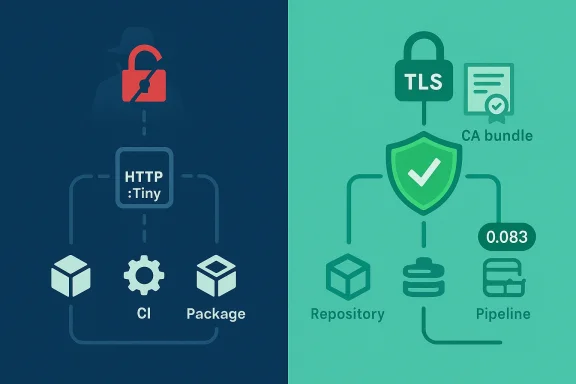
When a tiny, widely used HTTP client slips into an insecure default mode, the consequences ripple far beyond a single library — they reach package managers, CI pipelines, internal tooling, and any application that quietly trusts “https://” without actually verifying who’s on the other end. CVE-2023-31486 exposed exactly that failure: HTTP::Tiny — a small, core Perl HTTP client — shipped with an insecure TLS default prior to version 0.083, requiring developers to opt in to certificate verification. The change that fixed the problem reversed the default to secure-by-default, but the fallout and the lessons about defaults, supply-chain risk, and detection remain relevant for every organization that runs Perl code today.
Its ubiquity matters: when a module like HTTP::Tiny sets an insecure default, it doesn’t only affect a dozen apps — it can affect hundreds of downstream packages and millions of runtime invocations across servers, developer machines, CI runners, and IoT devices.
Version 0.083 changed the default to verify server certificates. To preserve compatibility for legacy deployments, the maintainers provided an environment flag that allowed the previous, insecure default to be re-enabled where necessary.
The practical outcomes are straightforward and severe:
If the default constructor doesn’t verify certificates, that call silently trusts any TLS endpoint that presents a certificate — legitimate or not — and many codebases never add the explicit parameter to change that behavior.
If you need to supply custom CA trust material, use the SSL options to point at a CA file:
Caveat: counts of “how many CPAN modules were affected” vary by scan method and definition of “affected” (direct call, indirect dependency, or optional use). Community reports suggested hundreds of downstream packages could be impacted, but exact numbers vary between analyses. Treat such counts as indicators of scope, not definitive tallies.
For organizations, this raises several governance points:
However, escape hatches are dangerous when used long-term. They delay remediation, increase technical debt, and risk being overlooked during audits.
Practical steps you can apply today are simple: inventory, upgrade, and enforce secure constructors. Where updates are delayed by legacy constraints, quarantine the exceptions, and treat compatibility flags as temporary, not permanent, fixes. The next vulnerability may not be so easy to spot — security that depends on developer assumptions or implicit defaults is fragile. Make secure defaults a first-class part of your software hygiene.
Source: MSRC Security Update Guide - Microsoft Security Response Center
 Background
Background
What is HTTP::Tiny and why it matters
HTTP::Tiny is intentionally small and dependency-light: a single-file HTTP/1.1 client that aims to be correct, simple, and easily embeddable. Because of those qualities it is used in countless scripts, libraries, and higher-level tools across the Perl ecosystem. It has been part of Perl’s core distribution since Perl 5.13.9 and is also available as a standalone CPAN distribution for systems that prefer separate packaging.Its ubiquity matters: when a module like HTTP::Tiny sets an insecure default, it doesn’t only affect a dozen apps — it can affect hundreds of downstream packages and millions of runtime invocations across servers, developer machines, CI runners, and IoT devices.
The core issue in plain terms
Prior to version 0.083, HTTP::Tiny did not verify TLS/SSL certificates by default. That means code that uses HTTP::Tiny to perform HTTPS requests — including requests that read package manifests, download code, or interact with APIs — could be sending or receiving sensitive data under an encrypted channel without actually confirming the identity of the remote server. An attacker able to perform a man-in-the-middle (MitM) could intercept, inspect, or alter traffic without an obvious trace.Version 0.083 changed the default to verify server certificates. To preserve compatibility for legacy deployments, the maintainers provided an environment flag that allowed the previous, insecure default to be re-enabled where necessary.
What CVE-2023-31486 actually says
CVE-2023-31486 describes an insecure default TLS configuration in HTTP::Tiny versions before 0.083, where certificate verification was disabled unless explicitly enabled by the user. The vulnerability is classed under improper certificate validation (CWE-295), because the library’s default initialization failed to enforce a crucial security check for TLS connections.The practical outcomes are straightforward and severe:
- A MitM attacker with network access between client and server can present a forged TLS certificate and the client will accept it by default.
- Sensitive data can be intercepted, altered, or injected.
- Systems that download code or dependencies over HTTPS can be tricked into installing tampered packages.
Timeline and fixes
- The insecure default behavior had been present in releases prior to 0.083.
- The issue was publicly disclosed in 2023 and tracked as CVE-2023-31486.
