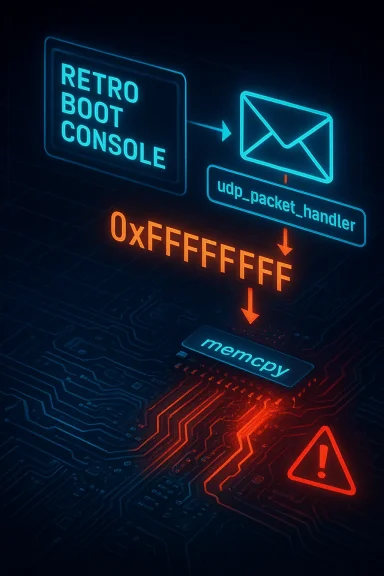
An integer underflow in the network handling code of Das U-Boot through version 2019.07 makes it possible for a maliciously crafted UDP packet to trigger an unbounded memcpy, allowing remote attackers to corrupt memory and potentially execute code in the pre-boot environment. The flaw, tracked as CVE-2019-14199, stems from a signed/unsigned arithmetic mistake in the path that processes incoming UDP payloads and hands length values to a function pointer named udp_packet_handler; the underflow produces a huge size value which is then passed to memcpy, producing an out-of-bounds copy.
U-Boot (Das U-Boot) is the ubiquitous open-source bootloader used across countless embedded devices, development boards, routers, set-top boxes, industrial appliances and other systems. Its networking stack — which supports DHCP, BOOTP, TFTP, NFS and other services — is convenient for development and network boot scenarios but also increases the security surface of devices that expose it.
In July 2019, a coordinated security review disclosed a set of vulnerabilities in U-Boot’s network and NFS handling code. Among those findings, CVE-2019-14199 describes an arithmetic underflow in the function that parses UDP packets, which permits an attacker to force a very large copy length into memcpy, resulting in an unbounded memory copy. Upstream fixes and distribution-level patches followed, and U-Boot was bumped to later releases that remedied the issue.
This article explains the vulnerability in technical terms, examines how it can be exploited in practice, evaluates risk for device owners and integrators, shows how it was fixed upstream, and offers a comprehensive mitigation and remediation plan for administrators, OEMs and security teams.
In the U-Boot case the chain looks like this, conceptually:
Distribution vendors (Debian, Ubuntu and others) applied these upstream fixes in subsequent U-Boot package versions and backported fixes for supported releases as appropriate. Typical vendor guidance recommended upgrading to patched releases (U-Boot 2019.10 or later, or distribution-specific patched packages) or applying the vendor-provided updates.
If a device cannot be updated to a patched U-Boot promptly, temporary mitigations include disabling network features in the bootloader build, or isolating devices at the network level so that U-Boot’s UDP/TFTP/DHCP/NFS functionality is not reachable by untrusted hosts.
Two ecosystem-level realities make bootloader bugs particularly consequential:
For device integrators and administrators, the key action is clear: inventory your devices, verify U-Boot versions, apply vendor or upstream updates, and minimize the attack surface by disabling unnecessary pre-boot network services. For the broader embedded ecosystem, this episode reinforces the need to treat bootloader code with the same security discipline applied to modern OS kernels and userland services: rigorous input validation, automated analysis, and a reliable update and patch distribution model.
Source: MSRC Security Update Guide - Microsoft Security Response Center
 Background
Background
U-Boot (Das U-Boot) is the ubiquitous open-source bootloader used across countless embedded devices, development boards, routers, set-top boxes, industrial appliances and other systems. Its networking stack — which supports DHCP, BOOTP, TFTP, NFS and other services — is convenient for development and network boot scenarios but also increases the security surface of devices that expose it.In July 2019, a coordinated security review disclosed a set of vulnerabilities in U-Boot’s network and NFS handling code. Among those findings, CVE-2019-14199 describes an arithmetic underflow in the function that parses UDP packets, which permits an attacker to force a very large copy length into memcpy, resulting in an unbounded memory copy. Upstream fixes and distribution-level patches followed, and U-Boot was bumped to later releases that remedied the issue.
This article explains the vulnerability in technical terms, examines how it can be exploited in practice, evaluates risk for device owners and integrators, shows how it was fixed upstream, and offers a comprehensive mitigation and remediation plan for administrators, OEMs and security teams.
