The short answer is: No — Azure Linux is not, and cannot be treated as, a categorical guarantee that other Microsoft products do or do not include the same open‑source component; for CVE‑2024‑1874 in particular the practical exposure is Windows‑specific and therefore Azure Linux itself is not the primary risk vector, while other Microsoft products or services that run PHP on Windows (or ship Windows PHP builds) are the ones operators must check immediately.
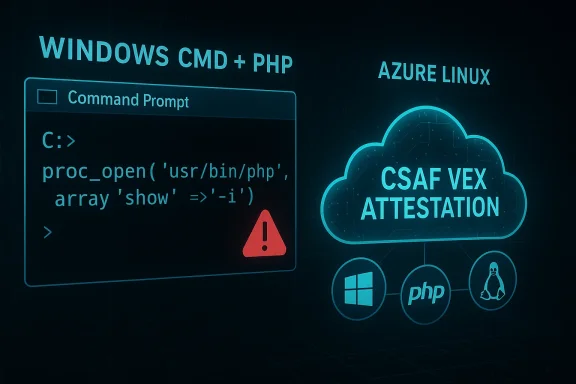
CVE‑2024‑1874 emerged as part of a broader class of “BatBadBut” command‑injection issues that affect how several runtimes prepare and escape command‑line arguments when launching batch files on Windows. The bug is a flaw in PHP’s proc_open() handling when the $command parameter is supplied in array form: under specific conditions, arguments are not escaped correctly and a malicious argument can be interpreted by the Windows command processor, enabling arbitrary command execution.
The PHP project issued security releases that remedied the original defect; later follow‑up fixes addressed edge cases in the original remediation. Those fixes—and the versions that include them—are the canonical mitigations for systems running PHP. Importantly, the root cause is not a Linux kernel driver or a typical “library” that is identically exercisable across OSes; it is an interaction between PHP’s process‑launching logic and Windows’ command‑line/batch execution behavior. That operating‑system dependence is why the vulnerability manifests on Windows deployments and why Linux distributions (including Azure Linux) are not exposed in the same way.
Microsoft’s public security machinery has adopted a product‑scoped attestation model: for certain upstream open‑source components Microsoft has published machine‑readable CSAF/VEX attestations that say “Azure Linux includes this open‑source library and is therefore potentially affected,” and Microsoft has committed to update those attestations if additional Microsoft products are identified. That wording is deliberate and useful — it’s an authoritative signal for customers using Azure Linux — but it is not a statement of exclusivity. In plain terms: when Microsoft names Azure Linux, it is telling you “we checked this product and found the component”; it is not telling you “no other Microsoft things contain this component.” That nuance matters for incident triage and enterprise risk management.
The vulnerability occurs because, when the invoked target is a Windows batch file (.bat or .cmd), the Windows CreateProcess semantics implicitly cause cmd.exe to be used and to re‑parse the command line. Under those conditions the PHP escaping code did not fully anticipate Windows’ parsing idiosyncrasies and some crafted arguments could escape their intended argument context and be treated as new commands or control operators by cmd.exe. In short: PHP thought it had bypassed the shell; Windows’ behavior (and nuances in the way PHP built the command line for batch files) meant that bypass was illusory.
In short: Azure Linux being named means Azure Linux is a known and attested carrier; it is not a global non‑exposure statement for all Microsoft SKUs, nor is it a guarantee that other Microsoft products have been exhaustively checked.
CVE‑2024‑1874 is a useful reminder of two perennial truths in software security. First, subtle differences in operating‑system semantics can turn a seemingly safe API pattern into a dangerous vector; second, vendor attestations are powerful but limited tools — they accelerate triage for the named product, but do not replace rigorous artifact‑level verification across an organisation’s entire estate. Follow the checklist above, patch aggressively where PHP runs on Windows, and use Microsoft’s VEX/CSAF outputs as the starting point for an evidence‑based remediation program rather than the final word.
