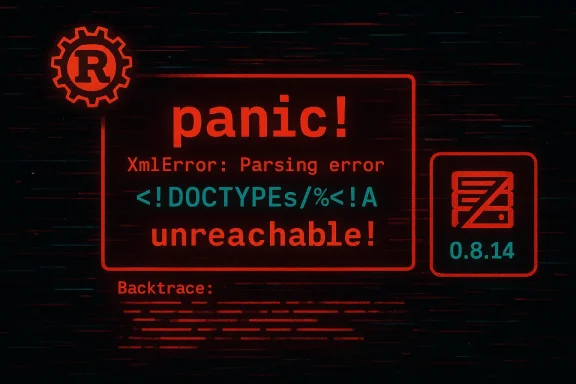
A small, innocuous-looking malformed XML string can crash an XML parser and take a service offline — that’s the practical reality behind CVE-2023-34411, a high‑severity denial‑of‑service vulnerability in the widely used Rust crate xml-rs that affected versions 0.8.9 through 0.8.13 and was fixed in 0.8.14.
The xml-rs crate is a pure‑Rust XML library commonly used by Rust programs and downstream projects (including serialization wrappers like serde-xml-rs). In June 2023 a contributor found a parsing path where the crate attempted to format an error message for an unexpected
This vulnerability is a classic availability problem: an attacker who controls XML input (for example, any network endpoint or file upload that accepts XML) can craft a document that triggers the panic and causes the consuming application to crash, restart, or otherwise become unavailable. Security scanners and vulnerability databases classified the issue as high severity (CVSS around 7.5 in public trackers) because no privileges or user interaction are required and the impact is a complete loss of availability for the affected component while the attacker continues to send malformed inputs.
Yet small fixes can require broad coordination. Because xml-rs is used transitively, many downstream projects needed to bump versions, rebuild, and re‑release. That supply‑chain friction explains why even simple bugs can produce real operational pain if not tracked and patched promptly. (github.com)
If you manage Rust services that parse XML, treat this as both a concrete patching task (update xml-rs to 0.8.14 or later) and a prompt to harden how your systems accept and handle untrusted data. Short, surgical code fixes can close the vulnerability — but operational controls, dependency hygiene, and safer parsing practices are what prevent similar incidents from recurring. (github.com)
Source: MSRC Security Update Guide - Microsoft Security Response Center
 Background / Overview
Background / Overview
The xml-rs crate is a pure‑Rust XML library commonly used by Rust programs and downstream projects (including serialization wrappers like serde-xml-rs). In June 2023 a contributor found a parsing path where the crate attempted to format an error message for an unexpected <! token by entering an unreachable code path; when the library encountered certain malformed markup it invoked a panic, crashing the thread or process that tried to parse the input. That defect is tracked as CVE‑2023‑34411 and the upstream fix landed in the 0.8.14 release. (github.com)This vulnerability is a classic availability problem: an attacker who controls XML input (for example, any network endpoint or file upload that accepts XML) can craft a document that triggers the panic and causes the consuming application to crash, restart, or otherwise become unavailable. Security scanners and vulnerability databases classified the issue as high severity (CVSS around 7.5 in public trackers) because no privileges or user interaction are required and the impact is a complete loss of availability for the affected component while the attacker continues to send malformed inputs.
