Premium Server versions earlier than v8.5. The cleanest operational takeaway is simple: if you are still on an unsupported or legacy WebCTRL deployment, you should treat this as a patch-and-contain event, not a routine bulletin. l context
Automated Logic’s WebCTRL platform sits in a category that IT leaders often underestimate until a bulletin lands: it is the supervisory layer for building automation, where heating, cooling, access, and other physical-world controls are coordinated across a facility. That makes the product unusually sensitive to both network exposure and protocol trust. In the March 19, 2026 CISA advisory, the vendor and CISA framed the issue as one affecting commercial facilities at global scale, with the company headquartered in the United States and systems deployed worldwide.
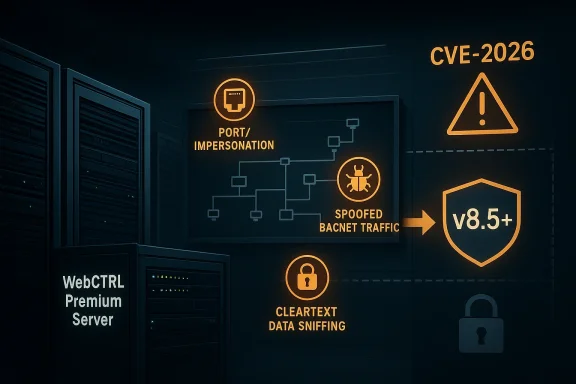
What makes the currly important is that it is not a single bug with a single remediation path. The CISA notice groups three flaws with different attack characteristics: a port-binding issue, a spoofing issue tied to BACnet traffic, and cleartext transmission of sensitive information. All three converge on one common weakness: trust in protocol traffic that is not sufficiently authenticated or protected on the wire. In other words, this is not just about one code defect; it is about the security assumptions embedded in the communication model itself.
Automated Logic has already been moving re secure architecture for several years. In 2022, the company announced BACnet Secure Connect support for WebCTRL, describing BACnet/SC as a way to secure building automation networks using accepted IT security standards. The vendor said WebCTRL v8 software, a BACnet/SC virtual hub, and a BACnet/SC router form the practical path to deploy the more secure model, either on-premises or in the cloud. (automatedlogic.com)
That matters because the CISA advisory specifically points affected customers toward the same direction. Automated Logic notes that WebCTRL 7 is end of life and has been out of support since January 27, 2023, while supported versions of WebCTRL 8.5 cumulative releases and later are paired with secure configuration guidance, BACnet/SC support, and best practices for segmentation and access control. The message from both CISA and the vendor is consisot a quick workaround so much as a modernization step. (automatedlogic.com)
The timing also fits a broader pattern in industrial cybersecurity. CISA continues to publish ICS advisories because building systems, energy systems, and other operational technologies often rely on long-lived protocols and devices that were not originally designed for hostile networks. BACnet is a classic example: it remains deeply embedded in building controls, but its original design assumptions leave room for sniffing, spoofing, and other interception attacks unless defenders add compensating controls. That is exactly the gap BACnet/SC was meant to close. (automatedlogic.com)
The advisory at a glance
CISA assigns the vulnerabilities high severity overall, with one critical issue and two high-sevisory’s risk statement is blunt: exploitation could allow an attacker to read, intercept, or modify communications. For builtranslates into both confidentiality and integrity risk, not just service disruption.What is affected
WebCTRL Premium Server versions earlier than v8.5** are listed as affected.- The advisory applies to sysmmercial facilities and notes worldwide** deployment.
- The vendor’s own guidancebCTRL 7 is EOL and unsupported since January 27, 2023**.
- Supported customers are pointed to WebCTRL 8.5 cumulative releases and later.
The th6-25086: under certain conditions, an attacker could bind to the same port** used by WebCTRL and impersonate the service.
- CVE-2026-32666: WebCTRL systems communicating over BACnetocol’s lack of network-layer authentication, enabling spoofed packets to be processed as legitimate.
- CVE-2026-24060: service informin cleartext BACnet packets, allowing sniffing, interception, and mverity snapshot
- CVE-2026-24060: CV- CVE-2026-25086: CVSS 7.7, High.
CVSS 7.5, High**.
Why BACnet is the real story
BACnet is not a modern zero-trust protocol. It was built for interoperability in building automation, not for an environment where attackers may have access to adjacent networks, compromised endpoints, or externally reachable management surfaces. CISA’s description of CVE-2026-32666 makes that point directly by noting that WebCTRL does not implement additional validation of BACnet traffic, so an attacker with network access could spoof packets toward either the serverThe protocol trust problem
BACnet traffic can be useful and brittle at the same time:- It enables broad interoperability across controllers and supervisory systems.
- It often assumes a trustworthy internal network.
- It can be monitored, captured, and replayed by an attacker who reaches the same segment.
- It becomes especially risky when layered on legacy deployments that lack stronger transport protections. atters in OT
The operationalotocols expose structure and content in the clear, defenders face several problems at once:
- Attackers can map the environment more easily.
