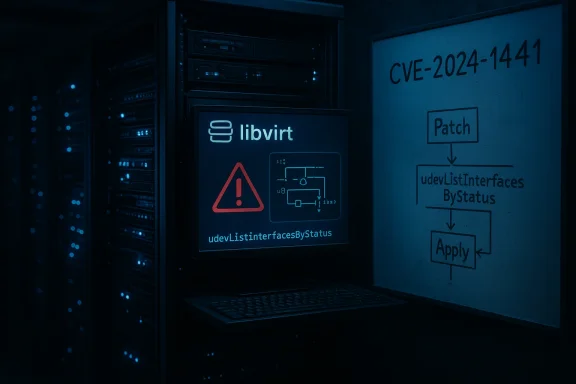
Libvirt has been assigned CVE-2024-1441 for an off-by-one bug in the udevListInterfacesByStatus() function that can be triggered by an unprivileged client to crash the libvirt daemon, producing a denial-of-service condition for virtualization management on affected systems.
Libvirt is the de facto user-space management layer for many Linux virtualization stacks, including KVM/QEMU, and provides the RPC interfaces and daemons that orchestration tools and administrators rely on. On 11 March 2024 the issue now tracked as CVE-2024-1441 was disclosed: an off-by-one boundary check in the udev-based interface listing routine could cause the server-side libvirt daemon to attempt to read or dereference beyond the intended buffer when presented with more interface entries than the function’s local array can hold. That boundary error, combined with changes in how callers handle NULL or zero-length arrays, made a crash reliably reproducible in specific call patterns.
The defect is not a remote code execution vulnerability; its primary impact is availability. The published CVSS v3 score for this defect is 5.5 (Medium), reflecting a local attack vector with low complexity and low required privileges, and an outcome limited to denial of service rather than confidentiality or integrity loss.
A one-line logic change illustrates the problem succinctly: the code originally used a condition equivalent to
The crash is visible in the management tier (libvirtd or the libvirt-managed RPC daemon), which can disrupt management operations and client tooling that expect the daemon to remain available.
Distributors that ship libvirt reacted by building patched packages and issuing security advisories and errata. Enterprise and community vendors that released fixes include major Linux vendors; downstream packages were updated for multiple releases, and distribution security teams recommended applying the updates through standard package-management channels. Where backports were required (for older LTS kernels and long-term distribution trees), maintainers produced cherry-picked patches and rolled them into point releases of libvirt packages.
The practical consequence for administrators is straightforward: install the available security update for libvirt from your distribution, and restart the libvirt daemon to bind in the fixed code.
For administrators who operate multi-OS environments, the operational patterns are directly transferable: restrict access to control sockets and APIs, apply vendor updates promptly, and instrument the management plane for visibility and fast recovery.
However, the broader takeaways remain: continuous fuzzing and stricter input validation, combined with conservative exposure of management interfaces, are essential to keep virtualization management robust. For operators, the action is immediate and unambiguous: install the patched libvirt packages, restart the daemon, and tighten access control around any libvirt endpoints. For maintainers, the action is structural: use automated testing and secure-by-default APIs to reduce the likelihood that a latent off-by-one or boundary error can translate into an operational outage.
If you manage virtualization hosts with libvirt, prioritize the patch and verify that only trusted accounts can reach your libvirt service. The fix is small; the risk of ignoring it is operationally material in environments where non-privileged users can reach the management plane.
Source: MSRC Security Update Guide - Microsoft Security Response Center
 Background
Background
Libvirt is the de facto user-space management layer for many Linux virtualization stacks, including KVM/QEMU, and provides the RPC interfaces and daemons that orchestration tools and administrators rely on. On 11 March 2024 the issue now tracked as CVE-2024-1441 was disclosed: an off-by-one boundary check in the udev-based interface listing routine could cause the server-side libvirt daemon to attempt to read or dereference beyond the intended buffer when presented with more interface entries than the function’s local array can hold. That boundary error, combined with changes in how callers handle NULL or zero-length arrays, made a crash reliably reproducible in specific call patterns.The defect is not a remote code execution vulnerability; its primary impact is availability. The published CVSS v3 score for this defect is 5.5 (Medium), reflecting a local attack vector with low complexity and low required privileges, and an outcome limited to denial of service rather than confidentiality or integrity loss.
