CVE-2022-3509 is a parsing bug in Google’s Protocol Buffers Java implementation that can be triggered by crafted text‑format messages to force excessive object churn and long JVM garbage‑collection pauses, producing a denial‑of‑service (DoS) condition in vulnerable applications; operators should treat any service that parses untrusted protobuf textformat input with the affected protobuf‑java or protobuf‑javalite versions as high priority to inventory and patch.
Protocol Buffers (protobuf) is a ubiquitous serialization format used across services, clients, and tooling. While most production flows use the compact binary wire format, protobuf also supports a human‑readable textformat that some applications accept for configuration, debugging, or management interfaces. CVE‑2022‑3509 targets that textformat parsing path in the Java runtime (both core and javalite variants) and was reported alongside a cluster of parser‑related protobuf CVEs in 2022.
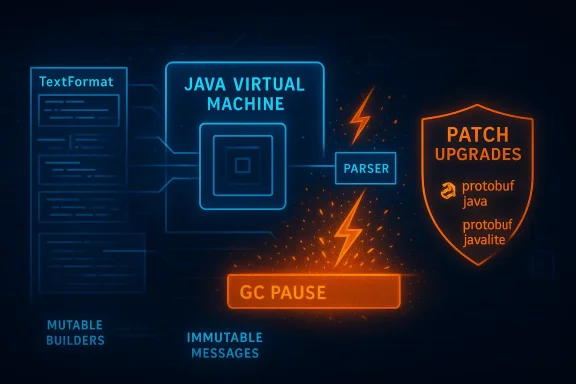
The vulnerability manifests when the TextFormat parser processes inputs containing multiple instances of non‑repeated embedded messages that themselves contain repeated or unknown fields. Under those conditions the library repeatedly converts objects between mutable and immutable internal representations. That thrashing drives sustained allocations and deallocations which, in typical long‑running JVM processes, cause prolonged garbage collection pauses — effectively denying availability to the application even though no memory corruption or integrity breach occurs. The issue is operationally a resource‑exhaustion DoS, not an RCE or data‑integrity flaw.
Practical guidance:
--g verification in large estates (Windows & Azure contexts)
WindowsForum readers commonly run mixed estates and cloud workloads. In addition to direct application upgrades, follow these enterprise steps:
Threat intelligence and vendor tracking at disclosure time did not show widespread in‑the‑wild exploitation for this specific CVE, but that absence should not be interpreted as low urgency. Parser‑driven resource exhaustion is a straightforward and attractive attack for adversaries seeking to disrupt services, and similar parser bugs (different CVEs across languages and libraries) have been weaponized in targeted outages. Treat the vulnerability according to your asset criticality and exposure profile. ([wiz.io](CVE-2022-3509 Impact, Exploitability, and Mitigation Steps | Wiz analysis: strengths, limits, and residual risks
For WindowsForum readers: prioritize visibility and SBOMs across both on‑prem Windows workloads and Azure images, treat vendor attestation as a helpful but not exhaustive signal, and add parsing‑centric telemetry (GC pause monitoring, request size/rate alarms) to your standard incident detection playbook. The combination of prompt patching and pragmatic defensive controls will neutralize the practical risk from CVE‑2022‑3509 while reducing exposure to future parser‑driven availability vulnerabilities.
Source: MSRC Security Update Guide - Microsoft Security Response Center
 Background / Overview
Background / Overview
Protocol Buffers (protobuf) is a ubiquitous serialization format used across services, clients, and tooling. While most production flows use the compact binary wire format, protobuf also supports a human‑readable textformat that some applications accept for configuration, debugging, or management interfaces. CVE‑2022‑3509 targets that textformat parsing path in the Java runtime (both core and javalite variants) and was reported alongside a cluster of parser‑related protobuf CVEs in 2022.The vulnerability manifests when the TextFormat parser processes inputs containing multiple instances of non‑repeated embedded messages that themselves contain repeated or unknown fields. Under those conditions the library repeatedly converts objects between mutable and immutable internal representations. That thrashing drives sustained allocations and deallocations which, in typical long‑running JVM processes, cause prolonged garbage collection pauses — effectively denying availability to the application even though no memory corruption or integrity breach occurs. The issue is operationally a resource‑exhaustion DoS, not an RCE or data‑integrity flaw.