What went wrong: a concise technical summary
The root cause
At the core of the problem was error‑reporting code in the xml-rs lexer that handled token formatting. When the lexer identified an unexpected<! sequence — which in correctly formed XML starts markup declarations, e.g. <!DOCTYPE or <!-- — it attempted to create a human‑readable message by formatting the token. The formatting code used an unreachable!() default arm for tokens that were not enumerated, which means a malformed sequence could reach code that explicitly panicked because it was assumed to be impossible. That assumption turned out to be false for certain broken inputs. (github.com)The practical trigger
The public reproducer that accompanied the fix used an input such as:- "<!DOCTYPEs/%<!A"
panic! with an "entered unreachable code" backtrace. After the patch the same input yields a clean parse error (an Err result) rather than a panic. The change is surgical: avoid calling unreachable!() in the token Display implementation and return a proper error string instead. (github.com)Why panic is important in Rust libraries
Rust distinguishes code errors (Result/Option) from logic errors where the program cannot continue (panic). Libraries intended to be embedded in long‑running services must avoid panics on malformed input — they should return errors so callers can recover. A panic inside a thread can unwind into application code or abort the whole process depending on build configuration. In either case, a well‑constructed input‑validation bypass should not be able to crash service infrastructure. The xml-rs bug violated that principle by converting a recoverable malformed input into an unrecoverable panic. (github.com)Timeline and remediation
- Vulnerable versions: xml-rs >= 0.8.9 and < 0.8.14. The issue was introduced by a patch identified by maintainers and traced back to a specific commit; the author and maintainers merged a fix on June 1, 2023. (github.com)
- Fix: The upstream fix added a non‑panicking handling for the
MarkupDeclarationStarttoken in the token formatting logic so that unexpected<!tokens produce a normal parse error rather than a panic. The change was small but correct by design: return an error path instead of invokingunreachable!(). (github.com) - Public classification: The issue was assigned CVE‑2023‑34411 and was cataloged by NVD and public vulnerability vendors; third‑party databases and security vendors gave the vulnerability high severity and published guidance recommending upgrade to 0.8.14 or later.
Who should care and why
- Maintainers of Rust services or libraries that directly call xml-rs to parse XML input must treat this as urgent for any runtime that consumes untrusted XML (network APIs, file ingestion pipelines, RSS/processors, or any embedded XML handling).
- Projects that include xml-rs indirectly — for example, via serde-xml-rs or other higher‑level XML wrappers — must update their dependency lockfiles and CI builds because a transitive xml-rs pull (or an older Cargo.lock) can leave the service vulnerable. Dependency trees in Rust can carry small libraries all the way into production images, so transitive exposure is real and common.
- Systems that run with panic=abort (common in some build configurations or constrained runtimes) face a stronger impact: a panic can stop the whole process immediately, not just unwind a thread. That makes the vulnerability more severe in particular deployments. (github.com)
Concrete steps for immediate mitigation (operational checklist)
If you maintain Rust code that uses xml-rs (directly or transitively), take these immediate actions:- Upgrade the dependency:
- Ensure any Cargo.toml entries referring to xml-rs are constrained to version >= 0.8.14 and rebuild. Lockfiles (Cargo.lock) must be refreshed and committed in non-library projects. (github.com)
- For dependent libraries:
- Run a dependency audit (cargo audit or your SCA tool) to find where xml-rs is included transitively and update those projects or raise PRs to bump versions. If you vendor dependencies, refresh the vendored copy.
- Harden XML input handling:
- Validate and sanitize XML input at ingress. If you can, deny or log suspicious constructs (unexpected
<!usage outside known DOCTYPE/comment contexts). - If XML is optional, consider rejecting XML payloads from untrusted sources altogether or placing them on an isolated parsing worker with a strict timeout.
- Runtime guardrails:
- Run parsers in worker processes or threads with limits (timeouts, memory caps, circuit breakers). That reduces blast radius if an unpatched binary still encounters malformed input.
- CI/Release hygiene:
- Add strict dependency‑pinning checks to CI and fail builds when any vulnerable crate versions are present.
- Add a step that runs
cargo update -p xml-rs --precise 0.8.14as part of a temporary emergency update script where appropriate.
Deeper analysis: severity, attack surface, and real-world risk
Severity and exploitability
Public vulnerability databases and security vendors classified this as high‑severity denial of service. The reasons are straightforward:- Exploit prerequisites: An attacker only needs to supply crafted XML input; no authentication or local access is required when XML comes from the network.
- Impact: A successful exploit leads to a panic that can crash a thread or the whole process, causing total loss of availability for the affected component while exploitation continues.
Attack vectors and typical vulnerable contexts
- Public HTTP endpoints that accept XML-based POSTs, SOAP, SOAP‑like APIs, RSS/ATOM ingestion, or legacy systems that accept XML uploads are primary risk surfaces.
- Message ingestion pipelines and interprocess XML serialization (e.g., clipboard or interop with older systems) also present a risk if inputs are not validated.
- CI/build systems or developer tooling that process XML (e.g., formatter outputs, test fixtures) could be crashed by intentionally malformed files if those tools are exposed to untrusted content.