What exactly went wrong: the technical root cause
The vulnerable function
The flaw lives in the udev backend implementation used by libvirt when enumerating network interfaces. The function in question, udevListInterfacesByStatus(), collects names for detected interfaces into a caller-provided array. The implementation contained a comparison that allowed writing (or dereferencing) when the count of interfaces equaled the declared array length.A one-line logic change illustrates the problem succinctly: the code originally used a condition equivalent to
- if (count > names_len) break;
- if (count >= names_len) break;
How the bug became exploitable
The bug was introduced when the udev-based interface backend was added (the function traces back to earlier libvirt releases), and it was made worse by later changes (circa 2019) that modified the semantics of the caller-side verification to accept NULL pointers paired with a size value of 0. That change meant the off-by-one no longer produced a rare out-of-bounds write; it became a deterministic dereference of a NULL pointer in a particular input scenario. An unprivileged client that can make the affected RPC call — for example, a local user with access to libvirt’s socket — can craft input to hit the exact array/failure conditions and crash the libvirt daemon.The crash is visible in the management tier (libvirtd or the libvirt-managed RPC daemon), which can disrupt management operations and client tooling that expect the daemon to remain available.
Who and what is affected
- Any host running an impacted version of libvirt with the udev interface backend enabled is potentially affected.
- Exploitation requires local access: a process or user account that can connect to libvirt’s communication endpoint (often a UNIX domain socket) or otherwise invoke the vulnerable code path.
- Cloud or multi-tenant systems that expose libvirt management interfaces to low-privilege tenants, containers, or CI runners are the highest risk, because an attacker with modest privileges could cause a host-level management outage.
- The vulnerability does not directly allow reading guest memory, stealing credentials, or altering guest disk contents. Its principal effect is to make management APIs unavailable and, in some setups, to interfere with operations that rely on the daemon (start/stop/migrate/checkpoint, etc.).
Patching and vendor response
Upstream maintainers addressed the defect with a minimal but correct change to the failing boundary test. The libvirt development mailing list and the upstream commits show that the patch was pushed promptly and that it was assigned CVE-2024-1441.Distributors that ship libvirt reacted by building patched packages and issuing security advisories and errata. Enterprise and community vendors that released fixes include major Linux vendors; downstream packages were updated for multiple releases, and distribution security teams recommended applying the updates through standard package-management channels. Where backports were required (for older LTS kernels and long-term distribution trees), maintainers produced cherry-picked patches and rolled them into point releases of libvirt packages.
The practical consequence for administrators is straightforward: install the available security update for libvirt from your distribution, and restart the libvirt daemon to bind in the fixed code.
Risk assessment: how dangerous is CVE-2024-1441 in the wild?
Scope of impact (short answer)
The bug is a local, low-privilege denial-of-service. In well-configured environments where libvirt is reachable only by trusted administrators, the real-world risk is modest. In multi-tenant or misconfigured environments where non-privileged users can access libvirt APIs, the risk is materially higher and warrants rapid patching.Factors that reduce risk
- Attack requires local access to the libvirt endpoint; it cannot be triggered purely over the public network unless the service was mistakenly exposed.
- There is no evidence the bug leads to code execution; it appears limited to crashing the daemon (availability impact).
- Many organizations already restrict access to libvirt sockets or protect libvirtd with system-level controls (UNIX socket permissions, TLS for remote connections, firewalling) that prevent unprivileged clients from reaching the daemon.
Factors that raise risk
- Virtualized hosts that intentionally expose libvirt endpoints (for remote administration, orchestration, or APIs within multi-tenant control planes) provide a live attack surface.
- Containerized workloads or CI systems that share the host’s libvirt socket may inadvertently grant untrusted code access.
- An attacker could leverage repeated crashes as part of a broader disruption or to hinder incident response (e.g., preventing administrators from using libvirt to inspect or remediate guest state).
Operational impact scenarios
- On an admin workstation or isolated lab machine, a crash of libvirtd is a nuisance: restart the service and continue.
- On a production virtualization host, a daemon crash can interrupt automation (management APIs, monitoring, and scheduled operations). Depending on the orchestration layer, the practical effect could be partial loss of management visibility rather than immediate guest termination. However, some management actions (e.g., live migration or dynamic configuration changes) could fail mid-procedure, increasing operational risk.
- In cloud or hosting platforms that expose libvirt to tenants or over poorly controlled networks, an attacker with only guest or container privileges could cause service outages across multiple hosts if chaining access.
Mitigation and recommended actions (immediate and medium-term)
Immediate steps for operators (apply within hours)
- Patch libvirt: Install the vendor-provided security update for your distribution. This is the definitive fix and must be the top priority.
- Restart the libvirt daemon: After updating, restart libvirtd (or the distribution’s equivalent) to load the patched code. Typical commands are
systemctl restart libvirtdorsystemctl restart virtqemuddepending on the setup. - Harden access: Ensure libvirt’s UNIX socket and any remote endpoints are accessible only to trusted users. Tighten permissions on /var/run/libvirt/* and related sockets.
- Audit recent crashes: Check system logs and libvirt logs for unexplained libvirt daemon crashes or core dumps that could indicate exploitation attempts. Look for crash timestamps and repeated failures.
- Temporary access restriction: If patching is not immediately possible, consider temporarily restricting libvirt access (e.g., by disabling remote TCP listeners or changing socket permissions) to reduce risk while you stage updates.
