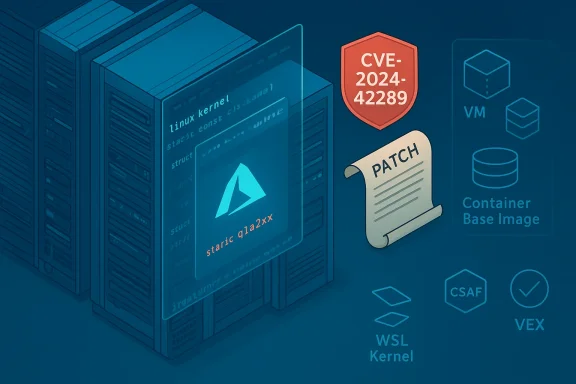
Microsoft’s brief MSRC note that “Azure Linux includes this open‑source library and is therefore potentially affected” is accurate — but it is a product‑scoped inventory attestation, not a technical guarantee that no other Microsoft product can include the same vulnerable Linux kernel driver. Treat Azure Linux as a confirmed, high‑priority carrier for CVE‑2024‑42289 (the qla2xxx SCSI driver bug), but do not assume exclusivity: other Microsoft‑distributed kernels, images, or artifacts that include the same upstream kernel commit or build configuration could also be carriers until they are verified or explicitly attested. s://nvd.nist.gov/vuln/detail/cve-2024-42289)
CVE‑2024‑42289 is a Linux kernel defect in the SCSI qla2xxx driver (used for QLogic Fibre Channel adapters) that can trigger kernel NULL‑pointer dereferences and crashes during vport deletion. The National Vulnerability Database records the technical symptoms and stack traces for the issue; distribution advisories and stable kernel commits contain the upstream fixes. Operators running kernels that include the vulnerable qla2xxx code path must treat the problem as a kernel‑level availability risk and apply vendor patches promptly.
Microsoft’s Security Response Center (MSRC) page for this CVE contains a short FAQ sentence that many administrators have noticed: “Azure Linux includes this open‑source library and is therefore potentially affected.” That sentence is Microsoft’s product‑level mapping for this vulnerability: it confirms MSRC inspected Azure Linux build outputs and found the implicated upstream kernel code, making Azure Linux images an authoritative remediation target. Microsoft also states it began publishing machine‑readable CSAF/VEX attestations in October 2025 and will update CVE mappings if it identifies additional Microsoft products that ship the component. Read in context, the MSRC line isency signal — but it is deliberately scoped to the product family Microsoft checked.
Operationally and defensively: No — Azure Linux is not necessarily the only Microsoft product that could include the qla2xxx driver and therefore potentially be affected. Any Microsoft product or image that ships a Linux kernel build matching the vulnerable commit range and kernel configuration (i.e., builds that include qla2xxx as built-in or as a module) could be a carrier. Examples of such artifacts include WSL2 kernel images, Azure‑tuned kernels for VM SKUs, Marketplace images, AKS node images, and Microsoft‑published container base images — all of which must be verified individually.
To be absolutely clear: the presence of the qla2xxx source in an upstream tree and its inclusion in a binary artifact is a build‑time property. Microsoft’s statement says they verified Azure Linux; it does not certify that every Microsoft image and kernel has been exhaustively scanned.
Cross‑checking the technical facts with independent trackers (NVD’s CVE entry and distribution advisories such as Ubuntu’s USN) confirms the kernel nature of CVE‑2024‑42289, its availability impact, and the standard remediation path — update the kernel and reboot. Use those vendor advisories to identify the exact patched package versions you must install.
Microsoft’s public transparency — naming Azure Linux and committing to machine‑readable VEX/CSAF attestations — is welcome and helps customers automate remediation for the artifacts Microsoft has enumerated. But operational security depends on treatpositive signals about inspected artifacts*, not as implicit safety guarantees for everything else Microsoft ships. CVE‑2024‑42289 is a kernel driver bug; the blast radius is determined by which artifacts include that kernel code and which images and devices you run. Verify, patch, and monitor — and treat the MSRC attestation as a starting point, not the finish line.
