Microsoft’s short, product‑scoped wording on CVE‑2024‑41007 — that “Azure Linux includes this open‑source library and is therefore potentially affected” — is accurate for the Azure Linux product family, but it is not a technical guarantee that no other Microsoft product could also include the same vulnerable Linux kernel code. ://nvd.nist.gov/vuln/detail/CVE-2024-41007)
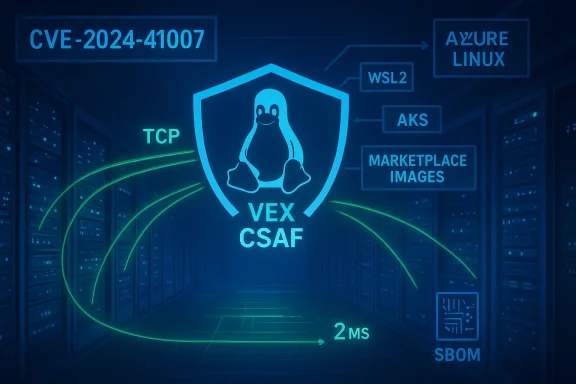
CVE‑2024‑41007 is a Linux kernel networking robustness bug tracked as “tcp: avoid too many retransmit packets.” The flaw affects the TCP retransmission timer logic when a socket is using TCP_USER_TIMEOUT and the remote peer has retracted its receive window to zero. In that condition, the kernel’s tcp_retransmit_timer() could end up retransmitting packets every two jiffies (about 2 ms on HZ=1000 systems) for an extended period — roughly up to four minutes after TCP_USER_TIMEOUT has expired. The upstream fix makes sure tcp_rtx_probe0_timed_out() respects the socket’s icsk->icsk_user_timeout value so retransmits back off or the socket eventually times out instead of hammering the wire.
This is primarily an availability and performance defect — not a straightforward confidentiality or remote code‑execution flaw. Its practical effect is excessive retransmission traffic from an affected host, which can cause local and network congestion, degraded throughput, and, in some environments, knock‑on availability problems. Several distro and vendor trackers (Debian, Ubuntu, Red Hat, Rocky/Oracle/Red Hat errata) and aggregated CVE feeds catalog the issue and provide fixed kernel package guidance.
Critically, Microsoft’s phrasing is deliberately scoped and not exclusive. The company’s public VEX/CSAF rollout began with Azure Linux (a phased program to publish machine‑readable attestations) and Microsoft has said it will update CVE entries if additional Microsoft products are later found to ship the implicated upstream component. Absence of another Microsoft product’s name in the MSRC entry is therefore an absence of attestabsence of the vulnerable code. In practical terms, treat “not attested” Microsoft artifacts as unverified* rather than safe.
Source: MSRC Security Update Guide - Microsoft Security Response Center
 Background / Overview
Background / Overview
CVE‑2024‑41007 is a Linux kernel networking robustness bug tracked as “tcp: avoid too many retransmit packets.” The flaw affects the TCP retransmission timer logic when a socket is using TCP_USER_TIMEOUT and the remote peer has retracted its receive window to zero. In that condition, the kernel’s tcp_retransmit_timer() could end up retransmitting packets every two jiffies (about 2 ms on HZ=1000 systems) for an extended period — roughly up to four minutes after TCP_USER_TIMEOUT has expired. The upstream fix makes sure tcp_rtx_probe0_timed_out() respects the socket’s icsk->icsk_user_timeout value so retransmits back off or the socket eventually times out instead of hammering the wire.This is primarily an availability and performance defect — not a straightforward confidentiality or remote code‑execution flaw. Its practical effect is excessive retransmission traffic from an affected host, which can cause local and network congestion, degraded throughput, and, in some environments, knock‑on availability problems. Several distro and vendor trackers (Debian, Ubuntu, Red Hat, Rocky/Oracle/Red Hat errata) and aggregated CVE feeds catalog the issue and provide fixed kernel package guidance.
What Microsoft actually published — and what it means
When MSRC (Microsoft Security Response Center) writes: “Azure Linux includes this open‑source library and is therefore potentially affected by this vulnerability,” that is a product‑level attestation: Microsoft has inspected the Azure Linux build outputs (the distribution/kernel packages it publishex banner) and found the upstream kernel code mapped to the CVE present in those artifacts. That makes Azure Linux a confirmed remediation priority.Critically, Microsoft’s phrasing is deliberately scoped and not exclusive. The company’s public VEX/CSAF rollout began with Azure Linux (a phased program to publish machine‑readable attestations) and Microsoft has said it will update CVE entries if additional Microsoft products are later found to ship the implicated upstream component. Absence of another Microsoft product’s name in the MSRC entry is therefore an absence of attestabsence of the vulnerable code. In practical terms, treat “not attested” Microsoft artifacts as unverified* rather than safe.
