A double-free flaw in the libdwarf DWARF-processing library — tracked as CVE-2024-2002 — can cause applications that consume malformed DWARF debug data to crash unpredictably, enabling sustained or repeated denial-of-service conditions; the defect was reported in early 2024 and has been addressed in updated libdwarf releases, but the scope and patch availability vary across distributions so operators must confirm and remediate affected packages immediately.
DWARF is the de facto standard for debugging information embedded in object files, executables, and symbol files used by compilers, linkers, debuggers and many development tools. libdwarf is a small C library that implements reading and writing of DWARF data and ships inside packages such as dwarfutils and is consumed by development toolchains and some runtime tooling.
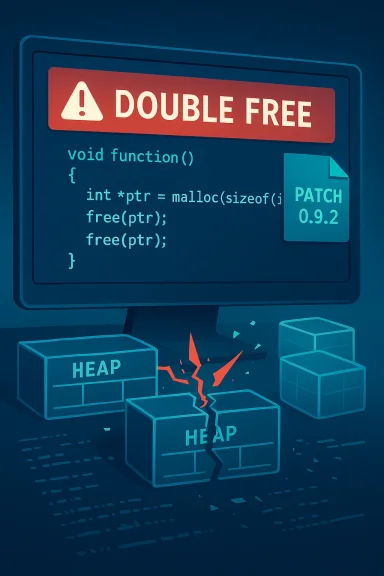
The vulnerability CVE-2024-2002 was discovered while fuzzing DWARF handling code: when libdwarf processes a multiply-corrupted DWARF object it may attempt to free the same heap allocation twice (a double-free), producing undefined behavior that commonly appears as crashes, aborts, or memory corruption. The public vulnerability records summarize the root cause as a double-free in a particular allocation path introduced during error-handling changes.
Why this matters: tools that parse DWARF — debuggers, symbol servers, binutils subcommands, automated analysis pipelines, and CI systems that post-process build artifacts — often handle files from untrusted or semi-trusted sources (third‑party packages, remote build caches, or fuzzed inputs). If any of those tools link to an affected libdwarf binary, a crafted DWARF payload can be used to crash a process and cause availability loss for services that ingest or index debugging information.
Suggested checks (adapt these to your environment):
Treat the vulnerability as availability-first (deny-of-service) with a non-trivial possibility of escalation in specific contexts; prioritize remediation for any host or service that ingests third‑party object files and make the fix part of your standard image-rebuild and CI-hygiene cycles. Upstream records and vendor advisories provide the necessary fixes and regression tests — apply them, validate your images, and follow the monitoring guidance above to close the risk window.
Source: MSRC Security Update Guide - Microsoft Security Response Center
 Background
Background
DWARF is the de facto standard for debugging information embedded in object files, executables, and symbol files used by compilers, linkers, debuggers and many development tools. libdwarf is a small C library that implements reading and writing of DWARF data and ships inside packages such as dwarfutils and is consumed by development toolchains and some runtime tooling.The vulnerability CVE-2024-2002 was discovered while fuzzing DWARF handling code: when libdwarf processes a multiply-corrupted DWARF object it may attempt to free the same heap allocation twice (a double-free), producing undefined behavior that commonly appears as crashes, aborts, or memory corruption. The public vulnerability records summarize the root cause as a double-free in a particular allocation path introduced during error-handling changes.
Why this matters: tools that parse DWARF — debuggers, symbol servers, binutils subcommands, automated analysis pipelines, and CI systems that post-process build artifacts — often handle files from untrusted or semi-trusted sources (third‑party packages, remote build caches, or fuzzed inputs). If any of those tools link to an affected libdwarf binary, a crafted DWARF payload can be used to crash a process and cause availability loss for services that ingest or index debugging information.
Overview of the disclosure and patching status
- The vulnerability was publicly recorded in March 2024 and assigned CVE‑2024‑2002; multiple vulnerability trackers list the issue as a double-free introduced by code added in 2021.
- Upstream and downstream tracking indicate the bug was fixed in the libdwarf upstream release packaged as libdwarf-0.9.2 (tarrelease mentioned in upstream bug logs) and distributors published package updates at different cadences. The upstream bug page and regression test entries show the problem was identified via fuzzing and fixed with a commit tied to the 0.9.2 release.
- Multiple distribution security advisories (Amazon Linux, SUSE, Debian trackers and distribution advisories) and third‑party vulnerability databases note the same root cause and advise updating to patched package versions. However, CNA assessments differ on attack vectors and severity metrics — some CNAs and vendor trackers mark the issue as network‑exploitable while others consider it local — so defenders should treat exploitability conservatively and prioritize remediation for any host that processes untrusted DWARF data.
