The curl project’s advisory for CVE-2024-2398 describes a straightforward but consequential bug: when an application enables HTTP/2 server push, libcurl can leak previously allocated header memory if a pushed stream exceeds the library’s header limit and is aborted — a leak that can amount to multiple megabytes per response and that fails silently unless the calling application or environment detects growing memory use. Microsoft’s update-guide wording that “Azure Linux includes this open‑source library and is therefore potentially affected” is an accurate, product-scoped attestation: it confirms Azure Linux was inventoried and found to carry an affected libcurl variant, but it is not—and should not be read as—a technical guarantee that no other Microsoft products or images include the same vulnerable code. This distinction matters for defenders, operators and product owners who must triage exposure across a heterogeneous estate rather than relying on a single-vendor attestation as a universal safety net.
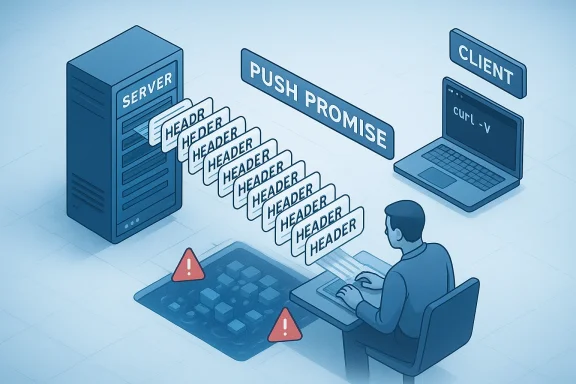
CVE-2024-2398 is a memory‑management bug in curl/libcurl that affects HTTP/2 server-push handling. The curl project reported the issue and released a corrective change in the 8.7.0 release; prior versions in the range introduced by an earlier commit and up to 8.6.0 are identified as affected. The defect occurs when libcurl receives more header entries in a PUSH_PROMISE (or equivalent pushed response) than the library’s configured header-item limit (1000 by default). On aborting a push in that error path, libcurl failed to free all allocated header structures, producing a resource leak that can be repeatedly triggered by a malicious or misbehaving server.
libcurl is a widely embedded networking component: it exists as the curl command-line tool, as the libcurl library consumed by native applications, and it is packaged into many OS distributions and container base images. Because the vulnerability is triggered by HTTP/2 server push — a relatively rarely used feature in most HTTP workloads — the practical exposure profile is lower than arbitrary remote code execution flaws, but it is a real operational risk for long-running processes and servers that interact with untrusted HTTP/2 endpoints or act as clients of servers capable of push. In constrained or multi-tenant environments, leaking multiple megabytes per response can produce process instability, denial of service via memory exhaustion, or silent degradation that complicates incident response.
Microsoft’s public guidance for CVEs often includes concise machine‑readable attestations mapping upstream components to Microsoft product families. For a growing number of upstream issues the company has begun publishing CSAF/VEX attestations for Azure Linux and, over time, other product families. The phrase Microsoft uses — that “Azure Linux includes this open‑source library and is therefore potentially affected” — accurately communicates that Azure Linux images have been inventoried and found to contain the implicated library. It does not mean Microsoft checked every product, every kernel build, or every binary it ships. Microsoft’s planned and ongoing rollout of machine‑readable attestations improves transparency, but the attestation is an inventory result and not a categorical exclusion of all other products.
Longer, operational answer: Microsoft’s phrasing is intentionally scoped. An attestation that “Azure Linux includes this library” is a statement of fact for that product family, not a statement that all Microsoft products were searched and found clean. Microsoft ships many distinct artifacts that can independently include third‑party components: Windows system binaries, WSL kernels, marketplace VM images, Azure Marketplace appliances, container base images, Azure agent binaries, and unmanaged customer images. Each of those artifacts is constructed independently and can contain different versions or builds of libcurl (or different HTTP stacks altogether). Until Microsoft publishes attestations or updates mapping additional product families to the vulnerability, or until you verify a specific artifact’s SBOM / package list, you should assume uncertainty for other Microsoft-supplied images and agents.
Key operational takeaway: treat the Azure Linux attestation as a canonical, high‑confidence negative/positive for that product family — but do not use it as a shortcut to decide that other Microsoft products are unaffected. Inventory and verify the artifacts you actually run.
