Apache’s CVE-2024-39884 — a regression in the 2.4.60 line that can cause local source files to be served raw when legacy content-type handlers (for example, AddType-based PHP mappings) are used — is fixed upstream, and Microsoft’s Security Response Center (MSRC) has publicly confirmed that Azure Linux images include the affected component and are therefore potentially in‑scope. That confirmation is authoritative for Azure Linux, but it is not a technical guarantee that Azure Linux is the only Microsoft product that could contain the vulnerable Apache HTTP Server builds. Operators must treat MSRC’s wording as a product‑level attestation, and they must still perform artifact-level inventory across the broader estate to be safe.
Why this is important to parse correctly:
Act now: inventory, patch/rebuild, and mitigate — and do not assume safety simply because a single vendor attests only one product.
Source: MSRC Security Update Guide - Microsoft Security Response Center
 Background / Overview
Background / Overview
What CVE‑2024‑39884 is, in plain language
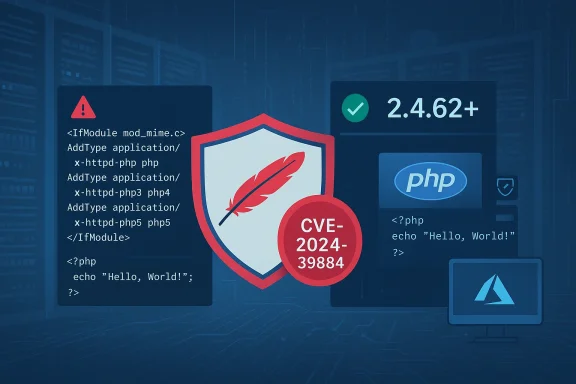
CVE‑2024‑39884 is a regression introduced in Apache HTTP Server 2.4.60 that affects how legacy content‑type based handler mappings (for example, directives using AddType or similar legacy MIME-to-handler mappings) are applied when a resource is requested indirectly (for example via Alias, certain RewriteRule patterns, or other request-routing features). Under those specific conditions, Apache could fail to apply the configured handler and instead send the raw file contents to the client — for example, serving a PHP source file as text instead of passing it to the PHP interpreter. That leads to source code disclosure and can leak credentials, secrets, and business logic. The Apache project documented the issue and shipped a fix in 2.4.61, with follow‑on fixes addressing partial fixes in subsequent releases.A quick technical précis
- A regression in the core handler-dispatch path caused some legacy handler mappings (AddType, etc.) to be ignored for indirect requests.
- Attackers who can cause indirect requests to sensitive resources may retrieve raw source files (for example, .php files).
- The vulnerability is configuration-dependent, but the conditions that produce it are common enough in real-world web applications and hosting environments to make the bug high-impact when present.
Where the fixes landed
Apache documented the initial fix for CVE‑2024‑39884 in the 2.4.61 release and then addressed a partial‑fix regression with an additional patch shipped in 2.4.62; users are recommended to run 2.4.62 or later to ensure the regression and related follow-ups are fully addressed. Distribution vendors quickly produced downstream updates.What Microsoft actually said — and why the wording matters
Microsoft’s Security Response Center has adopted a concise FAQ format for many open‑source Linux CVEs: the MSRC entry for this class of Linux/Apache issues (and similar advisories) states that Azure Linux includes the open‑source library and therefore is potentially affected, and that Microsoft has begun publishing machine‑readable CSAF/VEX arollout that started with Azure Linux). Microsoft also says it will update CVE entries if additional Microsoft products are found to include the implicated component. That phrasing is intentionally product‑scoped and procedural.Why this is important to parse correctly:
- The MSRC sentence is an authoritative attestation for the named product (Azure Linux). If you run Azure Linux images published by Microsoft, treat them as in‑scope and consume Microsoft’s updates.
- The wording is not a categorical negative statement that no other Microsoft product could ever contain the same upstream component. Microsoft explicitly reserves the right to update the mapping as it completes inventories for other product artifacts.