Technical analysis: what a double-free means here
What is a double-free and why it’s dangerous
A double-free occurs when program logic frees the same heap block twice. This violates allocator invariants and typically corrupts allocator metadata, leading to immediate crashes, later heap corruption, or, in some cases, conditions that attackers can manipulate to achieve arbitrary code execution. In practice, the most frequent, immediate impact is availability loss — crashes and aborts — but the potential exists for more severe outcomes depending on context, allocator, and surrounding code. The public record for CVE‑2024‑2002 explicitly flags unpredictable results and availability impact.How this manifested in libdwarf
The bug was introduced as part of logic intended to prevent memory leaks when creating unattached error records — cases where a Dwarf_Error must be created but no Dwarf_Debug context is available. Under certain corrupt DWARF inputs (reported by fuzzers), libdwarf’s error-path cleanup attempted to free the same internal item twice. Upstream regression tests and the patch log show multiple SIGABRT/SIGSEGV fuzz traces that map to the bug and are resolved by the fix committed to the 0.9.2 release. That history is recorded in the libdwarf issue tracking and regression notes.Attack surface and exploitation scenarios
- Tools that parse DWARF from local build artifacts (linkers, debuggers, symbol servers) are the most common victims because DWARF is typically embedded in files that are loaded from disk.
- Services that ingest object files over the network — e.g., symbol indexing services, remote build caches, or container registries that extract symbols — can create remote attack surfaces if they accept and parse untrusted debugging information. Some advisories treat the vector as network (i.e., data delivered remotely to a parsing service), while others treat it as local; the correct classification depends on how each environment uses libdwarf. This discrepancy is visible across vendor advisories and underscores the need for defenders to evaluate their own deployment models.
Real-world impact: availability and supply-chain considerations
Direct operational impacts
The immediate and best-documented impact is denial of service: applications processing a malicious or malformed DWARF object can crash or abort. For single-purpose command-line tools this is a transient annoyance; for long-running services (symbol servers, debuginfo indexers, automated CI runners) repeated crashes can lead to sustained outages and degraded developer workflows. Operators that rely on automated tooling to index or analyze binaries should treat this as a high‑priority availability risk. SUSE et al. list "High" availability impact in their scoring matrix.Supply-chain and developer tooling risk
Because libdwarf is embedded in developer toolchains, a vulnerable library can propagate in several ways:- Containers and build images that include dwarfutils or libdwarf can distribute an exploitable binary widely across developer and CI infrastructure.
- Symbol sanitizer/stripping pipelines that handle untrusted third‑party artifacts or CI artifacts from forks can be forced to process crafted files that crash service components.
- Hosted services that accept uploaded debug artifacts (e.g., private symbol servers, crash-reporting backends) can be remotely triggered if they parse DWARF without isolation.
What vendors and trackers say (summary of authoritative guidance)
- NVD and multiple vulnerability trackers summarize the flaw as a double-free in libdwarf that occurs while handling multiply‑corrupted DWARF objects. These sources list March 2024 as the disclosure timeframe.
- Upstream libdwarf regression notes and the upstream tarrelease list the fix as part of the 0.9.2 release and show regression test names that match fuzzing traces; these records document that the problem was introduced in versions beginning with libdwarf‑0.1.0 and fixed in 0.9.2.
- Distribution advisories vary: Amazon Linux published an ALAS advisory that includes libdwarf updates; SUSE and Debian trackers also catalog the issue and its status for their packages. The CVSS base score used by Red Hat and some trackers is in the High range, but SUSE’s internal vector treated the attack as requiring local access and rated the base score lower — again, the difference depends on how you consume DWARF data.
Detection and verification: how to find affected systems
Start by inventorying where libdwarf and dwarfutils are installed and where DWARF is parsed in your environment.Suggested checks (adapt these to your environment):
- Package inventory
- RPM-based systems: run package queries for libdwarf, dwarfutils or dwarf packages (for example: query for libdwarf, dwarfutils, or any distro-specific packaging).
- Debian-based systems: check dpkg for dwarfutils and libdwarf packaging entries.
- Container and image scanning
- Scan container images and CI build images for packages that include libdwarf. Treat images as a first-class part of your inventory, since patched host packages do not patch containers already built.
- Service mapping
- Identify running services that parse debug information: symbol servers, crash report processors, debuginfo extractors, QA fuzzers, or any tool that consumes object files (strip, objdump, dwarfdump, debuginfod-related tooling).
- Reproduce safely (for triage)
- If you must reproduce the crash to confirm vulnerability, do so in an isolated sandbox or VM with no network access, using only test artifacts and off‑network tools. The upstream regression notes reference specific fuzz regressioncases; if you have a secure fuzzing sandbox they can be used to validate presence of the fault.
Immediate mitigation and remediation (prioritized actions)
The overall remediation strategy is straightforward: identify, patch, and harden. Follow this prioritized action plan.- Identify affected packages and versions.
- Look for libdwarf and dwarfutils packages in your package manager and image registries. The upstream fix is present in libdwarf-0.9.2 and downstream packagers have released updates — install the distro-specific updates as soon as they are available.
- Patch systems and rebuild images.
- Apply vendor-supplied updates for your distribution (Amazon Linux ALAS advisories, distro security updates). Rebuild and redeploy any container images that include the vulnerable libdwarf binary.
- Isolate or restrict services that parse untrusted DWARF.
- If patching will take time, limit the exposure of services that accept uploaded debug artifacts. Restrict interfaces to trusted networks, require authentication, and throttle uploads to reduce the chance of automated fuzz-driven attacks.
