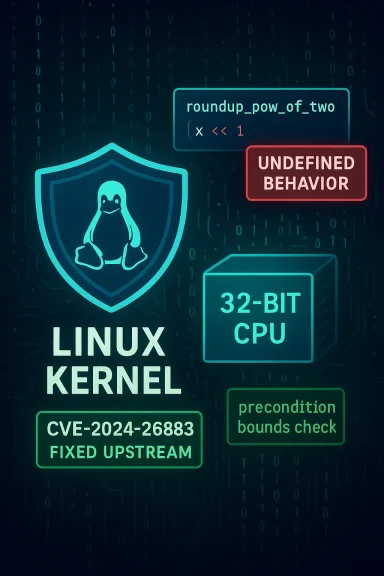
The Linux kernel received a targeted fix in April 2024 for a subtle arithmetic/overflow mistake in the BPF stackmap code that can be triggered on 32‑bit architectures — a defect tracked as CVE‑2024‑26883 that can produce undefined behavior, memory mis‑calculations and availability impacts on systems that allow untrusted BPF map creation.
The affected code lives in the kernel’s extended Berkeley Packet Filter (eBPF/BPF) subsystem, in the stackmap implementation that computes hash-bucket sizing with a helper called
This bug is part of a recurring class of BPF correctness issues discovered by automated kernel fuzzers such as syzbot and by manual code review — vendors and distributions responded with targeted patches and distribution updates in the weeks and months following public disclosure. The surrounding pattern — misplaced overflow checks and unchecked rounding — has appeared in related BPF fixes (for examAP_HASH family) and was fixed with the same general approach: validate input/range before performing operations that can overflow.
Source: MSRC Security Update Guide - Microsoft Security Response Center
 Background / Overview
Background / Overview
The affected code lives in the kernel’s extended Berkeley Packet Filter (eBPF/BPF) subsystem, in the stackmap implementation that computes hash-bucket sizing with a helper called roundup_pow_of_two(). On 32‑bit architectures, the implementation performed a left shift on an unsigned long to compute a power-of-two rounding, and then attempted to detect overflow only after that rounding. Because that left shift can invoke undefined behavior on 32‑bit CPUs (shifting into or past the word size), the later check was unreliable and could miss overflow conditions entirely. The short, practical consequence: a crafted request that exercises the DEVMAP_HASH/stackmap path can cause incorrect internal sizing, leading to kernel instability or denial‑of‑service.This bug is part of a recurring class of BPF correctness issues discovered by automated kernel fuzzers such as syzbot and by manual code review — vendors and distributions responded with targeted patches and distribution updates in the weeks and months following public disclosure. The surrounding pattern — misplaced overflow checks and unchecked rounding — has appeared in related BPF fixes (for examAP_HASH family) and was fixed with the same general approach: validate input/range before performing operations that can overflow.
Technical analysis: what went wrong, in plain terms
The arithmetic trap on 32‑bit
- The stackmap code needed to compute the number of buckets as a power of two, so it called
roundup_pow_of_two(n_entries). That helper performs shifts to compute the next power of two. - On a 64‑bit kernel, those shifts live in a sufficiently large unsigned long and are benign for realistic inputs; on a 32‑bit kernel, the same left shift can move bits beyond the representable width and the result is undefined behavior according to the C standard.
- The original overflow test only inspected the rounded result (for example, checking whether the result was zero), but if UB occurred inside the rounding, the behavior of that check is not portable or guaranteed — it may appear to “work” on some CPUs/compilers and fail catastrophically on others.
Why checking afterward is insufficient
A check after the dangerous computation cannot reliably detect UB that may already have corrupted the value; the correct defensive pattern is to validate the input and ensure it lies within a safe range before doing operations that could overflow. Kernel maintainers implemented the fix by moving the bounds test earlier — ensuring the code refuses sizes that would force an unsafe shift — rather than relying on the rounded value to indicate success. The change is minimal but important: it replaces a late, unreliable guard with a precondition that prevents UB entirely.How the bug is reached
The practical reachability of the defect depends on whether userland processes can create the affected BPF maps (stackmaps or DEVMAP_HASH). In many systems, BPF map creation is a privileged or semirestricted operation; in others, unprivileged user namespaces, container environments and evolving kernel knobs can grant the ability to create BPF maps to non‑root processes. Automated fuzzers like syzbot successfully triggered the condition on real kernels, which is how the problem was detected.Impact: availability, integrity, and exploitation potential
Availability-first vulnerability
Vendors classify CVE‑2024‑26883 primarily as an availability and memory‑safety problem. The two most concrete outcomes are:- Immediate kernel instability / OOPS: Incorrect sizing or UB inside kernel code can produce oopses or panics, causing processes or entire hosts to crash or hang.