Short answer to the user’s question
No — Azure Linux is not necessarily the only Microsoft product that could include the vulnerable open‑source kernel code for CVE‑2024‑41007. It is the only Microsoft product Microsoft has publicly attested (so far) to include the implicated upstream code. Other Microsoft‑distributed kernel artifacts — for example, the WSL2 kernel image Microsoft ships, Azure Marketplace VM images, AKS node images, custom VM images, or any Microsoft‑published kernel modules or images — could carry the same vulnerable code depending on their build‑time kernel version and configuration. Until Microsoft publishes additional VEX/CSAF attestations naming those artifacts as “Known Affected” or “Not Affected,” or until you verify those artifacts directly, they remain operational unknowns.Technical verification and cross‑references
To ensure accuracy I verified the technical details of the vulnerability against multiple, independent sources:- The National Vulnerability Database (NVD) summarises the defect and the upstream rationale (two‑jiffy retransmits and the need to honor icsk->icsk_user_timeout).
- Distribution trackers (Ubuntu and Debian security trackers) and upstream distro advisories reflect the same technical narrative and list fixed kernel package mappings. These vendors are canonical sources for which kernel packages/releases include the backported fix.
Why Azure Linux attestation is useful — and why it is limited
Microsoft’s attestation about Azure Linux provides two very valuable things:- A clear, authoritative opzure Linux customers: Microsoft has inspected their Azure Linux artifacts and found them to include the vulnerable upstream component, so you must prioritize patching those images.
- A machine‑readable path forward (VEX/CSAF) that enables automated triage once Microsoft extends its attestations to additional product families.
- The exact upstream commit range (which patch level the build is based on).
- Per‑build kernel configuration flags (CONFIG_* items) that enable or disable subsystems.
- Local vendor patches or backports applied at build time.
Practical implications for Microsoft customers and administrators
If you run Microsoft‑provided artifacts in your environment, treat the following as your prioritized playbook:- Patch Azure Linux images immediately. Microsoft ha as a confirmed carrier. Apply Microsoft’s published kernel updates, reboot into patched kernels, and verify the running kernel version.
- Inventory all Microsoft‑supplied kernel artifacts you run:
- WSL2 kernel images (the kernel Microsoft ships with WSL2 on Windows).
- Azure Marketplace VM images and Marketplace appliances.
- AKS node images (if using Microsoft‑curated node images).
- Any custom or partner VM images provided via Microsoft distributions.
- Containers are less likely to include a kernel, but images that ship kernel modules, initramfs, or specialized tooling can rtifacts.
Use SBOMs, image scanning, and artifact metadata to find Microsoft‑distributed kernels in your estate. - Verify kernel builds and config:
- Check running kernel version and compare to vendor advisories that map CVE‑2024‑41007 to fixed kernel releases.
- Inspect kernel config (zcat /proc/config.gz or /boot/config-$(uname -r)) to confirm relevant features; though this CVE affects core TCP retransmit logic (not an optional driver), knowing kernel version and stability tree is decisive.
- Where patching is delayed:
- Apply containment controls: restrict local untrusted users who might manipulate socket options, restrict permissions that allow setting TCP_USER_TIMEOUT (if possible).
- Monitor for symptomatic behavior: repeated retransmit bursts from hosts, elevated network retransmit counters, or unusual traffic spikes corresponding to two‑millisecond retransmit intervals.
- Subscribe to Microsoft’s VEX/CSAF feeds and distro adviso phased VEX/CSAF rollout began with Azure Linux; watch for updates naming additional Microsoft products and for “Fixed” state changes in attestations.
Detection, monitoring and hunting guidance
Because CVE‑2024‑41007 is an availability/performance bug, detection focuses on observing aberrant network behavior and kernel timer/ TCP retransmit signs:- Monitor kernel logs (dmesg) and network interface statistics for sustained retransmits and link saturation events tied to particular hosts.
- Use network telemetry (sFlow, NetFlow, or packet capture) to look for repeated retransmissions at very short intervals from a single TCP flow or socket — a pattern of tightly spaced retransmits every few milliseconds is a strong signal.
- Monitor per‑socket retransmit counters where available; telemetry tools that surface socket‑level metrics (e.g., ss -i or netstat with retransmits) can reveal sockets that do not back off.
- On hosts you suspect are unpatched, capture a small packet trace and confirm whether retransmits are occurring at ~2 ms spacing in the presence of TCP_USER_TIMEOUT and a zero window condition.
Risk analysis — who should care most
- High priority: Cloud and multi‑tenant hosts that expose virtual NICs and accepExcessive retransmits from a VM can affect tenant bandwidth quotas, cause noisy‑neighbor impacts, or trigger provider‑side alarms. If you run Azure Linux images on shared infrastructure, patching is urgent.
- Medium priority: Edge servers, appliances, or on‑prem servers that rely on stable TCP behavior, especially if you run long‑lived, high‑throughput TCP connections with aggressive offload settings.
