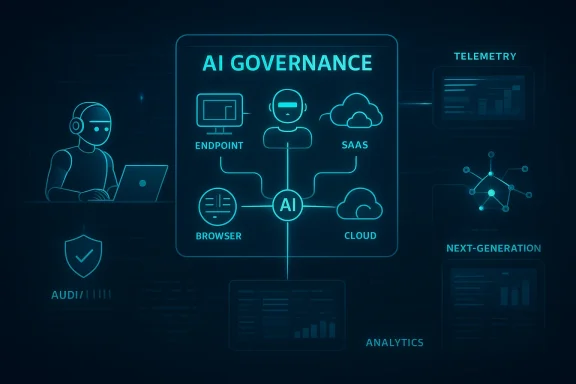
CrowdStrike’s latest platform update is more than a routine feature refresh: it is a clear sign that the company sees the next security battleground as the intersection of AI governance and security operations modernization. The new Falcon AI protections are built around the idea that the endpoint is now where AI behavior can be observed, constrained, and audited, while the expanded Falcon Next-Gen SIEM push aims to make mixed-vendor SOC environments easier to run. That combination matters because enterprises are no longer just asking how to stop malware; they are asking how to govern AI agents, watch them in real time, and keep legacy security stacks from becoming a drag on response speed. CrowdStrike’s own messaging around Falcon Shield and Falcon Next-Gen SIEM shows that it has been moving in this direction for months, with AI agent visibility, SaaS telemetry, and SIEM integration increasingly presented as one connected platform story. been converging on two urgent themes all year: AI adoption is spreading faster than governance, and SOC teams are still trying to escape the cost and complexity of older SIEM architectures. CrowdStrike’s newest announcements sit directly at that intersection. Its pitch is that AI agents should be treated as first-class enterprise assets, and that their actions should be monitored from the endpoint outward across SaaS, browser, and cloud layers. That framing reflects a broader market shift away from purely preventive controls and toward continuous visibility, policy enforcement, and behavior analysis. ready been building the pieces of this stike announced Falcon Shield capabilities for AI agent visibility across SaaS, including support for OpenAI ChatGPT Enterprise and Codex, plus broader governance for AI agent identities and permissions. It also described Falcon Next-Gen SIEM as a platform for ingesting first-party and third-party telemetry into a more flexible security analytics layer. Those earlier moves matter because the new announcement is not starting from scratch; it is extending a strategy that has been unfolding across identity, SaaS, cloud, and SIEM. dis also consistent with the company’s long-standing positioning around its Falcon plstraightforward: if AI agents can take actions that look like ordinary user behavior, then the endpoint becomes one of the most useful places to observe those actions in context. That is especially relevant as attackers increasingly try to compromise or misuse AI systems themselves. The company’s threat narrative now leans heavily on the idea that malicious activity may hide inside legitimate-looking AI workflows, which makes runtime monitoring more important than static policy alone.
At the same time, the SIEM side of i has been pushing Falcon Next-Gen SIEM as a way to modernize security operations without forcing a rip-and-replace migration. The new Microsoft Defender for Endpoint telemetry support fits that approach: it offers a way for organizations already invested in Microsoft endpoint security to use CrowdStrike’s SOC tooling without adding another endpoint agent. That is a commercially smart move, because it lowers friction for mixed estates and gives CrowdStrike a better chance of becoming the visibility and analytics layer rather than just another point product.
The release’s emphasis on AI agent discovery, governance, and runtime protection across multiple surfactlonger know where AI begins and ends. Employees are using desktop tools like ChatGPT, Gemini, Claude, DeepSeek, Microsoft Copilot, O365 Copilot, GitHub Copilot, and Cursor, while AI-enabled workflows are also showing up inside SaaS and cloud services. CrowdStrike’s approach suggests that the old boundary between “endpoint security” and “cloud security” is too narrow for the agentic era.
Key implications include:
The company’s visibility story extends beyond desktop apps into SaaS and cloud. It says it can discover AI agent usage and permissions in platforms including Microsoft Copilot iesforce Agentforce, ChatGPT Enterprise, OpenAI Enterprise GPT, and Nexos.ai. That breadth is strategically important because it lets CrowdStrike position itself as the common control layer across many different AI ecosystems rather than a vendor locked to one model provider or one productivity stack.
