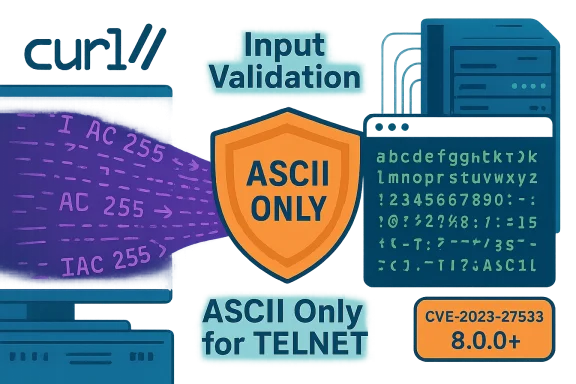
The curl TELNET input-validation bug tracked as CVE-2023-27533 is a deceptively simple but broadly consequential flaw: curl versions prior to 8.0 accepted unfiltered TELNET username and option strings and forwarded them verbatim into TELNET negotiation, allowing attacker-supplied bytes to be interpreted as protocol commands or negotiation bytes. That behavior opened a path for special-element injection during TELNET handshakes that, depending on the calling application and environment, could lead to information disclosure, denial-of-service, or even remote code execution. The issue was reported and fixed by the curl project in March 2023; the upstream fix restricts TELNET username and option input to ASCII, and distributions subsequently shipped patched curl packages.
TELNET is an old, character‑oriented network protocol with a built‑in negotiation phase that uses in‑band command bytes — notably the IAC (Interpret As Command) byte — to switch options and modes between client and server. When applications that embed libcurl expose TELNET parameters (for example via a web form, a script argument, or an automation job), those user-supplied strings can reach curl's TELNET negotiation code. If that code does not neutralize control bytes, an attacker can embed negotiation commands or other non‑printable characters that change the semantics of the session. This is exactly the root cause described in the official curl advisory: curl forwarded username and "telnet options" without proper input scrubbing, allowing TELNET option IAC injection.
curl’s advisory and the CVE descriptions from public repositories converge on the same corrective action: only accept ASCII characters for TELNET username and options, and treat any user‑controlled input with strict validation. The curl project fixed the behavior in the 8.0.0 release and published the specific patch and timeline. Distributors — including major Linux vendors — responded with updates shortly after the upstream release.
This ambiguity is important: the vulnerability is real and the fix is simple, but the real‑world ease of exploitation depends on system configuration, calling code, and whether TELNET is enabled. In short: treat the CVE as actionable for systems that meet the exploitation preconditions, but do not panic if you do not run TELNET or if the application never forwards untrusted user input into curl’s TELNET parameters.
This means the risk model should be conditional:
Limitations and residual concerns:
Recommended action plan for administrators and product teams:
Source: MSRC Security Update Guide - Microsoft Security Response Center
 Background / Overview
Background / Overview
TELNET is an old, character‑oriented network protocol with a built‑in negotiation phase that uses in‑band command bytes — notably the IAC (Interpret As Command) byte — to switch options and modes between client and server. When applications that embed libcurl expose TELNET parameters (for example via a web form, a script argument, or an automation job), those user-supplied strings can reach curl's TELNET negotiation code. If that code does not neutralize control bytes, an attacker can embed negotiation commands or other non‑printable characters that change the semantics of the session. This is exactly the root cause described in the official curl advisory: curl forwarded username and "telnet options" without proper input scrubbing, allowing TELNET option IAC injection.curl’s advisory and the CVE descriptions from public repositories converge on the same corrective action: only accept ASCII characters for TELNET username and options, and treat any user‑controlled input with strict validation. The curl project fixed the behavior in the 8.0.0 release and published the specific patch and timeline. Distributors — including major Linux vendors — responded with updates shortly after the upstream release.
Why this matters: the attack surface and consequences
TELNET is rarely used in new deployments, but it persists in legacy systems, embedded devices, testing tools, appliance management consoles, and custom automation where administrators prioritized convenience over modern, encrypted protocols. Those environments share two risk factors that make CVE‑2023‑27533 meaningful:- Many integrations call libcurl indirectly, so an embedded curl bug can affect an endpoint even when the application’s authors did not intend TELNET use.
