Microsoft’s short public attestation that “Azure Linux includes this open‑source library and is therefore potentially affected” is accurate for the inventory Microsoft has completed, but it is not a technical proof that no other Microsoft product could contain the same vulnerable PyTorch code. rview
CVE‑2024‑31584 is an out‑of‑bounds read in PyTorch that affects the mobile FlatBuffers loader (torch/csrc/jit/mobile/flatbuffer_loader.cpp) in releases prior to v2.2.0. The vulnerability can cause crashes or information disclosure when a specially crafted FlatBuffer is processed; upstream PyTorch fixes were merged and the vulnerability is tracked in mainstream CVE databases.
Microsoft’s MSRC entry for this CVE (the terse product mapping line the user quoted) functions as a product‑scoped inventory attestation: it confirms Microsoft’s inspection of a particular product — Azure Linux — and reports that the upstream component is present in that product and is therefore potentially affected. That statement is an important and actionable signal for Azure Linux customers, but it is deliberately scoped and arantee.
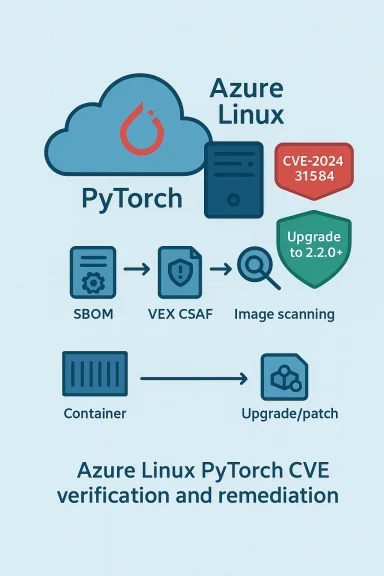
In parallel, Microsoft has expanded transparency by publishing machine‑readable VEX/CSAF attestations for Azure Linux and related artifacts, a program announced publicly in October 2025 — a step intended to help organizations automate whether a given CVE applies to Microsoft products. Microsoft has said it will update CVE/VEX records if impact to additional products is identified.
CVE‑2024‑31584 is a reminder of two enduring truths in modern security: open‑source vulnerabilities propagate into many downstream artifacts, and vendor attestations are powerful but scoped tools — they improve transparency when present, but they do not absolve defenders from validating their own environment. Act now: inventory, scan, and patch.
Source: MSRC Security Update Guide - Microsoft Security Response Center
CVE‑2024‑31584 is an out‑of‑bounds read in PyTorch that affects the mobile FlatBuffers loader (torch/csrc/jit/mobile/flatbuffer_loader.cpp) in releases prior to v2.2.0. The vulnerability can cause crashes or information disclosure when a specially crafted FlatBuffer is processed; upstream PyTorch fixes were merged and the vulnerability is tracked in mainstream CVE databases.
Microsoft’s MSRC entry for this CVE (the terse product mapping line the user quoted) functions as a product‑scoped inventory attestation: it confirms Microsoft’s inspection of a particular product — Azure Linux — and reports that the upstream component is present in that product and is therefore potentially affected. That statement is an important and actionable signal for Azure Linux customers, but it is deliberately scoped and arantee.
In parallel, Microsoft has expanded transparency by publishing machine‑readable VEX/CSAF attestations for Azure Linux and related artifacts, a program announced publicly in October 2025 — a step intended to help organizations automate whether a given CVE applies to Microsoft products. Microsoft has said it will update CVE/VEX records if impact to additional products is identified.
 What the technical record says about CVE‑2024‑31584
What the technical record says about CVE‑2024‑31584
- The defect is an out‑of‑bounds read rooted in PyTorch’s FlatBuffer parsing for mobile models; the vulnerable code lives in torch/csrc/jit/mobile/flatbuffer_loader.cpp.
- The fix was included in the PyTorch 2.2.0 release series; thus, users are advised to use PyTorch v2.2.0 or later (or vendor-supplied distributions that include the upstream patch).
- Public vulnerability trackers (NVD, Debian security tracker and distribution advisories) list the CVE, affected versions, and vendor responses; distribution-specific packaging timelines vary, so some Linux distributions may already ship patched packages while others may lag.
Microsoft’sns in practice
Microsoft’s sentence — “Azure Linux includes this open‑source library and is therefore potentially affected” — should be parsed as two, separate claims:- A product‑inure Linux does include the affected upstream component (the PyTorch package or code paths that map to the CVE).
