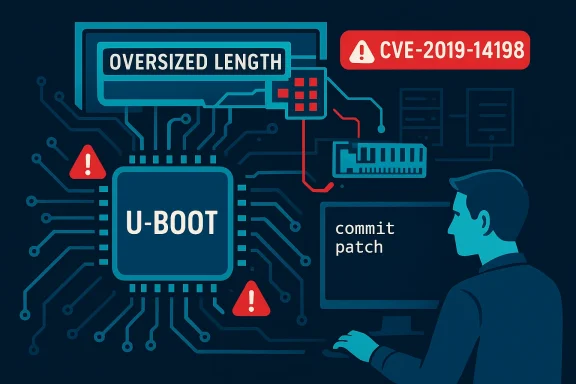
An unbounded memcpy in U-Boot’s NFS reply handler left a wide swath of embedded and development hardware exposed to remote memory corruption and — in many realistic configurations — remote code execution during network boot operations, a defect formally tracked as CVE-2019-14198. (nvd.nist.gov)
Das U-Boot (commonly called U-Boot) is the de facto open-source bootloader used across millions of embedded systems, development boards, network appliances, and IoT devices. Its responsibilities include initializing hardware, loading kernels or images from local storage, and supporting network boot operations such as TFTP and NFS. Because U-Boot frequently runs before any operating system protections are in place, bugs in its parsers and network stacks carry outsized risk: exploitation at boot can lead to persistent, early-stagerd to detect or remediate. (nvd.nist.gov)
CVE-2019-14198 was disclosed in mid‑2019 and affects U-Boot releases up to and including 2019.07. The vulnerability is an out‑of‑bounds write (CWE‑787) caused by an unbounded memcpy invoked from the NFS reply parsing logic — specifically inside the function that handles NFS read replies (nfs_read_reply) when the code path reaches the store_block handling for NFSv3 responses. The net effect: an attacker controlling or impersonating an NFS server can craft reply packets that cause U-Boot to copy more data than a destination buffer can hold, overrunning stack or heap memory and enabling crashes or arbitrary code execution on vulnerable devices. (nvd.nist.gov)
Multiple downstream advisories and distribution trackers recorded the flaw along with remediation timelines and patched package versions; Debian, SUSE, and other distributions list the issue and provide fixed packages and backports. (security-tracker.debian.org)
Two practical implementation mistakes make this scenario dangerous:
Distribution trackers provide practical guidance about fixed package versions. For example, Debian marked the issue fixed in the 2020.01+dfsg‑1 source package and later releases; SUSE and other vendors published advisories and backports for affected product lines. Those distribution advisories are useful because many embedded and appliance vendors consume U‑Boot trees from downstream packaging rather than pulling upstream directly. (security-tracker.debian.org)
The patch series that backported and labeled the changes for distributions included explicit notes acknowledging the reporter and the affected functions, and they modified net/nfs.c to add the missing checks and correct the length handling. The presence of a specific commit hash and a referenced patch in distribution layers provides a clear remediation trail for integrators and sysadmins.
