Go’s net/http HTTP/2 “rapid reset” weakness (CVE-2023-39325) is real, it was fixed upstream, and Microsoft’s short public mapping that “Azure Linux includes this open‑source library and is therefore potentially affected” is an authoritative product‑level attestation — but it is not a blanket guarantee that no other Microsoft product can contain the same vulnerable code. ([groups.google.cogle.com/g/golang-announce/c/iNNxDTCjZvo/m/UDd7VKQuAAAJ))
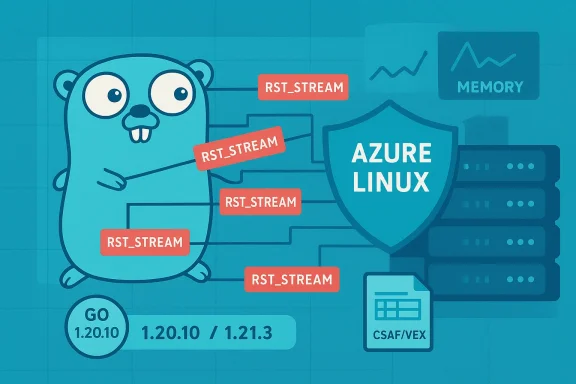
CVE‑2023‑39325 describes a denial‑of‑service risk in Go’s HTTP/2 implementation where a malicious client can create many requests and immediately send RST_STREAM (reset) frames. Because HTTP/2 allows many concurrent streams, a mis-handling of resets could let an attacker drive the server to spawn lots of handler goroutines that keep working even though the client has reset the stream — consuming CPU, memory, and other resources until the server degrades or crashes. The fix ensures that the number of simultaneously executing handler goroutines is bounded to the HTTP/2 stream concurrency limit (MaxConcurrentStreams); when the limit is hit new requests are queued and the server will close the connection if the queue grows unbounded. (app.opencve.io) (groups.google.com)
Why this matters: many cloud services, edge components, container images, and binaries (including ones Microsoft builds and publishes) either embed Go’s standard library or explicitly import golang.org/x/net/http2. Any product that ships a Go binary built with an affected stdlib or vendor dependency is at risk of the behavior described by this CVE until the binary is rebuilt with a fixed version. The Go project issued point releases that include the fix and explicitly called out the issue in the release notes. (groups.google.com)
This wording is helpful and important for Azure Linux users: it gives a clear action signal — patch your Azure Linux images. However, it is not a categorical statement that no other Microsoft product or image contains the same vulnerable code. Microsoft’s public mapping is an authoritative confirmation for the named product, not an exhaustive inventory of every Microsoft artifact. Multiple independent community analyses and forum threads haveioft’s attestation is product‑scoped, not an exclusivity guarantee.
When Microsoft expands the VEX entries to list additional products or images carrying the vulnerable component, those entries will be the authoritative signal for whatever product is named. Microsoft has said it williare identified — but until that happens, use the vendor attestation as a strong but scoped data point, not as universal proof of absence elsewhere.