Real-world exploitation likelihood
This is not a remote, spectacular remote‑code‑execution zero day: it’s a denial‑of‑service by panic. That limits the damage to availability rather than code execution or data exfiltration. However, availability attacks are serious when they can be triggered repeatedly without privileges and when they take critical services offline (APIs, ingestion pipelines, monitoring agents). Public trackers report the issue as having a measurable, non‑negligible exploitation probability.Why the fix was simple — but the risk was real
The code change in xml-rs was very small: avoid invoking unreachable code while formatting token errors and instead return an error string for theMarkupDeclarationStart token. That simplicity illustrates a broader lesson in secure coding: small, defensive corrections in error‑handling paths often prevent outsized reliability and security consequences.Yet small fixes can require broad coordination. Because xml-rs is used transitively, many downstream projects needed to bump versions, rebuild, and re‑release. That supply‑chain friction explains why even simple bugs can produce real operational pain if not tracked and patched promptly. (github.com)
Long‑term recommendations for Rust projects that parse XML
- Prefer error‑returning behavior in libraries: Libraries intended for embedding should never panic on malformed external input. Maintain a clear API contract that returns Result/Errors on parse failures.
- Add parsing sandboxing: Parse untrusted XML in a separate process or worker thread with resource limits and a supervisor that can restart workers but keep the service alive.
- Use dependency scanning and automated pull requests: Tools that generate automated dependency upgrades reduce the window of exposure for transitive vulnerabilities.
- Enforce panic policies in CI: Turn on warnings for any public panics and add fuzzing/test cases that exercise error formatting paths.
- Consider safer libraries or hardened forks for critical systems: Evaluate other XML parsers that emphasize deny by default behavior and robust error handling. If replacing xml-rs, benchmark and test compatibility thoroughly. (Quick‑XML is an example of an alternative parser in the Rust ecosystem; evaluate it against your threat model and test corpus before switching.)
Suggested incident response for operators who detected crashes
If you detect application restarts, panics, or unexplained crashes associated with XML handling:- Identify whether xml-rs is present, directly or transitively, in the running binary (cargo tree, built artifacts, or SBOM).
- If present and below 0.8.14, schedule an emergency patch: build and deploy an image with xml-rs updated to 0.8.14 and ensure all nodes are replaced.
- While patching:
- Block external sources that submit XML to affected endpoints if feasible (temporary WAF rule or ingress filter).
- Configure logging to capture the offending payload safely (store only metadata or sanitized copies; avoid saving raw malicious data to avoid downstream parsing).
- After patching, verify parsers return errors rather than panics for the public reproducer input and monitor for any repeated malformed input patterns to see if exploitation attempts were occurring. (github.com)
Tradeoffs and potential pitfalls
- Blindly replacing a crate version in large dependency graphs can break builds or change behavior. Test thoroughly in staging before mass deployment.
- Some downstream packages may not pin xml-rs and will inherit the fixed version automatically on
cargo update, but others that vendor or pin older lockfiles will remain vulnerable until explicitly updated. - Defensive mitigations (timeouts, sandboxing) reduce blast radius but do not substitute for the fix; they should be combined with the version upgrade.
- Assuming a panic is harmless because it’s "only DoS" underestimates operational and reputational risk. Availability failures during business‑critical windows can be more damaging than many confidentiality or integrity bugs.
What defenders should learn from CVE‑2023‑34411
- Error handling matters: code paths that are labeled "this can never happen" are brittle. Malformed external input routinely violates such assumptions.
- Small changes can ripple: a single
unreachable!()in an error formatter turned an otherwise recoverable parse error into a high‑impact availability issue. - Supply‑chain hygiene must be continuous: transitive dependencies are real attack surface and need automatic scanning and timely upgrades.
Takeaway / Conclusion
CVE‑2023‑34411 is an instructive case where a minimal change in token formatting turned malformed XML into a service‑stopping panic. The fix was small and upstream was responsive, but the incident highlights perennial software‑security themes: never assume external input can't be malformed, defend for recoverability rather than panic, and keep dependency update and auditing processes tight.If you manage Rust services that parse XML, treat this as both a concrete patching task (update xml-rs to 0.8.14 or later) and a prompt to harden how your systems accept and handle untrusted data. Short, surgical code fixes can close the vulnerability — but operational controls, dependency hygiene, and safer parsing practices are what prevent similar incidents from recurring. (github.com)
Source: MSRC Security Update Guide - Microsoft Security Response Center