However, two qualifiers matter when assessing actual risk:
For practitioners: prioritize inventorying firmware and network‑booting devices, apply patches or vendor-supplied updates as available, and where possible disable or isolate NFS/TFTP boot services. For vendors and integrators: treat bootloaders as critical, include them in SBOMs and patch management, and invest in secure update and recovery mechanisms that make post‑discovery remediation and distribution records provide the evidence trail for the vulnerability description, remediation commits, and packaged fixes, enabling both technical verification and practical patching plans. (nvd.nist.gov)
Source: MSRC Security Update Guide - Microsoft Security Response Center
 Background / Overview
Background / Overview
Das U-Boot (commonly called U-Boot) is the de facto open-source bootloader used across millions of embedded systems, development boards, network appliances, and IoT devices. Its responsibilities include initializing hardware, loading kernels or images from local storage, and supporting network boot operations such as TFTP and NFS. Because U-Boot frequently runs before any operating system protections are in place, bugs in its parsers and network stacks carry outsized risk: exploitation at boot can lead to persistent, early-stagerd to detect or remediate. (nvd.nist.gov)CVE-2019-14198 was disclosed in mid‑2019 and affects U-Boot releases up to and including 2019.07. The vulnerability is an out‑of‑bounds write (CWE‑787) caused by an unbounded memcpy invoked from the NFS reply parsing logic — specifically inside the function that handles NFS read replies (nfs_read_reply) when the code path reaches the store_block handling for NFSv3 responses. The net effect: an attacker controlling or impersonating an NFS server can craft reply packets that cause U-Boot to copy more data than a destination buffer can hold, overrunning stack or heap memory and enabling crashes or arbitrary code execution on vulnerable devices. (nvd.nist.gov)
Multiple downstream advisories and distribution trackers recorded the flaw along with remediation timelines and patched package versions; Debian, SUSE, and other distributions list the issue and provide fixed packages and backports. (security-tracker.debian.org)
How the bug works (technical explanation)
The trigger: nfs_read_reply → store_block
At a high level, the vulnerable flow occurs when U-Boot issues an NFS READ request to a server and receives a reply containing one or more data blocks. The NFS reply handling logic decodes the RPC/NFS packet and, in the code path for NFSv3, calls a helper that copies the server-provided block payload into the bootloader’s buffer via memcpy. That copy relies on a length check that — in certain edge cases — fails to bound the actual number of bytes copied, enabling the write past the intended buffer limit. (nvd.nist.gov)Two practical implementation mistakes make this scenario dangerous:
- The code performs a length comparison that is syntactically present but semantically incorrect, letting an attacker-supplied signed length be misinterpreted as a large unsigned value (integer sign issues and inadequate validation). This can turn a small or negative length into a very large copy size.
- The destination buffer’s size and the actual data length aren’t reconciled consistently across different code paths, so even a non‑maliciously large payload may slip through in certain NFS reply configurations.
Realistic exploitation model
Exploitation is straightforward in environments where U-Boot uses network boot (NFS) and receives NFS replies from an untrusted or compromised server:- An attacker who controls the NFS server can craft NFS READ replies containing malicious length fields and payloads.
- An on‑segment attacker (e.g., ARP spoofing, MitM) can impersonate or intercept NFS traffic and inject malicious replies, because U-Boot does not have the protections of a mature OS network stack.
- The attack surface includes development boards and devices that accept remote boot instructions — many devices enable NFS/TFTP for convenience during development or for diskless operation in production.
What was affected and how it was fixed
Affected versions
Upstream U-Boot releases through 2019.07 are listed as vulnerable. CPE metadata and vulnerability trackers explicitly mark all U‑Boot versions up to and including 2019.07 as in scope for CVE-2019-14198. This is a clear upstream boundary: versions released after the 2019.07 tree that include the NFS fixes are not vulnerable once the fixes are present. (nvd.nist.gov)Distribution trackers provide practical guidance about fixed package versions. For example, Debian marked the issue fixed in the 2020.01+dfsg‑1 source package and later releases; SUSE and other vendors published advisories and backports for affected product lines. Those distribution advisories are useful because many embedded and appliance vendors consume U‑Boot trees from downstream packaging rather than pulling upstream directly. (security-tracker.debian.org)
The upstream fix(s)
U-Boot maintainers accepted patches that add a correct bound check on the data length before performing memcpy in the nfs_read_reply/store_block path. The patch set fixed the missing validation and addressed related integer/length handling issues in the NFS reply parser. The upstream repository references specific commits that remediate the problem; downstream recipes and vendor trees incorporated these commits or equivalent backports. OpenEmbedded and vendor BSPs applied combined patches for a related cluster of NFS reply issues (CVE-2019-14194 and CVE-2019-14198).The patch series that backported and labeled the changes for distributions included explicit notes acknowledging the reporter and the affected functions, and they modified net/nfs.c to add the missing checks and correct the length handling. The presence of a specific commit hash and a referenced patch in distribution layers provides a clear remediation trail for integrators and sysadmins.