Source: MSRC Security Update Guide - Microsoft Security Response Center
 Background / Overview
Background / Overview
CVE‑2023‑39325 describes a denial‑of‑service risk in Go’s HTTP/2 implementation where a malicious client can create many requests and immediately send RST_STREAM (reset) frames. Because HTTP/2 allows many concurrent streams, a mis-handling of resets could let an attacker drive the server to spawn lots of handler goroutines that keep working even though the client has reset the stream — consuming CPU, memory, and other resources until the server degrades or crashes. The fix ensures that the number of simultaneously executing handler goroutines is bounded to the HTTP/2 stream concurrency limit (MaxConcurrentStreams); when the limit is hit new requests are queued and the server will close the connection if the queue grows unbounded. (app.opencve.io) (groups.google.com)Why this matters: many cloud services, edge components, container images, and binaries (including ones Microsoft builds and publishes) either embed Go’s standard library or explicitly import golang.org/x/net/http2. Any product that ships a Go binary built with an affected stdlib or vendor dependency is at risk of the behavior described by this CVE until the binary is rebuilt with a fixed version. The Go project issued point releases that include the fix and explicitly called out the issue in the release notes. (groups.google.com)
What the Go project fixed, and which versions are patched
- The Go project’s announced fix is included in the minor releases Go 1.20.10 and Go 1.21.3. The golang.org/x/net/http2 package also contains a corresponding fix in v0.17.0 for users who configure HTTP/2 manually. Those releases enforce the concurrent-handler bound described above. This was communicated in the official Go releases and related change lists. (groups.google.com)
- Multiple independent vulnerability databases and vendor advisories summarize the same remediation: upgrade stdlib to Go 1.20.10 or 1.21.3 (or later) and upgrade golang.org/x/net/http2 to v0.17.0 or later. Those third‑party advisories are useful cross‑checks when you’re tracking which upstream commits or CLs implement the fix. (app.opencve.io)
What Microsoft publicly said — and what that statement actually means
Microsoft’s Security Response Center (MSRC) entry for this CVE includes a short FAQ answer that reads, in effect: “Azure Linux includes this open‑source library and is therefore potentially affected by this vulnerability.” That statement is a precise, product-scoped inventory attestation: it affirms that Microsoft’s Azure Linux distribution was inspected and found to include the upstream component referenced by the CVE, and therefore Azure Linux images are in‑scope for remediation. Microsoft has also described a commitment to publish machine‑readable CSAF/VEX attestations and to update mappings as additional Microsoft products are identified. ([ac5529/https%3A/msrc.microsoft.com/update-guide/vulnerability/CVE-2024-26757)This wording is helpful and important for Azure Linux users: it gives a clear action signal — patch your Azure Linux images. However, it is not a categorical statement that no other Microsoft product or image contains the same vulnerable code. Microsoft’s public mapping is an authoritative confirmation for the named product, not an exhaustive inventory of every Microsoft artifact. Multiple independent community analyses and forum threads haveioft’s attestation is product‑scoped, not an exclusivity guarantee.
Short answer to the user’s question
- No — Azure Linux is not necessarily the only Microsoft product that could include the vulnerable open‑source component referenced by CVE‑2023‑39325. Microsoft’s public statement names Azure Linux because Microsoft checked that distribution and found the upstream component there; it does not prove that other Microsoft products cannot carry the same vulnerable library. Treat the MSRC attestation as authoritative for Azure Linux b the broader Microsoft product portfolio.
- The correct operational posture for defenders and operators is: prioritize Azure Linux images for immediate remediation if you run them, but also perform artifact‑level verification and scanning across other Microsoft images, binaries, SDKs, agent packages, and container images present in your estate. Microsoft has committed to expanding CSAF/VEX attestations and updating CVE mappings when additional affected Microsoft products are identified; until that mapping is published, assume other Microsoft artifacts could be affected and verify.
Why the attestation vs exclusivity distinction matters
A short, machine‑readable VEX/CSAF attestation that “Product X includes component Y” is an inventory statement: it tells customerwas checked and confirmed in scope. That is valuable and actionable for operators who run that exact product. But there are several important reasons you cannot infer global exclusivity from such a statement:- Large vendors ship many artifacts. A single library can appear in many places: container builde runtimes, internal agents, telemetry collectors, appliance firmware, and more. A product‑level attestation confirms audit coverage for the named product but doesn’t mean every Microsoft-built binary or image has been exhaustively scanned.
- Binary reuse and rebuilds create duplicates. The same vulnerable upstream code can be replicated across multiple product images via shared build tooling, vendor packaging, or third‑party components. Until a vendor’s attestations enumerate each artifact, defenders must do their own artifact discovery.