How the bug works: technical overview
The vulnerable pattern: underflow -> large length -> unbounded memcpy
At the core of CVE-2019-14199 is a common, high-risk programmer error: subtracting a larger unsigned value from a smaller one (or otherwise producing a negative intermediate) and then using the result as an unsigned length. In practice this produces an integer underflow (wraparound) so the small or negative logical length becomes a very large unsigned integer.In the U-Boot case the chain looks like this, conceptually:
- A UDP packet arrives and is processed by the bootloader’s network receive path.
- The network parsing routine computes a payload length or a remaining-buffer length by subtracting header sizes or offsets — arithmetic that assumes a valid, well-formed packet.
- Due to insufficient validation, an attacker-controlled packet can make that subtraction produce a negative result; when cast or interpreted as an unsigned size, the negative value becomes a large size (e.g., 0xffffffff… for 32- or 64-bit sizes).
- That large size is passed into a handler invocation (via the udp_packet_handler pointer) and eventually into a memcpy call that copies the payload without proper bounds checking.
- The result is an out-of-bounds memory write: data from the network is copied far beyond the destination buffer and can overwrite control data, function pointers, or stack frames.
Why UDP parsing is a special risk
UDP is connectionless and lightweight; bootloaders commonly implement only minimal validation of incoming datagrams because they are intended for controlled development environments (e.g., DHCP responses, TFTP/NFS servers on the local network). That creates two concerns:- Attackers do not need to establish or maintain TCP connections or perform complex handshakes; they can send a single crafted UDP packet to trigger the bug.
- Bootloaders often assume peer-controlled or local network environments and therefore perform less strict length and sanity checks than kernel or user-space network stacks.
Where this appears in real devices
Crucially, this vulnerability is only exploitable when U-Boot is configured with networking support enabled and the offending code paths are reachable. Common scenarios where that occurs include:- Devices configured for network boot (TFTP, NFS) or firmware updates over the network.
- Development boards and test devices where U-Boot’s net stack is active by default.
- Devices exposing a management or provisioning network with U-Boot services available.
Discovery, disclosure and remediation timeline (concise)
- Security researchers examined U-Boot’s networking code and reported a group of parsing and copy issues affecting NFS and UDP handling.
- Public disclosure occurred in mid-to-late July 2019 alongside upstream communication with U-Boot maintainers.
- U-Boot maintainers published fixes in subsequent upstream commits and the project released later versions that include corrective checks. Distribution vendors integrated those fixes and released updated U-Boot packages.
- Multiple downstream advisories (distributions, security trackers) flagged CVE-2019-14199 as critical, recommended upgrades to U-Boot 2019.10 (or later security-patched builds), and issued vendor-specific guidance.
Assessing exploitability and impact
Technical impact
- The vulnerability enables remote memory corruption via an attacker-supplied UDP packet.
- Successful exploitation can produce memory overwrite beyond intended buffers, which in embedded contexts often enables:
- Arbitrary code execution in the U-Boot context (remote code execution, RCE) if control-data overwrite is possible and memory protections are absent or ineffective.
- Persistent or transient denial-of-service (crashing the bootloader, corrupting environment variables).
- Tampering with boot-time behavior that could lead to compromised images or firmware replacement.
Factors that affect practical exploitation
- Network reachability: U-Boot’s network services must be reachable from the attacker. Many devices do not expose U-Boot over the public Internet; realistic threats often require local network access or compromised LAN position.
- U-Boot configuration: Not all builds enable every network handler. If the device’s U-Boot was built with network features disabled (common in locked-down production images), the vulnerability may be unreachable.
- Hardware/compile-time mitigations: Some boards or toolchains enable stack canaries, relocation/ASLR-like techniques, or config-time protections that make exploitation harder — but bootloaders often lack full runtime hardening found in modern OS kernels.
- Availability of code-reuse gadgets: Even with memory corruption, achieving RCE may require gadgets or predictable memory layout. On small embedded systems, limited libraries or static linking might make exploitation easier or harder depending on platform.
- Vendor response: Patches and upgrades reduce risk for updated devices; however, many embedded devices do not receive bootloader updates regularly.
Realistic threat model
- For development boards, lab systems, or network-booted devices on local networks, the vulnerability is highly exploitable and should be considered an immediate security issue.
- For consumer devices where U-Boot networking has been removed or disabled in production images, the risk is lower but not negligible: misconfigured devices, recovery modes, or aftermarket modifications can re-enable vulnerable code paths.
