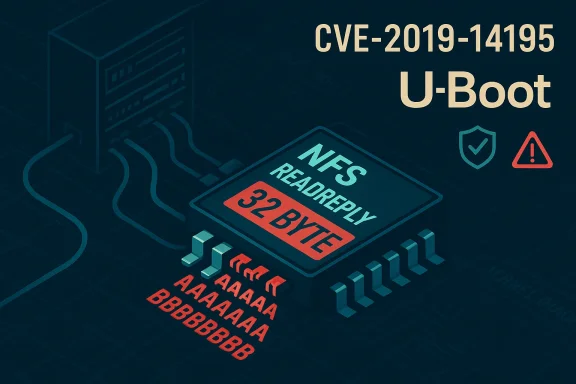
An overlooked parsing bug in Das U-Boot’s NFS reply handling — tracked as CVE-2019-14195 — allows an attacker who can control the NFS responses seen by a device to trigger an unbounded memcpy and corrupt U-Boot’s stack or heap, creating a realistic pathway to code execution during early boot. The flaw affects U-Boot releases through 2019.07 and was responsibly disclosed and patched upstream, but its discovery exposed a common hard-to-manage class of problems for bootloaders: network‑facing parsing code that trusts attacker-controlled length fields.
Das U-Boot (the “universal boot loader”) is the de facto open-source bootloader used across a huge range of embedded and IoT devices. U-Boot can fetch boot artifacts over the network (TFTP, NFS) in development flows and in diskless deployments. That network-facing functionality is powerful — and dangerous when parsing code fails to validate lengths and counts extracted from wire data. Semmle’s security research team audited U-Boot’s networking code with CodeQL and disclosed a cluster of NFS‑related parsing bugs in mid‑2019. Several of those issues were assigned CVE identifiers including CVE-2019-14195. The public writeup and disclosures made clear the attack surface: a device using U-Boot’s NFS/TFTP features (or a device exposed to a malicious actor on the same network) could receive crafted replies that trigger unsafe memcpy calls.
The specific vulnerability CVE-2019-14195 is an unbounded memcpy with an unvalidated length inside the function that handles an NFS READLINK reply (nfs_readlink_reply). In short: an attacker-controlled length field is parsed and later used directly as the memcpy size without sufficient bounds checking, allowing writes beyond the intended buffer. Upstream maintainers accepted a targeted patch in late summer 2019; the fix adds explicit validation of the reply data before copying. (gitlab.com)
Caveat: exploit development and public disclosure timelines do not always align with patch timelines. For defenders, the prudent assumption is that if code is reachable by attacker-controlled network data and it contains unchecked memory operations, exploitation is feasible — so patching and isolation are warranted regardless of public exploit evidence.
For defenders the message is straightforward: assume that any code which parses external input can be wrong; prioritize patching devices in your fleet, restrict network boot surfaces, require signed boot chains where possible, and push vendors for firmware updates for devices in your inventory. For developers, apply rigorous defensive programming to all wire parsing logic today — the cost of one careful bounds check is a fraction of the cost of a compromised device tomorrow.
Source: MSRC Security Update Guide - Microsoft Security Response Center
 Background / Overview
Background / Overview
Das U-Boot (the “universal boot loader”) is the de facto open-source bootloader used across a huge range of embedded and IoT devices. U-Boot can fetch boot artifacts over the network (TFTP, NFS) in development flows and in diskless deployments. That network-facing functionality is powerful — and dangerous when parsing code fails to validate lengths and counts extracted from wire data. Semmle’s security research team audited U-Boot’s networking code with CodeQL and disclosed a cluster of NFS‑related parsing bugs in mid‑2019. Several of those issues were assigned CVE identifiers including CVE-2019-14195. The public writeup and disclosures made clear the attack surface: a device using U-Boot’s NFS/TFTP features (or a device exposed to a malicious actor on the same network) could receive crafted replies that trigger unsafe memcpy calls.The specific vulnerability CVE-2019-14195 is an unbounded memcpy with an unvalidated length inside the function that handles an NFS READLINK reply (nfs_readlink_reply). In short: an attacker-controlled length field is parsed and later used directly as the memcpy size without sufficient bounds checking, allowing writes beyond the intended buffer. Upstream maintainers accepted a targeted patch in late summer 2019; the fix adds explicit validation of the reply data before copying. (gitlab.com)
What the bug is, in plain terms
How the vulnerability arises
- U-Boot parses an NFS reply packet into a local RPC structure.
- The code reads a 32-bit length value from the reply and later uses that value as the byte count for a memcpy.
- The implementation did not robustly check that the parsed length fits within the boundaries of the source packet or the destination buffer.
