NASM users and maintainers should treat CVE‑2022‑46456 as a live, unresolved memory‑safety issue: Netwide Assembler (NASM) v2.16 contains a global buffer overflow in the dbg output code (function dbgdbg_typevalue in /output/outdbg.c) that can crash the assembler and, depending on circumstances, may be harnessed for more serious memory‑corruption outcomes. (bugzilla.nasm.us)
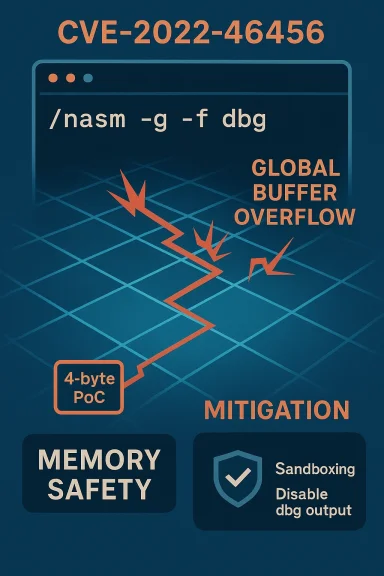
NASM (the Netwide Assembler) is a long‑lived, widely used assembler for x86/x86‑64 development workflows, build systems, and low‑level toolchains across Linux distributions, CI pipelines, and developer desktops. The flagged defect is tracked as CVE‑2022‑46456 and was publicly recorded in early January 2023 after an upstream bug report and an AddressSanitizer proof‑of‑concept were published. The defect is a global buffer overflow in the debug‑output path and is specifically triggered when NASM is asked to emit debug tracing using the dbg output format (the assembler flags involved are the debug generation options such as -g combined with -f dbg). (bugzilla.nasm.us)
Security databases and distribution trackers treat the vulnerability differently: some trackers list a High impact rating (CVSS 3.x 7.8 as reported by several aggregators), while vendor or distro assessments sometimes consider the practical impact more modest (CVSS 3.x values of 6.1 appear in other feeds). The divergence reflects real uncertainty about whether the overflow can be turned into reliable code execution, or whether the practical effect is an immediate crash / denial‑of‑service when processing crafted input.
Key technical takeaways:
Source: MSRC Security Update Guide - Microsoft Security Response Center
 Background / Overview
Background / Overview
NASM (the Netwide Assembler) is a long‑lived, widely used assembler for x86/x86‑64 development workflows, build systems, and low‑level toolchains across Linux distributions, CI pipelines, and developer desktops. The flagged defect is tracked as CVE‑2022‑46456 and was publicly recorded in early January 2023 after an upstream bug report and an AddressSanitizer proof‑of‑concept were published. The defect is a global buffer overflow in the debug‑output path and is specifically triggered when NASM is asked to emit debug tracing using the dbg output format (the assembler flags involved are the debug generation options such as -g combined with -f dbg). (bugzilla.nasm.us)Security databases and distribution trackers treat the vulnerability differently: some trackers list a High impact rating (CVSS 3.x 7.8 as reported by several aggregators), while vendor or distro assessments sometimes consider the practical impact more modest (CVSS 3.x values of 6.1 appear in other feeds). The divergence reflects real uncertainty about whether the overflow can be turned into reliable code execution, or whether the practical effect is an immediate crash / denial‑of‑service when processing crafted input.
The technical facts: what is broken, and how
Where the overflow lives
The root cause sits inside the dbg output backend in NASM’s source tree — file output/outdbg.c, function dbgdbg_typevalue. The original bug report includes an AddressSanitizer (ASan) trace showing an out‑of‑bounds read at line 459 of outdbg.c; the ASan trace demonstrates the read landing 16 bytes to the right of a global array namedtypes and 16 bytes left of another global dbgdbg_pragma_list, which confirms the bug is a global buffer overflow rather than a heap or stack overflow. The upstream bug report also included a minimal fuzzer‑reduced proof‑of‑concept file (a 4‑byte test case) that reliably triggers the ASan abort when NASM is built with sanitizers. (bugzilla.nasm.us)Key technical takeaways:
- The overflow is triggered inside the code path that formats or interprets debug information for the dbg back end.
- The PoC is extremely small and was produced via fuzzing + afl‑tmin, suggesting a parsing boundary or unchecked copy in a parser/formatter function.
- The crash is reproducible in instrumented builds (ASan). The reported crash trace shows the assembler fails during normal file assembly when debug output is enabled. (bugzilla.nasm.us)
Practical exploitation considerations
Memory corruptions break down into a few exploitability categories. This vulnerability’s characteristics point to two realistic outcomes:- Deterministic denial‑of‑service (DoS): the assembler crashes when presented with crafted input that exercises the dbg output path. For environments that run NASM automatically on untrusted inputs (for example, automated packaging, containerized file conversions, or public build services that accept custom assembly snippets), a remote or local attacker who can place a crafted file where NASM will assemble it could force repeated crashes. Many scanners and distro notices emphasize the DoS/availability angle.