Severity, exploitability and real-world impact
Severity scores and interpretation
NVD assigns a high/critical severity rating for this CVE (CVSS v3: 9.8 in earlier NVD entries) with a network attack vector, low complexity, and no required privileges. Distribution security trackers vary slightly on the measured impact depending on their threat modeling, but the consensus is that this is a high‑impact remote memory‑corruption vulnerability when network boot is enabled. SUSE and Rapid7 reported it as high/critical for affected product contexts. (nvd.nist.gov)However, two qualifiers matter when assessing actual risk:
- Attack surface: the vulnerability is exploitable only if U‑Boot’s network boot (NFS) is used or if a device processes attacker-controlled NFS replies. Many production devices disable network boot by default; conversely, development boards and diskless systems commonly enable it.
- Exploit complexity: while the vulnerability itself is a straightforward unbounded copy, turning that into reliable RCE across different board configurations and memory models can require additional engineering and target knowledge. That said, many real‑world exploit scenarios for bootloaders have been straightforward enough to warrant immediate attention. (nvd.nist.gov)
Evidence of active exploitation
Public records and distribution trackers do not show widespread, confirmed active exploitation in the wild tied to this specific CVE. EPSS and exploit telemetry for older bootloader CVEs often show low public exploit rates, primarily because exploitation requires boot-stage access and specific device configurations. But the absence of widespread exploitation does not equal absence of risk; attackers frequently target unpatched embedded kit and network-facing boot services. Distribution advisories and vendor responses treated the issue seriously, issuing fixes and guidance.Who should care — and what to do now
Devices and organizations most at risk
- Manufacturers and integrators who build devices that use U‑Boot for network boot (including NFS/TFTP).
- DevOps and engineering teams that use network boot during development (Raspberry Pi, BeagleBoard, Xilinx/ARM development boards).
- Enterprises that manage fleets of network-booting appliances or diskless compute nodes.
- Users of third-party appliances whose firmware contains U-Boot 2019.07 or earlier and which expose network booting interfaces.
Immediate mitigations
- Apply upstream or distribution patches: upgrade U‑Boot to a fixed upstream commit or a distribution package that includes the CVE fixes. Debian, SUSE, and other distributors list fixed package versions and advisories. ([security-tracker.debiaty-tracker.debian.org/tracker/CVE-2019-14198))
- Disable network boot where it is not required: the simplest operational mitigation is to turn off NFS/TFTP network booting in device configs, preventing the vulnerable code paths from being used.
- Restrict network exposure to boot services: ensure NFS/TFTP services are reachable only from trusted, segmented management VLANs or via authenticated channels.
- Audit device firmware versions: identify devices that use U‑Boot and check their version strings. Many embedded vendors ship U‑Boot in their firmware; OEMs and IT administrators must ask vendors for evidence of remediation.
- Factory reset and secure update: if a device is suspected of compromise, consider a complete reset and use vendor-signed firmware update processes to reimage devices safely.
Long term and supply‑chain advice
- Treat bootloaders as critical software: include U‑Boot and other early-boot components in SBOMs (software bill of materials) and firmware inventories.
- Build secure update flows that can reflash bootloaders and verify integrity (as many devices cannot be fully remediated without vendor-supplied firmware images).
- Vendors should fast-track minimal, well-tested backports for widely deployed BSPs; end users should insist on vendor transparency about U‑Boot versions shipped in firmware. Community discussions and tracking threads underscore how downstream packaging complicates patch rollout.
Critical analysis: strengths, weaknesses and systemic lessons
Notable strengths in the response
- Upstream and downstream ecosystems responded: within weeks and months of disclosure, upstream commits and distribution advisories acknowledged and fixed the root cause; distribution packaging (Debian, SUSE) later incorporated the fixes into stable releases. The presence of tracked commits and distribution notes creates a verifiable remediation trail. (nvd.nist.gov)
- The fix was straightforward and localized: the vulnerability stemmed from a missing or incorrect bound check and was amenable to a small, audit-friendly patch rather than a large redesign.