- Apply runtime mitigations.
- Use process sandboxing, seccomp, or containerization to isolate components that parse DWARF. Ensure ASLR, stack canaries and hardened malloc implementations are enabled where feasible to reduce escalation risk.
- Monitor and respond.
- Add detection rules to capture abnormal terminations of symbol services and indexers. Monitor crash patterns (core dumps, service restart loops) and map them back to packages to locate vulnerable nodes.
- Consider temporary workarounds.
- If you cannot patch immediately, run DWARF‑parsing tools under more restrictive user accounts, inside ephemeral containers, or disable automated ingestion of remote symbol artifacts until updates are in place.
Suggested long-term hardening for developer ecosystems
- Treat debugging metadata as part of your attack surface. Enforce validation: when ingesting artifacts from forks, CI pipelines, or third parties, perform strict validation and scanning before parsing.
- Add fuzzing and regression tests for your build pipelines. The issue was found by fuzzing; integrating fuzz checks into CI is one of the fastest ways to surface future parser robustness problems.
- Move critical parsing components to hardened, sandboxed services that have clear restart and circuit-breaker behavior to limit the blast radius of crashes.
- Maintain a distribution and image inventory: a central registry of base images and packages makes it faster to roll out fixes across manydes.
Practical checks and commands (examples you can adapt)
- RPM-based systems (example):
- Query: rpm -qa | grep -i dwarf
- Debian-based systems (example):
- Query: dpkg -l | grep -i dwarf
- Container scanning:
- Inspect Dockerfiles/base images for packages (search for dwarfutils/libdwarf) and rebuild images with patched packages.
Detection guidance: log indicators and behavioral signatures
- Repeated crashes or SIGABRT/SIGSEGV in processes that perform symbol extraction or debugging tasks.
- Spike in crash-report uploads correlated with symbol‑ing jobs.
- Core files from processes such as dwarfdump, objdump, debuginfo extractors, or custom symbol-indexers showing stack frames inside libdwarf allocation or free routines.
- Use your crash collection and observability pipeline to tag and triage these crashes; core evidence is frequently the most reliable indicator that the system tried to process malformed DWARF content.
Risk analysis and critical appraisal
Strengths of the response so far
- The issue was discovered via fuzzing and fixed upstream quickly with regression test artifacts recorded; that rapid upstream response and the presence of regression testcases is a strength — it permits downstream packagers to produce reliable patches and for operators to validate fixes. Documentation indicating the fix in libdwarf-0.9.2 and regression traces demonstrates strong upstream triage and transparent remediation.
- Multiple distribution advisories and cloud provider security advisories have surfaced, which reduces the time window where unpatched installations are the only line of defense. Amazon Linux, SUSE, Debian and others have cataloged updates.
Remaining risks and caveats
- Variant attack vectors and inconsistent scoring: CNAs and distributors disagree on whether the vulnerability is network‑exploitable or local — the answer depends on each organization’s architecture (whether a service parses remote DWARF data). That means some teams may underestimate risk if they assume local only; defenders should adopt a conservative posture.
- Patch lag across ecosystems: Not all distributions or product images receive immediate updates; containers or legacy images often remain unpatched for long periods. Tracing the library through images and build artifacts takes real work and is a likely operational gap.
- No known public PoC ≠ no exploitability: While trackers don’t report a widely circulated exploit PoC at disclosure, the bug is straightforward to trigger in fuzzing and causes reliable crashes — so the absence of public exploitation evidence is not strong assurance.
Recommendations for WindowsForum readers (practical checklist)
- Urgently identify: inventory hosts, containers, and images that include libdwarf/dwarfutils.
- Patch: apply vendor security updates (use your distro’s security advisories and package manager) and rebuild containers that include the affected package. Confirm the package version corresponds to the fixed release noted in distro advisories or upstream release notes.
- Isolate: temporarily restrict services that accept debug artifacts from untrusted sources, or run them within tighter sandboxes until patched.
- Monitor: add alerts for abnormal process terminations in symbol and debug-processing services and collect core dumps for triage.
- Harden CI: add fuzz regression and parsing tests for object file pipelines to catch similar regressions earlier.
- Communicate: notify developer teams and third‑party vendors who supply build images or symbol services so they can update images and packages.
Conclusion
CVE‑2024‑2002 is a realistic, high‑availability risk that affects a component used pervasively in development and analysis toolchains. The problem is a classic double-free — trivial to demonstrate under fuzzing and capable of producing crashes or corrupting memory — and was fixed upstream with regression artifacts that downstream vendors have used to ship updates. The defensive task is plain but operationally broad: inventory, patch, rebuild images, and isolate any services that parse untrusted DWARF artifacts.Treat the vulnerability as availability-first (deny-of-service) with a non-trivial possibility of escalation in specific contexts; prioritize remediation for any host or service that ingests third‑party object files and make the fix part of your standard image-rebuild and CI-hygiene cycles. Upstream records and vendor advisories provide the necessary fixes and regression tests — apply them, validate your images, and follow the monitoring guidance above to close the risk window.
Source: MSRC Security Update Guide - Microsoft Security Response Center