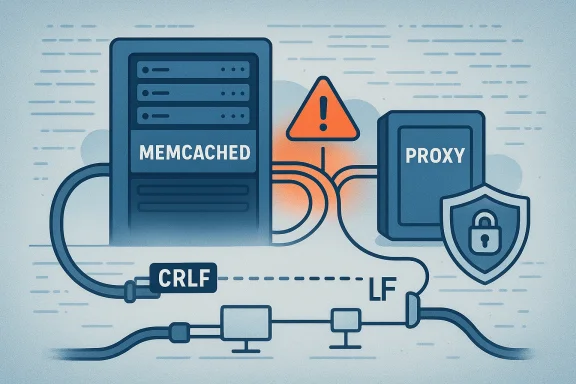
The discovery that a single missing carriage return could destabilize widely deployed caching infrastructure exposed a familiar, uncomfortable truth: simple parser assumptions still cause outsized operational and security consequences. CVE‑2023‑46853 is an off‑by‑one error in Memcached’s proxy request handling that appears when a request ends with a bare '\n' instead of the expected '\r\n'. The defect was fixed in the upstream 1.6.22 release, but the vulnerability’s reach, the ambiguity around exploitability, and the operational realities of memcached deployments make this more than a narrow developer bug — it is a timely reminder that network-facing parsers and optional subsystems deserve careful scrutiny and a fast, disciplined patch cadence.
Memcached is a high‑performance, in‑memory key-value cache used by countless web applications and platforms to accelerate read paths and relieve databases. The project maintains a compact core with an optional proxy subsystem that users compile and enable explicitly. The proxy mode re-implements a text protocol parser to bridge clients and backends and to support features such as routing and sharding. The vulnerability tracked as CVE‑2023‑46853 was introduced into that proxy parser and affects Memcached builds that include and run the proxy subsystem.
Upstream maintainers identified the bug in the 1.6.22 release cycle and issued a targeted change described as “proxy: fix off‑by‑one if \r is missing.” The commit and release notes clarify the scope: the proxy parser assumed requests used strict CRLF ("\r\n") line endings, but the implementation historically accepted lone LF ("\n") too. That inconsistency produced cases where tokenization and length accounting could go wrong — an archetypal off‑by‑one issue — and the patch replaces uses of reqlen-based arithmetic with an explicit end-of-line index to avoid indexing past the buffer. (github.com)
Key, verifiable facts:
However — and this is important for defenders and incident responders — the RCE aspect is context dependent and less clearly documented. Several vendor advisories and package trackers describe the impact as “crash resulting in denial of service, or possibly execute arbitrary code.” That phrasing is accurate: an off‑by‑one leading to memory corruption can sometimes be escalated to code execution, but doing so reliably requires specific memory layout and exploitation primitives that are not universally present. In other words, DoS is a practical, high‑confidence outcome; remote code execution is a plausible but lower-confidence outcome without a demonstrated public exploit.
What this means operationally:
Practical verification steps for operators:
Editorial takeaways for engineers:
Inventory checks (high priority)
Conclusion: treat CVE‑2023‑46853 as an urgent patching item for proxy‑enabled memcached installations, harden network exposure for all caching tiers, and use this incident to test the completeness of your inventory and patching workflows — optional features become surprises only when they are forgotten. (github.com)
Source: MSRC Security Update Guide - Microsoft Security Response Center
 Background
Background
Memcached is a high‑performance, in‑memory key-value cache used by countless web applications and platforms to accelerate read paths and relieve databases. The project maintains a compact core with an optional proxy subsystem that users compile and enable explicitly. The proxy mode re-implements a text protocol parser to bridge clients and backends and to support features such as routing and sharding. The vulnerability tracked as CVE‑2023‑46853 was introduced into that proxy parser and affects Memcached builds that include and run the proxy subsystem.Upstream maintainers identified the bug in the 1.6.22 release cycle and issued a targeted change described as “proxy: fix off‑by‑one if \r is missing.” The commit and release notes clarify the scope: the proxy parser assumed requests used strict CRLF ("\r\n") line endings, but the implementation historically accepted lone LF ("\n") too. That inconsistency produced cases where tokenization and length accounting could go wrong — an archetypal off‑by‑one issue — and the patch replaces uses of reqlen-based arithmetic with an explicit end-of-line index to avoid indexing past the buffer. (github.com)
What exactly is the bug?
At a technical level, CVE‑2023‑46853 is a classic parser boundary error rooted in assumptions about line terminators. When the proxy parser encountered a request terminated with a bare line feed ('\n') rather than the two‑byte carriage return + line feed ('\r\n'), internal index math could miscalculate the length of tokens, allowing an off‑by‑one read or write during request processing. In practice the behavior could lead to crashes (denial‑of‑service) and, in some configurations and depending on surrounding memory layout, might make memory corruption exploitable for code execution. Several distributor advisories therefore treat the impact as DoS with a possible RCE vector, while the upstream release notes emphasize that the fix addresses the parser indexing problem.Key, verifiable facts:
- Affected upstream range: memcached before 1.6.22.