- Denial‑of‑service (DoS): Repeated exploitation opportunities or malformed map requests can sustain or persistently degrade service availability, especially on systems with constrained recovery (embedded devices, appliances).
Exploitation: local vector, escalation possibility
- Attack vector: The flaw is exploitable by local users who can create or manipulate BPF maps (i.e., it is not a straightforward remote, unauthenticated network exposure).
- Privilege requirements: The CVSS vectors and vendor writeups show a requirement for at least some privileges on the host (local privileges or the ability to run code as a local user permitted to create BPF objects).
- Post‑exploitation risk: While public reporting emphasizes availability, undefined behavior in kernel memory math is a classic stepping stone. In theory, carefully constructed inputs could morph a denial‑of‑service into memory corruption or privilege escalation, but such a conversion depends on a long and fragile chain of conditions. No broad, reliable privilege‑escalation exploit was publicly documented in major advisories at the time the patch was released; however, the presence of UB in kernel paths always merits caution because it increases the attack surface for advanced local attackers and exploit developers. This absence of public exploit reports should not be read as a guarantee of non‑exploitability.
What was changed in the patch (the right way to fix it)
The upstream kernel patches for CVE‑2024‑26883 follow the defensive programming principle: validate inputs before doing arithmetic that can overflow. Concretely:- The code now performs a range check against a safe maximum before calling
roundup_pow_of_two()so that any left-shift inside the helper is guaranteed not to exceed the representable width on 32‑bit platforms. - The guard was moved from a posterior check of the rounded result to a precondition on the number of entries.
- Equivalent fixes were applied consistently to other BPF map types that copied the original logic, closing the same class of bug in related code paths.
Who is affected — inventory and prioritization
Immediately prioritize systems that meet one or more of the following:
- Hosts running 32‑bit kernels (x86_32, ARM32, older MIPS, etc.). These are the primary platforms where the UB arises.
- Embedded appliances, IoT devices, routers, or industrial devices that still use 32‑bit kernels and expose any user‑space interface allowing BPF map creation.
- Multi‑tenant or container hosts that allow untrusted containers to create BPF maps or that have unprivileged BPF enabled for userspace.
- Distribution kernels with the vulnerable commits included in their trees — several major distributions shipped patches or advisories shortly after disclosure; consult distribution advisories for exact package names and versions.
Lower priority (but not to ignore)
- Pure 64‑bit server farms with strict kernel hardening and no route for unprivileged BPF map creation. While most 64‑bit kernels do not exhibit the same UB, code duplication and porting mistakes can leave related code paths vulnerable; keep these systems patched as well.
Vendor responses and patch availability
Multiple vendors and distributions published advisories and backports after the issue was disclosed:- Amazon Linux (ALAS) recorded the CVE and lists patched kernel packages for Amazon Linux 2023 images, with vendor-specific severity and CVSS mappings. Distribution‑provided kernels were updated to include the fix.
- Red Hat / other Linux vendors integrated the upstream fix in stable and long‑term support trees; commercial packages and advisories document whether a no‑fix or backport is being provided for particular product branches. Industry databases mirror those updates.
- Security research services and vulnerability trackers (Rapid7, Wiz, and others) published technical writeups and mitigation guidance that mirror upstream rationale and recommend updating to fixed kernels.
Practical mitigation checklist (for administrators)
Apply the fixes in the following order; the list is prioritized for speed and operational safety.- Patch: Install vendor-supplied kernel updates that include the CVE‑2024‑26883 fix. This is the definitive mitigation.
- Inventory 32‑bit hosts: Identify systems that still run 32‑bit kernels and assess whether those systems allow untrusted local users or containers to create BPF maps. Target those hosts for immediate patching or isolation.
- Reduce BPF attack surface: Where possible, restrict BPF map creation to privileged users. Options vary by distribution and kernel version — typical approaches include:
- Enforcing capability controls (CAP_BPF/CAP_SYS_ADMIN) and user namespace limitations.
- Using kernel configuration knobs to restrict unprivileged BPF use if available on your kernel branch.
- Applying container runtime policies that prevent untrusted containers from requesting BPF capabilities.
(Specific sysctl names and knobs vary by kernel version and distribution; consult your vendor documentation.) - Harden and monitor: Add kernel oops/crash monitoring, collect and retain dmesg logs, and configure alerting for new or repeated kernel oopses. Frequent or reproducible oopses are a strong sign of attempted exploitation.
- Isolate legacy devices: If embedded or legacy devices cannot be patched immediately, isolate them from sensitive networks and minimize the set of users and processes that can interact with them.