Source: MSRC Security Update Guide - Microsoft Security Response Center
 Background / Overview
Background / Overview
CVE‑2024‑1874 emerged as part of a broader class of “BatBadBut” command‑injection issues that affect how several runtimes prepare and escape command‑line arguments when launching batch files on Windows. The bug is a flaw in PHP’s proc_open() handling when the $command parameter is supplied in array form: under specific conditions, arguments are not escaped correctly and a malicious argument can be interpreted by the Windows command processor, enabling arbitrary command execution.The PHP project issued security releases that remedied the original defect; later follow‑up fixes addressed edge cases in the original remediation. Those fixes—and the versions that include them—are the canonical mitigations for systems running PHP. Importantly, the root cause is not a Linux kernel driver or a typical “library” that is identically exercisable across OSes; it is an interaction between PHP’s process‑launching logic and Windows’ command‑line/batch execution behavior. That operating‑system dependence is why the vulnerability manifests on Windows deployments and why Linux distributions (including Azure Linux) are not exposed in the same way.
Microsoft’s public security machinery has adopted a product‑scoped attestation model: for certain upstream open‑source components Microsoft has published machine‑readable CSAF/VEX attestations that say “Azure Linux includes this open‑source library and is therefore potentially affected,” and Microsoft has committed to update those attestations if additional Microsoft products are identified. That wording is deliberate and useful — it’s an authoritative signal for customers using Azure Linux — but it is not a statement of exclusivity. In plain terms: when Microsoft names Azure Linux, it is telling you “we checked this product and found the component”; it is not telling you “no other Microsoft things contain this component.” That nuance matters for incident triage and enterprise risk management.
What CVE‑2024‑1874 actually is — technical details
How proc_open() can be used safely (and how it failed here)
proc_open() provides a way for PHP scripts to spawn external processes and interact with their stdio streams. To avoid shell interpretation of arguments, PHP supports passing the command as an array: the array form is meant to bypass the shell and allow safe, per‑argument passing. The idea is simple: the runtime creates a process directly and hands arguments to the OS, avoiding shell parsing that can turn arguments into additional commands.The vulnerability occurs because, when the invoked target is a Windows batch file (.bat or .cmd), the Windows CreateProcess semantics implicitly cause cmd.exe to be used and to re‑parse the command line. Under those conditions the PHP escaping code did not fully anticipate Windows’ parsing idiosyncrasies and some crafted arguments could escape their intended argument context and be treated as new commands or control operators by cmd.exe. In short: PHP thought it had bypassed the shell; Windows’ behavior (and nuances in the way PHP built the command line for batch files) meant that bypass was illusory.
Attack surface and prerequisites
- The vulnerability is exploitable when:
- PHP is running on a Windows host, and
- application code calls proc_open() using the array form for the command, and
- the application supplies attacker‑controlled data into one of those arguments, and
- the invoked target is a batch script or command that causes cmd.exe to be involved.
- The exploit requires remote input that reaches application code that calls proc_open() in that unsafe pattern.
- The vulnerability is not a generic remote exploit against arbitrary PHP installations; it requires the specific combination above.
Scope: Windows vs. Linux
- This flaw is inherently Windows‑centric because it depends on cmd.exe’s parsing and the way Windows executes .bat/.cmd files.
- On Linux systems, including Azure Linux, the shell behavior and process‑launch semantics differ; therefore Linux builds of PHP were not susceptible to the same cmd.exe parsing vector in the same way.
- Linux PHP packages still received updates during the incident cycle because the upstream fix was applied to the PHP source tree and distributions track PHP versioning; but the exploitability model that triggered the high criticality assessment was Windows‑specific.
What Microsoft’s Azure Linux message actually means — reading the nuance
Microsoft has been publishing product attestation metadata in CSAF/VEX format to make it easier for customers and automation systems to understand which Microsoft product families ship specific upstream components. When Microsoft says “Azure Linux includes this open‑source library and is therefore potentially affected,” two distinct facts are being conveyed:- Microsoft has completed an inventory for the Azure Linux product family and found the upstream component in those images; therefore Azure Linux customers should treat their Azure Linux images as in‑scope for triage and remediation.
- Microsoft has a process promise: they will update the CVE and the VEX/CSAF records if they identify additional Microsoft products that also ship the component.
In short: Azure Linux being named means Azure Linux is a known and attested carrier; it is not a global non‑exposure statement for all Microsoft SKUs, nor is it a guarantee that other Microsoft products have been exhaustively checked.