Strengths:
Source: MSRC Security Update Guide - Microsoft Security Response Center
 Background / Overview
Background / Overview
CVE-2024-2398 is a memory‑management bug in curl/libcurl that affects HTTP/2 server-push handling. The curl project reported the issue and released a corrective change in the 8.7.0 release; prior versions in the range introduced by an earlier commit and up to 8.6.0 are identified as affected. The defect occurs when libcurl receives more header entries in a PUSH_PROMISE (or equivalent pushed response) than the library’s configured header-item limit (1000 by default). On aborting a push in that error path, libcurl failed to free all allocated header structures, producing a resource leak that can be repeatedly triggered by a malicious or misbehaving server.libcurl is a widely embedded networking component: it exists as the curl command-line tool, as the libcurl library consumed by native applications, and it is packaged into many OS distributions and container base images. Because the vulnerability is triggered by HTTP/2 server push — a relatively rarely used feature in most HTTP workloads — the practical exposure profile is lower than arbitrary remote code execution flaws, but it is a real operational risk for long-running processes and servers that interact with untrusted HTTP/2 endpoints or act as clients of servers capable of push. In constrained or multi-tenant environments, leaking multiple megabytes per response can produce process instability, denial of service via memory exhaustion, or silent degradation that complicates incident response.
Microsoft’s public guidance for CVEs often includes concise machine‑readable attestations mapping upstream components to Microsoft product families. For a growing number of upstream issues the company has begun publishing CSAF/VEX attestations for Azure Linux and, over time, other product families. The phrase Microsoft uses — that “Azure Linux includes this open‑source library and is therefore potentially affected” — accurately communicates that Azure Linux images have been inventoried and found to contain the implicated library. It does not mean Microsoft checked every product, every kernel build, or every binary it ships. Microsoft’s planned and ongoing rollout of machine‑readable attestations improves transparency, but the attestation is an inventory result and not a categorical exclusion of all other products.
What CVE-2024-2398 actually does (technical breakdown)
How the leak occurs
- libcurl supports HTTP/2 server push, where a server can send additional responses (pushed streams) alongside the response to a client-initiated request.
- libcurl enforces a cap on the number of header entries it will accept for a push (the implementation tracked a limit of 1000 header entries).
- When the number of received header entries exceeds this limit, libcurl aborts the pushed stream; the abort path contained a cleanup bug and did not free all header structures previously allocated for the push.
- Because the error condition is silent to the caller (the abort occurs internally), applications that rely on libcurl can continue operating while the process memory consumption grows.
Practical consequences
- Each improperly freed push can leak multiple megabytes; multiple pushes or repeated malicious responses can produce an observable memory growth.
- Long-lived agents, daemons and services that use libcurl (for telemetry, software updates, API calls) are most at risk of slow memory exhaustion.
- The issue is not a remote code execution primitive; its likely impact vector is availability degradation (DoS through memory exhaustion) and stealthy resource leakage.
Where it matters
- Any product or image that ships an affected libcurl (versions from the introduced commit up to 8.6.0) and that either:
- Enables HTTP/2 in its libcurl build, and
- Uses server-push features or connects to endpoints that might send pushes
is potentially affected. - If a vendor’s libcurl binary was built without HTTP/2 support (for example, the build lacks nghttp2 or HTTP/2 support was disabled), a vulnerable libcurl version may still be present but practically not exploitable for this specific issue. That nuance is important but must be verified per artifact.
Is Azure Linux the only Microsoft product that includes the vulnerable library?
Short, practical answer: No — not necessarily. Azure Linux is the only Microsoft product Microsoft has publicly attested to include the implicated open‑source component for this CVE (i.e., Microsoft’s inventory work has confirmed Azure Linux images contain a libcurl package in the affected range). That attestation is authoritative for Azure Linux customers and is the correct operational signal: if you run Azure Linux, treat the product as in scope and apply updates.Longer, operational answer: Microsoft’s phrasing is intentionally scoped. An attestation that “Azure Linux includes this library” is a statement of fact for that product family, not a statement that all Microsoft products were searched and found clean. Microsoft ships many distinct artifacts that can independently include third‑party components: Windows system binaries, WSL kernels, marketplace VM images, Azure Marketplace appliances, container base images, Azure agent binaries, and unmanaged customer images. Each of those artifacts is constructed independently and can contain different versions or builds of libcurl (or different HTTP stacks altogether). Until Microsoft publishes attestations or updates mapping additional product families to the vulnerability, or until you verify a specific artifact’s SBOM / package list, you should assume uncertainty for other Microsoft-supplied images and agents.