- The bug is present in the proxy subsystem and only affects builds started with proxy support enabled and running in proxy mode. The upstream release notes call this out explicitly: “This does not affect you unless you build with --enable-proxy and enable the proxy at start time.”
- The upstream commit that fixes the issue is 6987918… and the commit message explains the change and the author’s caution while testing. (github.com)
Impact and exploitability: DoS confirmed, RCE plausible but unproven
Security advisories and distribution trackers converge on a reliable picture: the bug can be used to crash memcached instances running the proxy, producing denial‑of‑service. Multiple downstream notices and vulnerability databases assign critical severity and a high CVSS score (commonly quoted as CVSS v3.1 = 9.8), primarily because memcached typically listens on network sockets and the vulnerability is trivially reachable across the network where the proxy is exposed.However — and this is important for defenders and incident responders — the RCE aspect is context dependent and less clearly documented. Several vendor advisories and package trackers describe the impact as “crash resulting in denial of service, or possibly execute arbitrary code.” That phrasing is accurate: an off‑by‑one leading to memory corruption can sometimes be escalated to code execution, but doing so reliably requires specific memory layout and exploitation primitives that are not universally present. In other words, DoS is a practical, high‑confidence outcome; remote code execution is a plausible but lower-confidence outcome without a demonstrated public exploit.
What this means operationally:
- If memcached is running proxy mode and accessible from untrusted networks, an attacker can cause immediate service disruption by sending specially formed requests that end with LF-only line endings.
- The severity classification (e.g., CVSS 9.8 in many databases) correctly reflects worst-case impact assumptions that include potential confidentiality and integrity effects if RCE were achieved. Defenders should treat the vulnerability as urgent.
Who is affected?
Not every memcached user. The vulnerability is strictly scoped to:- Memcached builds older than 1.6.22, and
- Those builds that include the optional proxy subsystem (built with --enable-proxy) and have the proxy enabled at runtime.
Practical verification steps for operators:
- Confirm memcached’s version: e.g., the memcached binary’s -h or package manager inspection will show the packaged version. Distributors list which package versions contain the upstream fix.
- Verify whether you built or use a memcached package with proxy support enabled. Upstream warns plainly that if you aren’t using proxy mode you aren’t affected by this specific bug.
The upstream fix and what it reveals about QA
The upstream patch changed parser internals to stop relying on reqlen-based "minus-two" arithmetic and instead compute an explicit end index (endlen) to delimit token parsing. That change closes the off‑by‑one window and was introduced as part of a broader set of proxy subsystem hardening and tests in 1.6.22. The commit message is candid: the maintainer said they “weren’t 100% confident” with the change at first and opened a PR to stage it while running broader tests — a useful, transparent note about legitimate uncertainty in parser refactors. (github.com)Editorial takeaways for engineers:
- Parser code that mixes historical len‑minus arithmetic with partial acceptance of variant terminators (LF vs CRLF) is fragile. Backcompat choices that accept nonstandard inputs complicate correctness.
- The fix is surgical but also exposes the value of expanding tests for boundary conditions, for both canonical and noncanonical line endings.
- Maintaining a small, opt‑in proxy subsystem inside a high‑performance project reduces the attack surface for many users — but its opt‑in nature also increases the chance that CI and packaging permutations miss it.
Detection and hunting guidance
Because memcached is network‑facing and the vulnerability is triggered by malformed proxy requests, detection and hunting should focus on two domains: inventory and anomalous traffic.Inventory checks (high priority)
- Confirm memcached version on all hosts: check package manager (rpm, dpkg, apk, etc.) or the memcached binary to find versions older than 1.6.22. Distribution security notices list package versions that include the fix; if your package is older, treat it as vulnerable until patched.
- Verify whether memcached was built with proxy support. If you obtained memcached from a package repository, check package metadata or vendor advisories — upstream explicitly notes that the issue only affects proxy builds.
- Look for incoming requests to memcached that end with lone '\n' line terminators. If you capture packet traces or application logs that record raw requests, search for requests that omit '\r' before '\n'.
- Monitor for repeated malformed proxy requests followed by memcached crashes or process restarts. Correlate with syslog, service manager events, and application errors from caches timing out.
- If you have network IDS/IPS sensors that can parse memcached text protocol, consider adding custom signatures to detect suspicious proxy requests with LF-only endings or anomalous multiget spacing patterns. (No standardized public IDS rule for CVE‑2023‑46853 was published at time of this advisory; build rules should be validated in test.)
Mitigations and recommended remediation steps
- Patch now (primary remediation)
- Upgrade memcached to 1.6.22 or later from upstream or install your vendor’s fixed package as provided in distribution advisories. Multiple distributors (Ubuntu USN, Debian tracker, SUSE, Amazon Linux ALAS) published updates and backports — use their packages where possible.
