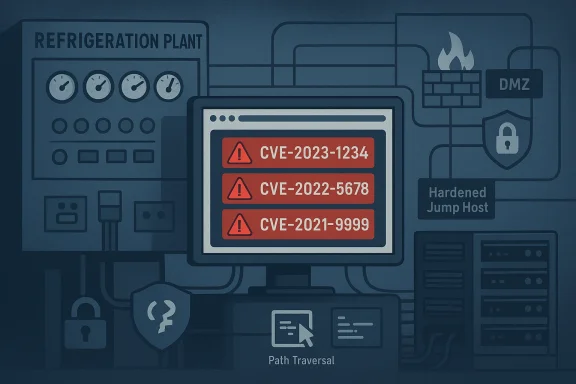
Copeland’s XWEB family — widely deployed web‑supervisors for refrigeration, HVAC and building‑automation systems — is the subject of a high‑severity coordinated advisory that names a large cluster of authentication‑bypass, input‑validation, path‑traversal, and memory‑safety flaws capable of denial‑of‑service, credential theft, and remote code execution against internet‑accessible and poorly hardened devices. om](https://webapps.copeland.com/Dixell/Pages/XWEB_PRO?utm_source=openai))
Background / Overview
Copeland (Dixell brand) XWEB and XWEB Pro devices are web‑based supervisory platforms used in commercial refrigeration, HVAC controls, and cold‑chain monitoring. They expose a browser interface and a set of web APIs intended for remote monitoring and configuration; models in the XWEB PRO line include the XWEB 300D PRO, XWEB 500D PRO and XWEB 500B PRO among others.On February 26, 2026, a coordinated ICS advisory flagged multiple vulnerabilities affecting XWEB PRO firmware through version 1.12.1 and earlier; the advisory catalogs more than twenty tracked CVE identifiers and rates the aggregate vendor equipment impact at a maximum severity (CVSS v3-based vendor rating = 10). The advisory explicitly warns that successful exploitation could let an attacker bypass authentication, crash tmory or execute arbitrary code — outcomes that range from operational disruption to full device compromise.
This article summarizes the technical findings, evaluates the real‑world risk to operators, explains practical detection and mitigation steps, and assesses longer‑term lessons for administrators responsible for refrigeration and HVAC supervisory networks.
What was disclosed (quick technical summary)
- AffectD PRO, XWEB 500D PRO, XWEB 500B PRO running firmware versions <= 1.12.1**.
- Nature of defects: a mix of authentication bypass, improper input neutralization (XSS/OS command injection), path traversal, stack‑based buffer overflows, and **use of weak or broken cryptographic aler both web‑UI logic flaws and underlying input‑parsing routines.
- Scope of tracked CVEs: multiple identifiers were assigned (the advisory lists more than twenty CVEs, e.g., CVE‑2026‑25085, CVE‑2026‑21718, CVE‑2026‑24663 and others), reflecting a clusteng defects rather than a single design flaw.
- Impact vectors: unauthenticated HTTP requests or specially crafted web payloads can be used to perform account takeover, upload or invoke files outside of intended directories, trigger memory overflows, and in some cases achieve remote code execution — all of which are classic web‑interface ainst embedded devices.
Why this matters: risk to facilities and cold‑chain operations
The XWEB family sits at an operationally sensitive junction: it provides remote visibility and control for refrigeration systems that directly affect temperature‑sensitive goods and building climate control. Successful exploitation can therefore lead to:- Operational disruption: manipulated setpoints, disabled alarms, or forced service modes can spoil inventory in cold‑chain systems or cause HVAC failures in commercial sites.
- Safety and compliance consequences: food‑safety regulations and pharmaceutical cold‑chain standards depend on trustworthy telemetry and alarms; tampering can trigger regulatory and liability exposure.
- Access pivoting and lateral movement: once a web supervisor is compromised, attackers often use it as a beachhead to access maintenance laptops, vendor VPNs, or connected control networks.
- Ransom and extortion vectors: industrial operator downtime and food‑spoilage are lucrative leverage points for extortion‑driven attackers.