Direct answer to the user’s question (expanded)
- If you are asking “Is Azure Linux the only Microsoft product that includes this open‑source library and is therefore potentially affected?” the correct operational answer is: No, Azure Linux is not necessarily the only Microsoft product that could carry a given upstream component, and Microsoft’s attestation is a scoped statement for Azure Linux only.
- If you are asking specifically about CVE‑2024‑1874 (the PHP proc_open() command‑injection issue), then for this vulnerability the practical exposure is focused on Windows PHP builds and Windows hosts. Azure Linux — as a Linux distribution — does not present the same cmd.exe attack surface; it therefore is not the primary thing you should worry about for this exact CVE. Conversely, Microsoft artifacts that run PHP on Windows — Windows Server images, custom Windows VM images, any legacy Windows App Service or service that allowed Windows PHP handlers — are the places to look.
Why this distinction matters to operators and security teams
- Treat Microsoft’s VEX/CSAF attestation for Azure Linux as authoritative for Azure Linux images. If you run Azure Linux, you should follow Microsoft’s remediation guidance and patch those images.
- Do not assume that a lack of Microsoft attestation for other Microsoft products means “not affected.” If you operate other Microsoft artifacts — Windows Server images, Marketplace images, containerized appliances, on‑premises Microsoft product integrations, or Azure services that run Windows code — you must verify those artifacts individually.
- For CVE‑2024‑1874, prioritize inventorying Windows‑based artifacts that might include PHP. The class of possible carriers is different from a Linux kernel driver vulnerability and requires a different lookup approach.
Practical detection and triage steps (what to do now)
Follow these steps in order. The numbered list is a practical playbook you can run in minutes.- Inventory Windows hosts and services
- Identify any Windows virtual machines, Windows Server images, and Windows‑based PaaS components in your environment.
- Query your orchestration/CMDB system for installations of PHP on Windows.
- Identify PHP runtime versions on candidate hosts
- Run php -v on the host or check the runtime configuration exposed via your management tooling.
- Compare results to the patched versions: ensure hosts are running PHP versions that include the fix for CVE‑2024‑1874 and the follow‑up trailing‑space bypass fix where applicable.
- Locate code that uses proc_open() with array syntax
- Search application source for proc_open( [ or proc_open( array(...) ) patterns.
- Pay special attention to code that passes user‑controlled values into those arguments.
- Prioritize any host running vulnerable PHP on Windows
- If you find Windows hosts running an affected PHP version and the application calls proc_open() with user data, treat that host as high priority for patching and code review.
- Apply patches and mitigations
- Upgrade PHP to a patched release (see the “Fixed versions” section below).
- Where immediate upgrades are not possible, search for and neutralize code paths that call proc_open() with untrusted data and consider temporary mitigations (deny input vectors, apply strict input validation, or remove the use of proc_open()).
- Monitor for indicators and proof‑of‑concept exploits
- Enable logging around process creation and application error logs; look for unexpected command invocations or non‑standard process arguments.
- Watch threat intel feeds for known PoCs and IOCs tied to this CVE family.
- Ingest Microsoft’s CSAF/VEX attestation feed
- If you operate Azure Linux images or Microsoft artifacts, automate ingestion of Microsoft’s machine‑readable attestations so your CI/CD and vulnerability management systems can correlate product mappings automatically.
Fixed versions, timeline and follow‑ups — what to patch to and why
- The upstream PHP project fixed the primary issue in the security releases dated in April 2024. The initial releases that included the fix for CVE‑2024‑1874 were:
- PHP 8.1.28
- PHP 8.2.18
- PHP 8.3.6
- A follow‑up bypass variant (CVE‑2024‑5585) showed the original fix could be bypassed when command names included trailing spaces; that issue was fixed in subsequent micro‑releases:
- PHP 8.1.29
- PHP 8.2.20
- PHP 8.3.8
- Operational guidance:
- If you run PHP on Windows, upgrade to at least the releases above that correspond to your PHP major line. If you cannot upgrade immediately, apply code-level mitigations (avoid array form for proc_open() where input is from untrusted sources and perform strong input validation).
- If you run PHP on Linux, apply distro/package updates as your distribution recommends; the PHP source fixes were applied upstream and distributions released security updates to reflect those changes. Even though the Windows‑specific exploit vector may not apply on Linux, running the latest patched PHP remains good hygiene.