Technical anatomy: what actually goes wrong
How TextFormat parsing normally behaves
TextFormat parsing builds message objects from a line‑oriented, human‑readable representation by creating sub‑message instances and merging fields into their parent message. To be efficient, protobuf implementations often use mutable builder objects while parsing, then convert those builders into immutable message instances for storage and use. This strategy minimizes defensive copying for normal inputs.The root cause: repeated mutable↔immutable conversions
CVE‑2022‑3509 arises from a pathological combination of input shapes: multiple occurrences of a sub‑message field that the protobuf schema marks as non‑repeated (single cardinality), where the contained sub‑message carries repeated fields (or protobuf unknown fields). The parser’s current logic recreates a new sub‑message and merges it into the existing field rather than updating the existing mutable builder in place. Each merge forces the runtime to convert between mutable and immutable representations repeatedly. On a large or intentionally crafted input, this leads to a high rate of allocation and deallocation, which produces long GC pauses in the JVM and reduces or eliminates application responsiveness.Why this causes Denial of Service
The JVM garbage collector is optimized for normal allocation patterns; when an application suddenly produces a torrent of short‑lived objects, GC activity spikes and pauses can grow from milliseconds to seconds or longer depending on heap size and GC configuration. For latency‑sensitive services (APIs, ingress proxies, real‑time pipelines), these pauses translate directly into unavailable service endpoints, timeouts, and user‑visible outages. Vendors who analyzed the bug characterized it as a CWE‑400 uncontrolled resource consumption vulnerability with clear availability impact.Affected versions and remediation timeline
Google and downstream trackers converged on the same set of fixed versions: protobuf‑java and protobuf‑javalite versions prior to 3.21.7, 3.20.3, 3.19.6 and 3.16.3 are vulnerable, and the corresponding patched releases should be used. Vendors and vulnerability databases recommend upgrading to those fixed versions or later as the primary remediation.Practical guidance:
- If yourrotobuf dependency (Maven coordinates like com.google.protobuf
 rotobuf-java or protobuf-javalite), ensure the resolved version is at or above the patched release for your major line.
rotobuf-java or protobuf-javalite), ensure the resolved version is at or above the patched release for your major line. - If you consume third‑party binaries (containers, platform images, SDKs) that bundle protobuf, verify the bundled protobuf version via SBOMs, package manifests, or inside‑image package lists. Microsoft and other vendors publish attestation and vendor advisories for affected product artifacts; do not assume a vendor statement about one product implies safety for all artifacts.
Where you are likely to be exposed (attack surface)
Not all protobuf users are exposed. The exploit vector is specific: an attacker must be able to supply crafted textformat protobuf inputs to a vulnerable parser. Common exposure patterns include:- Administrative or diagnostic endpoints that accept textformat payloads for configuration or debugging.
- Management interfaces and CLIs that accept pastable textformat messages.
- Log ingestion or telemetry pipelines that parse human‑readable protobuf dumps submitted by clients.
- Internal microservices that unintentionally accept textformat input because they expose a protobuf parsing library without explicit input validation.
Detection and hunting: how to spot probable exploitation or exposure
Detection focuses on two classes of telemetry: JVM resource signals and anomalous parsing inputs.- JVM signals to monitor:
- Repeated long GC pause events (G1 or CMS logs), particularly correlated with spikes in request rates.
- Rapid increases in CPU and heap allocation rate on processes that normally exhibit steady memory behavior.
- Thread dumps showing stalled request‑handling threads waiting for GC to complete.
- Application signals to monitor:
- Unusually large or repetitive textpayloads submitted to endpoints that accept protobuf-ish input.