The vulnerabilities in detail (technical breakdown)
Authentication and default‑credential weaknesses
Some of the reported flaws allow attackers to bypass authentication or exploit predictable/default credential generation. Embedded devices frequently use convenience features (temporary or time‑based “one‑day” admin tokens, or vendor provisioning passwords) that can become when combined with network exposure. The advisory cites authentication bypass as a primary failure mode that can grant administrative control without valid credentials.Input‑handling and command injection
Improper neutralization of special elements in OS commands (OS command injection) and unsafe web‑page input handling (XSS, unsanitized parameters sent to system calls) are reported. These weakns to pass crafted payloads that the device will execute on the underlying OS or use to write web shells and arbitrary files into served directories.Path traversal and file‑overwrite
Path‑traversal defects allow attackers to traverse out of the intended webroot and read or overwrdded context, this may disclose authentication secrets, configuration files, or upload code that the web server later executes.Memory corruption and buffer overflows
Several CVEs reported involve stack‑based buffer overflows and other memory corruption conditions. These are the technical class most likely tocode execution when exploited with carefully crafted inputs and can also cause crashes and persistent DoS.Cryptography weaknesses
Use of weak/broken cryptographic algorithms and poor randomization in credential handling are listed. Weak crypto magnifies the risk from interceential replay attacks, especially when devices are reachable over untrusted networks.Vendor posture and independent corroboration
Copeland maintains a product portal for XWEB documentation, firmware downloads, and release notes — evidence that patches and version tracking are available through vendor channels. Copeland’s documentation cites XWEB PRO software versions and notes password security policy changes in recent releases. That vendor material is an important place for operators to check firmware bulletins and updated installation guidance.Independent reporting by trade and security press has previously covered security findings in Copeland devices and related Dixell products, including high‑severity clusters that required firmware updates. Those past disclosures show both the industry impact of Copeland device flaws and that large installed bases exist across commercial refrigeration. This corroborates the advisory’s warning that XWEB deployments are globally distributed and materially significant to commercial facilities.
Immediate mitigation checklist (operational triage)
Treat these steps as thtions for any environment using affected XWEB PRO models.- Inventory and isolate
- Identify every XWEB device model and firmware version on the network. Focus on the XWEB 300D PRO, XWEB 500D PRO and XWEB 500B PRO units first.
- Segregate supervisory web interfaces from the internet and from general business networks using firewalls, VLANs, and access control lists.
- Block external exposure
- Ensure XWEB web interfaces and management ports are not reachable from the internet. If they are, block access immediately or apply a deny‑by‑default policy at the edge.
- Restrict remote access
- If remote access is needed for vendors or technicians, require a hardened jump host or an MFA‑protected VPN with host posture checks. Avoid exposing device web UIs directly to remote staff.
- Apply vendor updates where available
- Check Copeland’s update portal and apply firmware updates recommended by the vendor as soon as operational windows permit. The vendor site lists XWEB PRO software updates and related release notes.
- Compensating controls where patching is delayed
- Disable unused web services, restrict management to specific IP ranges, enable strong admin passwords, and remove or disable any documented temporary/default accounts.
- Detection and logging
- Enable detailed logging on perimeter devices and centralize logs. Hunt for suspicious POST requests, unusual file writes, directory traversal patterns (../ sequences), and requests to administrative CGI endpoints.
- Prepare for incident response
- If compromise is suspected, collect full device images, preserve logs, disconnect the device from networks after documenting activity, and follow your organization’s IR plan.
Detection and forensic indicators to hunt for
- Unusual or repeated HTTP requests containing encoded traversal strings (../) or command separators.
- Requests hitting CGI endpoints, upload handlers, or diagnostic pages that are not used in normal operations.
- Sudden configuration changes or new user accounts created on XWEB devices.
- Outbound connections from the XWEB device to unexpected hosts (a possible sign of a webshell or beacon).
- Abnormal CPU/memory spikes, reboots, or crashes coincident with web traffic spikes (could indicate buffer overflow exploitation or DoS attempts).
Patch management and operational constraints
Patching embedded supervisory devices can be operationally disruptive. Many XWEB deployments are in critical cooling paths where a device reboot is nontrivial and requires coordination with facilities teams. Follow a staged approach:- Validate updates in a lab or test device when available.
- Schedule maintenance windows with engineering teams and affected business stakeholders.
- If a vendor patch requires configuration changes (for example, replacement or removal of temporary credentials), test those changes for operational side effects.
- Keep a rollback plan and current backups of device configurations.