Microsoft product scope — examples of what to check in a Microsoft environment
For system owners trying to decide which Microsoft artifacts to inspect, common places to look include:- Windows virtual machines and server images (IaaS) that host PHP applications.
- Legacy or custom Windows App Service instances where PHP may have been installed or custom PHP runtimes were used.
- On‑premises or cloud images in the Azure Marketplace that include Windows and a preinstalled PHP runtime.
- Any Microsoft‑delivered appliances or partner‑distributed virtual appliance images that embed Windows and PHP.
- Desktop/server products that embed PHP for administrative functionality (rare, but possible in some bundled appliances or management UIs).
- Note: Linux artifacts such as Azure Linux, WSL distributions, or Linux App Service plans do not provide the cmd.exe environment that this CVE exploits; still, keep them updated as a best practice.
Risk analysis — strengths, limitations, and potential pitfalls
Notable strengths of Microsoft’s attestation approach
- Machine‑readable CSAF/VEX attestations accelerate automated triage and enable security teams to ingest product mappings directly into vulnerability management pipelines.
- Publicly stating the product inventory increases transparency and gives customers declarative guidance about where to start remediating.
Potential risks and common misunderstandings
- Mistaking product‑scoped attestations for global guarantees: many customers will read “Azure Linux includes this open‑source library and is therefore potentially affected” and assume only Azure Linux needs attention. This is incorrect for multi‑artifact vendors.
- Overlooking Windows artifacts: for CVE‑2024‑1874, the high‑risk surface is Windows‑hosted PHP; failing to include Windows images in your inventory will leave gaps.
- Treating absence of attestation as absence of risk: until Microsoft (or any vendor) has scanned and published attestations for all products, silence is not a clean bill of health.
Recommended operational checklist (quick, actionable)
- Immediately: identify Windows hosts that run PHP. If any hosts are on vulnerable PHP versions, upgrade or isolate.
- Short term (hours to days): search codebases for proc_open() usage; patch applications that pass untrusted input into arguments.
- Medium term (days to weeks): automate ingestion of vendor CSAF/VEX attestations and reconcile them with your CMDB.
- Long term (weeks to months): adopt artifact‑level verification and per‑image SBOMs (software bills of materials) for vendor images you run; require vendors to publish VEX attestations for each product family you consume.
A cautionary note on “only Azure Linux” claims
When vendors publish “Azure Linux includes X library and is therefore potentially affected,” treat that sentence as a precise inventory statement for Azure Linux — not a universal statement about every vendor product. Large, multi‑artifact vendors will inevitably stagger inventory work: they often attest one product family at a time and expand coverage. Operationally, a security team should:- Prioritize the attested product (Azure Linux) for remediation if you run it;
- But also proactively verify any other artifacts you run from the same vendor, especially those that could plausibly include the same upstream code or runtime; and
- Assume “not yet attested” = “unknown” until the vendor declares Not Affected or you confirm locally.
Final recommendations for WindowsForum readers / system administrators
- If you run PHP on Windows: patch now. Upgrading PHP to the fixed versions is the simplest, most reliable remediation. Then perform an application code audit for unsafe use of proc_open().
- If you run PHP on Linux (including Azure Linux): apply vendor/distribution updates; while the Windows cmd.exe vector does not apply the same way, it is still best practice to keep upstream packages current.
- For organizations that consume Microsoft images and services:
- Ingest Microsoft’s CSAF/VEX outputs and use them as part of your automated triage.
- Don’t assume exclusivity when Microsoft names one product; perform local verification on any Microsoft artifact your estate relies on.
- For development teams: avoid using proc_open() with untrusted input; prefer safer alternatives or explicit sanitization and avoid relying on the array form as a panacea for shell escapes—understand the runtime semantics for the platforms you target.
CVE‑2024‑1874 is a useful reminder of two perennial truths in software security. First, subtle differences in operating‑system semantics can turn a seemingly safe API pattern into a dangerous vector; second, vendor attestations are powerful but limited tools — they accelerate triage for the named product, but do not replace rigorous artifact‑level verification across an organisation’s entire estate. Follow the checklist above, patch aggressively where PHP runs on Windows, and use Microsoft’s VEX/CSAF outputs as the starting point for an evidence‑based remediation program rather than the final word.
Source: MSRC Security Update Guide - Microsoft Security Response Center