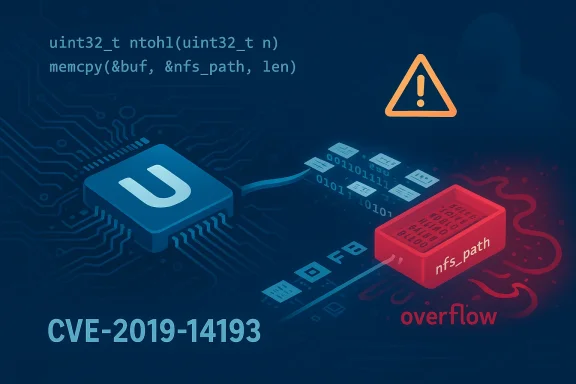
The U‑Boot bootloader contains a critical NFS parsing bug that was assigned CVE‑2019‑14193: an unbounded memcpy in the nfs_readlink_reply handler that uses an attacker‑controlled length without validation, allowing remotely supplied NFS responses to trigger memory corruption and, in the worst case, remote code execution on devices that expose U‑Boot’s networking functionality.
Das U‑Boot (commonly called U‑Boot) is the universal boot loader used by a wide range of embedded systems, development boards, IoT devices, and some consumer hardware. It can fetch next‑stage payloads over network protocols such as TFTP and NFS, which is convenient for diskless development and network boot scenarios—but it also expands the attack surface to include network‑supplied data parsed before secure‑boot or image verification runs. Security researchers used CodeQL and manual review to identify a family of network‑parsing bugs in U‑Boot’s NFS and UDP handling; the nfs_readlink_reply issue is one of the CVEs that resulted from that audit.
U‑Boot is typically built into firmware images or delivered as part of OS packages for development and production boards. Embedded devices rarely receive the same patch cadence as servers and desktops, so bootloader vulnerabilities like this one can remain live in the field for years unless device manufacturers, board vendors, or maintainers of distribution packages push updates. Several distributions and vendors published advisories and backported patches after disclosure; nevertheless many devices that shipped with vulnerable U‑Boot versions remain at risk.
The vulnerable pattern appears in the NFS reply parsing path (nfs_readlink_reply) where the code:
Two additional vectors that make the problem worse:
After publication, downstream distributions and vendors issued package updates and patches. Multiple distribution security trackers (Debian, Ubuntu, SUSE, and others) published notices and fixed package versions; packagers also prepared a set of patches for the vulnerable files. The openSUSE and other distribution build recipes show patch names explicitly tied to the CVEs (for example, patches labeled “CVE-nfs-fix-stack-based-buffer-over” and “CVE-2019-14194-CVE-2019-14198-nfs-fix”). This demonstrates that fixes were produced and applied in distro packaging trees.
Practical signals that a device is patched:
The research community’s use of CodeQL and public disclosure prompted fixes and packaged updates, but the operational reality remains: many devices will carry the vulnerable code long after a fix is available. That gap makes network controls, strict build hygiene, and robust update mechanisms critical for anyone deploying U‑Boot in production.
Source: MSRC Security Update Guide - Microsoft Security Response Center
 Background
Background
Das U‑Boot (commonly called U‑Boot) is the universal boot loader used by a wide range of embedded systems, development boards, IoT devices, and some consumer hardware. It can fetch next‑stage payloads over network protocols such as TFTP and NFS, which is convenient for diskless development and network boot scenarios—but it also expands the attack surface to include network‑supplied data parsed before secure‑boot or image verification runs. Security researchers used CodeQL and manual review to identify a family of network‑parsing bugs in U‑Boot’s NFS and UDP handling; the nfs_readlink_reply issue is one of the CVEs that resulted from that audit.U‑Boot is typically built into firmware images or delivered as part of OS packages for development and production boards. Embedded devices rarely receive the same patch cadence as servers and desktops, so bootloader vulnerabilities like this one can remain live in the field for years unless device manufacturers, board vendors, or maintainers of distribution packages push updates. Several distributions and vendors published advisories and backported patches after disclosure; nevertheless many devices that shipped with vulnerable U‑Boot versions remain at risk.
What the bug actually is (technical overview)
At its core, CVE‑2019‑14193 is a bounds‑check omission: a length value parsed from an NFS reply is converted from network byte order and then used directly as the length argument to memcpy without validating that the length fits within the destination buffer or even that the source packet contains that many bytes.The vulnerable pattern appears in the NFS reply parsing path (nfs_readlink_reply) where the code:
- parses a 32‑bit length field using ntohl(),
- decides if the returned path begins with a slash or not, and
- calls memcpy(dest, src, rlen) using that rlen value, and then writes a trailing NUL.
- rlen can be larger than the destination buffer,
- rlen can be crafted to cause integer wrap/underflow in subsequent arithmetic,
- memcpy will copy attacker‑controlled data out of bounds, producing stack or heap corruption that an attacker can (in many builds) convert into code execution. A paraphrased excerpt of the vulnerable logic shows the pattern researchers flagged.