The runtime angle is equally significant. CrowdStrike is not only cataloging AI tools; it is also talking about prompt-layer protections and behavioral monitoring. That suggests the company recogniAI security, visibility without enforcement quickly turns into a dashboard with no teeth. By pushing into monitoring and control, CrowdStrike is trying to prove that AI security can be operationalized rather than merely observed.
It also reflects a broader market shift toward open architecture and data-agnostic security operations. Crowdlt it wants Falcon Next-Gen SIEM to work across a wide ranes, and Microsoft is simply the most visible example because of Defender’s scale. The integration reinforces the idea that the winner in SIEM may not be the vendor with the tightest lock-in, but the one that can unify the most valuable signals with the least friction.
Important takeaways:
That is important because SIEM replacement is often stalled by economics as much as by technology. Even when a legacy platform is functionally weak, organizations hesitate if moving data will create new cost centers oes. By focusing on pipeline filtering, real-time routing, fexternal data access, CrowdStrike is trying to make migration feel less like a technical project and more like a financial optimization exercise.
This is also where CrowdStrike’s broader SIEM story becomes relevant. The company has been adding AI-driven UEBA, case management, identity security automation, and threat hunting across third-party data. st the latest proof point in a larger campaign to convince buyers that Falcon Next-Gen SIEM can sit aboastructure without demanding a full rebuild. That is a strong market position if CrowdStrike can keep the performance promises believable.
This helps explain why CrowdStrike is focusing so heavily on behavior monitoring and permissions mapping. If an AI agent is operating inside a SaaS app, browser, or cloud environment, the dangerous part is not necessarily the presence of the AI tool itself; it is what that tooit can cause downstream. In that sense, AI security collapses into a classic enterprise problem: who has access, what can they do, and how do we know when they are doing something unusual?
The practical implications are:
This is where the company’s cross-platform visibility becomes a competitive differentiator. Support for tools like Microsoft Copilot in Power Platform, Salesforce Agentforce, ChatGPT Enterprise, and OpenAI Enterprise GPT means CrowdStrike is trying to own the control plane for AI behavior, not jur of AI. That approach makes the product more useful in the real world, where most enterprises are mixing multiple AI services whether they planned to or not.
It also sets up a broader platform contest. If AI security becomes a governance problem across identity, endpoints, browsers, and cloud workloads, then the best products will be the ones that can correlate those domains rather than isolate them. CrowdStrike’s value proposition is that aces to see the chain. The question is whether that visibility can stay accurate and low-friction as AI usage accelerates.
The deeper logic here is that data economics have become a first-class buying criterion. Many organizations are tired of paying to ingest and retain huge volumes of low-value telemetry just in case it becomes useful later. CrowdStrike’s focus on filtering in the pipeline, correlating in real timewhere it already resides speaks directly to that frustration.
That makes the contest less about endpoint replacement and more about analytics gravity. If CrowdStrike can become the place where Microsoft telemetry, third-party signals, and AI-related behavioral data all come together, it may win the next phase of SOC transformation without needing a full-staThat is a more realistic route to adoption than the all-or-nothing pitch of the past.
There is also a notable emphasis on interoperability. CrowdStrike keeps describing ignostic, and compatible with external systems rather than insisting on a closed environment. That is an important message for enterprises that already have Microsoft-heavy estates, an adopt CrowdStrike incrementally rather than replace everything at once.
The opportunity is substantial:
The SIEM side should also resonate with enterprises trying to cut ingestion costs and simplify analyst workflows. Query translation, federated search, and pipeline optimization are not flashy features, but they can be the difference between a successful modernization project and a stalled one. InSOC teams are already overworked, reducing toil can be as valuable as adding a new detection type.
The bigger consumer lesson is that the line between browser, app, and workplace security is dissolving. When employees use AI tools embedded in desktop apps, SaaS platforms, or browser extensions, the behavior can no longer be treated as isolated experimentation. CrowdStrike’s release ke convenience on the surface may be a new exposure path underneath.