- Test before mass rollout: On large fleets, stage the kernel package in test environments and validate boot and key workloads before widespread deployment.
Detection and incident response
Indicators to watch for
- Kernel oopses, panics, or unexplained reboots in logs that correlate with user‑space actions creating or manipulating BPF maps.
- System logs showing repeated failures from BPF map creation syscalls or audit records for CAP_BPF/CAP_SYS_ADMIN granted to untrusted processes.
- Behavior anomalies on embedded devices (frozen networking, hung control plane) after inputs from local interfaces.
Response steps if you suspect exploitation
- Quarantine the host from sensitive networks (to prevent lateral movement).
- Collect volatile evidence: dmesg, kernel logs, journalctl output, and a copy of the running kernel symbol table if possible.
- Do not reboot the system unless necessary; reboots may lose crucial memory state useful fo4. Apply the patch in a controlled manner; if patching is infeasible immediately, mitigate by disabling or restricting BPF map creation for unprivileged users.
- If the host is part of a multi‑tenant service, initiate tenant isolation and forensic review to detect potential privilege escalation.
Developer and architecture lessons
CVE‑2024‑26883 is, at heart, a defensive programming lesson for systems‑level developers:- Preconditions over postconditions. When arithmetic or shifts could overflow, validate inputs first. A late check can be defeated by UB that occurs during computation.
- Be explicit about widths. Code that is correct on a 64‑bit build can be incorrect on 32‑bit builds. If code must be portable across word sizes, explicitly use sized types and bounds checks.
- Automated fuzzers matter. Many of these BPF issues were discovered by syzbot or other fuzzing infrastructure that repeatedly stress kernel APIs with exotic inputs; maintainers should treat fuzzing results as high‑priority signals.
- Consistency across copies. The same code pattern was duplicated across hashtab, stackmap, and DEVMAP_HASH variants; any fix must be replicated to clones and backported to stable branches — incomplete fixes leave residual risk.
Strengths of the upstream approach — and where risk remains
What was done well
- The fix itself is small and narrowly scoped, following the kernel’s principle of minimal, correct changes to eliminate undefined behavior. This reduces the chance of regressions.
- Vendors and distributions moved quickly to publish advisories and patch packages once the issue was publicized. Amazon Linux and other maintainers documented the CVE and available fixes.
- The detection chain — fuzzers, triage, and upstream commits — demonstrates the kernel community’s ability to surface and close architecture‑specific UB.
Remaining concerns and caveats
- Residual clones and backports: If branches or vendor trees miss a backport, devices remain vulnerable for months or years — especially custom or embedded kernels where upstream patches do not automatically propagate. Administrators should not assume all vendor kernels are patched unless explicitly stated.
- Local vector; privileged user risk: Systems that permit untrusted users to create BPF objects remain an attack surface. Policies and kernel knobs are not uniform across distributions, so centralized hardening guidance must be adapted per environment.
- Possible exploit evolution: Although public advisories emphasized availability and there were no widespread public RCE exploits reported at disclosure, UB in kernel paths is attractive to exploit developers; a DoS‑focused bug can be an early step toward more severe exploits if combined with other memory‑corruption primitives. This risk profile argues for conservative, fast patching.
Recommended timeline for remediation (practical plan)
- Within 24–72 hours: Inventory all 32‑bit kernel hosts and categorize them by exposure (internet‑facing, multi‑tenant, internal). Apply emergency isolation to devices that permit untrusted BPF usage.
- Within 1–2 weeks: Apply vendor kernel patches to high‑risk systems (multi‑tenant hosts, embedded appliances in production). Validate in test before mass rollout.
- Within 1 month: Complete patching of all remaining systems and confirm that vendor‑supplied kernels include the fix across stable releases. Implement monitoring for kernel oops trends that may indicate exploitation attempts.
- Ongoing: Build BPF usage policies into configuration management and container hardening checklists so the attack surface is reduced proactively for future BPF‑related findings.
Closing analysis — why this CVE matters to WindowsForum readers
Even though CVE‑2024‑26883 targets a low‑level, Linux kernel‑specific code path and is most relevant to administrators of 32‑bit systems or multi‑tenant Linux hosts, the implications are broad for modern infrastructure operators:- Embedded and industrial devices continue to run 32‑bit kernels in the field; those fleets can be exposed to sustained availability issues if vendor updates do not reach them.
- Multi‑tenant cloud and container environments must account for local attack vectors that the kernel exposes; seemingly obscure kernel arithmetic errors can escalate into service outages.
- The fix illustrates a reliable security engineering pattern: validate before you compute. Small changes in defensive coding practices yield outsized reductions in risk.
Source: MSRC Security Update Guide - Microsoft Security Response Center