Significant risks and weaknesses exposed
- Patch adoption lag across vendors: embedded and appliance vendors frequently lag upstream, leaving many devices vulnerable long after the upstream fix. Devices with limited or no secure update mechanism may remain exposed indefinitely.
- AttU‑Boot runs with minimal protection and often exposes services (NFS/TFTP). Small logic errors in protocol parsing produce high-impact outcomes because bootloaders lack modern mitigations found in full OSes (ASLR, DEP, KASLR on many targets).
- Attribution and detection gaps: boot-stage compromises can be invisible to typical OS-level detection and require specialized firmware integrity checks to detect post‑exploit persistence.
- The broader pattern: the CVE sits alongside several related NFS parsing CVEs (a cluster of CVE-2019-1419X issues) that demonstrate a repeating class of protocol parser errors in U‑Boot. This suggests audit gaps in code handling network protocols in boot environments and a need for defensive programming and automated analysis tools focused on early boot code.
Vulnerability disclosure and community coordination
The disclosure and remediation process illustrates both good and bad aspects of open-source security handling. On one hand, the issue was responsibly reported and tracked with CVE metadata and upstream fixes; on the other hand, the complexity of downstream packaging, vendor BSPs, and embedded product lifecycles produced a prolonged period during which devices could be exposed. Public community threads and mailing-list discussions documented both the vulnerability details and the patching work, offering a useful record for integrators.Practical guidance for Windows-focused administrators and engineers
Although U‑Boot is primarily an open‑source, Unix/Linux ecosystem component, Windows administrators can be affected indirectly by network exposure and the infrastructure that hosts NFS servers, developer workstations, and CI/CD systems:- Audit the network: look for network-subnet level Nming from developer or test segments and move these services behind management VLANs.
- Harden CI runners: ensure build servers that provide TFTP/NFS for device boot are isolated and use strong host-based controls.
- Vendor engagement: obtain firmware SBOMs and ask vendors whether firmware images include U‑Boot 2019.07 or prior; require evidence of remediation or an update plan.
- Monitor for indicators: while kernel-level IDS may not see bootloader exploits directly, watch for unusual boot-time reconfigurations, failed firmware updates, or unexpected device behavior after reboots. Community discussion threads note the difficulty of patch rollout and the tendency of some devices to remain unpatched without explicit vendor action.
Detection and forensic challenges
Because U‑Boot runs before an operating system loads, post‑compromise detection is difficult. A successful exploit at boot can:- Alter boot scripts or environment variables persisted in flash.
- Patch firmware images or create persistent backdoors into the boot flow.
- Prevent firmware updates from being applied correctly by intercepting or subverting update infrastructure.
Closing assessment
CVE‑2019‑14198 is a representative and instructive case of how a small logic error in protocol parsing — an incorrect length check guarding a memcpy — can escalate into a high‑severity remote vulnerability when it exists in early‑boot code. The technical root cause is straightforward, and the upstream fix was likewise surgical; the harder problem is operational: tracking U‑Boot versions across firmware supply chains, ensuring vendors apply backports, and securing network boot services to reduce exposure.For practitioners: prioritize inventorying firmware and network‑booting devices, apply patches or vendor-supplied updates as available, and where possible disable or isolate NFS/TFTP boot services. For vendors and integrators: treat bootloaders as critical, include them in SBOMs and patch management, and invest in secure update and recovery mechanisms that make post‑discovery remediation and distribution records provide the evidence trail for the vulnerability description, remediation commits, and packaged fixes, enabling both technical verification and practical patching plans. (nvd.nist.gov)
Quick checklist (what to do next)
- Inventory devices and firmware: identify devices using U‑Boot and check version strings.
- Patch where possible: upgrade U‑Boot to a fixed upstream commit or apply vendor firmware updates containing the patch. (security-tracker.debian.org)
- Disable network boot if unused; segment network boot services otherwise.
- Request SBOMs and remediation timelines from vendors for any device that cannot be patched immediately.
- Monitor for suspicious boot-time activity and be ready to perform a secure factory reflash if compromise is suspected.
Source: MSRC Security Update Guide - Microsoft Security Response Center