The zlib library’s inftrees.c bug tracked as CVE-2016-9840 is a subtle but consequential example of how a tiny, non‑portable C optimization can become a wide‑ranging security headache — it allowed improper pointer arithmetic in zlib 1.2.8 to create undefined behavior that, in downstream contexts, could lead to data corruption, crashes and denial‑of‑service on many products that embed zlib. This article breaks down what went wrong, why the fix required removing a micro‑optimization, which systems were exposed, and exactly what practitioners should do to find and remediate the vulnerability in heterogeneous environments.
zlib is one of the most widely deployed compression libraries in the world: it’s embedded in operating systems, web servers, container runtimes, networking stacks, file formats and countless applications. Because zlib typically runs inside code that handles externally supplied compressed data (HTTP traffic, archives, protocol payloads), a bug in its decompression path can become an attack surface for remote inputs. That broad footprint is why even a seemingly small pointer arithmetic bug merits a high severity rating and aggressive backporting across distributions and vendors.
The specific report for CVE-2016-9840 points at the inftrees.c source file in zlib 1.2.8. The vulnerability description is concise: an out‑of‑bounds or undefined pointer calculation could be triggered by specially crafted compressed data, producing context‑dependent impacts. Depending on the consumer, that could be a simple crash or a far more severe integrity/availability compromise. Because many products embed zlib (sometimes as a bundled library), the downstream blast radius is large.
Key points about the upstream fix:
Notable vendor/distribution responses included:
Two important caveats:
Source: MSRC Security Update Guide - Microsoft Security Response Center
 Background and why this matters
Background and why this matters
zlib is one of the most widely deployed compression libraries in the world: it’s embedded in operating systems, web servers, container runtimes, networking stacks, file formats and countless applications. Because zlib typically runs inside code that handles externally supplied compressed data (HTTP traffic, archives, protocol payloads), a bug in its decompression path can become an attack surface for remote inputs. That broad footprint is why even a seemingly small pointer arithmetic bug merits a high severity rating and aggressive backporting across distributions and vendors.The specific report for CVE-2016-9840 points at the inftrees.c source file in zlib 1.2.8. The vulnerability description is concise: an out‑of‑bounds or undefined pointer calculation could be triggered by specially crafted compressed data, producing context‑dependent impacts. Depending on the consumer, that could be a simple crash or a far more severe integrity/availability compromise. Because many products embed zlib (sometimes as a bundled library), the downstream blast radius is large.
A technical look: what inftrees.c did and why it was wrong
What inftrees.c is responsible for
inftrees.c implements a core part of the DEFLATE decompression algorithm: building the Huffman decoding tables used by the inflater. The function is performance‑sensitive — it runs on every compressed stream — and historically the code contains small optimizations intended to reduce indexing costs and memory overhead.The problematic optimization: subtracting an offset from a pointer
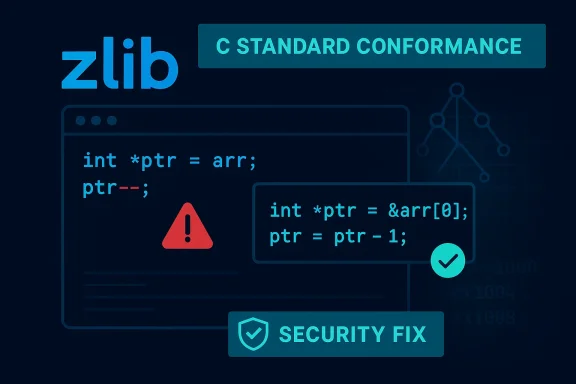
The faulty optimization made an array pointer point into the middle of an array by subtracting an offset from the pointer and then using that pointer as if it were an array base. Concretely, the implementation adjusted pointers so downstream code could index with values that assumed a shifted base. While this can work on some compilers and platforms, the C standard does not guarantee defined behavior for pointers decrementing below the start of an allocated array; using such pointers can produce undefined behavior. A security audit (and subsequent review) recommended eliminating that micro‑optimization because it made the code non‑portable and opened the door to out‑of‑bounds accesses in some contexts. (github.com)Why undefined behavior matters for security
Undefined behavior in C is dangerous because compilers are free to make assumptions that can change generated code semantics, and different optimization levels may alter whether an incorrect pointer expression causes a memory access that overruns a buffer or simply produces an incorrect value. When an attacker can control the inputs (compressed data), they can craft sequences that push internal indexes to edge cases, provoking the undefined behavior into a reproducible crash or memory corruption. In practice, that means the issue ranged from denial of service (easy and immediate) to potential integrity or confidentiality impacts in certain consumers that used zlib in more complex ways.The fix: remove the optimization, preserve correctness
Rather than attempting a subtle patch that reintroduces pointer tricks safely across platforms, zlib’s maintainer removed the offset pointer optimization entirely. The upstream commit replaced the pointer arithmetic with explicit index adjustments that are strictly conformant to the C standard. That change is intentionally small and surgical — the aim was to remove undefined behavior while preserving performance characteristics as much as possible. The commit that implements this removal is recorded in the zlib repository and was included in the zlib maintenance stream that developers and downstream packagers used to produce secure zlib binaries. (github.com)Key points about the upstream fix:
- The change removes the practice of decrementing an array pointer to create a shifted base.