Two additional vectors that make the problem worse:
- U‑Boot’s packet handlers sometimes compute lengths from UDP/IP headers without verifying that the packet payload is as large as advertised, which can lead to integer underflow and miscomputed copy sizes earlier in the receive path. This can enlarge the attack surface beyond NFS responses to other UDP services in the same code.
- Other NFS helper functions—nfs_read_reply, nfs_lookup_reply and others—exhibit the same class of mistakes (either missing checks or checks insufficient to catch crafted negative/overflow cases). Combined, these weaknesses form a cluster of remote memory‑corruption issues in U‑Boot’s network stack.
Why this is dangerous in practice
- Network‑exposed attack vector: The code path is reachable from the network. An attacker who can supply NFS replies (for example, by being on the same LAN or controlling an NFS server used by a device) can send crafted packets to trigger the bug. That makes the attack vector remote and, importantly, unauthenticated.
- Potential for remote code execution: Memory corruption caused by out‑of‑bounds writes to global or stack buffers is a classic pathway to RCE. Embedded bootloaders often lack modern runtime protections (full ASLR, stack canaries, NX protections, or the protections may be inconsistently enabled across builds), so an overflow in U‑Boot has a realistic path to arbitrary code execution on many targets. Security Lab and subsequent CVE records assigned high severity scores for these issues.
- Pre‑verification timing: Because U‑Boot parses network data before handing control to higher stages or performing image verification in many configurations, a successful exploit at this stage can subvert secure boot processes or cause device jailbreaks before signature checks run. That makes the impact more severe than a typical post‑boot exploit.
- Widespread exposure on devices: U‑Boot is widely deployed across architectures and boards. Even if mainstream distributions update packaged u‑boot binaries, many manufacturers ship firmware images that are not updated for months or years, leaving devices exposed in the field. Distribution advisories and package updates exist, but coverage is uneven.
What the security community found and how it was disclosed
The vulnerability family was discovered by researchers using CodeQL inspection as well as manual review. The Security Lab writeup (and associated CodeQL challenge) uncovered a set of similar memcpy/MEMREAD patterns across U‑Boot’s NFS and UDP code paths; MITRE assigned a series of CVEs (including CVE‑2019‑14193) for these issues. The researchers followed coordinated disclosure procedures with U‑Boot maintainers; the initial public post and mailing list announcements were made in July 2019.After publication, downstream distributions and vendors issued package updates and patches. Multiple distribution security trackers (Debian, Ubuntu, SUSE, and others) published notices and fixed package versions; packagers also prepared a set of patches for the vulnerable files. The openSUSE and other distribution build recipes show patch names explicitly tied to the CVEs (for example, patches labeled “CVE-nfs-fix-stack-based-buffer-over” and “CVE-2019-14194-CVE-2019-14198-nfs-fix”). This demonstrates that fixes were produced and applied in distro packaging trees.
Patching and vendor status (what to look for)
If you manage embedded Linux boards, development images, or distribution packages, the safe action is to confirm that your U‑Boot binaries are built from source that includes the post‑disclosure fixes (i.e., not the vulnerable v2019.07 snapshot or earlier). Distribution trackers list the patched binary packages and the point at which fixes were applied; for example, Ubuntu and Debian entries reference patched u‑boot package versions and release updates that include mitigations for the CVEs. Check your distribution’s security tracker or your device vendor’s firmware advisories for specific package version numbers.Practical signals that a device is patched:
- The U‑Boot source tree used to build your firmware was updated after July–August 2019 to include NFS parsing guard checks and safe handling of network length fields.
- Your distribution’s u‑boot package metadata shows a security update that references the CVE(s) and lists fixed binary versions (Ubuntu’s OSV and Debian security tracker pages record such fixes).
- Disable U‑Boot networking where not required, or disable NFS support in U‑Boot builds. This removes the exposed code path entirely.
- Block NFS traffic to and from devices at the network perimeter and restrict which hosts can act as NFS servers for development boards.
- Use network segmentation to isolate boards that require network booting from untrusted networks.
Security Lab’s advisories explicitly recommend applying patches as they are released, and until patched, avoiding network‑based booting features that allow the vulnerable codepath to be exercised.
Detection and hunting guidance
Detecting exploitation of a bootloader vulnerability is challenging because the bug occurs before the OS is loaded, and many devices do not log U‑Boot activity to remote collectors. Still, operators can use several approaches:- Audit firmware images: extract and compare the U‑Boot binary in your device’s firmware against patched package binaries or upstream source commits (if you build from source, check your git revision). Tools that build reproducible artifacts or package metadata inspection will help confirm whether a patched U‑Boot is present. Distribution advisories list the patched package versions to match.
- Network monitoring: look for suspicious or unexpected NFS traffic patterns, especially malformed or unusually large NFS replies targeted at devices during early boot. A malicious NFS server on the same subnet is a red flag.
- Review device configuration: verify whether U‑Boot is configured to attempt NFS/TFTP network boot or to accept BOOTP/DHCP/TFTP responses at boot time; disable those features when not needed.