- Error traces in server logs around parsing, builder merges, or unexpected InvalidProtocolBufferException traces.
- Network telemetry showing repeated similar POST/PUT payloads from the same client IPs.
- Instrument GC logging and pipe GC pause histograms into your observability pipeline; alert on pause percentiles exceeding normal baselines.
- Search logs for TextFormat entry points or for endpoints that include “text” or “TextFormat” in messages.
- For public endpoints, look for a sudden rise in long, line‑oriented POST payloads that contain repeated sub‑message markers — these are suspicious.
Immediate miton checklist
If you identify potential exposure in your environment, prioritize as follows:- Patch: upgrade protobuf dependencies to the fixed releases listed earlier (≥ 3.21.7 / 3.20.3 / 3.19.6 / 3.16.3 depending on branch). This is the definitive fix.
- Inventory: enumerate artifacts that may carry vulnerable protobuf jars:
- Maven/Gradle dependency trees (mvn dependency:tree, gradle dependencies).
- Container images: generate SBOMs (Syft, CycloneDX) and inspect for protobuf jars.
- Platform images and vendor artifacts: verify vendor attestation entries and package lists rather than assuming everything is up to date. Microsoft emphasizes product‑scoped attestations and recommends artifact‑level verification where no attestation exists.
- Short‑term controls when patching is delayed:
- Reject or canonicalize textformat input at the edge. Prefer accepting only the binary wire format where feasible.
- Apply rate limits and request size limits on endpoints that accept textual payloads.
- Place a WAF or API gateway rule to block unusually repetitive or oversized multipart text messages.
- Harden JVM process limits (container memory caps) to prevent a single process from destabilizing a whole host.
- Test and deploy: once upgraded, thoroughly test parsing paths with both normal and malformed textformat inputs to ensure the fix behaves as expected.
- Rebuild artifacts: for Java, redeploying with updated dependency versions is typically sufficient. For compiled images or vendor‑supplied bundles, you may need to rebuild images or apply vendor patches and redeploy. ]
Hardening: defensive engineering beyond patching
Upgrading fixes the known code path, but engineering teams should treat parsing code as a sustained risk surface. Recommended hardening:- Prefer binary protobuf for network APIs and reserve textformat for local debug tools only.
- Lid schemas on public endpoints; validate messages against expected shapes and reject unexpected fields early.
- Apply strict input validation: reject embedded messages when you expect scalars, limit repeated field lengths, and enforce maximum nesting depths.
- Add per‑request CPU and memory quotas where your platform allows (container limits, cgroups).
- Add cardinality guards and canonicalization where textual values become labels or metrics to avoid resource exhaustion via label explosions.
--g verification in large estates (Windows & Azure contexts)
WindowsForum readers commonly run mixed estates and cloud workloads. In addition to direct application upgrades, follow these enterprise steps:
- Asset discovery: run package scans inside Windows‑based container images and Linux host images to list Maven/JAR artifacts that include protobuf. Use tools that can inspect JAR manifests and Maven coordinates in built images.
- SBOMs for images and ars for third‑party images and vendors. Where vendors publish VEX/CSAF attestations (Microsoft has begun publishing product‑scoped attestations), use those attestations as a starting point but always verify artifacts you actually run. Microsoft’s product attestation approach is useful but explicitly product scoped — absence of an attestation does not equal absence of the library.
- CI/CD hygiene: ensure your Maven or Gradle builds pin dependency versions or use dependence locks; avoid open ranges that silently update to vulnerable or unexpected transitive libraries.
- Rebuild static bundles: if you distribute or run prebuilt agent binaries or fat jars that embed dependencies, rebuild them with patched dependencies and redeploy. Static artifacts compiled with older dependencies remain vulnerable even after host package updates.