- Attackers with local network access (e.g., malicious Wi‑Fi, compromised router) can attempt to deliver crafted UDP packets to reachable devices and attempt exploitation.
How U-Boot and distributions fixed the defect
Upstream U-Boot maintainers patched the parsing logic to ensure that integer arithmetic that produces lengths cannot underflow, and added explicit bounds checks before any memcpy operations. The fixes were small in code size but significant in impact: ensuring that computed lengths are validated as non-negative and within buffer bounds before passing them to handlers or performing copies.Distribution vendors (Debian, Ubuntu and others) applied these upstream fixes in subsequent U-Boot package versions and backported fixes for supported releases as appropriate. Typical vendor guidance recommended upgrading to patched releases (U-Boot 2019.10 or later, or distribution-specific patched packages) or applying the vendor-provided updates.
If a device cannot be updated to a patched U-Boot promptly, temporary mitigations include disabling network features in the bootloader build, or isolating devices at the network level so that U-Boot’s UDP/TFTP/DHCP/NFS functionality is not reachable by untrusted hosts.
Detection and inventory: finding affected devices
For security teams and engineers tasked with remediation, locating devices running vulnerable U-Boot versions is the first step.- Firmware / boot logs: Many U-Boot builds print a version string during boot (e.g., “U-Boot 2019.07” or similar). Collecting syslog, serial console logs, or automated boot-time telemetry can reveal U-Boot versions.
- Device manifests: OEM device management systems, build pipelines and firmware repositories often contain information about the bootloader versions shipped with particular SKUs and production runs.
- Package inventories: For Linux distributions, package management and CVE scanners will flag U-Boot packages that are vulnerable; security trackers maintained by distributions often list specific fixed package versions.
- Network scanning — with caution: Passive network monitoring can detect devices responding to bootloader-level UDP protocols. Active scanning to elicit U-Boot responses can be dangerous: it may brick or hang devices. Any active reconnaissance must be carefully tested and performed only with authorization.
Remediation and mitigation checklist
If you manage devices that may include vulnerable U-Boot builds, follow a prioritized remediation plan:- Immediate containment
- Isolate devices that expose bootloader network services from untrusted networks.
- Block UDP datagrams to and from the devices on management VLANs unless absolutely necessary.
- Disable remote access to device serial consoles from untrusted networks.
- Apply upstream or vendor patches
- Upgrade U-Boot to a patched upstream release (the U-Boot project shipped fixes post-2019.07 — 2019.10 and later include corrections).
- If you use distribution-supplied U-Boot packages, install the vendor-updated package versions released for your distribution.
- For OEM devices, check for vendor firmware updates that include the patched bootloader; apply per vendor instructions.
- Build-time mitigations (for integrators and OEMs)
- Rebuild U-Boot for production with network features disabled (CONFIG_CMD_NET, DHCP, BOOTP, NFS, TFTP) unless required.
- For devices that need networking in U-Boot, ensure the build uses conservative, audited handlers and include defensive checks.
- Consider enabling available compile-time or runtime hardening options where supported.
- Operational mitigations
- Limit network exposure of provisioning ports and restrict management networks with ACLs and segmentation.
- Use secure provisioning techniques: signed boot components and firmware verification to limit the impact of pre-OS compromise.
- Maintain an inventory of devices and their U-Boot versions for future vulnerability triage.
- For devices that cannot be updated
- Where updating firmware is impossible, document the risk and isolate devices as much as feasible.
- Use compensating controls: network segmentation, monitoring for anomalous broadcasts, and physical security.
Guidance for developers and OEMs: secure bootloader practices
This vulnerability underscores several recurring secure development themes for bootloaders and embedded firmware:- Validate all network-derived lengths: Never perform arithmetic on lengths or offsets without explicit bounds checks. Treat all network input as untrusted.
- Avoid unsafe legacy APIs: Prefer bounded-copy primitives or explicit length-checking wrappers rather than raw memcpy with calculated sizes.
- Least functionality in production: Reduce the attack surface by disabling non-essential features (e.g., network boot services) in production builds.
- Defense-in-depth: Where possible, compile with available hardening options, and combine secure boot (verified boot) and signed images to mitigate post-exploit persistence.
- Maintenance and updateability: Provide a secure and tested firmware update path so that critical bootloader fixes can be distributed to devices in the field.
