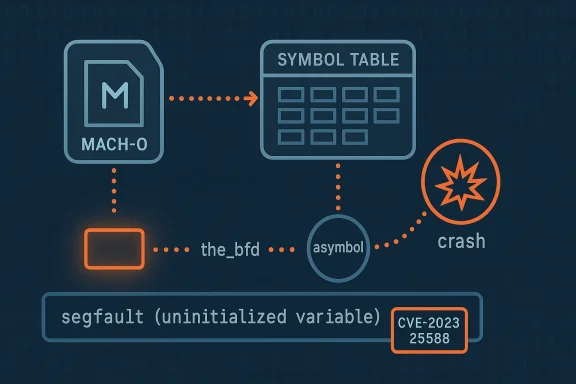
A subtle, low-level memory bug in the GNU Binutils BFD library — an uninitialized field named the_bfd inside the
Binutils is an essential suite of binary utilities that underpins toolchains across Linux distributions and embedded toolchains. At the heart of many Binutils features is BFD (Binary File Descriptor library) — the abstraction layer that lets tools open and inspect object files in many formats (ELF, Mach‑O, PE, etc.). BFD exposes a number of structures for symbols and sections;
CVE‑2023‑25588 arises from a code path that builds a synthetic symbol table for Mach‑O files: the function
How BFD,
From an operational perspective, however, availability is often the most consequential property in production systems. If a CI runner, automated build pipeline, or on‑device diagnostic service automatically invokes Binutils on attacker‑controlled or third‑party Mach‑O files, the attacker can repeatedly trigger crashes to:
Source: MSRC Security Update Guide - Microsoft Security Response Center
asymbol structure when handled by bfd_mach_o_get_synthetic_symtab — can cause commonly used tools (objdump/readelf/strip/etc.) to crash when they process crafted Mach‑O objects, producing a local denial‑of‑service. The vulnerability, tracked as CVE‑2023‑25588, is not an elegant remote takeover but it is a practical, real‑world reliability and supply‑chain hazard for environments that parse untrusted object files or run automated processing of third‑party binaries.
 Background
Background
Binutils is an essential suite of binary utilities that underpins toolchains across Linux distributions and embedded toolchains. At the heart of many Binutils features is BFD (Binary File Descriptor library) — the abstraction layer that lets tools open and inspect object files in many formats (ELF, Mach‑O, PE, etc.). BFD exposes a number of structures for symbols and sections; asymbol is one such structure used for representing symbols. An uninitialized or mishandled field within these structures can produce undefined behavior when code paths assume the field contains a valid pointer.CVE‑2023‑25588 arises from a code path that builds a synthetic symbol table for Mach‑O files: the function
bfd_mach_o_get_synthetic_symtab. In certain code paths that construct symbols, the the_bfd field of an asymbol instance can remain uninitialized. When later code dereferences or otherwise depends on that field, the result is undefined behavior that manifests as a crash — a denial‑of‑service in practical terms. This class of flaw maps to CWE‑457: Use of Uninitialized Variable.What exactly is broken (technical overview)
How BFD, asymbol, and synthetic symtabs relate
- BFD provides a common API so tools like
objdump,readelf,nm, and linkers can operate on multiple object formats. asymbolis the BFD internal representation of a symbol; it carries fields such as name, section, value, and an associated BFD pointer (here,the_bfd).- The Mach‑O synthetic symbol table creation routine attempts to synthesize symbol entries when certain Mach‑O constructs are present;
bfd_mach_o_get_synthetic_symtabis the routine that does this work for Mach‑O support.
the_bfd remains uninitialized on a constructed asymbol, later code that assumes it points to a valid bfd structure may dereference it. On modern platforms that leads to crashes, process termination, and therefore service interruption. The practical impact is availability loss for any process or automation step that invokes Binutils on a crafted Mach‑O file.Conditions required for a crash
- The vulnerable code path is exercised when Binutils is built with Mach‑O support and then asked to parse a Mach‑O object that triggers the synthetic symtab creation path.
- Exploitation is local: an attacker must get the target process or user to cause Binutils to load or inspect the crafted Mach‑O file (for example, by giving the file to a developer, CI job, or automated in‑house analysis system).
- The vulnerability causes crashes (availability loss) rather than remote code execution according to multiple public advisories; confidentiality and integrity impacts are assessed as none in published tracking databases.
Affected versions and scope
- The weakness is present in GNU Binutils releases that include the affected Mach‑O code path. Public trackers list Binutils 2.40 and derivative distribution package versions as affected, and multiple distributions issued fixes or backports.