- User-supplied strings reach libcurl in multiple ways: command-line parameters, web forms, APIs that accept host/credential data, and automation scripts. When those pipelines are not hardened, the attacker can inject negotiation bytes.
Technical analysis: root cause and patch
How TELNET negotiation can be abused
TELNET negotiation uses in‑band control bytes; the most important is IAC (255 decimal), which prefixes TELNET commands. If an application allows an attacker to craft a username or telnet-option string that includes IAC sequences, those bytes will be interpreted as negotiation commands by the recipient (server or intermediary), potentially enabling:- forced option negotiation that the client or server did not intend,
- insertion of control sequences that confuse or crash implementations,
- injection of bytes that downstream components interpret as data with control effects.
The upstream fix
The official fix implemented by the curl maintainers enforces an input restriction: only ASCII characters are accepted for TELNET username and telnet-option strings. The patch was small and targeted: it prevents non‑printable and special negotiation bytes from being accepted and forwarded, thereby eliminating the path for IAC injection. The fix was merged and shipped as part of curl 8.0.0, coordinated with the advisory publication in March 2023.Introduced / affected versions
- Introduced in curl 7.7 and present in versions through 7.88.1 (inclusive).
- Fixed in curl 8.0.0; versions >= 8.0.0 are not affected.
Who was affected: vendors and distributions
The vulnerability appears in libcurl itself, which means any product bundling or linking to a vulnerable libcurl can inherit the risk. The usual downstreams reacted as follows:- Major Linux distributions issued updates and advisories (Ubuntu, Debian, Red Hat, SUSE, Oracle Linux, Alpine). Ubuntu and Debian list the CVE and show patched packages in supported releases. Red Hat and SUSE maintained advisories and recommended upgrades.
- Cloud and appliance vendors that include curl in management agents or embedded tools issued their own bulletins or listed the CVE in their advisories. IBM included CVE‑2023‑27533 in a WinCollect bulletin; other vendors referenced the fixed libcurl packages.
- OEMs or proprietary appliance vendors that still enabled TELNET by default were at higher risk because TELNET must be active for exploitation in many configurations; some vendor advisories called this out explicitly.
Exploitability and real‑world evidence
Publicly available records and vendor advisories describe the vulnerability and demonstrate the fix, but we did not find authoritative, widespread reports of reliable exploit code or large‑scale active exploitation tied to CVE‑2023‑27533 at the time of this article. Feed aggregators and vulnerability databases list the CVE with varying severity metrics and exploitability estimates; some sources treat it as moderate to high potential severity because of the theoretical RCE vector, while others assign more conservative scores where context (e.g., TELNET enabled, user input exposure) reduces practical risk.This ambiguity is important: the vulnerability is real and the fix is simple, but the real‑world ease of exploitation depends on system configuration, calling code, and whether TELNET is enabled. In short: treat the CVE as actionable for systems that meet the exploitation preconditions, but do not panic if you do not run TELNET or if the application never forwards untrusted user input into curl’s TELNET parameters.
Detection, hunting, and indicators
Because CVE‑2023‑27533 is an input‑sanitization flaw, detection is best accomplished through a combination of code review, configuration inventory, and runtime monitoring:- Inventory and binary scans: identify hosts that have curl/libcurl versions >=7.7 and <=7.88.1. Package managers and vulnerability scanners already include this capability; check vendor advisories for patched package names.
- Configuration checks: locate services and scripts that call curl with TELNET or that pass user input to curl arguments such as --user or --telnet-option. Static code searches for those flags in automation, CI scripts, and web back ends is an effective first step.
- Behavioral detection: monitor for unexpected TELNET negotiation bytes originating from client hosts (IAC sequences embedded in session negotiation fields) or for abnormal TELNET session behavior after an automated request. Network IDS signatures can flag TELNET negotiation with unexpected patterns.
- Application log review: examine logs where applications echo or record the values passed to curl. If logs contain control characters or non‑ASCII bytes in username/option fields, that indicates suspicious input.
Mitigation and patching strategy
The remediation path is straightforward but must be prioritized based on exposure:- Immediate action — inventory and patch:
- Identify instances of curl/libcurl in the vulnerable version range. Use your package manager, software inventory tools, or container image scans.
- Upgrade to curl 8.0.0 or later, or apply the upstream patch if you cannot upgrade. The upstream advisory and commit offer the exact change.