- Fuzz and static analysis for pre-boot code: Bootloader code should be subjected to the same scrutiny as kernel and application code: static analyzers, fuzzing of network parsers, and code reviews.
Incident response: if you suspect exploitation
If you suspect that a device has been targeted or exploited via a U-Boot network parsing bug, take these steps:- Immediately isolate the device from networks to prevent further remote interaction.
- Preserve boot logs and serial console output for forensic analysis; these may contain indicators of abnormal behavior during the boot phase.
- If possible, extract a copy of the bootloader binary (or a device image) for offline analysis and version identification.
- Reflash the device with a patched bootloader build or a vendor-supplied firmware image, ensuring a secure update procedure.
- Review device environment variables and persistent storage for signs of tampering (e.g., altered boot commands or untrusted network boot URLs).
- Where appropriate, escalate to vendor support channels and coordinate with software maintainers for deeper analysis.
Broader lessons and ecosystem implications
CVE-2019-14199 is one of a family of vulnerabilities discovered in U-Boot’s network and NFS code during the same disclosure period. Together they highlight how long-lived, widely embedded components can accumulate security debt: bootloaders are written by skilled engineers with an emphasis on hardware bring-up and reliability, but security considerations can lag behind.Two ecosystem-level realities make bootloader bugs particularly consequential:
- Many devices with long lifecycles are rarely updated at the bootloader level. Even when distribution or upstream patches exist, practicalities (device management, user coordination, potential bricking risk) mean many devices remain unpatched for years.
- Bootloaders are executed before the OS and often run with minimal defenses, and they control the earliest stages of system integrity: a compromised bootloader can undermine any later protections.
Strengths and limitations of the public fixes
Strengths:- The upstream patching approach for this class of bugs was small and focused: validating lengths and preventing underflows eliminates the immediate exploit vector without major architectural changes.
- Distribution vendors integrated fixes and provided package updates, and many project maintainers cooperated promptly with researchers.
- The incident and public write-ups spurred improved scrutiny of network parsers and encouraged safer programming practices in bootloader code.
- A fix in U-Boot source does not automatically translate to a fixed device. Devices in the field can remain vulnerable for years if OEMs do not reflash or ship updates.
- Some boards and products intentionally keep network features in U-Boot for manufacturing or recovery — and those use cases remain high-risk if not tightly controlled.
- The root class of problems (parsing complexity, unchecked arithmetic) is pervasive; similar defects can exist in other pre-OS code and in bespoke, vendor-provided bootloaders derived from U-Boot.
- It is difficult to quantify how many deployed devices remained vulnerable after the fix, because many vendors do not publish detailed inventories or update timelines. Any statistic about in-the-wild vulnerable devices should be treated cautiously unless backed by firm telemetry.
Practical checklist for administrators (quick reference)
- Identify devices that may use U-Boot (inventory, serial logs).
- Check U-Boot version strings; flag versions up to and including 2019.07 as potentially vulnerable.
- Apply vendor firmware updates or rebuild U-Boot with fixes (2019.10+ or patched backports).
- If immediate update is impossible:
- Disable U-Boot networking features in device builds where acceptable.
- Segment and firewall management/provisioning networks to restrict UDP exposure.
- Monitor for unusual UDP traffic patterns on local networks.
- For new product designs:
- Remove or tightly gate bootloader network services in production.
- Implement authenticated, signed boot flows.
Conclusion
CVE-2019-14199 is a stark reminder that low-level firmware, and especially network-facing bootloader components, cannot be treated as peripheral to security. A simple arithmetic underflow in the UDP parsing path produced a path to unbounded memcpy — and therefore remote memory corruption — in a widely used pre-OS component. The technical fix was straightforward and effective, but the more important challenge remains operational: ensuring that upstream fixes are actually deployed across the vast and diverse fleet of embedded devices that rely on U-Boot.For device integrators and administrators, the key action is clear: inventory your devices, verify U-Boot versions, apply vendor or upstream updates, and minimize the attack surface by disabling unnecessary pre-boot network services. For the broader embedded ecosystem, this episode reinforces the need to treat bootloader code with the same security discipline applied to modern OS kernels and userland services: rigorous input validation, automated analysis, and a reliable update and patch distribution model.
Source: MSRC Security Update Guide - Microsoft Security Response Center