The market will also be watching how CrowdStrike’s AI controls compare with the broader ecosystem’s push toward agent governance, identity-first security, and data-layer enforcement. If enterprise AI continues moving into production at the current pace, security products will increasingly be judged on their ability to unders what agents do on behalf of the business. That is a profound shift, and it favors vendors that can combine visibility with enforcement across multiple layers.
Watch for:
Source: SecurityBrief UK https://securitybrief.co.uk/story/crowdstrike-adds-ai-security-tools-microsoft-siem-link/
At the same time, the SIEM side of i has been pushing Falcon Next-Gen SIEM as a way to modernize security operations without forcing a rip-and-replace migration. The new Microsoft Defender for Endpoint telemetry support fits that approach: it offers a way for organizations already invested in Microsoft endpoint security to use CrowdStrike’s SOC tooling without adding another endpoint agent. That is a commercially smart move, because it lowers friction for mixed estates and gives CrowdStrike a better chance of becoming the visibility and analytics layer rather than just another point product.
 Why the AI Security Piece M built around a simple but important premise: AI agents are not passive software. They can execute commands, access data, and trigger workflows wfers or service identities. That makes them different from traditional applications, and it means the security model has to account for behavior, context, and runtime decisions rather than just binaries or signatures. CrowdStrike’s latest threat framing argues that attackers are already treating AI agents as a new kind of insider threat, which is why governance, discovery, and runtime protection are being bundled together.
Why the AI Security Piece M built around a simple but important premise: AI agents are not passive software. They can execute commands, access data, and trigger workflows wfers or service identities. That makes them different from traditional applications, and it means the security model has to account for behavior, context, and runtime decisions rather than just binaries or signatures. CrowdStrike’s latest threat framing argues that attackers are already treating AI agents as a new kind of insider threat, which is why governance, discovery, and runtime protection are being bundled together.
Endpoint as the AI control point
The most interesting part of the comp ndpoint should be the control point for AI security. That is a nuanced claim. On one hand, endpoint controls are familiar to defenders and easy to operationalize at scale. On the other hand, AI usage has spilled well beyond the endpoint into browsers, SaaS apps, cloud services, and embedded copilots, so CrowdStrike is effectively trying to use the endpoint as the anchor for a much wider visibility model.The release’s emphasis on AI agent discovery, governance, and runtime protection across multiple surfactlonger know where AI begins and ends. Employees are using desktop tools like ChatGPT, Gemini, Claude, DeepSeek, Microsoft Copilot, O365 Copilot, GitHub Copilot, and Cursor, while AI-enabled workflows are also showing up inside SaaS and cloud services. CrowdStrike’s approach suggests that the old boundary between “endpoint security” and “cloud security” is too narrow for the agentic era.
Key implications include:
- AI tools are becoming part of ordinary user behavior.
- Security teams need visibility into prompt-layer activity, not just app iance must span endpoint, browser, SaaS, and cloud.
- Runtime monitoring matters because agent actions can resemble normal work.
- Shadow AI is now an inventory problem as much as a policy problem.
What CrowdStrike says it can see
CrowdStrike says its sensors are detecting more than 1,800 distinct AI applications across enterprise deviceapplication instances. Those figures are meant to show scale, but they also highlight how quickly AI has become a sprawling operational issue. Even if individual deployments are benign, the volume alone tells security leaders that ad hoc AI usage is no longer marginal; it is a mainstream management problem.The company’s visibility story extends beyond desktop apps into SaaS and cloud. It says it can discover AI agent usage and permissions in platforms including Microsoft Copilot iesforce Agentforce, ChatGPT Enterprise, OpenAI Enterprise GPT, and Nexos.ai. That breadth is strategically important because it lets CrowdStrike position itself as the common control layer across many different AI ecosystems rather than a vendor locked to one model provider or one productivity stack.
The runtime angle is equally significant. CrowdStrike is not only cataloging AI tools; it is also talking about prompt-layer protections and behavioral monitoring. That suggests the company recogniAI security, visibility without enforcement quickly turns into a dashboard with no teeth. By pushing into monitoring and control, CrowdStrike is trying to prove that AI security can be operationalized rather than merely observed.