Source: MSRC Security Update Guide - Microsoft Security Response Center
 Background / Overview
Background / Overview
CVE‑2024‑42289 is a Linux kernel defect in the SCSI qla2xxx driver (used for QLogic Fibre Channel adapters) that can trigger kernel NULL‑pointer dereferences and crashes during vport deletion. The National Vulnerability Database records the technical symptoms and stack traces for the issue; distribution advisories and stable kernel commits contain the upstream fixes. Operators running kernels that include the vulnerable qla2xxx code path must treat the problem as a kernel‑level availability risk and apply vendor patches promptly.Microsoft’s Security Response Center (MSRC) page for this CVE contains a short FAQ sentence that many administrators have noticed: “Azure Linux includes this open‑source library and is therefore potentially affected.” That sentence is Microsoft’s product‑level mapping for this vulnerability: it confirms MSRC inspected Azure Linux build outputs and found the implicated upstream kernel code, making Azure Linux images an authoritative remediation target. Microsoft also states it began publishing machine‑readable CSAF/VEX attestations in October 2025 and will update CVE mappings if it identifies additional Microsoft products that ship the component. Read in context, the MSRC line isency signal — but it is deliberately scoped to the product family Microsoft checked.
What CVE‑2024‑42289 actually is (technical summary)
The bug in plain terms
- The qla2xxx driver implements support for QLogic Fibre Channel host bus adapters in the Linux kernel. CVE‑2024‑42289 arises during virtual port (vport) deletion logic: stale entries in an internal command array can cause attempted DMA unmap or other pointer dereferences on already‑freed or NULL structures, producing a kernel NULL‑pointer dereference and resulting crash. The NVD entry includes a canonical oops stack trace used by distributors to triage the fix.
Impact
- The vulnerability’s impact is primarily availability (kernel panics / crashes). Triggering the bug requires operations that exercise the qla2xxx driver’s vport deletion and error‑recovery code paths, commonly observed with Fibre Channel detach/recovery events under certain timing or resource conditions.
- Local exploitability is the expected vector: the bug is in kernel device driver logic rather than a remote network service. Nonetheless, because kernel code runs at the highest privilege, even a crash can be operationally serious in production or multi‑tenant environments.
The fix
- Upstream kernel maintainers applied a targeted corrective change to ensure the driver correctly synchronizes or clears stale entries and avoids dereferencing freed/NULL pointers during vport deletion. Distribution maintainers subsequently packaged fixed kernel releases or backports. Operators should update to the fixed kernel or kernel package recommended by their distribution or cloud vendor. Distribution advisories (Ubuntu, Red Hat, Amazon Linux, etc.) document the package-level remediation for affected kernels.
What Microsoft’s sentence actually means — precise interpretation
Microsoft’s public line — “Azure Linux includes this open‑source library and is therefore potentially affected” — does two things correctly:- It is an authoritative inventory statement for the **Azure Lift checked that product and found the implicated upstream kernel file(s), so Azure Linux images are in‑scope for remediation.
- It informs Azure customers where to prioritize immediate action (patch Azure Linux kernelspace packages first).
- It is not a guarantee that no other Microsoft product includes the same vulnerable qla2xxx code. Absence of a similar MSRC attestation for another product is absence of attestation, not *proof of abserosoft is rolling out CSAF/VEX attestations on a phased, product‑by‑product basis; the initial attestation for Azure Linux reflects the inventory work completed to date, not a universal scan of all Microsoft artifacts.
- Large vendors ship thousands of artifacts (VM images, Marketplace images, container base images, WSL kernels, firmware, agent packages). The same upstream kernel driver can be presages depending on kernel version, configuration flags, and backports. Until those artifacts are explicitly scanned and attested, defenders should treat them as unknown rather than not affected.
Is Azure Linux the only Microsoft product that includes qla2xxx (short answer)
Strictly speaking from Microsoft’s public mapping: Yes — Azure Linux is the only Microsoft product Microsoft has publicly attestplicated upstream kernel component for CVE‑2024‑42289 at the time of the advisory. That is what MSRC’s FAQ line communicates and it is authoritative for Azure Linux customers.Operationally and defensively: No — Azure Linux is not necessarily the only Microsoft product that could include the qla2xxx driver and therefore potentially be affected. Any Microsoft product or image that ships a Linux kernel build matching the vulnerable commit range and kernel configuration (i.e., builds that include qla2xxx as built-in or as a module) could be a carrier. Examples of such artifacts include WSL2 kernel images, Azure‑tuned kernels for VM SKUs, Marketplace images, AKS node images, and Microsoft‑published container base images — all of which must be verified individually.
To be absolutely clear: the presence of the qla2xxx source in an upstream tree and its inclusion in a binary artifact is a build‑time property. Microsoft’s statement says they verified Azure Linux; it does not certify that every Microsoft image and kernel has been exhaustively scanned.