Short answer to the user’s question
No — Azure Linux is not necessarily the only Microsoft product that could include the vulnerable Apache component. Azure Linux is the only Microsoft product Microsoft has publicly attested, to date, as containing the affected library (and that attestation is authoritative for Azure Linux images). However, absence of an MSRC attestation for other Microsoft artifacts is not proof those artifacts are free of the vulnerable package. Customers must therefore verify other Microsoft‑supplied images and runtime artifacts themselves (or await Microsoft’s VEX/CSAF attestations for those products).Why a single‑product attestation doesn’t prove exclusivity
Large vendors operate enormous, heterogeneous software estates and publish many artifacts — some of which are Microsoft‑maintained images (Azure Linux, platform runtime images), and many of which are third‑party or customer-supplied images distributed through Microsoft channels (Marketplace, container registries, GitHub actions runners, etc.). A given upstream package like Apache HTTP Server can therefore appear in many places:- Azure Marketplace VM images and signed appliances (first‑ and third‑party).
- Microsoft‑maintained container base images, App Service runtime images, and platform-managed base layers.
- Hosted CI/CD runner VM images (GitHub Actions self-hosted images and Microsoft-hosted runners).
- Marketplace container images and community images used as base layers for customer workloads.
- WSL distributions, internal tooling images, and other Microsoft‑published binaries or build artifacts.
Practical implications for defenders — a prioritized checklist
If CVE‑2024‑39884 (and its follow-on partial‑fix CVE‑2024‑40725) are relevant to your estate, follow a prioritized, evidence‑driven response plan:- Inventory first (high priority)
- Identify every Apache/httpd instance: VMs, containers, appliances, and Marketplace images. Use package manager queries on hosts and container image inspection for images. Example commands:
- Debian/Ubuntu: dpkg -l | grep apache2 ; apachectl -v
- RPM-based: rpm -q httpd ; apachectl -M
- Container images: run an inspection container and query inside the layer, or scan with a container scanner.
- Include CI/CD runner images and build images — these often contain server packages used during builds and tests.
- Prioritize exposures
- Publicly reachable sites and reverse proxies are highest risk.
- Any site that uses legacy AddType/AddHandler mappings for scripts (for example, AddType application/x-httpd-php .php) should be prioritized.
- Environments that use Alias, RewriteRule, or other indirect resource mapping that could trigger the regression should be treated as critical triage points.
- Patch or rebuild — the definitive fix
- Upgrade Apache to a fixed upstream release: ensure you are on Apache HTTP Server 2.4.62 or later (2.4.61 fixed the original regression but additional follow‑ups were required; 2.4.62 contains the complete fix set). If you use distribution packages, apply vendor-supplied security updates that map to those upstream fixes.
- Rebuildredeploy
- For container workloads, rebuild base images with patched packages and redeploy through CI/CD. Do not rely on runtime package upgrades inside long-lived container layers without rebuilding.
- Short‑term mitigations (if you cannot patch immediately)
- Prefer modern handler configuration: replace legacy AddType/AddHandler mappings with explicit SetHandler or FilesMatch/ProxyPassMatch driven handler configuration where possible. Avoid relying on legacy MIME-type handler mapping for script execution.
- Harden file system permissions: ensure source files (for example, *.php)e outside of the web server/user account when possible.
- Restrict access: limit public exposure of vhosts that may proxy or Alias into sensitive directories; use WAF rules or network ACLs to reduce attack surface.
- Detect and hunt
- Search web server logs for suspicious accesses to common script names that returned 200 with conr for atypical responses to Alias/Rewrite targets.
- Run vulnerability scans (Nessus, Qualys, Tenable, Trivy) against images and VMs to identify Apache versions less than the fixed baseline.
- Ask for attestations and SBOMs
- For Microsoft Marketplace images, partner appliances, and third‑party images: request SBOMs or VEX/CSAF attestations or scan the image in staging before deploying. Microsoflishing CSAF/VEX attestations, starting with Azure Linux, and will expand those attestations over time — treat published VEX mappings as authoritative for the product named.
Recommended configuration changes to reduce the window of exposure
- Replace AddType/AddHandler legacy mappings with explicit SetHandler or FilesMatch directives that unambiguously set the script handler only for intended locations. Many security advisories recommend this as both a mitigation and a long-term best practice.
- Validate and audit Alias and Rewrite rules: ensure that indirect mappings cannot point at directories that contain source files you expect to remain out of reach. Where feasible, avoid exposing application code via Alias/Rewrite unless the file is processed by the intended interpreter.
- Apply principle of least privileges to web content directories: ensure that only the web server process can read source files, and that directory listings or file reads are not permitted for unauthenticated users. This does not replace the fix but decreases blast radius.