- It replaces pointer arithmetic with well‑defined index math (e.g., subtracting a constant from indexes rather than pointers).
- It was backed by a security audit that recommended making the library strictly conformant to avoid undefined behavior. (github.com)
Severity, scoring and vendor responses
When CVE-2016-9840 was published the community assessed it as a high‑severity vulnerability (CVSS v3 values up to 8.8 appear in several trackers). That score reflects the combination of zlib’s ubiquity and the potential for remote inputs to trigger undefined behavior in decompression flows. Multiple vendors and distributions issued advisories and backported patches; you can find references in major trackers and vendor advisories.Notable vendor/distribution responses included:
- Distribution backports and security notices from Debian and Ubuntu, which tracked the issue and shipped patched zlib packages.
- SUSE and Red Hat classifying the issue as critical or high and publishing advisories and fixes.
- Enterprise vendors (e.g., IBM) that used zlib in their products published bulletins and recommended updates for affected products.
Who and what was affected?
- zlib 1.2.8 upstream: the bug existed in the upstream 1.2.8 sources and was addressed in subsequent zlib changes.
- Distribution packages and bundled zlib: many Linux distributions and downstream products backported the fix into their zlib packages; however, numerous vendor products (firmware, appliances, embedded devices) that bundle zlib in product images were affected until vendors issued updates.
- Applications that process untrusted compressed data: web servers, archive managers, protocol parsers, and any service that inflates DEFLATE streams from untrusted sources were at risk for crashes or denial of service if they used the vulnerable zlib build.
Exploitability and PoC: what the record shows
Public trackers record the technical root cause and the upstream fix, but there is no widely distributed, high‑quality proof‑of‑concept exploit that escalates CVE-2016-9840 into remote code execution in the wild. Most reports and vendor advisories described the vulnerability as permitting denial of service or unspecified impact under particular contexts. Security vendors and distribution trackers recorded varying CVSS vectors and environmental assessments — a sign that the practical impact depends heavily on how an application uses zlib and whether it exposes decompression endpoints to attacker‑controlled inputs.Two important caveats:
- Many CVE summaries consolidate downstream impact models (availability, integrity, confidentiality) into a worst‑case CVSS string; this can overstate RCE risk in the absence of a demonstrated exploit. Treat such strings as potential rather than demonstrated outcomes unless a PoC is published.
- Conversely, the absence of a public PoC does not mean an exploit is impossible; undefined behavior can behave differently on different compilers or CPU architectures, and a determined researcher could craft a case that yields memory corruption in a specific consumer, producing an escalation beyond a simple crash.
Detection: how to find vulnerable zlib in your environment
Finding affected zlib instances requires a two‑pronged approach: inventorying library versions and scanning for bundled copies.- Identify system zlib package versions:
- On Debian/Ubuntu: check the zlib1g package version via dpkg-query or the system package manager. If the package dates to pre‑fix releases, plan to update.
- On Red Hat/SUSE/CentOS: query rpm for zlib variants and check vendor errata to confirm whether the system build includes the inftrees.c fix.
- Find statically linked or bundled zlib:
- Use binary inspection: run strings or ldd / objdump on binaries that handle compressed data. Applications that ship with a private zlib will need application‑level patching or a rebuild.
