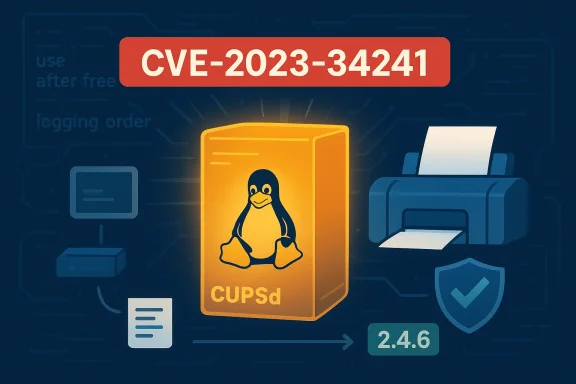
A subtle ordering mistake in CUPS’ connection-handling code quietly opened a wide door for disruption: a use‑after‑free in the cupsdAcceptClient() path (tracked as CVE‑2023‑34241) can crash the printing daemon and, under some conditions, expose sensitive in‑process data — a practical denial‑of‑service and potential confidentiality risk for any system running vulnerable builds of the Common UNIX Printing System.
CUPS (the Common UNIX Printing System) is the de facto print spooler on most Linux and many Unix‑like operating systems and has long been embedded into desktop distributions, appliances and some vendor firmware. The vulnerability assigned CVE‑2023‑34241 was disclosed in June 2023 and targets a use‑after‑free (UAF) in the connection acceptance logic inside cupsd, the central CUPS daemon.
At a high level the defect is straightforward: CUPS calls a function that closes (and thereby frees) an HTTP connection object, then — under certain logging and configuration conditions — attempts to read fields from that now‑freed object while creating a client log entry. That classic use‑after‑free sequence can produce memory corruption. In practice, the two most immediate and realistic effects are:
Because multiple third‑party trackers and exploit aggregators report public PoCs and because the crash path is relatively simple to reproduce with controlled connection attempts, operators should assume exploit code could be available or easily developed and prioritize fixes.
Given the relative simplicity of the triggering conditions and public reporting of proof‑of‑concepts, the correct operational posture is urgent patching, swift network isolation for unpatched services, and careful verification that the update has propagated to all software images and embedded devices under your control.
Administrators should stop treating print services as low‑value targets. A widely deployed daemon like cupsd is an attractive denial‑of‑service target and a potential conduit to confidential data when memory safety is breached. Patch, restrict, monitor and verify — in that order.
Conclusion
CVE‑2023‑34241 is a potent reminder that small mistakes in resource handling can have outsized operational impact when they touch daemon code that accepts network connections and runs with elevated privileges. The fix is available; the operational cost of delay is avoidable. Prioritize inventory and patching, harden network exposure to printing services, and treat logging‑related code paths with the same scrutiny you apply to authentication and input‑validation routines.
Source: MSRC Security Update Guide - Microsoft Security Response Center
 Background / Overview
Background / Overview
CUPS (the Common UNIX Printing System) is the de facto print spooler on most Linux and many Unix‑like operating systems and has long been embedded into desktop distributions, appliances and some vendor firmware. The vulnerability assigned CVE‑2023‑34241 was disclosed in June 2023 and targets a use‑after‑free (UAF) in the connection acceptance logic inside cupsd, the central CUPS daemon.At a high level the defect is straightforward: CUPS calls a function that closes (and thereby frees) an HTTP connection object, then — under certain logging and configuration conditions — attempts to read fields from that now‑freed object while creating a client log entry. That classic use‑after‑free sequence can produce memory corruption. In practice, the two most immediate and realistic effects are:
- Denial‑of‑service (DoS): an attacker can trigger crashes of the cupsd process, causing sustained loss of printing service availability until the service is restarted or the host is patched.
- Information exposure risk: because the bug causes cupsd to read memory that should have been reclaimed, there is a plausible—but less commonly demonstrated—risk that privileged in‑process data (for example, keys or transient secrets held by the daemon) could be leaked.
What exactly goes wrong: a technical breakdown
The vulnerable sequence
The underlying issue stems from the ordering of operations inside scheduler/client.c’s cupsdAcceptClient() path. A simplified description of the sequence is:- A new client connection is accepted by cupsd.
- Under some connection outcomes (failed hostname lookups, TCP wrapper rejections, or specific logging modes), cupsd calls a function that closes the HTTP connection — a call which frees memory owned by the connection object.
- Immediately afterward, cupsd attempts to log client information and calls functions that dereference fields of the already‑freed connection object.
When the bug is reachable
The code path is not unconditional: maintainers and vendor advisories identified two common triggers that make the problem reachable in practice:- Logging level settings: when LogLevel is set to warn or higher, the daemon executes the logging path that attempts to use the connection pointer after closing it.
- Network / name resolution and host access checks: the bug appears when there is a double IP address lookup (HostNameLookups Double) that fails, or when CUPS is compiled with TCP wrappers and the connection is refused by entries in /etc/hosts.allow or /etc/hosts.deny.
Scope: affected versions and platforms
- Affected CUPS versions: all releases from 2.0.0 up to and including 2.4.5. The upstream patch that fixes the problem first appears in the 2.4.6 release.
- Affected platforms: any system running a vulnerable CUPS build — desktop Linux distributions, many TTL prints servers, some router/NAS firmware images, and some macOS builds that include the affected CUPS codebase prior to vendor fixes.
- Vendor patches: major distributions and vendors released updates after disclosure. If you run Debian, Ubuntu, Fedora, Red Hat family distributions, Amazon Linux, or macOS, consult your platform's update channels and apply the CUPS‑related security updates.
Impact assessment: denial of service vs. confidentiality risk
Security trackers and vendor advisories converge on two principal impacts: availability and memory corruption. How these translate into operational risk depends on deployment.- Availability (most immediate concern): an attacker able to connect to a vulnerable CUPS listener can repeatedly trigger the problematic code path and crash cupsd. For services that expose printing to broad networks (or are reachable from untrusted subnets), this can produce sustained loss of availability while the attack continues, and persistent unavailability if reboots or service restarts are inhibited or uncoordinated in the environment. Microsoft’s vulnerability classification language — which emphasizes total loss of availability where applicable — reflects this operational severity for affected components.
- Confidentiality (plausible but contextual): because the defect is a use‑after‑free, memory contents that should have been protected may be read. In theory, an attacker could influence heap contents or cause the daemon to copy out memory that contains secrets. In practice, confirmed, reliable data exfiltration through this CVE has not been the widespread public story; however, several vendor advisories explicitly list possible exposure of sensitive data — including private keys held by the cups daemon — as a risk. This uncertainty argues for treating the vulnerability conservatively.
Timeline and vendor response
- Disclosure: June 2023 (the defect was publicly described and assigned CVE‑2023‑34241).
- Upstream fix: committed and released in CUPS 2.4.6 (the maintainers corrected the logging/close ordering so the connection is not freed before being logged).
- Downstream fixes: major Linux distributions and other vendors released security updates or backported patches to their package builds shortly afterward. macOS vendor advisories and platform updates that include the CUPS fix also appeared for Apple‑supplied builds.
Conflicting scores and exploitability notes — read this carefully
Different databases assigned different CVSS base scores and impact breakdowns for CVE‑2023‑34241. The variance stems from differing assumptions about the scope of impact (local vs. network), whether confidentiality is meaningfully impacted in typical deployments, and how easily an unauthenticated remote actor can trigger the specific conditions.- Some aggregators and vendor assessments placed the CVSS in the high‑severity band (CVSS 7.x), treating confidentiality exposure as a realistic outcome for privileged daemons.
- Others (including some NVD/Amazon Linux metadata) assigned a lower base score (CVSS 5.3) focused primarily on availability impact.
Exploits and proof‑of‑concepts
At disclosure time, public advisories did not present a widespread, weaponized exploit that reliably achieves remote code execution; however, vulnerability trackers later indexed proof‑of‑concepts and scripts that reproduce the crash conditions. Public proof‑of‑concepts and exploit code, when present, materially raise the urgency for patching.Because multiple third‑party trackers and exploit aggregators report public PoCs and because the crash path is relatively simple to reproduce with controlled connection attempts, operators should assume exploit code could be available or easily developed and prioritize fixes.
Detection: how to tell if you're affected or being targeted
Use the following checks to quickly determine exposure and potential exploitation:- Identify the installed CUPS package and version:
- Debian/Ubuntu: sudo dpkg -l | grep cups
- Red Hat/Fedora: rpm -q cups
- Generic: cups-config --version
- On systems using packages, confirm the binary package version is 2.4.6 or greater (or that the vendor has provided an equivalent patched build).
- Check whether cupsd is listening on network interfaces:
- ss -ltnp | grep :631 or netstat -ltnp | grep :631
- If cupsd listens on 0.0.0.0:631 or an externally routed interface, the daemon is reachable.
- Review cups and system logs for unexpected restarts/crashes:
- journalctl -u cups --since "7 days ago"
- /var/log/cups/error_log (location may vary)
- Look for unusual log entries around connection handling, repeated crashes, or stack traces that include cupsd.
- Search for local changes or unexplained regens of private keys if you suspect exfiltration: check certificate files and timestamps, inspect configuration change logs, and validate system integrity with the vendor package manager.
Mitigation and remediation guidance (practical, prioritized)
Apply the following playbook as soon as feasible. The first two items are mandatory for exposed systems.- Patch (highest priority)
- Update CUPS to the vendor‑supplied security update or upgrade to CUPS 2.4.6 or later.
- Apply distribution security updates (apt, dnf, yum, zypper, etc.) rather than attempting local source patches unless you manage bespoke builds.
- For macOS, apply Apple’s security updates when they include CUPS fixes; if you manage Macs centrally, deploy the macOS security update via your management tooling.
- Restart and verify
- After patching, restart the cupsd process and validate the version.
- Confirm that post‑patch logs no longer show the previously observed crash signatures.
- Network isolation (temporary mitigation)
- If patching will be delayed, block external access to TCP/UDP port 631 (IPPS/IPP) at network boundaries and host firewalls.
- Restrict printing services to internal, trusted management networks only.
- On hosts that must accept remote print jobs, consider using an IP‑whitelist or VPN-only access for print submission.
- Configuration hardening (temporary, mitigative)
- Review cupsd.conf:
- Reduce LogLevel from warn or debug to a lower level that does not trigger the problematic logging path. Note: changing LogLevel is a temporary mitigation and not a fix — do not rely on it as the primary remediation.
- Disable HostNameLookups Double or remove aggressive DNS lookup behaviors that can create the double‑lookup scenario.
- If your CUPS build was compiled with TCP wrappers and you do not need that functionality, recompile without TCP wrappers or ensure /etc/hosts.allow and /etc/hosts.deny rules do not produce rejection responses that trigger the vulnerable path.
- Validate dependent systems and firmware
- Many embedded devices, print servers and appliances include components of the CUPS codebase. Check vendor advisories and firmware updates for printers, NAS appliances and router firmware that may bundle vulnerable CUPS components.
- Monitor and respond
- Increase monitoring of cupsd behavior and implement alerting for abnormal restarts or crashes.
- If you detect suspicious activity consistent with exploitation (persistent crashes, unknown key rotations, unexpected outbound connections), consider an incident response escalation: preserve memory dumps, save packet captures of suspicious sessions, and consult your SOC/IR team.