Key operational takeaway: treat the Azure Linux attestation as a canonical, high‑confidence negative/positive for that product family — but do not use it as a shortcut to decide that other Microsoft products are unaffected. Inventory and verify the artifacts you actually run.
Why the MSRC wording is precise — and why users still need to act beyond it
Microsoft’s transparency model for third‑party CVEs has two parts that are helpful but create an operational gap if misunderstood:- Machine-readable attestations (CSAF/VEX) tell you which Microsoft product families were inspected and what was found for those products. That is excellent — those entries are authoritative and actionable for customers of those products.
- The rollout is phased and product‑scoped; Microsoft will extend attestations as more product inventories are completed and, when additional Microsoft products are found to ship the affected component, the company will update the CVE record.
How to verify whether a given Microsoft artifact is affected
The answer depends on the artifact type. Use the following artifact-level verification checklist:- Identify the artifact:
- Is it an Azure Marketplace VM image, a Windows system binary (curl.exe), a WSL kernel package, an Azure agent or a container base image?
- Check the artifact’s SBOM / package list / manifest:
- For Linux images, inspect the package manager (rpm/dpkg) or the supplied SBOM.
- For containers, examine the image layers or the software manifest used to build the image.
- Query the curl/libcurl version and build features:
- Run curl -V (or the programmatic equivalent) to get the libcurl version and the features list.
- Confirm whether HTTP/2 support is enabled in that build (look for “HTTP2”, “nghttp2”, or relevant features).
- If libcurl is present and the version falls in the affected range, verify whether the build enables server-push (HTTP/2) and whether the application actually uses push.
- If an SBOM is not available, extract the binary and inspect strings or run package-inspection tools to locate libcurl symbols or linked libraries; for static builds, you must inspect binary symbols or build manifests.
- If in doubt, assume the artifact is potentially affected and apply the mitigation steps below.
Recommended mitigations and remediation steps
Follow a three-track approach: Patch, detect, and harden.1) Patch (primary remediation)
- Upgrade libcurl/curl to a non‑vulnerable release: the upstream curl project fixed this issue in the 8.7.0 release. Where possible, update to 8.7.0 or later.
- For packaged distributions, apply the vendor-provided security update (distributors published mitigations and patches soon after disclosure).
- For container images, rebuild images based on updated base images or explicitly update the curl package during build.
- For applications that vendor or statically link libcurl, rebuild them against the fixed library and redeploy.
2) Detect (short-term compensations)
- Inventory: scan your fleet for curl/libcurl versions using endpoint management tools, vulnerability scanners, or custom scripts. For Linux, query package managers; for Windows, check the curl.exe version and features.
- Runtime monitoring: instrument long-lived processes (agents, daemons) to alert on unusual memory growth. A steady unexplained increase in resident set size (RSS) for a process that performs HTTP requests may be a sign of repeated leaks.
- Network-level mitigations: if reasonable, block or rate-limit connections to untrusted servers that could send malicious push frames. For services that contact many external endpoints, prefer whitelisting for operations requiring long-lived connections.
3) Hardening and code-level fixes
- Disable HTTP/2 server push if your application does not rely on it. Depending on your build and usage, this could be done by rebuilding libcurl without HTTP/2 support or by configuring the client to refuse push.
- Add defensive checks in your own application when consuming libcurl:
- Detect and handle aborted push streams and recover resources explicitly if possible.
- Limit the number of concurrent pushed streams or reject unexpected push events.
- Fuzz and test your own network-facing code paths with malformed or excessive header cases to validate memory handling under failure scenarios.
4) Communications with Microsoft and vendors
- If you rely on Microsoft-provided artifacts other than Azure Linux (WSL kernels, Marketplace images, Windows system binaries, agents), request applicable SBOMs or VEX attestations from Microsoft, and subscribe to the MSRC advisory feed for updates.
- If you operate an enterprise Microsoft contract, open a support case requesting explicit artifact inventory for affected components.
Detection playbook (step-by-step)
- Run fleet-wide queries to find all occurences of curl/libcurl:
- Linux: dpkg -l | grep curl or rpm -qa | grep curl
- Containers: scan image manifests for curl packages or run scanning tools across registry images
- Windows: check presence of curl.exe and run curl -V to extract version and features
- For each found instance, record:
- Package version and vendor package release number
- Build features (HTTP/2 yes/no)
- Whether the binary is statically linked or dynamically linked
- Prioritize remediation for:
- Internet-facing clients and long-running processes
- Multi-tenant agents and shared infrastructure components
- Patch tiered by risk and redeploy; for containers and images, push updated images through CI/CD and replace running containers.
