The Linux kernel vulnerability tracked as CVE-2024-39495 is a use-after-free in the greybus subsystem (gb_interface_release) triggered by a race between workqueue execution and object teardown, and Microsoft’s Security Response Center (MSRC) has publicly attested that Azure Linux includes the implicated upstream component and is therefore potentially affected — but that attestation is product‑scoped, not a categorical guarantee that no other Microsoft product or image could contain the same vulnerable kernel code.
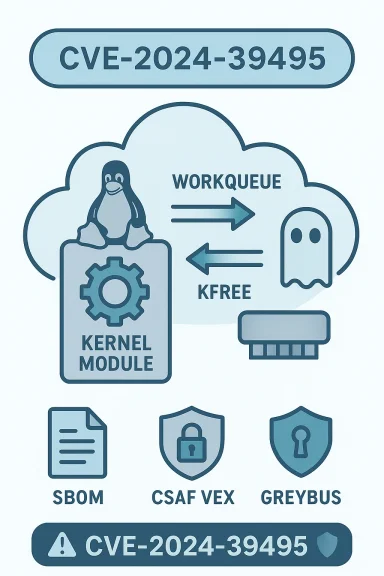
CVE-2024-39495 was reported against the Linux kernel’s greybus staging code. The bug arises when a work item that references an interface object can be scheduled concurrently with the code path that frees that same object; if the work executes after kfree() it may dereference freed memory, producing a classic kernel-level use-after-free (UAF). The upstream fix cancels or synchronizes pending work before freeing the object so the work cannot run against reclaimed memory.
The vulnerability has been cataloged by major vulnerability trackers and distribution advisories (for example, NVD, distribution security pages and vendor advisories) and was fixed in the stable kernel trees; multiple vendors have pushed distribution-specific kernel updates or backports to address it. Distribution trackers list specific fixed kernel versions and in many cases provide backport patches for older stable branches used in production.
Why this matters operationally
Two important clarifications:
Other Microsoft artifacts you should treat as “unverified” until proven otherwise
Vendors and operators can accelerate remediation and reduce uncertainty by:
Takeaway checklist (brief, actionable)
Source: MSRC Security Update Guide - Microsoft Security Response Center
 Background / Overview
Background / Overview
CVE-2024-39495 was reported against the Linux kernel’s greybus staging code. The bug arises when a work item that references an interface object can be scheduled concurrently with the code path that frees that same object; if the work executes after kfree() it may dereference freed memory, producing a classic kernel-level use-after-free (UAF). The upstream fix cancels or synchronizes pending work before freeing the object so the work cannot run against reclaimed memory.The vulnerability has been cataloged by major vulnerability trackers and distribution advisories (for example, NVD, distribution security pages and vendor advisories) and was fixed in the stable kernel trees; multiple vendors have pushed distribution-specific kernel updates or backports to address it. Distribution trackers list specific fixed kernel versions and in many cases provide backport patches for older stable branches used in production.
Why this matters operationally
- A kernel UAF can cause immediate instability (kernel oops, panic, denial-of-service) and, in some exploitation chains, may be a stepping stone toward privilege escalation or arbitrary code execution. The realistic attack vector is local (or guest/namespace) — an attacker needs a way to exercise the kernel paths that schedule and run the workqueue and trigger the timing window. Nevertheless, on multi-tenant or cloud hosts a guest or untrusted workload could, in principle, attempt to hit the condition.
What Microsoft actually said — and why the phrasing matters
Microsoft’s public CVE entries for a series of Linux-kernel vulnerabilities have adopted a short, consistent product‑mapping sentence: essentially, “Azure Linux includes this open‑source library and is therefore potentially affected,” coupled with a pledge to expand machine-readable CSAF/VEX attestations and update the mapping if additional Micrscovered to ship the same upstream component. That exact wording appears on Microsoft advisories and is intended as a targeted inventory attestation for Azure Linux customers. (msrc.microsoft.com)Two important clarifications:
- Attestation, not exclusivity: When MSRC says Azure Linux “includes” the component, that is an authoritative statement about Azure Linux artifacts Microsoft o contain the upstream code. It does not mean Microsoft is asserting that no other Microsoft product contains the same code. The absence of a similar MSRC line for Product X is an absence of attestation, not proof of absence.
- Phased VEX rollout: Microsoft began publishing machine-readable CSAF/VEX attestations as part of a phased program; product coverage grows as Microsoft inventories more artifacts. MSRC explicitly says it will update CVE mappings if impact to additional products is iors should treat Azure Linux as a confirmed carrier while recognizing that other Microsoft artifacts may remain “unverified” until Microsoft publishes more VEX attestations or until you verify them yourself.