- A potential‑impact assertion: because the affected component is present, Azure Linux images are potentially affected until the vendor‑provided patch or mitigations are applied.
Short answer to the user’s direct question
No — Azure Linux is not necessarily the only Microsoft product that could include the vulnerable PyTorch library. It is the only Microsoft product Microsoft has publicly attested (so far) as containing the upstream component referenced by CVE‑2024‑31584. That attestation is authoritative and actionable for Azure Linux customers, but it should not be read as proof that other Microsoft artifacts (images, containers, kernel builds, SDKs, appliance images, or packaged toolchains) cannot also carry the vulnerable code. Microsoft has committed to updating the CVE/VEX record if other affected products are identified.Why this distinction matters — real world implications
Many organizations assume that a vendor’s statement placing a CVE against one product is an implicit “only this product.” That assumption is dangerous for three reasons:- Microsoft distributes many artifacts derived from or built against the sam (for example: images used by cloud services, prebuilt container bases, development SDKs, and WSL kernels). Any of those artifacts can carry packaged libraries or vendored code that match the vulnerable upstream code path.
- A product‑level attestation is intentionally suct inventory exercise; absent additional attestations or machine‑readable VEX information for other Microsoft products, defenders must treat other Microsoft images as unverified rather than safe.
- Attackers seeking to exploit open‑source library bugs often target mispackaged,d copies of libraries in less obvious locations (containers, internal images, preinstalled packages on marketplace images), so relying on a single attestation creates blind spots.
Practical verification steps — what defenders should do now
If you operate Azure, Microsoft‑supplied images, or systems that use Microsoft artifacts, follow these prioritized steps to determine exposure and remediation needs.- Inventory all images, VMs, appliances, and containers your organization runs that are Microsoft-sourced: Azure Marketplace images, managed container registries, WSL images, Azure VM images, and packaged SDKs. Treat inventory as the single source of truth for artifact verification.
- For each artifact, locate the PyTorch package/version (pip/conda package metadata, distro package manager metadata, or filesystem hashes). If PyTorch is < 2.2.0, mark the artifact in‑scope.
- Use available SBOMs or VEX/CSAF attestations where Microsoft has published them (Azure Linux VEX entries are available as part of Microsoft’s transparency effort) to automate product=CVE mapping. Microsoft’s VEX rollout for Azure Linux began in October 2025 and is intended to accelerate this verification.
- If the artifact lacks an SBOM or VEX attestation, perform an image scan with your software composition analysis (SCA) tool or a trustworthy packaging tool that can enumerate Python packages, library files, and their versions.
- Prioritize remediation for any artifact that contains PyTorch < 2.2.0. The remediation options are:
- Upgrade PyTorch to v2.2.0 or later (preferred).
- Apply vendor/distro patches if the distribution provides patched packages.
- If neither is possible, isolate the artifact from handling untrusted model input and employ runtime containment controls (sandboxing, reduced privileges).
- Rebuild and redeploy images after applying the upgrade or patch; do not rely on in‑place pip upgrades alone for production images without testing.
- Apply compensating controls where immediate upgrades are impossible: restrict who can upload or run untrusted FlatBuffers or mobile models, enforce model validation routines, and add runtime memory‑safety monitoring where practical.
- Track MSRC VEX/CSAF feeds and the Microsoft update guide for any changes; Microsoft has said it will update records if it discovers additional products that include the component.
- If your organization uses Microsoft-managed services that accept user‑supplied models (for example platform services that execute customer models), coordinate with Microsoft support or your cloud team to confirm whether those service images have been inspected for the vulnerable component.
- Log and monitor for anomalous crashes, input parsing errors, or memory disclosure symptoms in services that process user models, since out‑of‑bounds reads can cause crashes and abnormal error patterns.
How to validate Microsoft’s attestation and how to question it constructively
Microsoft’s attestation is a valuable signal — treat it as authoritative for Azure Linux images Microsoft has checked. But do the following to reduce your risk:- Ask Microsoft for SBOMs or VEX entries for specific artifacts you rely on: the VEX/CSAF program is explicitly designed to support automation and customer queries.
- Where you run Microsoft marketplace images or prebuilt containers, require either a published SBOM, image manifeackages and versions, or you must run an internal validation scan before deploying them to production.
- Use reproducible image‑build pipelines and enforce third‑party package upgrades at build time rather than letting unmonitored images persist in registries.