- Potential memory corruption beyond a simple crash: the overflow is global and adjacent to other globals; in principle it can overwrite neighboring data structures. Several vulnerability assessments list arbitrary code execution as a possible impact if an attacker can control memory layout precisely and chain the overflow into a control‑flow hijack. However, public evidence of a reliable RCE (remote code execution) exploit is not present in vendor tickets or mainstream vulnerability trackers; the bug report only shows an ASan abort and a PoC crash. That gap is why some trackers give different CVSS scores and why several distros describe the issue as a crash with limited security impact.
Scope and affected systems
- Affected upstream: NASM v2.16 (the public advisory language references the v2.16 series). OSV and NVD entries list v2.16 as impacted; the upstream Git history shows the vulnerable code present across multiple commits in that time frame.
- Distribution status: many popular Linux distributions and scanners have entries for CVE‑2022‑46456. Some distributions and vulnerability feeds note the issue as unfixed in packaged builds or declare the package will not be patched due to limited security impact, creating an operational problem for downstream maintainers. Debian tracker notes the bug and includes the upstream bugzilla link with an annotation suggesting the crash is in a CLI tool and may not constitute a severe security impact for all users; other feeds (Ubuntu, Amazon Linux, Tenable) list higher severity and treat packages as pending fixes or unpatched. This split means administrators must check their distribution’s specific advisory and package version to decide whether they're considered vulnerable in that packaging context.
- Common deployment patterns that matter:
- Local developer machines where NASM is used interactively (lower risk unless untrusted inputs are assembled).
- Continuous integration (CI) and automated build systems that accept external contributions or process third‑party assembly artifacts (higher risk when the build system runs NASM on incoming or untrusted data).
- Packaging and distribution pipelines that build packages from upstream sources and may run NASM as part of automated processing steps.
- Toolchains and third‑party products that embed NASM or call it as part of a service (for example, some cross‑compilers or binary translation steps).
Conflicting assessments: crash vs. code execution
Public records show two competing but both credible assessments:- Crash‑focused view — several distro trackers and bug comments treat the issue as a reliability bug: the assembler crashes but cannot be easily turned into a privilege‑escalating remote exploit because NASM runs as a local CLI tool and the debug path is not always enabled in production use. Debian’s tracker includes a note summarizing the situation as “Crash in CLI tool, no security impact” in the packaged context used by Debian.
- Memory‑corruption/remote‑impact view — security vendors and vulnerability databases emphasize that a global buffer overflow adjacent to other globals is a dangerous memory‑corruption primitive and may be converted into arbitrary code execution in a forgiving environment (for example, where ASLR/dep are absent or the attacker can control memory layout); some vulnerability summaries explicitly list RCE as a possible impact if exploitation techniques are successful. The upstream PoC and ASan trace prove the overflow exists and is trivial to trigger in instrumented builds.
Vendor response and upstream status
- The upstream bug is recorded in NASM’s Bugzilla (bug 3392814) and was reported with a minimal PoC and ASan evidence. The bug entry remains open with no upstream patch attached in that tracker entry; the initial report dates to October 2022 and the CVE mapping appeared publicly in January 2023. That timeline suggests disclosure followed responsible reporting, but an upstream fix was not merged at the time the tracker snapshot was taken. (bugzilla.nasm.us)
- Distribution handling is asymmetric: some distros have chosen not to ship a fix (or to deem the package non‑critical in their environment), while security scanners flag installed NASM packages as vulnerable or pending. Several scanner plugins and advisories explicitly list “no vendor fix available” or “package will not be patched” as the remediation status, which places operational responsibility on packagers and end users.
- Community discussion: open forums and vulnerability roundups picked up the CVE and emphasized both the small PoC and the need to consider where NASM runs — automated build servers and CI runners are highlighted as realistic attack surfaces where an attacker might provide a malicious assembly file to cause a crash. Community threads archived in internal forum exports show similar patterns of debate about impact and patch responsibility.
Risk analysis: who should care most
- High‑sensitivity targets: any automated system that runs NASM as part of processing untrusted inputs — public CI, automated packaging systems, online compilers, build servers that accept external contributions. Attackers can use a trivial input (PoC was 4 bytes) to trigger the bug if the dbg output path is engaged; the crash can stop or interrupt builds and could cascade into supply chain disruption. (bugzilla.nasm.us)
- Desktop developers: lower immediate risk provided the developer does not assemble untrusted files with debug tracing enabled. However, developers running automated scripts that process third‑party code should treat NASM as any other tool in their CI chain and apply defensive controls.
- Packagers and distribution maintainers: because some distributions have not yet applied or shipped fixes, maintainers should make an explicit decision: either ship a patched NASM package (if a backport/fix exists) or document the reasoning for not patching (for example, if the packaged configuration disables the dbg path, or if the package is marked low‑risk by the distro’s security policy). Several trackers currently show varying statuses; packagers should follow their distribution’s security governance.