The Microsoft Defender for Endpoint Link
The Microsoft telemetry integration is arguably the most commercially shrewd part of the announcement. Falcon Next-Gen SIEM can now ingest and correlate data from Micrdpoint without requiring CrowdStrike’s Falcon sensor on those devices. That matters because many enterprises already rely on Defender at the endpoint but still want a more modern SIEM and SOC workflow layer. CrowdStrike is meeting those customers where they already are, which lowers switching costs and opens a path into organizations that might otherwise hesitate to deploy another endpoint agent.Why sensorless ingestion matters
From an enterprise architecture standpoint, sensorless ingestion is a practical compromise. It allows organizations to keep their current endpoint stack whiloand correlation layer. That is particularly useful for large hybrid environments, where standardizing every endpoint on one vendor is often unrealistic, politically difficult, or both.It also reflects a broader market shift toward open architecture and data-agnostic security operations. Crowdlt it wants Falcon Next-Gen SIEM to work across a wide ranes, and Microsoft is simply the most visible example because of Defender’s scale. The integration reinforces the idea that the winner in SIEM may not be the vendor with the tightest lock-in, but the one that can unify the most valuable signals with the least friction.
Important takeaways:
- Customers can keep Microsoft Defender for Endpoint on devices.
- CrowdStrtry into Falcon Next-Gen SIEM.
- SOC teams can modernize without a full endpoivcome easier to support.
- The integration strengthens CrowdStrike’s open-platform narrative.
The business case beneath the partnership
CrowdStrike’s message is not just technical; it is also economic. The company says its Onum integration can provide faster streaming, lower storage costs, faster incidentngestion overhead. Whether every customer sees the same numbers will vary, but the strategic argument is clear: the oleata sprawl, and CrowdStrike wants to reduce all three.That is important because SIEM replacement is often stalled by economics as much as by technology. Even when a legacy platform is functionally weak, organizations hesitate if moving data will create new cost centers oes. By focusing on pipeline filtering, real-time routing, fexternal data access, CrowdStrike is trying to make migration feel less like a technical project and more like a financial optimization exercise.
This is also where CrowdStrike’s broader SIEM story becomes relevant. The company has been adding AI-driven UEBA, case management, identity security automation, and threat hunting across third-party data. st the latest proof point in a larger campaign to convince buyers that Falcon Next-Gen SIEM can sit aboastructure without demanding a full rebuild. That is a strong market position if CrowdStrike can keep the performance promises believable.
AI Agents as the New Attack Surface
One of the clearest signals in CrowdStrike’s release is the company’s belief that AI agents are no longer experimental assistants. They are becoming active partsans they can be manipulated, abused, or turned against the organization. CrowdStrike’s threat logic is that attackers will increasingly target the agent itself, not just the app or platform behind it. That is a subtle but important change in how enterprises should think about risk.Malicious insiders, but synthetic
The company’s threat report and product messaging both point toward the same conclusion: compromised AI agents can behave like malicious insiders. That does not mean they are human-like in intent,ecan create the same kinds of damage that insider abuse usually causes. Access to sensitive information, permission to trigger workflows, and ability to move across connected systems all become security concerns once the agent is trusted to act on behalf of the business.This helps explain why CrowdStrike is focusing so heavily on behavior monitoring and permissions mapping. If an AI agent is operating inside a SaaS app, browser, or cloud environment, the dangerous part is not necessarily the presence of the AI tool itself; it is what that tooit can cause downstream. In that sense, AI security collapses into a classic enterprise problem: who has access, what can they do, and how do we know when they are doing something unusual?
The practical implications are:
- AI agents need identity-aware controls.
- Permissions should be reviewed like any other privileged workload.
- Behavioral baselines must include non-human activity.
- Audit trails need to capture agent actions, not just user actionsed at the workflow layer.
