The Linux kernel vulnerability tracked as CVE-2010-0291 — widely discussed at the time as the “do_mremap() mess” or the “mremap/mmap mess” — allowed an unprivileged local user to crash a system or, in some exploit scenarios, escalate to kernel privileges by abusing the kernel’s mmap/mremap logic in kernels prior to 2.6.32.4.
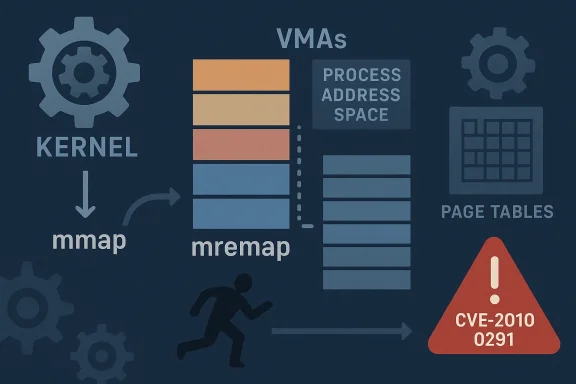
Memory management is central to an operating system’s security model. The Linux kernel exposes system calls such as mmap() and mremap() to let userland allocate, resize, or move virtual memory regions. Those calls must tightly enforce invariants about virtual memory areas (VMAs), page-table updates, and permission boundaries; a subtle mistake at this layer can convert normal user-space code into a vehicle for kernel crashes or privilege escalation.
CVE-2010-0291 was assigned after a coordinated set of upstream patches and public discussion in early 2010 that aimed to “untangle the do_mremap() mess” — a phrase used on kernel mailing lists to describe a complex collection of interdependent bugs and architecture-specific corner cases in the mmap/mremap code paths. The problem, in short, was that mmap/mremap logic could incorrectly manipulate VMAs and page-table entries under certain sequences of operations, leaving inconsistent mappings that could be exploited.
Gentoo and other distribution security advisories reported that proof-of-concept exploit code had been developed and used to escalate privileges on vulnerable systems, underlining that exploitation was not purely theoretical.
That said, the incident underscores perennial truths for system operators and kernel developers: memory-management code is high stakes, complexity multiplies risk, and only disciplined patch management and ongoing code-quality work will prevent similar vulnerabilities from becoming operational crises. Administrators responsible for legacy systems should verify that no host in their estate still runs an unpatched kernel from that era, and security teams should fold lessons from the do_mremap() mess into current auditing, fuzzing, and hardening efforts.
Source: MSRC Security Update Guide - Microsoft Security Response Center
 Background
Background
Memory management is central to an operating system’s security model. The Linux kernel exposes system calls such as mmap() and mremap() to let userland allocate, resize, or move virtual memory regions. Those calls must tightly enforce invariants about virtual memory areas (VMAs), page-table updates, and permission boundaries; a subtle mistake at this layer can convert normal user-space code into a vehicle for kernel crashes or privilege escalation.CVE-2010-0291 was assigned after a coordinated set of upstream patches and public discussion in early 2010 that aimed to “untangle the do_mremap() mess” — a phrase used on kernel mailing lists to describe a complex collection of interdependent bugs and architecture-specific corner cases in the mmap/mremap code paths. The problem, in short, was that mmap/mremap logic could incorrectly manipulate VMAs and page-table entries under certain sequences of operations, leaving inconsistent mappings that could be exploited.
Overview of the Vulnerability
What the CVE says
The CVE description is concise: the Linux kernel before 2.6.32.4 allows local users to gain privileges or cause a denial of service (panic) by calling either the mmap() or mremap() function. The vulnerability was cataloged and addressed across multiple vendor advisories and distribution security notices.The practical impact
- Denial of Service (DoS): A process could trigger a kernel panic or oops, taking the system down or leaving it unstable.
- Local Privilege Escalation (LPE): Under certain conditions, an attacker could craft sequences that resulted in arbitrary kernel memory being mapped with inappropriate permissions, potentially allowing code execution at kernel level. Evidence of proof-of-concept exploits and successful local escalations on vulnerable systems was reported by distribution advisories and security researchers at the time.
Technical anatomy: how mmap() and mremap() went wrong
mmap() and mremap(): the roadmaps of a memory region
At a high level:- mmap() creates or maps a new virtual memory area (VMA) in a process’s address space.
- mremap() moves or resizes an existing mapping; internally it may create, split, merge, or remove VMAs and must carefully copy or move page table entries (PTEs) and respect access permissions.