- Reproduce safely in lab: security researchers and maintainers have reproduced the vulnerability in QEMU‑based testbeds for analysis. If you have lab devices, emulate vulnerable builds and run controlled tests rather than testing on production appliances. (Several published walk‑throughs show how to compile v2019.07 U‑Boot and set up minimal NFS servers to reproduce behavior).
For developers: how this should never have happened, and how to prevent similar bugs
This class of vulnerability is textbook: data comes from an untrusted source, it is parsed, converted with ntohl/ntohs, and that numeric value reaches memcpy without checks. Avoiding it requires a combination of secure coding and defensive parsing:- Always validate lengths derived from the network against both the destination buffer size and the remaining source buffer length before performing copies.
- Prefer bounded copy functions or explicit range checks instead of blind memcpy when the length is attacker‑controlled.
- Use size_t for buffer sizes and check for integer overflows when adding offsets (e.g., pathlen + rlen).
- Factor parsing and bounds checks into a small set of robust helpers that are easier to audit and unit‑test.
- Add fuzzing and taint‑tracking scans (CodeQL, libFuzzer, afl‑based harnesses) as part of the CI pipeline. Security Lab used CodeQL to find multiple variants; that shows how static analysis can catch taint flows from ntohl to memcpy.
- Hardening at build time: enable stack canaries, NX, RELRO, and link‑time optimization where feasible for bootloader builds. While embedded builds sometimes omit these for size or compatibility reasons, enabling them where possible raises the bar for exploitation.
- Keep a strict release process for bootloaders and firmware that includes a security update path and signed releases so devices can be updated reliably.
Risk analysis: who is most at risk?
- Development boards and test rigs that are configured to network‑boot or to fetch file‑system resources over NFS are the primary risk group—these are commonly used in labs and manufacturing. An attacker on the same network or a compromised NFS server used during development can mount an attack without prior authentication.
- Consumer or industrial devices with U‑Boot present in firmware and exposed to untrusted networks (for example, remote management interfaces that allow reconfiguration of network boot options) are also at risk.
- Devices with no timely firmware update channel are the most concerning: a vulnerable U‑Boot embedded in firmware that is never updated leaves the device permanently exploitable unless mitigated by network controls. Distribution patches help OS images, but vendor firmware updates are the real fix for devices in the field.
- Devices compiled with modern mitigations (ASLR, stack canaries, NX) and with U‑Boot configured to reject network booting reduce the likelihood of successful exploitation.
- Secure boot flows that verify images before execution mitigate post‑boot compromise; however, they do not protect the system if the bootloader itself is compromised before verification steps.
Practical remediation checklist (for operators and firmware engineers)
- Inventory: Identify all devices and images that include U‑Boot (and record their U‑Boot version/revision).
- Patch: Apply vendor firmware updates that include patched U‑Boot builds. If you build your own U‑Boot, update to a post‑July‑2019 tree that includes NFS parsing fixes and rebuild firmwares. Distribution package updates (Debian, Ubuntu, SUSE, Fedora) list patched package versions; install those updates for affected systems.
- If patching is not immediately possible:
- Disable NFS and network boot features in U‑Boot configuration.
- Block NFS and related UDP traffic from untrusted networks; restrict NFS server access to trusted hosts.
- Test: In lab, validate patched images against previously vulnerable test cases (reproduce vulnerability in a controlled environment before and after patching).
- Monitor: Watch for unusual NFS traffic during device boot and implement network controls that make it harder for attackers to provide malicious NFS replies.
- Long term: Improve firmware update paths, enable signature verification and secure boot end‑to‑end, and incorporate automated static/dynamic analysis in the firmware CI pipeline.
The broader lesson: bootloader security matters
CVE‑2019‑14193 is not just a bug in one function; it’s a symptom of a larger class of errors that occur when low‑level code parses untrusted network data without defensive checks. Bootloaders sit at the earliest possible stage of system initialization, so vulnerabilities there carry disproportionate risk: they can undermine secure boot, enable persistent jailbreaks, and affect a huge number of embedded devices with slow or nonexistent patch lifecycles.The research community’s use of CodeQL and public disclosure prompted fixes and packaged updates, but the operational reality remains: many devices will carry the vulnerable code long after a fix is available. That gap makes network controls, strict build hygiene, and robust update mechanisms critical for anyone deploying U‑Boot in production.
Conclusion
CVE‑2019‑14193 is a severe, network‑accessible memory‑corruption vulnerability in U‑Boot’s NFS reply parsing (nfs_readlink_reply) that results from an unvalidated memcpy length. The vulnerability was discovered during a focused CodeQL audit that found multiple tainted memcpy call sites; it was disclosed in mid‑2019 and subsequently patched by maintainers and downstream distributors. Operators should verify that their U‑Boot binaries are patched (or apply vendor firmware updates), disable unneeded U‑Boot network features, and use network segmentation to isolate devices that require network booting. Developers and maintainers must also adopt defensive parsing practices, static analysis, and runtime hardening to prevent similar remote‑exploitation classes in low‑level boot code going forward.Source: MSRC Security Update Guide - Microsoft Security Response Center