- HTTP::Tiny 0.083 changed the default behavior: certificate verification is enabled by default.
- To ease migration, an environment variable (for backwards compatibility) was made available to restore the old behavior where necessary.
- Operating system vendors and package maintainers subsequently rolled out updates to their Perl packages and provided guidance to users and administrators.
Why this was a serious problem
Defaults drive developer behavior
Most developers assume “https” equals “secure by default.” For many high-level languages and popular HTTP clients that assumption holds true. When a tiny, dependable library deviates from that expectation and fails to verify certificates unless asked, it breaks an implicit security contract between code authors and their infrastructure.Wide reach, subtle failure modes
HTTP::Tiny’s low friction makes it ideal for scripts and libraries: it’s imported to do small jobs, often with minimal configuration. That’s precisely what makes the risk so insidious. It’s common to find ad-hoc scripts or early-stage prototypes using default constructors like:
Code:
my $http = HTTP::Tiny->new();
my $res = $http->get('[url]https://api.example.com/data');[/url]Supply-chain and package manager implications
Package managers and installers that fetch code over HTTPS are high-value targets for attackers. If those tools (or underlying libraries they rely on) accept any TLS certificate by default, an attacker capable of intercepting that download step can substitute malicious packages, thereby escalating a local vulnerability into a widespread supply-chain compromise.Technical specifics developers and ops need to know
Secure default in 0.083
- Behavior: Starting in HTTP::Tiny 0.083, the library verifies TLS server certificates by default.
- Compatibility: The maintainers added an environment variable to allow restoration of previous behavior for legacy systems that depend on the old default.
Environment flag for backward compatibility
- The library exposes an environment variable that can force the insecure-by-default behavior if necessary (i.e., to maintain legacy behaviour during migration). Systems should avoid relying on that flag except as a temporary mitigation while transitioning.
Prerequisites for HTTPS support
- To make HTTPS connections, HTTP::Tiny relies on platform TLS libraries. Certain minimum versions of supporting modules are required; if the required TLS stack isn’t present, HTTP::Tiny will report errors rather than silently degrade security. Make sure your runtimes install the appropriate SSL/TLS Perl modules.
How to create an explicitly secure HTTP::Tiny client
Developers should instantiate HTTP::Tiny with certificate verification explicitly enabled:
Code:
my $http = HTTP::Tiny->new( verify_SSL => 1 );
my $res = $http->get('[url]https://example.com/resource');[/url]
Code:
my $http = HTTP::Tiny->new(
verify_SSL => 1,
SSL_options => { SSL_ca_file => '/path/to/ca-bundle.crt' },
);Who was affected — and how broadly?
The vulnerability affected any installation using HTTP::Tiny versions before 0.083, which includes:- Standalone CPAN installations of HTTP::Tiny prior to 0.083.
- Perl core distributions that bundled the older HTTP::Tiny implementation (Perl’s inclusion of HTTP::Tiny in core since 5.13.9 means many older Perl runtimes inherited the behavior).
- Downstream projects and package ecosystems that relied on HTTP::Tiny for network operations — notably package managers, build scripts, or lightweight agents.
Caveat: counts of “how many CPAN modules were affected” vary by scan method and definition of “affected” (direct call, indirect dependency, or optional use). Community reports suggested hundreds of downstream packages could be impacted, but exact numbers vary between analyses. Treat such counts as indicators of scope, not definitive tallies.
Practical mitigations and remediation steps
For organizations and developers, the path to remediation is straightforward but requires attention to dependencies and the deployment pipeline.- Upgrade HTTP::Tiny to version 0.083 or later wherever possible.
- Audit code for any direct usage of HTTP::Tiny and ensure calls either:
- Construct with
verify_SSL => 1, or - Use a wrapper that enforces secure defaults.
- Search through scripts and repositories for the pattern
HTTP::Tiny->new()and other places where an HTTP::Tiny object might be created implicitly. - Check tooling and package managers (CI runners, bootstrap scripts, containers) for embedded Perl scripts or utilities that may rely on the insecure default.
- Ensure the runtime environment has a valid CA bundle available or that the system installs
Mozilla::CAor equivalent to provide a trusted CA store. - Remove or audit any use of the compatibility environment variable that restores the insecure default; if present, treat its usage as a temporary exception only.
- Where upgrades cannot be applied immediately, explicitly enable verification in code or wrap HTTP::Tiny with a hardened layer to enforce verify_SSL.
- Inventory all systems running Perl and identify runtime versions and installed HTTP::Tiny versions.
- For each machine, determine whether the system’s Perl overlies a vulnerable HTTP::Tiny or whether an application-installed CPAN copy is present.
- Apply vendor patches or perform CPAN upgrades to HTTP::Tiny 0.083+.
- Redeploy or restart services that embed Perl runtimes where necessary.
- Conduct controlled tests to validate that critical HTTPS flows fail if presented with invalid certificates (this verifies certificate verification is working).