Mitigations and practical guidance
This vulnerability has no single universal “fix” that applies across all environments; the appropriate steps depend on how NASM is used in your organization. Below are prioritized, actionable mitigations.Immediate (minutes to hours)
- Inventory: locate where NASM is installed and which versions are in use (both in developer environments and in CI/build hosts). Prioritize public or multi‑tenant build infrastructure and packaging hosts. Use package manager queries, container images, and CI job logs to identify invocations of nasm. This is critical because the exploitability depends on whether NASM runs in risky contexts.
- Block untrusted inputs: stop running NASM on input from untrusted sources. For example, block or quarantine contributions or inputs that come from outside trusted repositories until you can verify NASM usage is safe. If your CI system processes untrusted pull requests by running a full build that invokes NASM, change the workflow to run a security‑sanitized build instead.
- Disable debug output in automated runs: avoid invoking NASM with debug output options (e.g., do not use -f dbg or debug tracing in automated processes that process external artifacts). If your pipeline unconditionally enables debug generation, make it configurable and default to disabled for untrusted inputs. The vulnerability critically depends on the dbg back end being exercised.
- Containerize and sandbox: run NASM inside least‑privilege containers (unprivileged containers, seccomp profiles, or restricted sandboxes) so that a crash or exploited process cannot affectbuild systems, isolate per‑job containers and limit their filesystem/network access. This reduces blast radius even if code execution were possible.
Short term (days)
- Monitor upstream and distro advisories: check upstream NASM issue trackers and your distribution’s security tracker for patches or mitigations; subscribe to CVE and distro security mailing lists to receive updates. Because distributions vary in response, verify the actual package contents (e.g., whether the dbg format code is compiled/installed in your build of NASM). (bugzilla.nasm.us)
- Rebuild with hardening: where feasible, rebuild NASM from source with compiler hardening flags (FORTIFY_SOURCE, PIE, stack protection, RELRO) and consider applying a conservative patch to guard the dbg parsing path. That is a stopgap and requires QA; do not deploy untested binary patches into production without validation.
- Use runtime detection: add AddressSanitizer or similar memory‑sanitizing builds into CI for packages that ship NASM or for critical consumer software that embeds NASM. While ASan is not a production remedy, it helps triage and confirm exploitability during forensic analysis. (bugzilla.nasm.us)
Medium / long term (weeks to months)
- Patch upstream and downstream: if upstream publishes a fix, apply it to all affected packages and backport to stable branches. If the upstream remains unresponsive, maintainers should either remove the dbg back end from packaged builds (if feasible) or disable it by default and document the reason. Distribution maintainers must coordinate to avoid confusing statuses where some distros are patched and others are not.
- Reduce attack surface in CI: architects should adopt a principle of not executing arbitrary downstream tools on untrusted inputs; for example, run static checks and sandboxed emulations instead of fully executing language toolchains on contributions from unknown sources. This vulnerability is a textbook demonstration of why build farms should treat assembler and compiler invocations as untrusted code execution opportunities.
- Hardening and code review: upstream source maintainers should add static analysis and fuzzing harnesses to the debug output path and audit the code paths that parse or format debug metadata. The bug was discovered via fuzzing; integrating continuous fuzzing for assembler front ends and output back ends will help catch regressions. (bugzilla.nasm.us)
What defenders often miss
- Assume CLI tools are always innocuous: many operations assume assemblers and compilers are only used by trusted developers. When those tools are wired into automation (e.g., pluginable online compilers, submission systems, packaging servers) they become high‑value attack surfaces. This CVE is a reminder to treat toolchain binaries with the same threat model as any network‑accessible service when they run on hosted infrastructure.
- Watch the configuration: the vulnerability depends on the dbg output code path; if a packaged NASM build or an installed configuration never enables that feature, the practical exposure might be low. But that assumption must be verified from package contents and build flags, not assumed.
- Patching inertia: when upstream fixes are slow or maintainers deem an issue low priority, downstream distributions may either not patch or adopt divergent policies; operators who rely on packaged assets must perform their own risk assessment and not assume uniform handling across ecosystems. Several vulnerability scanners explicitly mark this CVE as “no vendor fix available” or “pending”, so the burden rests with administrators.
Conclusion and recommended next steps
CVE‑2022‑46456 is a credible global buffer overflow in NASM’s debug output code. The proof‑of‑concept and ASan evidence in the upstream bug report remove doubt that an overflow exists; the open question is whether that memory corruption can be turned into a dependable remote code execution primitive in typical deployment scenarios. Until that question is resolved, defenders must treat the issue conservatively:- Immediately inventory where NASM runs in your environment, with highest priority on multi‑tenant CI, build servers, and packaging infrastructure.
- Avoid running NASM on untrusted inputs and disable debug output (dbg back end) in automated processes.
- Isolate NASM invocations with containers or sandboxes and ensure process hardening and privilege restrictions.
- Track upstream and distribution advisories for an actual code fix; when a patch is published, test and roll it out promptly.
- If you operate distribution packages, decide whether to ship a patched build, disable the dbg back end, or document residual risk to downstream users.
Source: MSRC Security Update Guide - Microsoft Security Response Center