- Because the length comes directly from the remote NFS server’s reply, a malicious or compromised NFS server can craft values that cause memcpy to copy more bytes than the destination buffer can hold, producing an out‑of‑bounds write.
Why the bootloader context matters
Unlike a user‑space process on a modern OS, U‑Boot runs early in the device lifecycle with few of the protections (and very few of the monitoring tools) common later in boot. Successful exploitation here can:- Hijack boot flow to load arbitrary payloads before the kernel or secure boot checks;
- Persist a rootkit that is invisible to higher-layer integrity checks if the device lacks secure boot or has misconfigured verification; and
- Enable recovery/firmware‑level access for attackers who can physically or network-wise reach the device.
Timeline and responsible disclosure
- Discovery: Semmle’s team (led by Fermín Serna and colleagues) found multiple NFS and networking parsing problems in May 2019 while running CodeQL-based audits against U‑Boot.
- Upstream contact: U‑Boot maintainers were notified and acknowledged receipt; Semmle coordinated disclosure with the project to avoid mass exploitation prior to fixes.
- Public disclosure / CVE assignment: MITRE assigned CVE identifiers (including CVE-2019-14195) and several Linux distributions and trackers published advisories in July 2019.
- Patch: U‑Boot received an explicit commit that checks reply data before performing memcpy in nfs_readlink_reply (commit cf3a4f1e). The change was authored by Cheng Liu and committed with acknowledgments to the reporter. Administrators and distributors later shipped fixes in their u‑boot packages. (gitlab.com)
Technical analysis: why memcpy without validation is dangerous here
Attack primitive and exploitability
The vulnerability is an out‑of‑bounds write (CWE‑787) caused by copying more data into a limited buffer than it can hold. From an exploitation perspective:- If the memcpy overwrites a saved return address or function pointers on the stack, control flow hijack is possible.
- Even without immediate code execution, memory corruption can crash the bootloader and place the device into an insecure recovery mode or unverified fallback flow.
- Compiler and CPU mitigations (stack canaries, non‑executable stacks, ASLR) make exploitation more complex but not impossible — particularly on architectures used by many embedded devices, where such protections may be absent or inconsistently applied.
Why a single-line fix matters — and why it can also be incomplete
The upstream commit for CVE-2019-14195 inserts explicit checks on rpc_pkt.u.reply.data to ensure the declared length cannot exceed the packet length before copying. That direct fix gets to the heart of the immediate bug, but it does not rewrite the larger design: the presence of many memcpy calls that assume correct wire encoding still means future parsing errors are possible if similar validation is omitted elsewhere. Semmle’s original disclosure found multiple distinct call sites with the same pattern; each required attention. (gitlab.com)Who and what is affected
- Affected product: Das U‑Boot versions up to and including 2019.07. The vulnerability description explicitly enumerates this range.
- Practical exposure: Devices that use U‑Boot’s network boot features (NFS/TFTP) at runtime are in scope. Many development boards, diskless embedded devices, and certain IoT images that fetch their next-stage images over NFS can be vulnerable. Devices that never enable network boot or that use U‑Boot only to load from local, immutable storage are far less likely to be affected in practice.
- Distribution patches: Major Linux distribution trackers (Debian, Ubuntu, etc.) recorded the CVE and indicate that the packaged u-boot sources were updated and fixed in subsequent package versions; distributors provided package updates to mitigate the issue for affected installations. (security-tracker.debian.org)
Patching, mitigation, and detection guidance
What was fixed upstream
- The upstream fix (commit cf3a4f1e) added explicit validation ensuring that the rlen (parsed path length) and other reply-derived offsets were checked against the total packet length before any copying occurs. That eliminates the straightforward scenario where a crafted NFS reply causes memcpy to read or write past buffer limits. (gitlab.com)
Vendor/distribution actions
- Linux distributions packaged fixed u‑boot versions and released updates; Debian and Ubuntu trackers list fixed versions in their archives. Operators of general-purpose systems can and should install those u‑boot package updates where applicable. However, many embedded devices do not receive distribution-style updates; they rely on vendor firmware images. (security-tracker.debian.org)
Practical mitigations for operators (ordered)
- Inventory: Identify devices that use U‑Boot and determine whether network boot (NFS/TFTP) is enabled or possible at runtime.
- Patch where possible: If vendor firmware updates that include an upstream-fixed U‑Boot exist, apply them following vendor guidance.
- If you cannot patch immediately:
- Disable network boot support in U‑Boot configuration if feasible.
- Prevent untrusted NFS servers from being reachable by devices (network segmentation, access control lists).
- Use signed/verified boot chains so that even if U‑Boot is compromised, higher layers require signed images to run.
- Monitor for anomalies: Unexpected boot failures, new or unknown recovery images, or unusual network requests during boot are potential indicators.