Evidence and independent cross‑checks (why you can trust the remediation guidance)
- The Apache HTTP Server Project lists CVE‑2024‑39884 as fixed in 2.4.61 and documents a related follow-on CVE/partial‑fix (CVE‑2024‑40725) that was addressed in 2.4.62. Apache’s official vulnerability page is the authoritative source for the fix and affected versions.
- Multiple independent vulnerability trackers and vendor advisories documented the same facts and recommended the same remediations. Examples include Amazon Linux advisories and vendor security pages that mapped fixes to the upstream Apache releases — a practical confirmation that downstream distributors rolled out patches.
- Commercial vulnerability research and tracking sites described the attack vector (legacy AddType handler omission during indirect requests) and published mitigation advice (move away from AddType, upgrade to fixed releases). These independent analyses align with the Apache advisories and with mainstream distro advisories.
How to inspect Microsoft‑supplied artifacts for the vulnerable Apache package
Because MSRC has only attested Azure Linux so far, include the following artifact classes in your scan plan for Microsoft‑supplied artifacts:- Azure Marketplace VM images and appliances (both Microsoft‑published and third‑party Marketplace images).
- App Service built‑in runtime images and platform-provided container layers.
- Azure Container Registry images and any Microsoft‑branded container base images you consume.
- Hosted runner images / CI images (GitHub Actions / Azure DevOps hosted agents).
- WSL distributions and other Microsoft‑distributed images where customers may assume Apache is absent.
- Run package queries inside the VM or image layer (rpm -q httpd e2).
- Check web server binary versions (apachectl -v).
- Check enabled modules and config for handler mappings (apachectl -M ; grep -R \"AddType|AddHandler|SetHandler\" /etc/apache2 /etc/httpd).
- For containers, scan base images with container scanners (Trivy, Clair, Anchore) in your CI pipeline and gate image promotion on passing the scan.
Residual risks, gaps,t rely on a single vendor attestation
- Attestations are valuable automation inputs: Microsoft’s product‑level VEX/CSAF attestations remove ambiguity for the covered product. However, the attestation program is phased, and coverage is incomplete at any given moment.entry as unverified, not as proof of absence.
- Supply‑chain replication: the same vulnerable upstream code can appear in many artifacts via shared build tooling, reused base images, and third‑party Marketplace images. Until each artifact is inventoried and attested, defenders must perform their own scanning.
- Downstream release lag: even when upstream fixes are available, downstream distributors, appliance vendors, and Marketplace image authors take time to build, test, and publish patched packages. That lag creates a real window for exploitation unless images are rebuilt a.apache.org]
A short operational playbook you can implement this week
- Run a targeted Apache package sweep across all Azure subscriptions and on‑prem estates (VM gallery images, container registries, hosted runners). Flag any Apache builds in the 2.4.60–2.4.61 range.
- For flagged systems, schedndows; if that isn’t possible within 24–48 hours, apply mitigations (remove AddType mappings, switch to SetHandler/FilesMatch patterns, restrict public access). (cve.news)
- Rebuild any container images and redeploy to replace old layers with patched base images. Gate promotions on passing vulnerability scans.
- For Marketplace images or third‑party appliances, demand SBOMs or consumer attestation from the publisher before deploytage and scan the image in an isolated environment.
- Subscribe to MSRC’s CSAF/VEX feeds and your distro vendor advisories; use the feeds to automate triage for future incidents. Microsoft has committed to expanding attestations beyond Azure Linux and to updating CVE product mappings as additional artifacts are identified.
Conclusion
CVE‑2024‑39884 is a real and serious regression: a web server misconfiguration combined with a handler‑dispatch regression can expose source code to attackers. Apache fixed the regression, and multiple independent vendors and trackers corroborate the fix and the affected version ranges. Microsoft’s public advisory is useful and authoritative for Azure Linux — Microsoft has confirmed Azure Linux images include the implicated component and therefore are potentially affected — but that single attestation does not mean Azure Linux is the only Microsoft product that could possibly contain the vulnerable Apache build. The correct operational posture is to prioritize Azure Linux images for remediation if you run them, but also to perform thorough artifact‑level inventory and scanning for other Microsoft‑supplied images, containers, CI runner images, and Marketplace artifacts until Microsoft’s VEX/CSAF attestation program has been extended to cover those products or until you can confirm via SBOM and scanning that those artifacts are clean.Act now: inventory, patch/rebuild, and mitigate — and do not assume safety simply because a single vendor attests only one product.
Source: MSRC Security Update Guide - Microsoft Security Response Center