Technical verification and independent corroboration
To avoid ambiguity, every technical claim below is grounded in independent upstream and vendor-tracker evidence:- Canonical vulnerability description and technical summary: NVD’s CVE entry and distribution advisories describe the gb_interface_release race-to-free and the fix strategy (cancel pending work before freeing), and they list the kernel snapshots and stable-tree commits where the fix landed. This provides the baseline technical reference for the defect.
- Distribution and vendor corroboration: Several Linux distribution trackers (for example, Oracle/Elsa, AWS ALAS, and multiple distro advisories) catalog the CVE, note fixed package versions or backports, and publish vendor patches. These independent vendor records confirm the upstream technical details and provide guidance for operators running vendor kernels.
- Patch links and stable-tree commits: The upstream kernel stable trees contain the actual commits that close the race; distribution suppliers have used those commits as the canonical fix for backports. Even when access to the kernel.org web UI is constrained, distribution advisories and vulnerability databases point to the same commit IDs and the same fix rationale.
Why Azure Linux was named (and what to do about other Microsoft artifacts)
Why did MSRC single out Azure Linux? In short: Microsoft maintains the Azure Linux distribution lineage and those aried and found to include the implicated upstream code; therefore Azure Linux images are a confirmed remediation target. That does not mean Microsoft has finished inventorying every Microsoft-supplied artifact. Large vendors ship thousands of distinct images and binaries; inventory mapping and VEX attestations are phased product-by-product.Other Microsoft artifacts you should treat as “unverified” until proven otherwise
- WSL2 kernel images and their published sources (particularly if you or your users run custom WSL distributions).
- Azure Marketplace VM base images and Marketplace appliances (those images can include distro kernels or Microsoft-built kernels).
- AKS node images and managed node pools that may use Microsoft-provided base images or kernels.
- linux-azure kernel bundles and other Microsoft-published kernel artifacts used in Azure services.
- Microsoft-published container base images or SDK images (if they include or were built with a kernel artifact).
- Any statically linked or vendored binMicrosoft build pipelines that may embed kernel-adjacent code or utilities (note: static linking is less common for kernel code but can matter for user-space libraries).
Until Microsoft publishes a VEX attestation or your own artifact scanning confirms otherwise, assume uncertainty and verify these artifacts directly.
Practical steps: how to verify whether a given Microsoft-supplied artifact includes the vulnerable greybus code
If you operate Azure Linux images: follow Microsoft’s patch guidance and treat the product as in-scope immediately. For other Microsoft artifacts and any artifact you run in production, perform artifact-level verification with these steps.- Confirm kernel version and vendor package metadata
- On a running Linux instance: uname -a and check the exact kernel package (for example, dpkg -l | grep linux-image or rpm -q kernel). Map the kernel version to the upstream commits listed for the CVE (vendor advisories list the fixed versions/backports).
- Check whether the greybus module or config exists in the kernel
- Check compiled-in kernel config: zgrep GREYBUS /proc/config.gz or grep CONFIG_GREYBUS /boot/config-$(uname -r).
- Check for a module: lsmod | grep greybus or modinfo greybus (if the module exists under /lib/modules/$(uname -r)). If the module is neither built-in nor present, runtime exposure is low unless the kernel is rebuilt with the feature enabled. ([feedly.com](CVE-2024-3949
- Inspect the image filesystem (for containers, disk images, Marketplace images)
- For container images: run a temporary container and inspect /lib/modules, /boot, and config files; or use image-scanning tools that list installed kernel modules and packages.
- For VM images (Marketplace or Azure VM snaphe image and inspect the kernel package and /lib/modules for greybus artifacts.
- Search SBOMs and build artifacts
- If you can obtain an SBOM for the image/artifact, search for kernel package names and kernel config entries. Request SBOMs from vendors and marketplace publishers where available; Microsoft’s VEX/CSAF program aims to help with that inventory but the program is phased.
- Use vulnerability scanners and policy gates
- Run your standard vulnerability scanners (e.g., Nessus/Tenable, Qualys) and image scanners to detect kernels with versions older than the vendor-patched releases. Vendors such as Tenable have published detections for Azure Linux kernels referencing CVE-2024-39495. Use these as corroborating signals, but don’t rely solely on them — they detect versions and packages rather than actual exploitability at runtime.
- If a kernel is confirmed vulnerable and you cannot patch immediately
- Consider temporary mitigations: unload and blacklist the greybus module (rmmod greybus; add a blacklist file under /etc/modprobe.d/), but only if you are sure your hardware and workflows do not require greybus — blacklisting may break runtime features on devices that actually need the driver.