- Replace or retire devices that cannot be patched or adequately isolated.
Evidence of exploitation and public proof-of-concept
At disclosure time (and in follow-up tracking), there were no widely reported cases of in-the-wild exploitation of CVE-2019-14195 nor broadly published working proof-of-concept exploits. Security trackers and vendor advisories noted the vulnerability severity and the plausible exploitability, but did not report active abuse. Tools and scanners flagged systems with vulnerable u-boot packages for assessment. That said, the absence of public exploitation reports does not mean the risk is theoretical: the required primitives (network-sourced length field, unchecked memcpy) make realistic exploitation possible in favorable conditions, and attackers targeting embedded devices have historically leveraged similar patterns.Caveat: exploit development and public disclosure timelines do not always align with patch timelines. For defenders, the prudent assumption is that if code is reachable by attacker-controlled network data and it contains unchecked memory operations, exploitation is feasible — so patching and isolation are warranted regardless of public exploit evidence.
The broader lesson: parsing code in privileged early-boot components must be minimal and defensive
CVE-2019-14195 is one data point in a recurring theme:- Bootloaders and network stacks often implement byte-level parsing logic that assumes well-formed input.
- Memory safety errors (unchecked lengths, integer underflow/overflow in length calculations, assumptions about packet completeness) repeat across projects and languages when wire parsing is involved.
- The impact of compromise at boot is high because later defenses (OS-level policies, userland monitoring) may be bypassed.
Notable strengths and risks in the handling and aftermath
Strengths
- Responsible disclosure process: Semmle coordinated disclosure with the U‑Boot maintainers, who acknowledged and accepted fixes. That coordination limited the window in which the bug was public without an upstream patch.
- Focused, minimal fix: The upstream patch directly validated packet lengths before memcpy, removing the immediate vulnerability without a major refactor of the codebase. Small, surgical fixes reduce the chance of introducing regressions. (gitlab.com)
- Distribution remediation: Major distributions tracked the CVE and published package upgrades; Debian and Ubuntu listings show fixed packages were rolled into repo updates for affected releases. That provides a practical path to remediation for many users. (security-tracker.debian.org)
Risks and remaining concerns
- Firmware update complexity: Many embedded devices require vendor firmware updates to change their bootloader. If vendors do not provide timely firmware updates or if devices are end-of-life, operators may be left with unpatchable attack surface. Distribution package updates help hosts but not all embedded fleets. (security-tracker.debian.org)
- Recurrent patterns: The root cause is a recurring class of mistakes (unsafe use of memcpy with wire-provided lengths). Other call sites in the same codebase or in other projects may have similar errors; indeed, Semmle’s audit found multiple such call sites. A single commit fixes one instance but does not guarantee there are no variants remaining.
- Hardening variance: Devices differ wildly in whether they have stack canaries, NX protections, or ASLR. On devices without those mitigations, exploitation is easier and consequences more severe.
A short checklist for engineers and administrators
- For embedded/IoT engineers:
- Audit early-boot code paths that interact with the network for any use of memcpy/memmove/read without strong bounds checks.
- Prefer defensive parsing: validate packet sizes and offsets against total packet length before reading or copying.
- Where possible, reduce or disable network parsing in privileged early-boot code; move complex parsing into less-privileged stages that can be more robustly defended.
- Consider enabling verified boot so that even if U‑Boot is compromised, downstream firmware requires signatures.
- For IT/OT administrators:
- Identify devices that run U‑Boot and assess whether network boot (NFS/TFTP) is used or possible.
- Apply vendor firmware updates that include the upstream U‑Boot fixes where available.
- If patches are not available, isolate devices from untrusted networks and block access to potential malicious NFS servers.
- Monitor boot-time network traffic and unexpected device reboots as potential indicators of exploitation attempts.
Final assessment and closing thoughts
CVE-2019-14195 is a high‑impact but fixable vulnerability: an unchecked memcpy in U‑Boot’s NFS reply handler could enable early‑boot memory corruption and, under favorable conditions, code execution. The issue was responsibly discovered, disclosed, and patched upstream; distributions and some vendors rolled fixes into their packages/images. However, the incident highlights systemic difficulties in the embedded space: inconsistent patching, long device lifecycles, and the reality that privileged, early-boot parsing code is both necessary and inherently risky.For defenders the message is straightforward: assume that any code which parses external input can be wrong; prioritize patching devices in your fleet, restrict network boot surfaces, require signed boot chains where possible, and push vendors for firmware updates for devices in your inventory. For developers, apply rigorous defensive programming to all wire parsing logic today — the cost of one careful bounds check is a fraction of the cost of a compromised device tomorrow.
Source: MSRC Security Update Guide - Microsoft Security Response Center