- Search package archives and installers for zlib source code or the string “zlib 1.2.8” to identify older bundled copies.
- Network and behavioral indicators:
- Monitor for processes that crash on handling compressed payloads or for logs indicating repeated decompressor failures (inflate/deflate errors).
- Set up fuzzing or ingestion tests in a staging environment to see whether your decompression endpoints crash on malformed inputs — but only in controlled, isolated testing; fuzzing production services risks downtime.
Remediation and mitigation: concrete steps
- Inventory all zlib instances:
- Identify system packages (zlib1g, zlib-devel, zlib1) and note versions.
- Find statically linked instances inside application binaries or vendor appliances.
- Update system packages:
- Apply vendor security updates (Ubuntu, Debian, Red Hat, SUSE, etc.). Most mainstream distributions backported the fix into their zlib packages and released advisories. Reboot or restart services as required by your packaging policy.
- Rebuild or update applications that bundle zlib:
- For applications that include zlib in their tree or statically link it, rebuild against a fixed zlib or update the bundled copy to a fixed upstream commit (the commit that removed the offset pointer optimization is available in the upstream zlib repo). (github.com)
- Short‑term mitigations (if you cannot immediately patch):
- Restrict access to services that accept compressed inputs from untrusted sources by network controls (ACLs, WAF rules).
- Limit the handling of compressed payloads to authenticated, whitelisted clients when possible.
- Rate‑limit and monitor decompression endpoints for repeated malformed requests that could be triggering DoS attempts.
- Validate fixes:
- After applying vendor or upstream fixes, exercise decompression endpoints with known good corpuses and with controlled fuzz tests to ensure crash conditions no longer appear in patched builds.
- Confirm package versions against vendor advisories and CVE trackers.
Operational and supply‑chain considerations
CVE-2016-9840 highlights recurring supply‑chain realities:- Libraries may be present in two ways: as system packages and embedded copies. Patching the OS may not fix statically linked or bundled zlib contained inside proprietary installers or appliances.
- Vendor firmware and appliance updates are often slower than OS package updates. For appliances that cannot be patched quickly, apply compensating controls (network segmentation, traffic filtering, and monitoring).
- Because the vulnerability was a language‑level undefined behavior issue, it could manifest differently across compiler versions and CPU architectures; that complicates blanket exploit classification and makes vendor testing important.
Why the fix was conservatively simple — and why that matters for engineers
Removing the pointer subtraction optimization is a textbook example of security through correctness. The code optimization relied on behavior the C standard explicitly does not define; compiler optimizers and hardware can differ in their semantics for such constructs, making the bug non‑portable and fragile. The correct engineering posture was to sacrifice a trivial optimization in favor of unequivocal correctness across compilers and architectures. The upshot for developers: prefer portable, standard‑conforming constructs in security‑critical code paths, especially in widely reused libraries. (github.com)Final recommendations — a checklist for teams
- Patch system zlib packages now if you haven’t already: update distributions to the security‑patched zlib release.
- Identify and rebuild any binaries that statically link to zlib 1.2.8 or earlier; do not assume the system update will cover them.
- Use application‑level controls to limit untrusted compressed input exposure while you patch (WAFs, access controls, rate limiting).
- Add zlib and similar widely reused libraries to your SBOM and SCA processes so future CVEs hit your radar and inventory automatically.
- If you operate vendor appliances or third‑party software, confirm with vendors whether their product images include the fixed zlib and request updates where necessary.
Conclusion
CVE-2016-9840 is a reminder that the most dangerous vulnerabilities are sometimes not the glamorous remote‑code‑execution chains but the tiny, undefined behaviors that ripple through the software supply chain. The root cause was an illegal pointer manipulation — a micro‑optimization that violated the C standard — and the correct remedy was straightforward: eliminate the undefined behavior. Because zlib is foundational and ubiquitous, the community response was appropriately broad: upstream commits, distribution backports and vendor advisories. The practical lesson for engineers and security teams is durable: enforce portability and correctness in libraries, maintain accurate inventories of third‑party components, and treat language‑undefined constructs with suspicion in security‑sensitive code. (github.com)Source: MSRC Security Update Guide - Microsoft Security Response Center