- Traffic analysis can reveal process behavior and file updates.
- Replay and manipulation become more practical.
- Incident response becomes harder because “normal” traffic may already be weakly protected.
The port-binding flaw: impersonaection
CVE-2026-25086 is the most interesting of the three from a pure software-security perspective because it is described as a multiple binds to the same port condition. Under certain circumstances, an attacker can bind to WebCTRL’s port, send malicious packets, and impersonate the service without needing to inject code into WebCTRL itself.What that means in practice
This is not the same as a cl or memory-corruption exploit. Instead, it suggests a service-confusion problem:- If the attacker can claim the same port under the right conditions, they may intercept or redirect traffic.
- Clients may talk to the wrong process if validation is weak.
- Service identity becomes a network-level assumption rather than a verified property.
Why defenders should care
A port-binding flaw can be difficult to spot becausexpected traffic patterns while actually talking to a malicious surrogate. In a building-automation context, that could distort command flows, confuse monitoring, or produce subtle but dangerous discrepancies between what operators believe is happening and what controllers actually receive.Practical defensive implications
- Verify which processes own critical ports on WebCTRL hosts.
- Wvice listeners on management systems.
- Segment management interfaces from adjacent user traffic.
- Treat any unexpected port collision as an incident worth investigating.
The BACnet spoofing issue and the limits of perimeter security
CVE-2026-32666 matters because it lands squarely in te over whether OT networks can rely on perimeter security alone. The advisory says the systems inherit BACnet’s lack of network-layer authentication and that WebCTRL does not add enough validation to stop spoofed packets from being processed as legitimate.The attacker model
The advisory does not require the attacker to be a nation-state genius or to have physical access to the building. It saynetwork access. That is a much lower bar in real environments where:- remote access tunnels exist,
- contractors and integrators have network paths,
- business and OT networks are not cleanly separated,
- and poorly monitored internal networks can be traversed after a foothold elsewhere.
What spoofing can enable
Spoofed BACnet packets may be used to:- masquerade as legitimate control traffic,
- inject false commands or responses,
- alter the be,
- and undermine operator trust in telemetry.
Why BACnet/SC changes the calculus
Automated Logic’s BACnet/SC strategy is relevant here because the vendor describes BACnet/SC as using TLS 1.3, authenticated devices, and encrypteden devices. That is exactly the kind of layered trust the original BACnet model lacks. In effect, BACnet/SC is the vendor’s answer to the insecurity that CVE-2026-32666 exposes. (automatedlogic.com)The remediation path: upgrade, segment, and harden
CISA and Automated Logic are not pretending there is a magic band-aid for older deployments. The vendor’s own guidance points users of supported versions to security configuration guidance and BACnet/SC, while explicitly stating that WebCTRL 7 is end of life. The most secure path is to upgrade to the latest WebCTRL server application that supports BACnet/SC. ([automatedlogic.com](https://www.automatedlogic.com/en/company/securi Immediate actions- Inventory every WebCTRL Premium Server instance and verify the exact version.
- Identify any systems earlier than v8.5 as affected.
- **Prioritize unsupported WebCTR migration or replacement.
- Restrict network exposure so control systems areble.
- Isolate control networks behind firewalls and separate them from busiRecommended vendor-aligned path
- Move to WebCTRL 8.5 cumulative releases or later.
-re Connect** where feasible. (automatedlogic.com) - Use the vendor’s published secure configuration guidance. gmentation** so BACnet traffic does not roam freely.
- Review **access coote users and integrators.
Remote access cautions
CISA’s guidarucial: if remote access is required, use more secure methods such as VPNs, while recognizing that VPNs themselves need to be kept current and are only as secure as the devices that connect through them. That is especially relevant in building automation because remote maintenance shortcuts often become permanent convenience paths.How this fits into the wider ICS threat picture
Thisnot isolated. CISA continues to document serious issues in industrial and building automation software because these systems are attractive precisely where IT and physical operations converge. The combination of public IP exposure, remote maintenance, long-lived credentials, and aging protocols makes them ideal targets for opportunistic attackers and patient intruders alike. (automatedlogic.com)Why facility operators should pay attention
Commercial facilities often run on the assumption that “internal” equals “safe.” That assumption no longer holds.- A compromised laptop on the corporate side can become a bridge into OT.
- A third-party maintenance channel can provide a foothold.
- A misconfigured firewall can expose management services unintentionally.
- A legacy protocol can make packet spoofing easier than most operators expect.
Why this matters to ue is not confined to HVAC technicians or building engineers. IT teams own network segmentation, remote access, identity, and logging. If those layers are weak, the control system inherits the weakness. That is why CISA’s standard advice about firewall isolation and minimizing exposure remains so important in OT environments.
The lesson from BACnet/SC
BACnet/SC is nture; it is the architectural response to years of insecure protocol assumptions. Automated Logic’s own material describes it as using TLS 1.3, authentication, and encrypted communications between devices, and its 2022 launch notes say it was intended to make secure deployment on new and existing WebCTRL systems easier. The advisory shows why that transition matters. (automatedlogic.com)Operational checklist for defenders
The most useful response to this advisory is disciplined execution. Teams should turn the bulletin into a short, specific task list.Confirm exposure
- Locate every WebCTRL Premium Server in the environment.