- If you cannot patch immediately, implement compensating controls
- Disable proxy mode if you are not actively using proxy features — recompile without --enable-proxy or stop the proxy functionality at runtime where feasible. Upstream emphasized builds without enabled proxy are not affected.
- Restrict network exposure: ensure memcached listens only on private/internal interfaces (bind to 127.0.0.1 or internal IPs) and block access from untrusted networks using host firewalls or network ACLs. Many memcached incidents stem from public exposure.
- Implement network segmentation and allowlist access to memcached hosts. If possible, colocate memcached behind application host-only routes and avoid placing it on a public network.
- Use process hardening: run memcached as an unprivileged user, and use common OS protections (ASLR, hardened libc builds, and container runtime constraints) to raise the cost of exploitation.
- Operational response steps after patching
- Schedule a controlled upgrade during a maintenance window, roll out patched packages in small batches, and verify service behavior under load.
- Where memcached restarts lead to cache warm‑up problems, coordinate with application teams to avoid cascade effects (thundering herd) when caches are flushed or restarted.
- Monitor for failed or malformed requests and any recurrence of crashes after patching, which would warrant deeper investigation.
Detection/patch roll‑out checklist for sysadmins
- 1.) Inventory memcached hosts and confirm package and build flags. If you use a distro package, check the vendor security notice for the fixed package version.
- 2.) If using a custom build with proxy support: plan to rebuild from upstream 1.6.22 or later and redeploy.
- 3.) For immediate containment: bind memcached to local/internal interfaces and block external access to memcached ports (default 11211).
- 4.) Patch sequentially: test on a small set of servers, validate application behavior and cache performance, then roll out widely.
- 5.) After patching, review logs for suspicious inbound traffic correlated with prior crash windows to detect potential exploitation attempts.
Why this bug matters — a systems and supply‑chain perspective
At first glance, CVE‑2023‑46853 is a textbook parser edge case. But the operational and security implications are broader:- Optional subsystems increase the chance of overlooking attack surfaces. Because proxy mode is optional, not every deployment will be automatically covered by vendor packaging or admin attention, which can delay both detection and remediation. Vendor notes and upstream release text explicitly warn operators to check build flags.
- Small parsing differences (LF vs CRLF) are historically a rich source of security problems. Protocol implementations that accept nonstandard inputs for backward compatibility open subtle gaps where index math can misbehave. The memcached commit’s candid comment about inconsistent strictness underscores how backcompat interacts with correctness. (github.com)
- The vulnerability underscores the value of machine-readable vulnerability attestations and mappings. Microsoft’s VEX and CSAF initiatives (and distributors’ advisories) help downstream consumers understand whether a given product, build or distribution is truly affected. For memcached, that clarity — “only proxy builds running proxy mode” — materially lowers the number of affected installs, but only if operators read and act on the attestation.
Limitations and unresolved questions
- Public exploit availability: at the time of writing there were no widely verified, reliable public exploit modules demonstrating repeatable RCE against mainstream builds; most public advisories emphasize DoS and mention RCE as a possible outcome. That uncertainty matters: remediation urgency is high because DoS is trivial, but alarmist claims of immediate RCE everywhere are not supported by documented exploits in the wild. Treat RCE as a worst‑case risk and DoS as an operationally realistic outcome.
- Vendor CVSS and scoring differences: vulnerability databases sometimes show variant scores and guidance. Operators should combine the vendor/distributor advisories (for patch availability and package versions) with upstream notes (for whether proxy support was compiled in) before prioritizing remediation windows.
- Post‑fix behavior: the upstream author’s cautious note about further testing means operators who rely on custom memcached builds should run their full application test suites before mass deployment. The upstream release notes and commit both recommend testing the proxy subsystem more thoroughly. (github.com)
Final assessment and action plan
CVE‑2023‑46853 is a practical, high‑urgency vulnerability for memcached installations that run the optional proxy subsystem and expose that interface to untrusted networks. The technical root cause — an off‑by‑one parser indexing error triggered by LF-only line endings — is straightforward and fixed upstream in 1.6.22. Distributors quickly published fixes and backports, and operators should prioritize remediation as follows:- Immediately inventory your memcached footprint: identify versions and whether proxy mode is enabled. If proxy is not used, the vulnerability does not apply.
- If affected, patch to memcached 1.6.22 or install vendor packages that include the upstream fix. If patching is delayed, block access to memcached from untrusted networks, disable proxy mode, or recompile without --enable-proxy.
- Monitor for signs of exploitation (malformed request patterns and crashes) and coordinate with application owners to manage cache warm‑up after restarts.
- Consider expanding parser boundary tests and hardening CI for optional subsystems going forward. The easiest bugs to exploit are often the ones that arise from lenient inputs combined with brittle indexing logic. (github.com)
Conclusion: treat CVE‑2023‑46853 as an urgent patching item for proxy‑enabled memcached installations, harden network exposure for all caching tiers, and use this incident to test the completeness of your inventory and patching workflows — optional features become surprises only when they are forgotten. (github.com)
Source: MSRC Security Update Guide - Microsoft Security Response Center