- Implement temporary mitigations (disable / block server push if possible) while patches roll out.
Critical analysis: Microsoft’s attestation program — progress, strengths and residual risk
Microsoft’s public attestation that Azure Linux includes an implicated open‑source library is a positive step toward vendor transparency. Publishing CSAF/VEX attestations makes it easier for customers to automate triage and to integrate vendor signals into their vulnerability management pipelines. Azure Linux, being Microsoft’s published Linux distribution (CBL-Mariner lineage), was a logical early candidate for inventory mapping; Microsoft’s product-scoped attestations provide high-fidelity data for those particular artifacts.Strengths:
- Machine-readable attestations (CSAF/VEX) help automation and reduce guesswork for customers running attested products.
- Azure Linux customers receive a high-confidence signal and corresponding patch guidance.
- Microsoft’s commitment to update CVE mappings when additional products are found to ship the component creates an audit trail and process for expanding coverage.
- The attestation model is product-scoped and phased; absence of an attestation for a product does not prove absence of the vulnerable component.
- Microsoft ships many artifacts assembled independently; whether a given artifact is affected depends on build flags, static versus shared linking, and specific package versions.
- Customers who assume a single attestation implies a global vendor-wide update risk blind spots; defenders must still perform artifact-level inventory and scanning.
Developer and vendor guidance
If you maintain or build software that uses libcurl:- If you consume vendor-provided libcurl packages, patch promptly to the fixed version or apply vendor patches.
- If you statically link libcurl into your product, rebuild with an updated libcurl and re-release signed binaries.
- If you expose long-running processes that use libcurl for outbound HTTP connections, add memory‑use monitoring and graceful restarts as part of your resilience posture.
- If HTTP/2 server push is not needed, consider disabling it at build or configuration time.
- Publish SBOMs and VEX attestations for important artifacts and keep them updated. Customers will use these machine-readable signals to automate triage.
- Where practical, ship libcurl builds that document enabled features (HTTP/2, nghttp2 support) so customers can quickly determine exploitability.
What to tell customers and operators now
- If you run Azure Linux: follow Microsoft’s guidance — update curl/libcurl to a fixed package release as soon as vendor updates are available and apply the recommended mitigation steps.
- If you run other Microsoft artifacts: do not assume you are safe. Inventory the exact artifacts you run and verify whether libcurl is present and, if so, whether it is built with HTTP/2 support. Treat artifacts without manifest attestations as unverified until you check them.
- If you manage Windows endpoints: check whether curl.exe is present and verify its version and feature set (curl -V). If the shipped curl has no HTTP/2 support, the specific CVE may not be exploitable in that binary; still, consider vendor updates because upstream fixes can matter for a range of other CVEs and for third-party components that may be bundled separately.
- If you operate containers or use third‑party images: scan images for curl packages and rebuild or replace base images with updated versions.
Unverifiable or time‑sensitive points to watch for
- Whether a specific Microsoft product (beyond Azure Linux) contains an affected libcurl instance is an artifact-level fact that requires either a Microsoft attestation or an inspection of that product’s SBOM or runtime. Do not treat the absence of an attestation as evidence of absence.
- Microsoft’s public VEX/CSAF catalogue is an evolving asset; additional product mappings may appear over time as Microsoft completes more inventories. Customers should monitor MSRC advisories for updates.
- The exploitability of a libcurl version depends not only on version-number but on build-time features (HTTP/2 enabled) and linking (static vs shared). These are per-artifact properties and must be checked per binary.
Conclusion
CVE-2024-2398 is a libcurl memory‑leak bug in HTTP/2 push handling that can quietly consume memory when abused; the upstream project fixed the bug in the 8.7.0 release. Microsoft’s public statement that “Azure Linux includes this open‑source library and is therefore potentially affected” is a precise, product‑scoped claim that should prompt Azure Linux customers to remediate without delay. However, it is not a blanket guarantee that no other Microsoft product could be affected. The right operational response is artifact-level verification and quick patching: inventory your Microsoft-supplied images and binaries, determine whether libcurl is present and whether the build enables HTTP/2, and apply the upstream or vendor-supplied fixes. Microsoft’s attestation program improves transparency and reduces uncertainty for Azure Linux customers, but defenders must still do the work of scanning, validating SBOMs and applying fixes across their full estate rather than relying on a single attestation as the sole risk signal.Source: MSRC Security Update Guide - Microsoft Security Response Center