What to check in your estate — concrete, actionable verification steps
If you operate systems that consume Microsoft artifacts (Azure VM images, WSL, AKS nodes, Marketplace appliances, or Microsoft‑published container images), follow this checklist to move from “unknown” to “known” status fast.1) Inventory and prioritization
- Enumerate all Microsoft‑distributed images and kernels you run: Azure VM SKUs, Marketplace images, AKS node pools, WSL kernels, and any images pulled from Microsoft registries.
- Prioritize interactive and production workloads, and any systems using Fibre Channel HBAs or platform support for qla2xxx.
2) Kernel and module checks (on each Linux host)
- Check kernel version and package info:
- Debian/Ubuntu: dpkg -l | grep linux-image
- RHEL/CentOS: rpm -q kernel
- Check whether the qla2xxx module is present or compiled in:
- lsmod | grep qla2xxx
- modinfo qla2xxx (if module exists)
- grep -i qla2xxx /lib/modules/$(uname -r) -R
- Check kernel config for driver build flag:
- grep CONFIG_SCSI_QLA2XXX /boot/config-$(uname -r) || zcat /proc/config.gz | grep CONFIG_SCSI_QLA2XXX
- If the module is neither loaded nor present, the kernel likely wasn’t built with qla2xxx and cannot carry the defect — but you must still verify for each artifact image because kernels differ across distributions and Microsoft artifacts.
3) For WSL2 and Windows hosts
- WSL2 runs a Microsoft‑distributed kernel on many Windows installations. Query the WSL kernel version and the kernel image that WSL is using (wsl --status and examine the configured kernel file if custom). If WSL is using Microsoft’s distributed kernel, check whether that kernel build includes the qla2xxx driver and whether Microsoft has attested or patched it. Do n kernels include server‑grade device drivers for Fibre Channel — many WSL kernels are trimmed, but this must be verified.
4) For Azure VM images and Marketplace appliances
- Azure Marketplace or vendor images may use Microsoft‑published kernel builds or vendor kernels. For Microsoft‑maintained Azure kernels, check the distribution advisory that maps CVE numbers to azure kernel package versions (for example, Ubuntu’s USN advisories reference linux‑azure packages and list the kernel versions patched for wide CVE groups that include 2024‑42289). Update the kernels to the patched linux‑azure package versions and reboot.
5) Container images, CI/CD artifacts and SBOMs
- Use SBOMs, image scanners and CI build logs to identify binaries or kernels that include qla2xxx source or object code. Kernel modules can be embedded in initramfs or in container base images used for privileged containers; treat any privileged container that carries a kernel module as an investigation target.
6) If you find qla2xxx present
- Patch the kernel to a vendor‑supplied fixed package or apply the upstream commit and rebuild the kernel if you manage custom kernels.
- If you do not need the driver, consider blacklisting the module or disabling it in your kernel configuration for future builds:
- echo "blacklist qla2xxx" > /etc/modprobe.d/blacklist-qla2xxx.conf
- Reboot after kernel updates and validate that the fixed kernel is running.
Patch paths and vendor guidance (what to apply)
- For Azure Linux images and linux‑azure kernels, follow the Azure image or distro guidance: update package repositories and install the patched linux‑azure kernel package version referenced in distribution advisories (Ubuntu’s USN entries include the precise linux‑azure package targets for grouped kernel CVEs that include CVE‑2024‑42289). Reboot into the new kernel.
- For cloud distribution images (Debian/Ubuntu/Red Hat/Oracle/Alma/centos), apply the distributor’s kernel security updates; distribution advisories list the specific package releases and fixed versions.
- For custom kernel builds or appliances, apply the upstream qla2xxx patch commit from the kernel stable tree and rebuild/redeploy kernels according to your normal process.
Monitoring, detection and compensating controls
- Monitor kernel oops messages and dmesg logs for qla2xxx or qla2xxx_wq workqueue traces indicative of the known oops stack. The NVD entry includes a representative stack trace; use it to tailor log detection rules.
- In multi‑tenant or cloud environments, suspicious repeated crashes and reboot cycles on hosts backing many VMs are a high signal; investigate host kernel logs and the presence of QLogic HBA drivers.
- Where patching immediately is impossible, consider:
- Temporarily disabling Fibre Channel interfaces if operationally feasible.
- Blacklisting qla2xxx where hardware is not used.
- Scheduling maintenance windows to apply kernel upgrades and reboots.
Critical analysis — Microsoft’s approach: strengths and limitations
Strenable attestation for Azure Linux.** Microsoft’s MSRC mapping gives Azure customers a determinative signal: Azure Linux images were inspected and are in‑scope. That direct mapping makes triage and automation straightforward for customers using those artifacts.