- Debian’s tracker marks older releases as vulnerable and shows which Debian release branches received fixes; Ubuntu’s security notice lists fixed package versions for supported releases.
- Not every installation of binutils is affected in practice. A build of Binutils that omits Mach‑O support, or a Linux system that never processes Mach‑O files, will not exercise the faulty path. That said, many distributions build Binutils with broad file‑format support by default, and developer toolchains in multi‑platform projects often do encounter Mach‑O artifacts (for mobile, macOS CI, or embedded cross‑toolchains).
Severity, exploitability, and real‑world impact
What the CVE says vs. what it means for you
Public vulnerability trackers describe this as a flaw that “may lead to an application crash and local denial of service.” That maps to a medium‑severity operational risk in most CVSS mappings (Ubuntu’s security pages record a CVSS 3.x base score in the mid 5.0 range), because the issue is local and does not, by itself, yield code execution or data theft.From an operational perspective, however, availability is often the most consequential property in production systems. If a CI runner, automated build pipeline, or on‑device diagnostic service automatically invokes Binutils on attacker‑controlled or third‑party Mach‑O files, the attacker can repeatedly trigger crashes to:
- Disrupt continuous integration and deployment pipelines (preventing builds).
- Cause developer toolchains or debug services to fail when analyzing third‑party artifacts.
- Fill up monitoring noise and force manual troubleshooting that diverts engineering time.
Attack surface and likelihood
- Attack vector: Local (AV:L) — an attacker must cause a vulnerable binutils‑using process to open a crafted Mach‑O file. This often means social engineering (getting a user to inspect a malicious attachment), or baiting CI/build infrastructure with crafted artifacts.
- Privileges required: None (the vulnerable tool typically runs with the invoking user’s privileges).
- User interaction: Required — the user or an automated process must run the tool on a malicious file.
- Exploit difficulty: Low to medium — crafting malformed object files to exercise BFD synthetic symbol logic is nontrivial for casual attackers but is trivial for researchers and determined adversaries who already craft malformed binaries for fuzzing and exploitation.
Patches, vendor responses, and distribution status
Multiple distributions included CVE tracking and pushed fixes:- Debian lists the CVE and shows fixed package uploads for bookworm and later snapshots; the tracker points to a binutils commit where the patch was introduced. The Debian tracker also notes the underlying Sourceware bug ID that documents the code issue.
- Ubuntu published a security notice enumerating affected releases and the fixed package versions (Jammy, Focal, etc.), marking the vulnerability Medium and enumerating fixed package versions for each supported release. Administrators on Ubuntu should upgrade to the listed package versions.
- Red Hat and others included the CVE in their tracking systems; public advisories from vendor mirrors and third‑party vulnerability databases list Red Hat bug IDs and the NVD entry. Note: distribution timelines and version strings vary — always consult your vendor’s package repository for the exact fixed package in your environment.
Detection, mitigation, and hardening guidance
Below are practical steps for administrators, CI owners, and developers.Immediate remediation (short term)
- Patch promptly. Update Binutils to a fixed distribution package or rebuild from an upstream revision that includes the fix. On Debian/Ubuntu: run the usual package update flow and upgrade the
binutilspackage to the fixed version for your release. On RHEL/CentOS/Fedora families use your vendor’syum/dnf/microdnfupdate paths to install vendor-supplied fixes. Verify package release notes. - Isolate build and analysis jobs that handle third‑party object files. Run untrusted parsing/analysis in containers or ephemeral VMs; avoid processing unknown object files on long‑lived build hosts.
- Restrict processing of Mach‑O artifacts. If your tooling does not need Mach‑O support, rebuild Binutils without Mach‑O support where practical; this reduces the attack surface of BFD for that host.
Detection and monitoring
- Watch for repeated Binutils crashes (core dumps, segfaults) in developer workstations or CI logs. Jobs that suddenly fail on objdump/readelf/strip with segmentation faults or aborts deserve immediate triage.
- Add CI pre‑sanity checks to reject unknown/binary blobs sent to build pipelines, or force explicit operator review for any Mach‑O artifacts that a Linux CI encounters.
- Use host monitoring and centralized logging to detect anomalous processes invoking Binutils against user‑supplied files.
Hardening recommendations (longer term)
- Enable least privilege for build/analysis agents and run untrusted file parsing under seccomp/AppArmor/SELinux policies or in minimal containers.
- Where possible, use compiler warnings and sanitizers for developer toolchains: build toolchain components with
-Wuninitializedand, for testing, run with ASAN/UBSAN in CI to catch unexpected memory use. - Add file‑type gating to mail gateways and artifact stores: if a service must accept uploaded binaries, perform type‑checking and sanitize or quarantine Mach‑O content before any automated processing.