- The Go standard library is included implicitly when building Go binaries. A team that compiles a Go server with an older toolchain will embed the vulnerable behavior regardless of which distribution the server runs on. In other words, presence of vulnerable code is a function of how a given binary was built, not just which OS image it runs on. (groups.google.com)
Where the risk can hide inside Microsoft artifacts (and generally in any enterprise)
Below are the places you should check — they’re not an accusation that Microsoft necessarily ships the vulnerable code in all of them, but they are logical carriers of Go code in large vendor ecosystems and should be audited.- Container images and base OS images published by Microsoft (including Azure Marketplace images and management images).
- Azure agent components, telemetry or monitoring agents that Microsoft supplies to customer VMs or PaaS instances (any agent written in Go or embedding native Go modules).
- Microsoft SDKs and CLIs that are distributed as prebuilt Go binaries (for instance, third‑party or partner projects or community tools Microsoft distributes that may be Go‑based).
- Cloud native control plane components, operators, or Kubernetes bundles used by Microsoft services or supplied as bits (containers or binaries). Several vendors and distributions patched Kubernetes-related builds because they depended on Go — that same logic applies to vendor-supplied components.
- Any compiled binaries you install that were built with an older Go toolchain; the fix requires rebuilding with patched Go releases. (groups.google.com)
How to verify exposure in your environment (practical steps)
- Inventory first: collect the list of Microsoft-supplied images, binaries, SDK packages, agents, and containers you run. Don’t rely solely on product‑level CVE mappings; treat the MSRC attestation as a starting point.
- Detect Go binaries and find embedded build info:
- For binaries built with Go 1.18+, use the embedded build info: run
go version -m /path/to/binaryto print module and build metadata embedded in the executable. This will show the Go toolchain version used to build the binary, and the module dependencies recorded at build time. That makes it straightforward to discover whether a binary was built with a fixed or vulnerable Go version. Thego version -mbehavior and the debug/buildinfo support were added in Go 1.18. - If you cannot run
go version -m(older Go-produced binaries or stripped artifacts), use heuristics:strings,readelf/objdump, oridenton ELF/PE/Mach‑O to find Go build metadata or module markers, and pass suspicious candidates to tools that parse the Go build info. The presence of Go module metadata in the binary is a reliable indicator of Go origin. - Search for module imports:
- If you have source code or the image’s filesystem, search for references to
golang.org/x/net/http2ornet/httpusage patterns thas. For container images, use tools that can enumerate installed modules and packages inside images (image scanning tools or SBOM generators). - Check Go toolchain and module versions:
- If you find Go-built artifacts, verify whether the Go runtime or the modules are older than the fixed releases: affected stdlib versions are older than Go 1.20.10 / 1.21.3; affected golang.org/x/net/http2 is older than v0.17.0. If a binary was built with an older toolchain, rebuild it with a fixed Go release. (groups.google.com)
- For containers and images you do not build: assume they may be vulnerable until the vendor provides a rebuild, patch, or a VEX/CSAF attestation that explicitly lists the artifact as fixed. Microsoft has committed to expanding its machine‑readable attestations (CSAF/VEX) over time; use those attestations when available but do independent verification in the meantime.
- Apply network and application mitigations:
- Rate limit incoming HTTP/2 connections per client or IP.
- If possible, configure front‑line proxies or load balancers to limit streams per connection, limit simultaneous requests per client, or disable HTTP/2 for untrusted inbound endpoints until you can confirm server binaries are rebuilt with the patched Go runtime.
- Implement application‑level timeouts and worker pools that bound concurrency, independent of the HTTP/2 library behavior.
Rebuilding and remediating — recommended steps
- Identify binaries that use the vulnerable code. Use
go version -mwhere possible. - Rebuild those binaries with a fixed Go toolchain (Go 1.20.10, Go 1.21.3 or later) OR ensure dependent modules such as golang.org/x/net/http2 are upgraded to v0.17.0+ and then rebuild. Static rebuild is required — updating the OS runtime alone will not fix an already-built Go binary. (groups.google.com)
- Replace published container images with rebuilt images and redeploy. For images you do not control, coordinate with the vendor for patched releases or mitigation guidance.