Threat model and exploitation likelihood
While CISA’s advisory lists high‑impact attack paths, exploitation likelihood depends on exposure and operational hygiene:- High risk: internet‑facing or poorly segmented XWEB instances with default or weak access controls. These are likely to be trivial targets for opportunistic scanning and remote exploitation.
- Medium risk: internal network devices reachable from business networks that lack strict segmentation and monitoring.
- Lower risk: air‑gapped or well‑segmented supervisory systems accessed only via hardened jump hosts and MFA‑protected vendor channels.
What administrators should communicate internally
- Notify facilities, procurement, and operations that XWEB supervisory units are considered high‑priority for patching and segmentation.
- Prioritize affected models in change windows and make contingency plans for manual control in the event of a patch outage.
- Engage vendors (Copeland) and service providers to confirm update availability and to request installation guidance, especially in environments where redundancy or failover may be required.
Long‑term security recommendations
- Eliminate direct internet exposure for industrial device management interfaces. Use jump hosts, Bastion servers, or remote access appliances that provide MFA, host posture checks, and granular session logging.
- Harden embedded devices at provisioning time: set unique strong passwords, disable default accounts, remove temporary or developer backdoors, and enable secure protocols only (disable weak crypto and plaintext admin channels).
- Inventory operational technology (OT) endpoints and maintain a prioritized patch program that balances operational risk and security risk.
- Monitor upstream vendor security channels ar advisories to ensure prompt notification of new firmware releases and guidance. Copeland’s software update and product document pages are the primary vendor channels for XWEB updates. m](https://webapps.copeland.com/Dixell/Pages/SystemSoftwareUpdate?utm_source=openai))
Critical assessment: strengths and gaps in the disclosure and vendor response
Strengths- The advisory provides a comprehensive list of CVEs and explicit affected models and versions, which helps operators rapidly identify impacted assets.
- It reiterates well‑established ICS security best practices (isolate, patch, minimize exposure), giving practical, actionable guidance for administrators who must quickly triage risk.
- Vendor documentation that maintains a software update portal and release notes is an asset for controlled patching and recovery planning.
- Embedded device patching can be slow avisory’s effectiveness depends on timely vendor updates and operational willingness to schedule reboots in production cooling paths. The vendor portal lists updates but operational constraints may still delay adoption.
- If any of the vulnerabilities have public exploit code or web‑scanners adapted to detect the specific CVEs, the window for mass exploitation could close quickly; the advisory notes there were no known public exploits at the time of publication, but that status can change. Treat the absence of observed exploitation as temporary and act urgently.
- The advis hardening and network isolation, but organizations with poor asset inventory and weak monitoring will struggle to apply the guidance quickly—this remains an enduring challenge highlighted by prior incidents in refrigeration and HVAC environments. Independent reporting underscores that Copeland/Dixell ecosystems have had multiple high‑severity issues in recent years, so maintain increased vigilance.
Final recommendations (practical prioritized roadmap)
- Immediate (hours)
- Block public access to XWEB management ports.
- Identify and document all XWEB devices and firmware versions on the network.
- Short term (1–7 days)
- Deploy compensating controls: ACLs, firewall rules, and vendor VPNs with strict host validation.
- Increase logging and begin targeted hunts for the IOCs described above.
- Medium term (1–4 weeks)
- Schedule vendor‑recommended firmware upgrades in controlled maintenance windows.
- Validate patches in a test environment and update emergency rollback playbooks.
- Long term (quarterly to ongoing)
- Replace devices that are end‑of‑life or cannot be patched in a timely fashion.
- Integrate OT/ICS devices into the enterprise vulnerability and inventory program and run regular external scans for exposed management interfaces.
Copeland’s XWEB advisory is a potent reminder that web‑facing supervisory interfaces in critical commercial systems are attractive targets with real operational impact. The combination of authentication logic flaws, path traversal, command injection, and memory corruption defects creates a strong attack surface when these devices are reachable from untrusted networks. Administrators must act quickly to inventory, isolate, and patch affected XWEB PRO units while strengthening network segmentation and remote access controls to reduce the risk of disruption to refrigeration and HVAC operations.
Conclusion: treat XWEB devices as high‑priority assets for immediate remediation — block internet exposure, harden access, and apply vendor updates as soon as they can be safely validated in your environment. The operational stakes are real, and the time to act is now.
Source: CISA Copeland XWEB and XWEB Pro | CISA