- Lower priority: Systems that do not use TCP_USER_TIMEOUT or that operate behind middleboxes that do not present the offending zero‑window+GSO conditions; nevertheless, inventory is the deciding factor.
How to verify whether a given Microsoft artifact is affected
Because Microsoft’s attestation is product‑scoped, you should not assume other Microsoft artifacts are safe. Use this verification checklist:- Step 1: Identify the kernel version shipped in the artifact (WSL2 kernel or kernel package in the image). Check the exact kernel version string.
- Step 2: Map that kernel version to upstream commits or distribution changelogs to see whether the fix commit for CVE‑2024‑41007 is included in that build. Distribution advisories (Ubuntu, Debian, Red Hat, etc.) list fixed package versions that you can map to your kernel.
- Step 3: If the artifact is a Microsoft binary or image and Microsoft has published a VEX/CSAF attestation for it, use the attestation state (“Known Affected”, “Not Affected”, “Fixed”) as authoritative for that artifact. If no VEX attestation exists, treat it as “unverified.”
- Step 4: If you cannot patch the artifact immediately, plan for containment: isolate it from sensitive networks, restrict local privileges, and monitor.
- WSL2 kernel images Microsoft provides to Windows clients.
- Azure Marketplace VM images and any Microsoft‑published Marketplace appliances.
- AKS node images and any Microsoft‑managed node pools.
- Any Microsoft‑delivered kernel modules or inagent packages.
Recommended remediation and operational checklist (concise)
- Immediately update Azure Linux hosts to Microsoft’s patched images or kernel packages. Reboot where required.
- Inventory Microsoft‑supplied kernels and images across your environment (WSL2, Marketplace images, AKS node images, VM images). Flag anything built from older upstream kernels predating the fix.
- For each flagged artifact:
- Map kernel version to fixed upstream commit or distribution CVE advisory.
- Patch and rebuild images where possible. If you maintain Marketplace images, rebuild and republish with patched kernels.
- If a full patch is delayed:
- Implement containment: isolate the host, restrict NET_ADMIN-like capabilities,ility to set socket options.
- Increase monitoring for retransmit patterns and set alerts for anomalous network retransmit rates.
- Subscribe to Microsoft’s VEX/CSAF and vendor advisories to receive updates if Microsoft identifies additional affected products.
Strengths and potential risks in Microsoft’s approach
Strengths:- Microsoft’s decision to publish a clear attestation thdes the implicated upstream code gives Azure customers a direct, actionable signal and accelerates remediation in a prioritized product family. That transparency is operationally useful for customers running Azure Linux.
- The move to publish machine‑readable CSAF/VEX attestations (phased rollout starting with Azure Linux) aligns with modern supply‑chain security best practices and enables automation.
- Phased attestations create an attestation gap across Microsoft’s broad artifact surface. While Azureany Microsoft‑distributed artifacts remain unverified until Microsoft completes inventory work. That can produce confusion where defenders assume absence of a name equals safety — which is incorrect.
- The long tail problem: customers who run older images, or who rely on vendor images without timely rebuilding, can remain exposed despite the attestation for Azure Linux. Artifact‑level inspection and SBOMs remain essential.
Final assessment and guidance
- The MSRC statement that “Azure Linux includes this open‑source library and is therefore potentially affected” itative, and useful product‑level attestation for Azure Linux customers. Treat it as an immediate remediation directive for any Azure Linux hosts you run.
- However, do not assume Azure Linux is the only Microsoft product that could contain the vulnerable code. Other Microsoft‑distributed kernels and images may carry the same upstream code depending on build choices; the absence of an attestation for an artifact should be read as “unverified,” not “safe.” Perform artifact‑level inventory and verification for WSL2 kernels, Marketplace/AKS images, and any Microsoft‑provided kernel artifacts you run.
- The technical fix is upstream and distributed by vendors — update kernels using your distribution or Microsoft guidance. Confirm the running kernel matches a fixed release; where immediate patching is impossible, apply containment and monitoring for retransmit behavior.
Conclusion
CVE‑2024‑41007 is a kernel‑level TCP retransmit robustness flaw that can produce repeated, high‑frequency retransmissions when TCP_USER_TIMEOUT is in play and the peer’s window is zero. Multiple independent trackers (NVD, Ubuntu, Debian, vendor errata) confirm the technical details and point defenders to vendor fixed kernels. Microsoft’s MSRC attestation that Azure Linux includes the implicated code is authoritative for Azure Linux and should be treated as a high‑priority remediation signal, but it is not an exclusionary statement that other Microsoft artifacts cannot be affected. For a defensible posture: patch Azure Linux now, inventory and verify all Microsoft‑distributed kernel artifacts you run, subscribe to Microsoft’s VEX/CSAF feeds for updates, and apply containment and monitoring where immediate patching is delayed.Source: MSRC Security Update Guide - Microsoft Security Response Center