- Update your orchestration and ingress controls to mitigate exposure while you rebuild artifacts (rate limits, HTTP/2 stream caps, connection limits).
- Validate after rebuild: run simulated rapid‑reset tests in a controlled lab to ensure your patched server does not spawn excessive handlers under reset floods, and verify your front‑end behavior (queueing or connection termination) conforms to the patched semantics.
Detection and telemetry: signals to watch in your environment
- Spikes in goroutine counts or thread counts for known Go services during short windows of HTTP/2 trm to short-lived connections or many simultaneous handlers.
- Repeated CPU spikes tied to handling connections where the remote side issues RST_STREAM frames rapidly.
- Load-balancer or proxy logs showing many HTTP/2 streams coming from a small set of client IPs.
Vendor attestations and the role of VEX/CSAF
Microsoft’s commitment to publish machine‑readable VEX/CSAF attestations is an important advance in transparency: those attestations let customers automate the process of mapping CVEs to specific Microsoft artifacts. But these attestations are onlyoverage: an attestation for Azure Linux is an authoritative statement about Azure Linux; it doesn’t automatically cover every Microsoft image, SDK, or or enumerates broader coverage, defenders must pair vendor attestations with their own artifact discovery and SBOM validation.When Microsoft expands the VEX entries to list additional products or images carrying the vulnerable component, those entries will be the authoritative signal for whatever product is named. Microsoft has said it williare identified — but until that happens, use the vendor attestation as a strong but scoped data point, not as universal proof of absence elsewhere.
Strengths and risks in Microsoft’s public approach
Strengths- Microsoft’s concise attestation gives immediate, actionable guidance to Azure Linux customers: update those images and prioritize remediation. That saves time for the subset of customers who run Azure Linux images.
- The commitment to CSAF/VEX machine-readable attestations raises the bar for supply‑chain transparency and enables automation where coverage exists.
- Product‑scoped attestations can create a false sense of completeness. Operators who interpret “Azure Linux is affected” as “only Azure Linux is affected” will under‑search their estate and may miss vulnerable Microsoft‑supplied artifacts. Multiple community analyses and forum posts warn against this misinterpretation.
- The dependency model for Go means that vulnerabilities propagate into compiled binaries. Remediation therefore requires rebuihains; simply upgrading an OS package or updating runtime libraries in a container image won’t fix statically compiled Go binaries that were built with older versions. This rebuild step is operationally heavier than a simple package install. (groups.google.com)
Practical checklist for WindowsForum readers (quick, actionable)
- If you run Azure Linux images: prioritize applying the published updates/patches as Microsoft has advised. Treat Microsoft’s attestation for Azure Linux as high‑priority guidance.
- Inventory Microsoft-supplied binaries and images in your environment; find Go-built artifacts using
go version -mor image scanning. - Rebuild any internally controlled Go services with Go 1.20.10 / 1.21.3 or later, or upgrade golang.org/x/net/http2 to v0.17oups.google.com]([security] Go 1.21.3 and Go 1.20.10 are released))
- For third‑party or vendor images: request VEX/CSAF attestations or patched images; apply ingress rate limits and HTTP/2 stream caps where possible until patched artifacts are in place.
- Monitor telemetry for goroutine, CPU, or memory spikes tied to short HTTP/2 sessions and investigate immediately.
Conclusion
CVE‑2023‑39325 is an important availability bug in Go’s HTTP/2 handling that was fixed upstream by bounding concurrently executing handler goroutines to the stream concurrency limit. Microsoft’s public advisory identifying Azure Linux as including the implicated open‑source component is truthful and useful to Azure Linux customers, but it is a product‑scoped attestation — not proof that Azure Linux is the only Microsoft artifact that could contain the vulnerable library. Operators should treat Microsoft’s attestation as authoritative for the named product, prioritize those images for remediation, and at the same time conduct artifact‑level discovery and rebuild work across their estate to find and fix any other occurrences of the vulnerable Go code. (groups.google.com)Source: MSRC Security Update Guide - Microsoft Security Response Center