- Reduce attack surface: limit local access, enforce stronger tenancy isolation, and monitor for kernel oops and suspicious logs tied to workquer activity. Note: these are stopgaps, not substitutes for applying the kernel fix.
Patching and remediation guidance
- Prioritize Azure Linux images: because MSRC has attested Azure Linux as including the implicated component, make remediation of Azure Linux instances your highest-priority Microsoft-supplied target. Apply Microsoft-supplied kernel updates for Azure Linux as soon as they are available.
- Apply vendor kernel updates or backports: for other distributions and vendor-supplied kernels, apply the distribution-specific packages that contain the backported fix.teams and vendor advisories list the fixed package versions and backport commits to apply.
- Rebuild and redeploy container images and statically lin the host kernel will not fix an embedded or statically compiled artifact that itself includes vulnerable code paths; if a buildel-adjacent code into an image, rebuild with fixed components and push updated images through CI/CD gates.
- For WSL2: update WSL kernel packages distributed by MicrosoftMicrosoft occasionally publishes WSL kernel updates separately; verify that your WSL kernel binary includes the fix or apply the updated kernel package from the provider.
Operational checklist (a prioritized short list)
- Patch Azure Linux VMs and images immediately as Microsoft recommends.
- Scan your inventory for Microsoft-supplied artifacts (WSL kernels, marketplace images, AKS nodes, container base images). Treat them as “unverified” until validated.
- For each candidate artifact, confirm kernel version and whether GREYBUS is present (config/modules). Ifl predates the fix, schedule patch or rebuild.
- If immediate patching is impossible, apply temporary mitigations (module blacklisting only if safe, access controls, monitoring). Track and log mitigation windows and plan for follow-up.
- Request SBOM/VEX attestations from vendors and subscribe to Microsoft’s CSAF/VEX feeds to receive updated product mappings as Microsoft expands inventory coverage.
Risk assessment: what to expect if you ignore the attestation nuance
Some teams will see the MSRC att as sufficient: patch Azure Linux and assume all Microsoft artifacts are safe. That is risky. The reality of large-supplier software supply chains means the same upstream kernel code can appear in multiple artifacts depending on build configuration, kernel version, and whether vendor backports were applied. If you depend on Microsoft-published images beyond Azure Linux (for example, WSL kernels, Marketplace images or certain AKS node images), you must verify them individually; otherwise you risk leaving unpatched carriers in production.Why this pattern is common and how vendors are improving transparency
Large vendors have thousans and millions of images; mapping every CVE to every artifact is a nontrivial, phased process. Microsoft’s approach — start with Azure Linux (its own distribution family), publish attestations and CSAF/VEX data, and expand mapping as inventory work completes — is a pragmatic transparency improvement. It gives Azure Linux customers a clear priority signal while Microsoft continues to inventory other artifacts. But a phased rollout necessarily leaves a window of “unmapped” artifacts that must be verified by operators.Vendors and operators can accelerate remediation and reduce uncertainty by:
- Publishing SBOMs and machine-readable VEX attestations for more product families.
- Enforcing image-scanning and SBOM checks in CI/CD.
- Maintaining automated inventory of kernel versions across cloud images and container base images.
Conclusion — the short, operational answer
Azure Linux is the only Microsoft product that Microsoft has publicly attested to include the vulnerable greybus code for CVE-2024-39495 at the time of Microsoft’s advisory; that attestation is authoritative and means Azure Linux images must be treated as in‑scope and remediated promptly. However, that attestation is product‑scoped — it is not a guarantee that no other Microsoft product, image, kernel artifact, or containthe same vulnerable upstream code. Operators should prioritize Azure Linux patching, and simultaneously perform artifact-level discovecks, module inspections, SBOM and image scans) across other Microsoft-supplied artifacts they run until those artifacts are either attested as “Not Affected” or patched.Takeaway checklist (brief, actionable)
- Treat Azure Linux images as confirmed carriers and apply Microsoft’s kernel updates immediately.
- Scan and inventory all Microsoft-supplied artifacts you run (WSL kernels, Marketplace images, AKS images).
- Verify kernel version and GREYBUS presence with uname, config checks, and module inspections; apply vendor backports or patched kernels where needed.
- If immediate patching is impossible, consider temporary mitigations (module blacklist only if safe), tighten local access, and monitor for kernel oops/events.
- Subscribe to vendor VEX/CSAF feeds and request SBOMs for third‑party or marketplace artifacts to reduce inventory uncertainty over time.
Source: MSRC Security Update Guide - Microsoft Security Response Center