Browser, SaaS, and cloud all matter
CrowdStrike’s coverage across browsers, SaaS, and cloud suggests a recognition that AI usage is fragmented by design. People may start a task in a desktop chatbot, move it into a browser extension, and then connect it to a cl. Security teams need to follow that chain end to end if they want meaningful control.This is where the company’s cross-platform visibility becomes a competitive differentiator. Support for tools like Microsoft Copilot in Power Platform, Salesforce Agentforce, ChatGPT Enterprise, and OpenAI Enterprise GPT means CrowdStrike is trying to own the control plane for AI behavior, not jur of AI. That approach makes the product more useful in the real world, where most enterprises are mixing multiple AI services whether they planned to or not.
It also sets up a broader platform contest. If AI security becomes a governance problem across identity, endpoints, browsers, and cloud workloads, then the best products will be the ones that can correlate those domains rather than isolate them. CrowdStrike’s value proposition is that aces to see the chain. The question is whether that visibility can stay accurate and low-friction as AI usage accelerates.
SIEM Modernization Under Pressure
The SIEM market has been stuck in a familiar loop for years: too much data, too much cost, too much tuning, and too many analysts stuck hunting across disconnected systems. CrowdStrike’s latest message is that Falcon Next-Gen SIEM is designedngestion pain and making third-party data more usable. The Microsoft Defender integration strengthens that case because it proves the platform can ingest high-value telemetry even when CrowdStrike does not own the endpoint.The migration story matters
CrowdStrike is also adding features meant to make migration from legacy SIEM products less painful. Those include native Falcon Onum data pipelines, federated search across third-party stores, third-party threat intelligence integration, and ger SIEM searches into CrowdStrike Query Language. That is not just a usability feature; it is a migration strategy. It reduces the skill gap and lowers the barrier to trying Falcon Next-Gen SIEM as a replacement or parallel platform.The deeper logic here is that data economics have become a first-class buying criterion. Many organizations are tired of paying to ingest and retain huge volumes of low-value telemetry just in case it becomes useful later. CrowdStrike’s focus on filtering in the pipeline, correlating in real timewhere it already resides speaks directly to that frustration.
What this means for competitors
This is a direct challenge to legacy SIEM vendors, but it also puts pressure on platform rivals with strong SOC stories of their own. If CrowdStrike can demonstrate that it reduces storage overhead while preserving fidelity, then the company has a nk SIEM modernization is too expensive to justify. The Microsoft integration is especially helpful here becaeons: “We already use Defender, so why move?” CrowdStrike’s answer is now, effectively, “You do not have to move everything.”That makes the contest less about endpoint replacement and more about analytics gravity. If CrowdStrike can become the place where Microsoft telemetry, third-party signals, and AI-related behavioral data all come together, it may win the next phase of SOC transformation without needing a full-staThat is a more realistic route to adoption than the all-or-nothing pitch of the past.
CrowdStrike’s Platform Strategy
Case should be read as part of a broader platform consolidation strategy. The company is trying to connect AI security, identity, endpoint protection, cloud visibility, SaaS governance, and next-gen SIEM into one operational because security teams increasingly want fewer tools that understand more of the environment. It is also risky, because the more responsibilities a platform accumulates, the more it must prove it can do each of them well.One platform, many control points
What stands out is the consistency of CrowdStrike’s architecture language. Whether it is Falcon Shield, Falcon Next-Gen SIEM, or the new AI behavior protections, the company is pushing the same idea: **use one telemetry-rich platform to secure mul. That is a familiar pitch in cybersecurity, but it becomes more compelling when the platform can demonstrate useful joins between endpoints, SaaS identities, cloud workloads, and SIEM data.There is also a notable emphasis on interoperability. CrowdStrike keeps describing ignostic, and compatible with external systems rather than insisting on a closed environment. That is an important message for enterprises that already have Microsoft-heavy estates, an adopt CrowdStrike incrementally rather than replace everything at once.
Why this is happening now
The timing is not accidental. CrowdStrike’s own materials show that it has been moving aggressively through 2025 and into 2026 on AI agent visibility, AI detection and response, and SIEM transformation. The latest release simply ties those threads togethestomers to buy. In a market where AI governance and SOC modernization are happening simultaneously, that kind of packaging matters almost as much as the underlying technology.The opportunity is substantial:
- Security teams want fewer consoles and fewer agents.
- AI governance needs the same data fabric as SOC operations.
- Microsoft-heavy environments need integration, not ideology.