Medium-term and procedural measures (apply within days to weeks)
- Least-privilege for automation: Re-evaluate automation and CI systems that interact with libvirt. Provide the minimum necessary privileges and consider proxying or intermediating access via a hardened service that performs access checks.
- Network-level protections: Block access to any libvirt management ports at the network perimeter and enforce host-level firewall rules.
- Monitoring: Add monitoring for libvirt service restarts, crash counts, and anomalous RPC calls. Alert on repeated restarts or crashes.
- Incident handling playbooks: Update incident-response runbooks to include steps for detecting and remediating libvirt daemon crashes and to restore management functions quickly.
Engineering lessons and defensive recommendations
This report highlights several broader software-quality and operational lessons for teams that build or maintain virtualization management layers.1. Off-by-one bugs are persistent and cheap to fix — but expensive if they reach production
A single relational operator in a boundary test can upset the assumptions of the entire call chain. The fix here was a straightforward change in the comparison operator, but the fault had been latent for years and was amplified by a later API convenience change. Stronger pre-commit checks and code review discipline around boundary conditions would help catch these errors earlier.2. Input validation must be enforced at the right layer
The vulnerability became more severe after a change to caller validation semantics allowed NULL arrays with size zero. That demonstrates how defensive checks must be enforced at the point of allocation/deallocation and server boundaries, not only in higher-level API wrappers. Library functions that accept externally supplied buffer pointers need to validate both pointer and declared length before dereferencing.3. Use memory-safe idioms where feasible
While rewriting low-level C systems is not always practical, the libvirt example underscores the benefits of memory-safe patterns (e.g., bounds-checked helper functions, explicit capacity-tracking structures, or even selective use of safer languages for components that parse or deserialize external data). Projects should weigh the incremental engineering cost against the high cost of subtle memory-safety bugs.4. Fuzzing and automated testing pay dividends
A number of modern vulnerabilities in system daemons have been discovered via fuzz testing. Integrating fuzzing (AFL, libFuzzer, or corpus-based approaches) into CI pipelines — especially for RPC and serialization/deserialization logic — increases the odds of catching off-by-one and negative-length issues before release.5. Limit the trusted surface area in multi-tenant setups
Operationally, treat management daemons as high-value targets: minimize their exposure, standardize access control, and isolate management traffic from tenant workloads. A misconfigured management endpoint is an open invitation for low-privileged attackers.Practical checklist for sysadmins
- Apply vendor/libvirt security updates immediately.
- Restart libvirt-related services after patching.
- Review which users and services can access the libvirt socket; remove any unnecessary privileges.
- If you run orchestration or CI systems on hosts that connect to libvirt, validate their user context and isolation.
- Scan logs for libvirt crashes or core dumps and correlate with user sessions to identify unusual activity.
- Implement or verify monitoring that will alert on libvirt service instability.
- If you cannot patch immediately: restrict access to libvirt sockets and disable remote, unauthenticated listeners.
Why this matters to WindowsForum readers (and cross-platform operators)
Even though libvirt is a Linux-oriented project and WindowsForum’s readership may primarily manage Windows virtualization stacks, the issues raised by CVE-2024-1441 are universal: management-plane daemons with broad privileges can be the most strategic targets for attackers or accidental outages. The incident is a timely reminder to all virtualization platform operators — whether running hypervisor-based hosts on Linux, Windows Server Hyper-V, or cloud control planes — to practise robust access control, perform rapid patch management, and treat management APIs as attack surfaces that demand careful hardening.For administrators who operate multi-OS environments, the operational patterns are directly transferable: restrict access to control sockets and APIs, apply vendor updates promptly, and instrument the management plane for visibility and fast recovery.
Final thoughts and closing analysis
CVE-2024-1441 exemplifies how small coding errors — a single comparison operator — can escalate when combined with API changes and real-world deployment complexity. The vulnerability’s impact is constrained (availability-only, local vector), but that does not diminish its operational importance in shared or multi-tenant environments. The one-line upstream fix demonstrates healthy project responsiveness, and the coordinated distribution-level backports show standard security hygiene working as intended.However, the broader takeaways remain: continuous fuzzing and stricter input validation, combined with conservative exposure of management interfaces, are essential to keep virtualization management robust. For operators, the action is immediate and unambiguous: install the patched libvirt packages, restart the daemon, and tighten access control around any libvirt endpoints. For maintainers, the action is structural: use automated testing and secure-by-default APIs to reduce the likelihood that a latent off-by-one or boundary error can translate into an operational outage.
If you manage virtualization hosts with libvirt, prioritize the patch and verify that only trusted accounts can reach your libvirt service. The fix is small; the risk of ignoring it is operationally material in environments where non-privileged users can reach the management plane.
Source: MSRC Security Update Guide - Microsoft Security Response Center