Practical remediation checklist (quick action items)
- Identify boxes that run Binutils tools as part of automated pipelines (CI, artifact indexing, malware/scanner farms).
- Apply vendor updates for binutils packages. Verify versions against your distro advisory.
- If you cannot patch immediately, isolate or stop services that automatically run binutils on untrusted inputs.
- Add monitoring for repeated objdump/readelf crashes and core files.
- Enforce sandboxing/containers for all automated binary analysis jobs.
- Re‑scan repository/CI inputs to remove or quarantine any suspicious Mach‑O files.
Supply‑chain implications and real‑world scenarios
This CVE is a reminder that toolchain components are part of your attack surface. Even if binutils runs on Linux machines and Mach‑O is a macOS object format, the following realistic scenarios make this ostensibly “local and minor” bug operationally important:- A CI runner that automatically inspects external artifacts (for license scanning, metadata extraction, or signing) could be repeatedly crashed by a crafted Mach‑O uploaded to an artifact repository, disrupting builds.
- Cross‑platform build farms that accept macOS artifacts for cross‑compilation or packaging may parse Mach‑O files during verification steps and thus expose themselves.
- Malware analysts or automated scanners that open many untrusted binaries are attractive targets: a crafted Mach‑O used as a denial‑of‑service payload can waste analysis resources or force human attention. The broader history of Binutils receiving denial‑of‑service or memory‑handling fixes in recent years suggests that tools which read debug or object metadata are particularly brittle when facing hostile or malformed inputs.
Critical analysis: strengths of the fix, residual risks, and cautionary notes
What’s good
- The public tracking and distribution vendor ecosystem reacted: multiple distributions produced packages and advisories that list the fixed versions, and upstream code changes were made to initialize the field correctly. That demonstrates a functioning vulnerability triage and remediation pipeline for a core open‑source tool.
- The flaw itself is limited to availability impact in the common tracking records, making the immediate threat model easier to manage (patching and sandboxing sufficiently mitigates risk).
Where risk remains
- Local access requirement is not an absolute safety guarantee. Build and automation infrastructure often executes many binaries and can be induced to process attacker‑provided artifacts. Because exploitation is a matter of supplying a crafted Mach‑O file to a tool invocation, attackers who can influence artifact stores, CI inputs, or developer inboxes can cause sustained outages.
- Fixes applied in distributions may vary by release; long‑tail systems (EOL distributions, embedded systems with frozen toolchains) may remain vulnerable. Some vendors do not ship immediate updates for older major versions, leaving operators of legacy systems with limited options short of rebuilding from source.
- Upstream references and dates are sometimes inconsistent across trackers. Security trackers, distribution pages, and NVD entries occasionally show differing publication or fix dates; where dates matter for compliance timelines, always cite the vendor advisory and distribution security notice for your specific platform.
Unverifiable or uncertain claims (flagged)
- Some third‑party CVE aggregators list exploitation likelihood and CVSS vectors that are derived rather than authoritative. If you must report precise CVSS scores for compliance, cite the vendor security notice or NVD entry for the canonical vector. Public aggregators sometimes change their synthesized scores over time; treat them as guidance rather than authoritative ground truth.
Recommended long‑term changes for resilient toolchains
- Treat all binary‑parsing libraries used by CI and analysis systems as untrusted input processors and run them in hardened, ephemeral sandboxes.
- Add file provenance and whitelisting to artifact ingestion: require human approval or cryptographic attestation for artifacts from unknown sources before automated parsing.
- Incorporate fuzz testing into toolchain QA for any internal binary‑parsing utilities and consider reporting crafted testcases that crash upstream projects so the fixes land in source control quickly.
- Keep an authoritative internal inventory of language runtimes, toolchain binaries, and their versions; this makes prioritizing and validating vendor updates (and documenting patch status for audits) feasible.
Conclusion
CVE‑2023‑25588 is an instructive example of how a tiny, uninitialized field inside a ubiquitous library can produce outsized operational pain. The vulnerability itself is a denial‑of‑service risk rather than a direct code‑execution backdoor, but the environments most at risk are those that automatically parse, index, or analyze third‑party binaries — precisely the sort of automation modern development organizations rely on. Patch promptly, isolate untrusted processing with sandboxing and containerization, and treat your toolchain components with the same threat model you apply to network‑reachable services. Watching for repeated Binutils crashes and hardening CI/build systems against untrusted inputs will turn an inconvenient crash into a manageable maintenance task rather than a production outage.Source: MSRC Security Update Guide - Microsoft Security Response Center