- Buyers value cost reduction as much as detection quality.
- vantage.
Enterprise vs Consumer Impact
For enterprise buyers, this release is mainly about governance, operational efficiency, and risk reduction. The most immediate value sits in mixed environments where AI adoption is already underway but policy maturity is lagging. Companies with Miultiple AI tools in circulation, and a growing appetite for SIEM modernization are likely to see the strongest fit.Enterprise priorities
Enterprises will care about visibility into AI app usage, permissions, and runtime behavior, but they will care just as much about deployment friction. If CrowdStrike can deliver control without demanding a full endpoint overhaul, it may appeal to security leify major infrastructure changes. That matters especially for large organizations with global estates, multiple business units, and uneven standardization.The SIEM side should also resonate with enterprises trying to cut ingestion costs and simplify analyst workflows. Query translation, federated search, and pipeline optimization are not flashy features, but they can be the difference between a successful modernization project and a stalled one. InSOC teams are already overworked, reducing toil can be as valuable as adding a new detection type.
Consumer ripple effects
For consumers, the impact is more indirect but still important. As enterprises tighten AI controls, employees are likely to encounter more friction when they move between public AI tools and work systems. That may feel restrictive, but it also reflects a bgoverned business capability, not just a personal productivity shortcut.The bigger consumer lesson is that the line between browser, app, and workplace security is dissolving. When employees use AI tools embedded in desktop apps, SaaS platforms, or browser extensions, the behavior can no longer be treated as isolated experimentation. CrowdStrike’s release ke convenience on the surface may be a new exposure path underneath.
Strengths and Opportunities
CrowdStrike’s announcement has several clear strengths. It ties together two of the hottest enterprise security themes of 2026: AI governance and SIEM modernization. It also offers a credible answer to mixed-environment customers who want to keep Microsoft endpoint toolin visibility and reducing operational drag.- Strong alignment with current enterprise demand for AI controls.
- Practical support for Microsoft Defender for Endpoint environments.
- Broader visibility across endpoint, SaaS, browser, and cloud.
- A credible story for reducing SIEM ingestion and storage costs.
- Useful migration aids such as query t
- Better fit for heterogeneous estates than closed-stack approaches.
- Clear platform narrative that connects discovery, governance, and response.
Risks and Concerns
The main risk is overextension. CrowdStrike is trying to be the security layer for endpoints, AI agents, SaaS, browsers, cloud, and SIEM all at once. That is strategically attractive, but it also raises expectations that every layer will perform consistently under enterprise coin feels noisy, expensive, or hard to tune, the platform story weakens quickly.- AI application counts may be impressive but still hard to operationalize.
- Runtime monitoring can create alert fatigue if not tuned carefully.
- Sensorless SIEM ingestion may not satisfy every architecture team.
- Broad platform scope can make procurement and deployment more complex.
- Microsoft integalso raises dependency questions.
- SIEM cost savings claims will be scrutinized closely by buyers.
- Competing platforms may offer tighter native integration in some estates.
Looking Ahead
The next phase of this story will likely be defined by adoption quality rather than announcement volume. CrowdStrike has now shown that it can connect AI security, Microsoft telemetry, and next-gen SIEM into one narrative. What matters next is whether customers can actually deploy those capabilities without addinl overhead or creating new blind spots.The market will also be watching how CrowdStrike’s AI controls compare with the broader ecosystem’s push toward agent governance, identity-first security, and data-layer enforcement. If enterprise AI continues moving into production at the current pace, security products will increasingly be judged on their ability to unders what agents do on behalf of the business. That is a profound shift, and it favors vendors that can combine visibility with enforcement across multiple layers.
Watch for:
- Customer adoption of Microsoft Defender telemetry into Falcon Next-Gen SIEM.
- Evidence that CrowdStrike can reduce ingestion and storage costs at scale.
- Expanded support for additional AI platforms and agent frameworks.
- Deeper runtime enforcement beyond discovery and monitoring.
- Competitive responses from platform providers.
Source: SecurityBrief UK https://securitybrief.co.uk/story/crowdstrike-adds-ai-security-tools-microsoft-siem-link/