- If you discover a Microsoft artifact in your environment that contains the vulnerable PyTorch code and is not mentioned in Microsoft’s VEX/CSAF postings, report it to MSRC so they can reconcile product scope and (if necessary) update the CVE attestation. Multiple independent reviews of similar Microsoft attestations have recommended the same coordinated disclosure/feedback approach.
Strengths in — why this matters
Microsoft’s public attestation for Azure Linux and its VEX/CSAF rollout represent meaningful improvements in vendor transparency and are actionable for defenders. Those moves henefits:- Machine‑readable attestations let automated tooling determine which vendor products are in scope for a CVE, reducing analyst toil and false positives.
- Publicly stating the product that contains the upstream time customers spend chasing whether their images are affected. That clarity is especially valuable in large, heterogeneous cloud environments.
- Microsoft’s pledge to update CVE/VEX records when additionafied closes the loop: the attestations are not static statements but a process Microsoft expects to iterate on.
Remaining risks and caveats
- Attestation scope is limited. The published mapping is scoped to a product inventory exercise; it does not certify that other Microsoft artifacts are free of the vulnerable code. Customers must assume un‑attested artifacts are unverified until proven otherwise.
- Embedded or vendored copies: projects sometimes vendor code inside larger binaries or images. These copies can evade naive package checks and require file‑level scans and hash comparisons to detect.
- Distribution lag and packaging differences: even when upstream PyTorch is fixed in 2.2.0, package maintainers may apply the fix at different times; distribution packages can carry backports or divergent version numbers that complicate automated checks. Use distribution advisories in tandem with upstream release notes.
- Operational exposure through model execution: PyTorch’s mobile FlatBuffer loader is used in mobile and edge scenarios and in sandboxed model execution paths; if you run services that execute customer models, an attacker who can supply a crafted FlatBuffer could potentially trigger the vulnerability even if PyTorch is isolated in a container. Treat model execution endpoints as high‑risk.
Recommended remediation checklist (concise)
- Upgrade PyTorch to v2.2.0+ or install vendor/distro patches where they exist.
- Rebuild/prevent reuse of old Azure Marketplace images that contain PyTorch < 2.2.0.
- Use SBOMs / VEX feeds to automate whether Microsoft artifacts in your estate are in‑scope; subscribe to Microsoft’s published VEX for Azure Linux where available.
- Scan images and registries for vendored PyTorch files and FlatBuffer loaders if you run custom or third‑party images.
- Harden model ingestion endpoints and require strict validation of FlatBuffers or other model serialization formats.
- If you find an unexpected Microsoft artifact that contains the vulnerable code, report it to MSRC so the vendor can revise the VEX/CVE mapping if appropriate.
Industry context — how other vendors and distros treat the same question
The behavior Microsoft has shown — mapping an upstream CVE ave inspected and committing to publish machine‑readable attestations — is consistent with modern supply‑chain best practices. Other major distributors map CVEs to specific packages and images while making no claim of exclusivity. Security advisories from distributions (Debian, Red Hat, Ubuntu) typically list whether their packages are affected and which fixed versions they wiinely note when a vendor has not declared other product impact. Cross‑referencing NVD with distro advisories is the pragmatic way to confirm whether a package in a given image is indeed patched.What we could not verify (and how to treat those unknowns)
- There is no public evidence that Microsoft has found PyTorch <2.2.0 in other named Microsoft products beyond Azure Linux at the time of Microsoft’s attestation. That absence of public evidence is not proof of absence — it is simply an absence of attestation. Treat un‑attested Microsoft artifacts as unverified rather than safe until SBOMs or VEX data confirm otherwise.
Final analysis and guidance
- Microsoft’s public statement about Azure Linux is authoritative for that product: if you run Azure Linux images, you should treat them as potentially affected and follow the remediation steps above.
- Microsoft’s attestation is not a guarantee that Azure Linux is the only Microsoft product that could include PyTorch <2.2.0; other Microsoft‑controlled artifacts may carry the same upstream code until they are explicitly inventoried and attested. Defenders must therefore perform artifact‑level verification.
- The immediate, highest‑value action for nearly every organization is simple: inventory, scan, and upgrade PyTorch to v2.2.0+ in any artifact that includes it. Distribution security advisories and upstream release notes confirm v2.2.0 contains the necessary fix.
CVE‑2024‑31584 is a reminder of two enduring truths in modern security: open‑source vulnerabilities propagate into many downstream artifacts, and vendor attestations are powerful but scoped tools — they improve transparency when present, but they do not absolve defenders from validating their own environment. Act now: inventory, scan, and patch.
Source: MSRC Security Update Guide - Microsoft Security Response Center