Exploitability, threat model and real‑world risk
CVE‑2022‑3509 is a remote DoS in typical deployment models because an attacker only needs to supply crafted textformat input to any exposed parser that accepts it. However, practical exploitation requires that the application actually parses textformat input from untrusted clients; many production systems do not expose textformat parsing in public APIs, which reduces exposure.Threat intelligence and vendor tracking at disclosure time did not show widespread in‑the‑wild exploitation for this specific CVE, but that absence should not be interpreted as low urgency. Parser‑driven resource exhaustion is a straightforward and attractive attack for adversaries seeking to disrupt services, and similar parser bugs (different CVEs across languages and libraries) have been weaponized in targeted outages. Treat the vulnerability according to your asset criticality and exposure profile. ([wiz.io](CVE-2022-3509 Impact, Exploitability, and Mitigation Steps | Wiz analysis: strengths, limits, and residual risks
What’s good about the response to CVE‑2022‑3509
- The fix is surgical and versioned: upstream protobuf maintainers shipped patches and maintainers of downstream distributions published fixed package versions. Operators can remediate by upgrading to well‑defined releases.
- The vulnerability clas it’s an availability issue rooted in allocation patterns rather than memory corruption, so detection strategies (GC telemetry, rate limits) are effective mitigations.
What remains risky or uncertain
- Transitive dependency and supply‑chain exposure: many applications include protobuf indirectly; spotting every vulnerable consumer requires SBOMs and container scanning. Static, prebuilt artifacts remain a critical residual risk until l defaults: many systems keep debugging helpers or textformat acceptance enabled by default; operators may be unaware of these paths, increasing blind spots.
- Vendor attestation confusion: vendor advisories that attest a particular product as affected — for example Microsoft’s statements on specific product images — ct‑scoped; defenders must still perform artifact scans for other vendor artifacts rather than assuming safety.
Unverifiable claims and cautions
- Public exploit availability: at time of this writing, public proof‑of‑concept exploits were not widely reported. That absence cannot be taken as evidence of safety — attackers can privately weaponize parser bugs faster than public disclosure. Treat the PoC status as a live variable and monitor threat feeds. ([resos://www.resolvedsecurity.com/vulnerability-catalog/CVE-2022-3509)
Practical playbook: step‑by‑step for operators (priority order)
- Inventory: run dependency trace commands and SBOM generation across images and services to find protobuf artifacts. (mvn dependency:tree, gradle dependencies, Syft for images).
- Patch libraries: upgrade com.google.protobuf
 rotobuf‑java and protobuf‑javalite to the patched releases as soon as possible.
rotobuf‑java and protobuf‑javalite to the patched releases as soon as possible. - Rebuild static artifacts: rebuild fat jars and container images with updated dependencies and redeploy to replace any statically linked vulnerable code.
- Short‑term Defense: apply WAF/API gateway rules to block or throttle textformat payloads and impose request size and rate limits.
- Monitor: enable GC logging, add alerts for GC pause percentiles, and monitor application logs for parsing errors or repeated similar payloads.
- Long term: integrate fuzz testing for parser inputs into CI, require SBOMs for third‑party images, and instrument cardinality and allocation metrics in production.
Conclusion
CVE‑2022‑3509 is a sober reminder that parsing code — especially code that accepts human‑readable formats — remains a persistent attack surface. The bug itself is not a headline‑grabbing remote code execution; it is a reliable, low‑complexity path to disrupt availability by exploiting allocation and GC behavior in the JVM. The fix is straightforward: upgrade to the patched protobuf Java releases, inventory and rebuild artifacts that bundle vulnerable libraries, and harden parsing endpoints so that textformat inputs are either not accepted or strongly validated.For WindowsForum readers: prioritize visibility and SBOMs across both on‑prem Windows workloads and Azure images, treat vendor attestation as a helpful but not exhaustive signal, and add parsing‑centric telemetry (GC pause monitoring, request size/rate alarms) to your standard incident detection playbook. The combination of prompt patching and pragmatic defensive controls will neutralize the practical risk from CVE‑2022‑3509 while reducing exposure to future parser‑driven availability vulnerabilities.
Source: MSRC Security Update Guide - Microsoft Security Response Center