- Compensating controls for systems that cannot be patched immediately:
- Disable TELNET where feasible and replace it with SSH or another secure remote management protocol. TELNET is unencrypted and should be removed from modern deployments regardless of this CVE.
- Reject or sanitize user input before it reaches curl: implement strict input validation that strips non‑ASCII characters and blocks control bytes. This mirrors the upstream fix’s intent and reduces attack surface for callers that cannot upgrade immediately.
- Longer‑term hygiene:
- Audit any service that accepts user input and then calls system utilities or libraries that perform network negotiation. Adopt a “never trust user input” policy with sanitization at every boundary.
- For embedded vendors and packagers, ensure ABI‑compatible updates or backports for long‑lived products; inform customers and produce errata where TELNET remains enabled.
Practical hardening checklist for administrators
- Inventory: List all hosts and containers with curl/libcurl and determine the installed version. Use automated scanning where possible.
- Patch: Update curl to 8.0.0+ or apply the vendor patch/backport. Prioritize externally reachable hosts and appliances exposing TELNET services.
- Sanitize: Wherever your code accepts credentials or options from users or external systems, enforce character whitelists (printable ASCII) and block control bytes.
- Replace TELNET: Migrate management and automation to SSH or encrypted alternatives; disable TELNET services and remove TELNET from default configurations.
- Monitor: Add IDS/IPS signatures and application‑level logging to detect suspicious TELNET negotiation sequences; search logs for non‑ASCII username or option values.
Risk assessment — technical and programmatic considerations
CVE‑2023‑27533 has a noteworthy combination of properties: the underlying protocol (TELNET) uses in‑band control bytes that are easy to misuse, and libcurl is widely embedded. However, exploitation requires a specific chain of conditions — an environment where TELNET is used, where curl is invoked with user‑controllable credential/option input, and where the remote behavior of the server or intermediary will materially change the attacker's advantage (for example, causing code execution or file manipulation).This means the risk model should be conditional:
- High priority: legacy appliance management consoles, embedded systems, or custom web front‑ends that accept external input and invoke TELNET via curl. These are the exact environments where the bug becomes actionable.
- Medium priority: general servers that have curl installed but do not expose TELNET or do not accept untrusted input in TELNET parameters; the vulnerability is present but likely not exploitable.
- Low priority: systems where TELNET is disabled and no path exists for untrusted input to reach curl’s TELNET negotiation code. Still, maintainers should patch as part of normal vulnerability management.
Strengths and limitations of the fix
The upstream correction is a strong, surgical fix: it enforces input constraints (ASCII-only) rather than attempting brittle heuristics or wide behavioral changes. That approach minimizes regressions for legitimate users while closing the abuse vector. The fix was merged quickly and coordinated with a release to make distribution updates straightforward.Limitations and residual concerns:
- Backporting: vendors that maintain older ABI-compatible builds may need to backport the patch; delayed backports create windows where embedded devices remain vulnerable. Administrators of supported‑but‑old systems should track vendor advisories closely.
- Detection difficulty: because the vulnerability is an input‑sanitization issue, passive network detection without tuned signatures may miss subtle injection attempts embedded in otherwise normal sessions. Active hunting and code review are often required.
- Legacy protocols: TELNET remains a persistent risk across many environments. Single fixes help, but the broader mitigation must be protocol deprecation where practical.
Closing analysis and recommendations
CVE‑2023‑27533 is a textbook example of how small assumptions and legacy protocols can cascade into security issues in modern systems. The vulnerability is straightforward to patch; the fix was implemented by the curl team and propagated through distributors, so operational mitigation is primarily a matter of inventory, prioritization, and timely updates.Recommended action plan for administrators and product teams:
- Immediately inventory curl/libcurl instances and identify TELNET usage.
- Prioritize patching of externally reachable hosts and appliances, and apply vendor updates or upgrade to curl 8.0.0+.
- If you cannot patch immediately, disable TELNET and apply input sanitization at the application layer.
- For product teams and packagers: backport the fix into long‑lived builds where necessary, and notify customers where devices ship with TELNET enabled by default.
- Use this incident to audit other protocol code paths for similar input‑handling assumptions and to phase out legacy, insecure protocols.
Source: MSRC Security Update Guide - Microsoft Security Response Center