- **Commitment to machineMicrosoft’s phased rollout of CSAF/VEX attestations (announced as beginning in October 2025) is a material transparency improvement: machine‑readable product‑level attestations help large organizations automate triage and prioritization.
Limitations and risks
- Phased attestation can create an “attestation gap.” Starting with a single product family (Azure Linux) leaves other Microsoft artifacts un‑attested for a period. terpret the absence of attestations for other products as proof of safety risk leaving unverified carriers unpatched. The correct operational posture is to assume unknown = must verify rather than not affected.
- Binary reuse and rebuilds complicate inventory. The same upstream code can app Microsoft artifacts via shared build pipelines, container images, or vendor backports. A product-level attestation does not automatically propagate to all artifacts that repackage the same code.
- Customer responsibility to verify artifacts. Until the vendor enumerates every artifact, customers must contry (SBOMs, image scanning, kernel checks) across the estate. The MSRC statement is a necessary but not sufficient piece of evidence for an enterprise risk‑management process.
Practical recommendations for administrators
- Patch Azure Linux images immediately if you run them. Apply Microsoft’s and the distribution’s kernel updates and reboot into a patched linux‑azure kernel. Ubuntu’s USN bulletin grouping calls out linux‑azure package versions associated with many kernel CVEs and is an example of vendor guidance you should follow.
- Inventory all Microsoft‑distributed artifacts you consume. Don’t assume only Azure Linux matters. Check WSL kernels, Marketplace images, AKS node images, Microsoft‑published container base images, and any Microsoft-supplied kernel packages in your supply chain.
- Automate artifact verification where possible:
- Integrate CSAF/VEX feeds from vendors when available.
- Generate and consume SBOMs for images and appliances.
- Use kernel module scans (lsmod/modinfo) and file‑system searches in images to detect driver modules.
- For custom kernels and appliance images, apply upstream fixes or backports and rebuild images; then redeploy and validate.
- Maintain monitoring rules for kernel oops patterns matching the qla2xxx stack trace and escalate any repeated host crashes for immediate remediation.
Final assessment and context
Microsoft’s MSRC entry that names Azure Linux as a product that “includes this open‑source library and is therefore potentially affected” is accurate and operationally useful for any customer running Azure Linux images: treat that attestation as an authoritative remediation priority. However, the wording is intentionally narrow — it documents Microsoft’s inventory work for Azure Linux, not a comprehensive, cross‑product exclusion oft’s CSAF/VEX inventory rollout covers additional artifacts, defenders must verify other Microsoft‑supplied kernels and images individually. Treat “attested” as a positive signal for a named product and “unattested” as a gap that requires verification, not as evidence of safety.Cross‑checking the technical facts with independent trackers (NVD’s CVE entry and distribution advisories such as Ubuntu’s USN) confirms the kernel nature of CVE‑2024‑42289, its availability impact, and the standard remediation path — update the kernel and reboot. Use those vendor advisories to identify the exact patched package versions you must install.
Immediate checklist (copy‑and‑paste for ops)
- If you run Azure Linux images: update linux‑azure packages to the patched versions referenced in your distribution advisory and reboot.
- Inventory other Microsoft artifacts in your environment (WSL kernels, Marketplace images, AKS node images, Microsoft container bases).
- On each Linux host, run:
- uname -r
- grep CONFIG_SCSI_QLA2XXX /boot/config-$(uname -r) || zcat /proc/config.gz | grep CONFIG_SCSI_QLA2XXX
- lsmod | grep qla2xxx; modinfo qla2xxx
- If qla2xxx is present and you cannot patch immediately, consider blacklisting the module until a kernel update can be applied:
- echo "blacklist qla2xxx" > /etc/modprobe.d/blacklist-qla2xxx.conf
- Subscribe to MSRC / vendor CSAF/VEX feeds and distribution advisories and automate ingestion into your patch orchestration.
Microsoft’s public transparency — naming Azure Linux and committing to machine‑readable VEX/CSAF attestations — is welcome and helps customers automate remediation for the artifacts Microsoft has enumerated. But operational security depends on treatpositive signals about inspected artifacts*, not as implicit safety guarantees for everything else Microsoft ships. CVE‑2024‑42289 is a kernel driver bug; the blast radius is determined by which artifacts include that kernel code and which images and devices you run. Verify, patch, and monitor — and treat the MSRC attestation as a starting point, not the finish line.
Source: MSRC Security Update Guide - Microsoft Security Response Center