The core defects (high level)
The public analysis and vendor advisories coalesced around a few recurring root causes:- Missing or incorrect checks after internal unmap operations. If do_mremap() used do_munmap() internally but ignored or misinterpreted its return state, subsequent steps could proceed against an inconsistent mapping state. That could lead to page-table entries from one region being left mapped where another region’s protections applied.
- Address arithmetic and wraparound edge cases on 32-bit platforms. Some operations relied on arithmetic that could overflow in specific ranges, creating logic paths that incorrectly assumed PTE movement had completed. Contemporary and later fixes for related mremap bugs made explicit checks to avoid those wraparound mistakes.
- Complexity across architectures and the need for per-arch assembly fixes. The Linux kernel’s memory management code contains architecture-specific optimizations. Patches in late 2009 and early 2010 included architecture-level corrections as well as higher-level logic refactors described on mailing lists as an attempt to “untangle” the code. The result was a set of coordinated commits rather than a single trivial patch.
How this could become an LPE
The vulnerability chain typically relied on the kernel leaving page-table entries in place while the corresponding VMA metadata had changed, or on improperly applying page protections. Where the kernel erroneously allowed writable/executable page table entries to remain mapped into a VMA that otherwise should not permit such mappings, a carefully crafted user process could place shellcode at a user-controlled address and have it executed in a kernel context when execution crossed those corrupted mappings.Gentoo and other distribution security advisories reported that proof-of-concept exploit code had been developed and used to escalate privileges on vulnerable systems, underlining that exploitation was not purely theoretical.
Timeline and vendor response
Upstream fixes and kernel versions
The problem was addressed upstream through a set of commits that were incorporated into kernel trees and stabilized in subsequent releases. Distributors tracked the original vulnerability and released patched kernel packages well before the 2.6.32.4 baseline that the CVE references. Vendor advisories and distribution security notices record the fix as applied in their trees.Distribution advisories and vendor errata
- Red Hat documented the issue in errata and consolidated several mmap/mremap fixes as part of kernel updates; their advisory explicitly referenced CVE-2010-0291 as one of several important mmap/mremap flaws requiring immediate attention.
- Ubuntu, SUSE, and others listed CVE-2010-0291 in their security tracking pages and mapped affected kernel packages to patched versions for supported releases. Distributors often listed the upstream commit IDs and the package version that contained the fix.
- CERT / CISA and national CERTs included CVE-2010-0291 in vulnerability bulletins of February 2010, flagging it for administrators to patch due to the availability of proof-of-concept code.
Public discussion and disclosure
The “untangle the do_mremap() mess” conversation occurred on kernel mailing lists in late 2009 and January 2010, and the OSS-security thread and related mailing list archives explain both the complexity of the problem and why a single monolithic fix was insufficient — multiple commits across architectures and helper functions were necessary. That public thread formed part of the evidence used to assign the CVE and to coordinate disclosure.Exploitability: what operators needed to know in 2010 (and what still matters)
How easy was exploitation?
- The CVSS v2 base score mapped historically to a 4.6 (Medium) in many vendor trackers, indicating the vulnerability required local access but had low complexity to trigger in some contexts. The fact that PoC exploit code was reported increased urgency.
- Local access means attackers needed an account (or local code execution) to use mmap/mremap sequences; the vulnerability was not a remote network vector by itself. That limited immediate exposure to network-borne threats but made shared-hosting environments, multi-user servers, and systems with untrusted local users particularly sensitive.
Known proof-of-concept and real-world use
- Distribution advisories and security mailing lists reported working PoC code. Gentoo’s GLSA explicitly notes that PoC exploit code had been created and used to escalate to root on vulnerable kernels. Given that, any internet-exposed or multi-tenant host that had untrusted local processes needed to prioritize patching.
Attack surface considerations
- Systems allowing many VMAs per process (high vm.max_map_count) can sometimes expose more surface for memory-management bugs; some early workarounds suggested tuning vm.max_map_count as a stop-gap, though such mitigations are fragile and do not eliminate kernel-level logic flaws. Distribution advisories preferred full kernel updates.
Patching and mitigation guidance (practical steps for admins)
If you encounter this historically (or in any dormant legacy host), follow these steps:- Inventory kernels and check versions. Confirm whether any system is running a kernel older than 2.6.32.4 or any vendor kernel series that did not incorporate the upstream fixes. Distros will typically list the CVE against package versions; use vendor security tools to verify installed package versions.
- Apply vendor-supplied kernel updates. Patch kernels through your distribution’s package manager; do not attempt to cherry-pick upstream commits unless you are comfortable rebuilding and testing kernels comprehensively. Vendor packages incorporate necessary downstream compatibility adjustments.