- Record the installed version and patch level.
- Identify whether the server is on-premises or vendor-hosted.
-Cnet traffic is using legacy or secure transport.
Reduce attack surface
- Remove direct internet exposure.
- Limit inbound access to trusted management networks.
- Separate BACnet segments from standard corporate traffic.
- Disabls and review port ownership.
Strengthen trust boundaries
- Prefer BACnet/SC over legacy BACnet wherever possible.
- Enforce mutual authentication.
- Validate controller identities.
- Review ACLs and routing rules for management paths. (automatedlogic.com)
Improve detection
- Watch for unusual listeners or duplicated port bindings.
- Caicious BACnet traffic.
- Log remote access into the WebCTRL environment.
- Correlate anomalies with controller changes or device reconfigurations.
Prepare for incident response
- Preserve packet captures if spoofing is suspected.
- Keep firmware and server versirm backup and recovery procedures for controllers.
- Escalate signs of tampering as both cybersecurity and facilities issues.
Strengths and Opportunities
The strongest feature of this advisory is its clarity. CISA provides a concise, actionable picture of risk, and Automated Logic already has a forward path that replaces insens with BACnet/SC. That makes this less of a mystery disclosure and more of an upgrade forcing function. ([auto://www.automatedlogic.com/en/news/news-articles/bacnet-secure-connect-solutions-now-avaiilding-automation-system.html))Strengths
- Clear affected scope: versions earlier than v8.5 are named.
- Concrete remediation direction: upgrade to supported releases and use BACnet/SC.
- Mature vendor posture: Automated Logic publishes security guidance and a vulnerability reporting channel. (automatedlogic.com)
- Strong protocol rationale: BACnet/SC introduces authentication and encryption. (automatedlogic.com)
- Operational relevance: the impact maps directly to facd communications integrity.
Opportunities
- Use the advisory to accelerate OT asset inventory.
- Reclassify building systems as high-value network assets.
- Fold BACnet into segmentation policy reviews.
- Make version visibility part of facilities governance.
- Treat BACnet/SC migration as an IT/OT modernization project rather than a vendor upgrade. ([automatedlogic.com](httic.com/en/news/news-articles/bacnet-secure-connect-solutions-now-available--for-webctrl-building-automation-system.htmd Concerns
Key risks
- Legacy exposure: WebCTRL 7 is out may be no clean fix short of migration.
- Network trust abuse: BACnet spoofing becomes practical where segmentation is weak.
- Cleartext leakage: sensitive operational details can be captured from the wire.
- Silent impersonation: port-bindiicult to notice quickly.
- Operational drag: facilities teams may delay action if upgrade windows are hard to schedule.
Governance concerns
- Ownership may be split between facilities, OT, and IT.
- Patch approval processes may be slower than attacker timelines.
- Inventory gaps can leave older servers overlooked.
- Remocan obscure true exposure.
The hidden concern
The deeper issue is that building automation often runs quietly until something breaks. That cultural tendency can make defenders complacent. In reality, a “quiet” control system may be one that is already easy to observe, spoof, or impersonate. The absence of alarms is not the same as the absence of risk.What to Watch Next
The next few weeks should clarify how many organizations treat this as an emergency versus a deferred maintenance item. Watch for three signals: whether vendors push migration guidance aggressively, whether integrators accelerate BACnet/SC adoption, and whether defenders start surfacing additional exposure in legacy WebCTRL environments. (automatedlogic.com)Things worth monitoring
- Whether additional vendor notes refine the upgrade path.
- Whether CISA or other authorities add related monitoring guidance.
- Whether public exploit proof-of-concept material appears.
- Whether enterprise facilities teams accelerate segmentation projects.
- Whether managed service providers start reporting wider exposure among customers.
Signals of real progress
- WebCTRL 7 migration plans begin.
- BACnet/SC deployments increase.
- Legacy BACnet segments become isolated.
- Controlservers are moved behind tighter access controls.
- Logging and packet capture become standard in building automation monitoring. (automatedlogic.com)
Signals of trouble
- Organizations acknowledge the advisory but do not inventory affected hosts.
- Unsupported systems remain internet-reachable.
- Remote maintenance shortcuts stay in place.
- Patch windows are delayed indefinitely.
- Security and facilities teams operate in separate sibCTRL Premium Server advisory is important not because it introduces a brand-new class of threat, but because it perfectly illustrates the old one: insecure trust in control networks still creates practical attack paths, and legacy building systems remain too exposed for comfort. The good news is that Automated Logic has a more secure direction in BACnet/SC and a clear support boundary around WebCTRL 8.5 and later. The bad news is that organizations still running older versions will need to move, not merely monitor, if they want to reduce the risk to acceptable levels. (automatedlogic.com)
Source: cisa.gov Automated Logic WebCTRL Premium Server | CISA
Last edited: