Mbed TLS contained a certificate‑validation bug that could let certain malformed certificates be accepted as valid — a subtle but consequential lapse in the X.509 verification logic that affected multiple branches of the library and required coordinated package updates and rebuilds across the ecosystem.
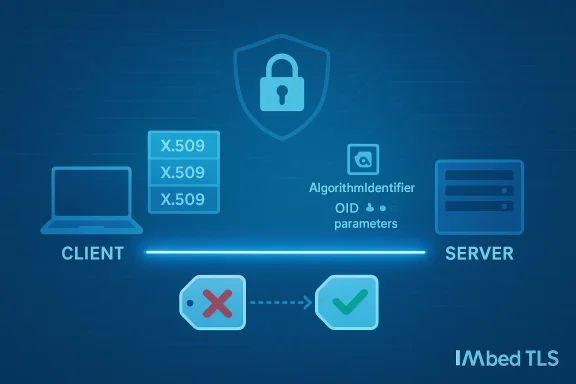
Mbed TLS is a widely used, lightweight TLS and X.509 library designed for embedded systems, IoT devices, and other constrained environments. Its certificate‑parsing and verification code is intended to implement the checks mandated by RFC 5280 and related standards, including correct handling of algorithm identifiers and their parameters in signatures.
CVE‑2020‑36478 (publicly disclosed in August 2021) describes an improper certificate validation defect in Mbed TLS where a NULL algorithm parameters entry could be misinterpreted as an array of REAL with size zero. That incorrect equivalence meant a certificate whose algorithm parameters did not match the expected form might nonetheless be treated as valid by the library — undermining the fundamental guarantee that a signature binds correctly to its algorithm context. This behavior was fixed in the mainline and supported LTS releases of Mbed TLS; operators were advised to update their deployments.
The Mbed TLS bug made the library treat a NULL algorithm‑parameters entry as equivalent to a zero‑length REAL array in some comparison codepaths. That is a misclassification at the ASN.1/tag level: two distinct encodings were treated as identical. In short, the code validated by size rather than by tag and content, which is insufficient for secure certificate validation and can let otherwise invalid signatures appear valid. Independent vulnerability trackers and vendor advisories documented this root cause and the resulting incorrect acceptance behavior.
However, residual risks remain:
The technical fix is straightforward — validate the algorithm parameters by tag and content rather than by size alone — and the Mbed TLS project, along with major distributors, implemented the necessary corrections in the releases cited above. Nevertheless, the operational work required to fully remediate an estate is often nontrivial: updating host packages, rebuilding images and static binaries, and auditing third‑party vendors all take time and coordination.
If you manage systems that consume or parse certificates, treat this CVE as a reminder to combine timely patching with disciplined supply‑chain hygiene: maintain SBOMs, scan container images, rebuild immutable artifacts, and make certificate‑validation logic part of your threat model and test suite. The underlying lesson is simple but crucial: cryptographic correctness is unforgiving — small parsing errors can produce outsized trust failures, and defenders must close both code and supply‑chain gaps to restore and preserve trust.
Source: MSRC Security Update Guide - Microsoft Security Response Center
 Background / Overview
Background / Overview
Mbed TLS is a widely used, lightweight TLS and X.509 library designed for embedded systems, IoT devices, and other constrained environments. Its certificate‑parsing and verification code is intended to implement the checks mandated by RFC 5280 and related standards, including correct handling of algorithm identifiers and their parameters in signatures.CVE‑2020‑36478 (publicly disclosed in August 2021) describes an improper certificate validation defect in Mbed TLS where a NULL algorithm parameters entry could be misinterpreted as an array of REAL with size zero. That incorrect equivalence meant a certificate whose algorithm parameters did not match the expected form might nonetheless be treated as valid by the library — undermining the fundamental guarantee that a signature binds correctly to its algorithm context. This behavior was fixed in the mainline and supported LTS releases of Mbed TLS; operators were advised to update their deployments.
Why this matters: algorithm parameters, ASN.1 tags, and trust
At the core of the problem is how ASN.1 encodings are parsed and compared when verifying a certificate signature. X.509 certificates encode the signature algorithm using an AlgorithmIdentifier structure that contains an OID and optional parameters. The exact ASN.1 tag and form of those parameters can change meaningfully between algorithm families (for example, RSA vs ECDSA vs some legacy algorithms). A correct verifier must check the presence, type, and value of those parameters — not only their length — before concluding that a signature uses the expected algorithm and parameters.The Mbed TLS bug made the library treat a NULL algorithm‑parameters entry as equivalent to a zero‑length REAL array in some comparison codepaths. That is a misclassification at the ASN.1/tag level: two distinct encodings were treated as identical. In short, the code validated by size rather than by tag and content, which is insufficient for secure certificate validation and can let otherwise invalid signatures appear valid. Independent vulnerability trackers and vendor advisories documented this root cause and the resulting incorrect acceptance behavior.
Technical analysis: what goes wrong, step by step
The mismatch: tag vs length
- An AlgorithmIdentifier has two pieces: an object identifier (OID) for the signature algorithm and an optional parameters field.
- Mbed TLS’s verification logic compared the length of the parameters in a way that could make a NULL parameters field look the same as an encoded zero‑length REAL array.
- Because the implementation relied on size checks at that point, it failed to reject a certificate when the parameters’ tag or actual content did not match the expected semantics.
Security implications
- If a certificate with a mismatched parameters encoding is accepted, that certificate could be used to impersonate a host or authorise a connection where it should have failed hostname/algorithm checks.
- The primary impact is integrity: an attacker presenting such a certificate to an unpatched client or server could pass verification checks that should have failed, opening a classic man‑in‑the‑middle (MITM) or impersonation pathway in contexts where trust relies solely on that signature validation.
- Because the vector is a network supplied certificate, the attack complexity is low when an attacker controls a server or can influence the presented certificate chain. Several vendor trackers assigned a high integrity impact and a high CVSS v3 base score (7.5) to the issue.
Affected versions and where the fix landed
The vulnerability affects Mbed TLS releases prior to the fixed releases named in advisories:- Fixed in Mbed TLS 2.25.0
- Fixed in the long‑term support branches 2.16.9 LTS and 2.7.18 LTS
Cross‑checks and evidence
To ensure this account rests on verifiable facts, the claim set above was cross‑checked against both national vulnerability repositories and multiple vendor advisories:- The U.S. National Vulnerability Database (NVD) catalogues CVE‑2020‑36478 and reproduces the canonical description of the defect and affected versions.
- Distribution security trackers such as Ubuntu’s CVE advisory and Debian’s security tracker list the same affected versions, the same technical summary, and the same remediation path (package upgrades / rebuilds). These sources confirm the fixed release numbers referenced above.
- Independent analysis pieces and vulnerability databases (Wiz, Rapid7, Vulert and others) corroborate the technical root cause (incorrect parameter tag checking) and the recommended mitigation (upgrade to fixed Mbed TLS releases).
Exploitability and real‑world risk
- Attack vector: Network — an attacker can present a crafted certificate chain during TLS handshake.
- Attack complexity: Low once an attacker can present or control the certificate (for example, a malicious server, a compromised CA, or a controlled subordinate CA).
- Primary impact: Integrity — the acceptance of a wrongly‑formed certificate undermines the binding between subject name and public key.
- Confidentiality / Availability: Not the central impact for this bug; the chief concern is impersonation/forgery rather than immediate data disclosure or DoS.
Detection: where to look in your estate
Finding whether you are affected is a combination of package inventory, binary inspection, and supply‑chain awareness. Practical, immediate checks include:- Inventory host packages:
- RPM-based systems: rpm -qa | grep -i mbedtls
- DEB-based systems: dpkg -l | grep -i mbedtls
- Inspect containers and images:
- Run a short container that lists /usr/lib, /usr/lib64, or package manifests inside the image; use image scanners (Trivy, Clair, Snyk) to enumerate packages and libraries.
- Scan for statically‑linked or vendored copies:
- Look for linked symbols or version strings embedded in binaries, or inspect language dependency manifests (go.mod, Cargo.lock, etc.) for references to mbedtls.
- Use SBOMs and vendor attestations where available:
- Consult vendor‑provided SBOMs and VEX/CSAF attestations for product artifacts; use them to narrow triage and identify images that must be rebuilt.
Remediation: how to fix it, step by step
- Upgrade Mbed TLS in all codebases and packages to at least:
- 2.25.0 (mainline), or
- 2.16.9 LTS, or
- 2.7.18 LTS
Confirm the version in package metadata or in the library version string embedded in your binaries. - Rebuild and redeploy:
- Recompile any application, library, or firmware that statically links or vendors Mbed TLS so the updated library is embedded at build time.
- Rebuild container images that included vulnerable Mbed TLS and republish them to registries; redeploy after verification.
- Apply vendor updates:
- For packaged distributions (Ubuntu, Debian, SUSE, etc.), install the vendor‑supplied security update and restart affected services if required.
- Test verification behavior:
- In staging, verify that certificate validation rejects known malformed certificates that previously would have passed.
- Run unit and integration tests exercising signature/algorithm parameter codepaths.
- Rotate keys where appropriate:
- If you have reason to suspect a compromise stemming from earlier acceptance of invalid certificates, rotate high‑value keys and credentials and inspect logs for suspicious interactions.
- Monitor and alert:
- Add telemetry for TLS acceptance anomalies (for example, successful TLS sessions where the presented certificate SAN does not match the expected host) and create alerts for unexpected certificate validations.
Short‑term mitigations and operational controls
If immediate patching is not feasible, apply compensating controls to reduce exposure:- Restrict network exposure: firewall or allowlist endpoints to prevent clients from connecting to untrusted external servers where an attacker could present a crafted certificate.
- Use application‑level hostname verification and certificate pinning on critical flows to add an extra check independent of the library’s algorithm‑parameters parsing logic.
- Isolate workloads: reduce the ability of untrusted tenants or co‑resident processes to influence celows or to intercept connections.
- Increase logging and monitoring of TLS negotiations and certificate chains to detect anomalous acceptance patterns.
Supply‑chain and ecosystem considerations
Two recurring problems complicate remediation efforts for TLS library bugs:- Many products statically embed open‑source libraries. Even if the distribution package is patched, those statically‑linked artifacts remain vulnerable until rebuilt and republished.
- Container images and firmware images are often immutable in production pipelines. Host package updates don’t modify embedded copies; rebuilding upstream artifacts is necessary.
Who should prioritize this — triage guidance
- Highest priority: network‑facing clients or services that accept server certificates from arbitrary endpoints (agents, crawlers, update fetchers, IoT devices that contact cloud endpoints).
- Medium priority: services that accept certificate inputs from semi‑trusted peers or that manipulate certificate metadata (proxies, load balancers that perform certificate parsing).
- Lower but real priority: internal tooling or build systems that embed older Mbed TLS versions, especially if those artifacts are distributed to customer environments.
Strengths of the response and remaining risks
The Mbed TLS maintainers and major distributors followed a standard remediation path: identify the root cause, publish an upstream fix, and provide patched releases and distribution updates. Vendors recorded fixed package versions and shipping timelines; many distros shipped backports for their supported branches. That coordinated approach is the right operational sequence and enables defenders to patch in a controlled fashion.However, residual risks remain:
- Immutable artifacts and third‑party binaries that were not rebuilt will continue to expose customers until vendors publish patched deliverables.
- Embedded and IoT devices with long lifecycles are sometimes slow to receive r be updated in practice.
- Automated scanning and dependency tracking are imperfect; organizations without SBOMs, image scanning, or artifact inventory will find it hard to achieve complete remediation.
Practical checklist — immediate actions (prioritized)
- Inventory all images, containers, packages, and binaries for Mbed TLS usage.
- Install vendor patches for distribution packages (apply security updates from Ubuntu/Debian/SUSE/etc.).
- Rebuild statically linked binaries and container images against patched Mbed TLS releases.
- Run negative tests in staging that present malformed algorithm‑parameter combinations to confirm rejected validation.
- Rotate keys / credentials used on hosts where unpatched Mbed TLS may have run if you suspect active misuse.
- Ingest vendor SBOMs and product attestations, and maintain a tracking dashboard for fixed vs still‑unfixed artifacts.
Final analysis and conclusion
CVE‑2020‑36478 is a classic example of how and tag/parameter handling errors can undermine certificate verification. The flaw was not a simple memory corruption; it was a validation correctness error that let incorrect encodings be treated as legitimate. That kind of defect directly affects the integrity of TLS connections and therefore requires serious, prioritized remediation.The technical fix is straightforward — validate the algorithm parameters by tag and content rather than by size alone — and the Mbed TLS project, along with major distributors, implemented the necessary corrections in the releases cited above. Nevertheless, the operational work required to fully remediate an estate is often nontrivial: updating host packages, rebuilding images and static binaries, and auditing third‑party vendors all take time and coordination.
If you manage systems that consume or parse certificates, treat this CVE as a reminder to combine timely patching with disciplined supply‑chain hygiene: maintain SBOMs, scan container images, rebuild immutable artifacts, and make certificate‑validation logic part of your threat model and test suite. The underlying lesson is simple but crucial: cryptographic correctness is unforgiving — small parsing errors can produce outsized trust failures, and defenders must close both code and supply‑chain gaps to restore and preserve trust.
Source: MSRC Security Update Guide - Microsoft Security Response Center