- Restrict untrusted local access. On multi-tenant or shared systems, ensure that user privileges are minimized and local access is controlled through policies, containerization, or virtualization until patches can be applied.
- Avoid fragile workarounds. Increasing vm.max_map_count or other tunables may temporarily change exploit conditions but do not fix kernel logic errors and may introduce other stability risks. Prefer updates to permanent mitigations.
- Monitor for evidence of exploitation. Look for signs of local privilege escalations, unexpected kernel oopses, or processes attempting abnormal memory-manipulation sequences. Where possible, collect forensic images before patching if compromise is suspected.
Why the do_mremap() mess mattered: broader lessons
Complexity and coupling are dangerous
The problem that produced CVE-2010-0291 was not a single-line error but the visible symptom of complex coupling between memory-management helpers, per-architecture code, and subtle arithmetic/return-path logic. When many small assumptions interact, the window for surprising behaviors widens.Upstream coordination helps, but disclosure is tricky
Fixing this class of bug required multiple patches, careful testing, and cross-architecture review. The public mailing-list conversation demonstrated that disclosure and coordination in complex kernel code paths must balance timely fixes with correctness across many platforms. That is why the CVE and vendor advisories referenced multiple commits and why distributions staged packages into their kernels rather than relying on a single upstream patch.Short-term mitigations are poor substitutes for a patch
Suggestions like raising kernel tunables to change resource limits are stop-gaps. Any mitigation that changes the exploitation surface without addressing the core logic risk is inherently brittle and should only be used to buy time for a proper patch rollout. Gentoo’s advisory specifically warned operators against relying on such static workarounds.Forensics and detection: what to look for
- Kernel oops/kdump patterns: Crash traces referencing mm/mremap paths, or stack traces containing do_mremap(), mremap(), move_page_tables(), or do_munmap() suggest attempts to trigger the vulnerability.
- Unusual use of mmap/mremap: Processes that repeatedly call mmap/mremap or attempt exotic remapping patterns may be suspicious on a hardened host.
- Sudden privilege changes from local accounts: Investigate any unexpected UID/EGID changes, SUID binary manipulations, or sudden root shells spawned from unprivileged contexts.
Strengths and limitations of the historical fixes
Notable strengths
- Comprehensive upstream effort. The set of commits and vendor patches showed a substantial effort to remove ambiguous logic and corner cases across architectures, reducing attack surface materially.
- Vendor responsiveness. Distributions mapped the CVE to specific package updates and pushed fixes to supported releases, with remediation guidance for administrators.
Potential residual risks
- Legacy systems left unpatched. The primary risk has always been long-lived hosts that never receive kernel updates (embedded devices, end-of-life systems, appliances). Those remain vulnerable unless retired or mitigation strategies applied.
- Similar logic flaws elsewhere. Fixing one “mess” does not eliminate the class of errors that gave rise to the CVE; memory-management complexity can produce other subtle flaws over time, especially as features and optimizations evolve. Kernel developers and auditors must remain vigilant.
Contextual takeaways for modern operators
Although CVE-2010-0291 is historically specific, the incident remains relevant as a teaching example:- Patch promptly: Kernel bugs that are exploitable locally can be turned into full compromises in shared environments; timely patching is the only reliable mitigation.
- Treat PoC availability as urgency: Public PoCs materially change risk calculus — they often make exploitation trivial for attackers with local access.
- Focus on system hygiene: Minimize untrusted local users, reduce attack surface in multi-tenant setups, and employ defense-in-depth (e.g., SELinux/AppArmor, containers with constrained capabilities, and immutability where feasible).
- Audit critical subsystems: Memory-management code, filesystem and device drivers, and syscall-handling paths deserve regular review and fuzzing since errors there can cross privilege boundaries.
Final assessment
CVE-2010-0291 was a meaningful local security flaw rooted in the kernel’s handling of memory remapping. It combined several small logic errors and platform-specific edge cases into an exploitable pattern that could cause kernel crashes and — in some cases where the requisite conditions were met — local privilege escalation. The Linux community responded with a coordinated series of fixes and distribution updates; those patches stabilized the affected code paths and reduced the immediate risk.That said, the incident underscores perennial truths for system operators and kernel developers: memory-management code is high stakes, complexity multiplies risk, and only disciplined patch management and ongoing code-quality work will prevent similar vulnerabilities from becoming operational crises. Administrators responsible for legacy systems should verify that no host in their estate still runs an unpatched kernel from that era, and security teams should fold lessons from the do_mremap() mess into current auditing, fuzzing, and hardening efforts.
Source: MSRC Security Update Guide - Microsoft Security Response Center