Practical administration examples (commands)
- Check CUPS version:
- cups-config --version
- dpkg -s cups | grep Version
- rpm -q cups
- Update on Debian/Ubuntu:
- sudo apt update
- sudo apt install --only-upgrade cups
- sudo systemctl restart cups
- Update on RHEL/Fedora:
- sudo dnf update cups
- sudo systemctl restart cups
- Temporarily block remote access on a host (example using ufw):
- sudo ufw deny in proto tcp to any port 631
- Inspect recent cupsd logs:
- sudo journalctl -u cups -n 200
- sudo tail -n 200 /var/log/cups/error_log
Incident response and forensic considerations
If you suspect a successful exploit or unexplained data exposure tied to cupsd:- Preserve evidence: do not reboot more than necessary; collect core dumps, memory snapshots, and the cups error log.
- Capture network traffic targeting port 631 for retrospective analysis.
- Compare key and certificate files against known good backups; if private keys used by cupsd could be exposed, rotate them and update dependent systems.
- If your environment mandates compliance reporting, document the affected hosts, the detection timeline, and the patch timeline.
- Conduct a root cause review to ensure updates are applied across all device classes — servers, desktops, embedded systems and vendor appliances.
Broader lessons: why logging order matters and supply‑chain risk
CVE‑2023‑34241 is a textbook example of how non‑spectacular code paths — logging and connection teardown — can become security vulnerabilities when resource lifetimes are mishandled. Several broader lessons emerge:- Resource lifetime discipline matters. Logging code that references objects after a close/free is a recurring source of memory safety defects. Defensive coding patterns should ensure that resources are validated before use and cleared / nulled after free.
- Low‑privilege components can expose privilege boundaries. A daemon that runs with elevated privileges (as cupsd often does) magnifies risk when an attacker can trigger its memory corruption.
- Supply chain and embedded risk. CUPS is embedded in many places beyond desktop Linux. A vulnerability in a ubiquitous open‑source component can persist in vendor firmware and older images long after upstream has released a fix — administrators must inventory devices and vendors.
- Configuration complexity can convert a benign function into an attack vector. Features like double hostname lookups or optional TCP wrappers altered the reachability of the bug; configuration surfaces should be evaluated for security implications.
Recommended checklist (actionable)
- Inventory: list every host and appliance that runs CUPS or includes CUPS-derived code.
- Patch: update to CUPS 2.4.6 or apply vendor patches immediately.
- Restrict: block or restrict access to port 631 from untrusted networks until patches are in place.
- Validate: restart cupsd, confirm patched version and absence of crash signatures.
- Monitor: add alerts for cupsd restarts/crashes, and watch for unusual log entries.
- Communicate: inform stakeholders — print server operators, helpdesk and security teams — of the vulnerability and the remediation plan.
- Verify vendor firmware: contact hardware vendors for appliances and networked printers to confirm whether a device contains patched CUPS code.
Final analysis and risk judgment
CVE‑2023‑34241 is not an exotic, remote full remote code execution (RCE) that immediately allows kernel takeover; it is, however, a practical, reproducible use‑after‑free in an often‑privileged daemon. That combination makes it operationally dangerous: it can be weaponized to repeatedly crash print services (a clear availability problem) and — under certain controlled or bespoke attack strategies — could be leveraged toward data leakage in memory.Given the relative simplicity of the triggering conditions and public reporting of proof‑of‑concepts, the correct operational posture is urgent patching, swift network isolation for unpatched services, and careful verification that the update has propagated to all software images and embedded devices under your control.
Administrators should stop treating print services as low‑value targets. A widely deployed daemon like cupsd is an attractive denial‑of‑service target and a potential conduit to confidential data when memory safety is breached. Patch, restrict, monitor and verify — in that order.
Conclusion
CVE‑2023‑34241 is a potent reminder that small mistakes in resource handling can have outsized operational impact when they touch daemon code that accepts network connections and runs with elevated privileges. The fix is available; the operational cost of delay is avoidable. Prioritize inventory and patching, harden network exposure to printing services, and treat logging‑related code paths with the same scrutiny you apply to authentication and input‑validation routines.
Source: MSRC Security Update Guide - Microsoft Security Response Center