Detection and scanning — how to find the exposures
Detecting vulnerable usage requires both code scanning and runtime checks.- Static search: grep repositories for
HTTP::Tiny->newor code that callsget,post, etc., on HTTP::Tiny objects whereverify_SSLisn’t set. Look for variant spellings or wrappers that pass through defaults. - Dependency analysis: inspect CPAN dependencies for modules that embed or call HTTP::Tiny. Use dependency tools to build a list of packages that transitively depend on HTTP::Tiny.
- Runtime verification: on a staging system, attempt to connect to a server with a deliberately invalid certificate and confirm the client rejects the connection. That validates whether verification is active.
- CI and image scans: include checks for HTTP::Tiny version in container/image scanning. Ensure build pipelines that install packages via CPAN or system package managers don’t bring in older HTTP::Tiny versions.
Supply-chain and policy implications
CVE-2023-31486 is emblematic of a recurring theme in software security: defaults matter. Libraries and runtimes set expectations. When a low-level library chooses an insecure default for compatibility, it pushes the burden of security onto every author downstream. That burden often goes unmet.For organizations, this raises several governance points:
- Depend on secure-by-default libraries. Prioritize dependencies that choose safety-first defaults.
- Enforce project-level secure-initialization policies. For example, create internal wrapper modules that instantiate common clients with secure settings.
- Treat environment variables that relax security as exceptions requiring formal approval.
- Add vulnerability scanning and dependency policy checks that flag insecure defaults, not just known CVEs.
- Recognize that small libraries propagate risk. A tiny module can create outsized attack surfaces when embedded into critical flows like package installs, auto-updaters, or bootstrap scripts.
Trade-offs and the maintainers’ dilemma
Changing defaults in a long-lived library is not trivial. Library maintainers balance two opposing pressures:- Security: modern expectations dictate that TLS libraries verify certificates by default to protect confidentiality and integrity.
- Compatibility: some users deliberately operate in environments with self-signed certificates or constrained trust models and rely on the old behavior.
However, escape hatches are dangerous when used long-term. They delay remediation, increase technical debt, and risk being overlooked during audits.
Real-world impact and exploitation risk
The vulnerability enables MitM attacks under conditions where an attacker can intercept traffic. Whether such attacks are trivially achievable depends on the deployment scenario:- Public networks, shared Wi-Fi, or misconfigured edge devices increase risk.
- For server-to-server communication within private networks, the window for MitM may be narrower; yet internal threat actors or compromised infrastructure still present a risk.
- Systems that fetch and execute code over HTTP::Tiny without verification — for example, package installers or bootstrap scripts — create a high-value target for attackers.
Hardening recommendations (practical examples)
- Always construct clients with verification enabled:
Code:
# Recommended: enforce verification
my $http = HTTP::Tiny->new( verify_SSL => 1 );- Make secure defaults central:
- Create an internal helper module, e.g., My::HTTP::Tiny::Safe, that always sets
verify_SSL => 1and adds standard SSL options. - Require code reviews to flag direct uses of HTTP::Tiny->new without
verify_SSL. - In CI pipelines:
- Fail builds if HTTP::Tiny < 0.083 is discovered in dependency graphs.
- Run tests that simulate invalid certificates to ensure connections fail.
- In operations:
- Avoid setting compatibility environment variables globally; if a legacy service needs the insecure behavior, isolate it and track a remediation plan.
- Ensure systems have an up-to-date CA bundle and consider standardizing on a vetted CA bundle provider.
Lessons for secure defaults across ecosystems
CVE-2023-31486 is not unique; similar issues have surfaced in other languages and libraries where insecure defaults persisted for convenience or compatibility. The following principles help prevent repetition:- Libraries that implement security-relevant features should be secure-by-default.
- When compatibility forces a change, document it prominently and provide migration guidance.
- Run ecosystem-wide scans to find latent insecure behavior — especially for small libraries embedded across many packages.
- Educate developers that “uses HTTPS” does not necessarily mean “verifies TLS certificates” unless the client library enforces that.
Conclusion
CVE-2023-31486 is both simple and sobering: an insecure default in a tiny client created a risk that could be amplified across countless applications and systems. The fix — flipping the default in HTTP::Tiny to verify certificates — was the correct technical response. The broader takeaway is organizational: ensure your dependencies are secure-by-default, scan for library behaviors that mismatch modern security expectations, and harden build and runtime environments so that a single misconfigured default cannot be leveraged into a supply-chain compromise.Practical steps you can apply today are simple: inventory, upgrade, and enforce secure constructors. Where updates are delayed by legacy constraints, quarantine the exceptions, and treat compatibility flags as temporary, not permanent, fixes. The next vulnerability may not be so easy to spot — security that depends on developer assumptions or implicit defaults is fragile. Make secure defaults a first-class part of your software hygiene.
Source: MSRC Security Update Guide - Microsoft Security Response Center