The Linux kernel fix for CVE-2024-44986 addresses a real, low-level IPv6 use‑after‑free (UAF) condition in ip6_finish_output2(), but Microsoft’s MSRC wording about Azure Linux being “the product that includes the open‑source library and is therefore potentially affected” is a product‑scoped attestation — useful and authoritative for Azure Linux customers, but not a technical proof that no other Microsoft artifact could contain the same vulnerable kernel code.
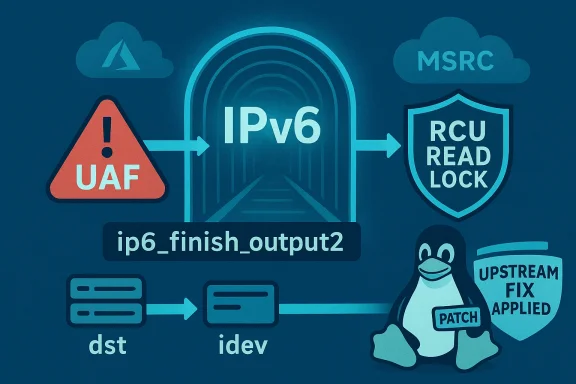
CVE‑2024‑44986 is a kernel‑space vulnerability discovered and fixed upstream in 2024. The root cause is a race / lifecycle bug in the IPv6 output path: when skb_expand_head() fails and returns NULL, the code path could leave the skb and its associated destination (dst) and interface device (idev) pointers in a state where they have been freed while still being referenced. The upstream patch ensures the relevant code holds the necessary RCU (Read‑Copy‑Update) protection — specifically rcu_read_lock() — so that dst and idev remain valid across the operation and the use‑after‑free is prevented.
Multiple independent trackers and distro advisories confirm the upstream fix was merged into the stable kernel trees and subsequently pulled into vendor packages or backported where necessary. Vendor security pages (distribution advisories and cloud‑provider kernel advisories) list the CVE, its technical description (skb_expand_head() → NULL → freed skb/dst/idev), and the fact that stable kernel branches received remedial commits. In short: the bug is real, the upstream fix is in place, and vendors have issued or are issuing kernel updates.
Therefore, treating Microsoft’s MSRC attestation for Azure Linux as authoritative for Azure Linux is correct — but operators should not assume the attestation implies there are no other Microsoft products to check.
CVE‑2024‑44986 is an important reminder that upstream kernel bugs propagate broadly across the Linux ecosystem — and that vendor attestations are a strong signal but only part of the operational work required to secure heterogeneous environments. Microsoft’s MSRC attestation that “Azure Linux includes the open‑source library” is a clear and useful piece of information; use it to prioritize patching Azure Linux immediately, and then follow the practical inventory and verification steps above to close the remaining blind spots in WSL, Marketplace images, and other Microsoft‑distributed artifacts.
Source: MSRC Security Update Guide - Microsoft Security Response Center
 Background / Overview
Background / Overview
CVE‑2024‑44986 is a kernel‑space vulnerability discovered and fixed upstream in 2024. The root cause is a race / lifecycle bug in the IPv6 output path: when skb_expand_head() fails and returns NULL, the code path could leave the skb and its associated destination (dst) and interface device (idev) pointers in a state where they have been freed while still being referenced. The upstream patch ensures the relevant code holds the necessary RCU (Read‑Copy‑Update) protection — specifically rcu_read_lock() — so that dst and idev remain valid across the operation and the use‑after‑free is prevented.Multiple independent trackers and distro advisories confirm the upstream fix was merged into the stable kernel trees and subsequently pulled into vendor packages or backported where necessary. Vendor security pages (distribution advisories and cloud‑provider kernel advisories) list the CVE, its technical description (skb_expand_head() → NULL → freed skb/dst/idev), and the fact that stable kernel branches received remedial commits. In short: the bug is real, the upstream fix is in place, and vendors have issued or are issuing kernel updates.
What Microsoft actually published (and how to read it)
Microsoft’s public guidance for MSRC CVE entries has recently begun including machine‑readable VEX/CSAF attestations that map an upstream CVE to specific Microsoft products. When an MSRC advisory says “Azure Linux includes this open‑source library and is therefore potentially affected,” that statement is:- Authoritative and actionable for Azure Linux images — Microsoft has completed an inventory for that product family and found the upstream component in those artifacts.
- Product‑scoped — it tells you what Microsoft has verified for the named product(s). It does not automatically assert that other Microsoft artifacts (WSL kernels, linux‑azure kernels, Marketplace images, internal appliance images, or third‑party images Microsoft distributes) were exhaustively scanned and found free of the component.
- Part of a rolling inventory model — Microsoft has said it will expand its attestations over time and update CVE mappings when additional Microsoft products are found to ship the same upstream component.
Why that distinction matters in practice
The Linux kernel is upstream, portable source code. Microsoft — like other large vendors — publishes and ships multiple, independently built Linux kernel artifacts across its product portfolio. Those artifacts include, but are not limited to:- Azure Linux distribution images (attested by MSRC)
- Microsoft‑provided kernel builds used by some Azure VM images (linux‑azure variants)
- The WSL2 kernel binary and its source tree (the Microsoft‑maintained kernel used to build WSL)
- Marketplace VM images and appliance images that bundle Linux kernels
- Any Microsoft device or appliance that embeds a Linux kernel (IoT, network appliances, specialized VM images)
Therefore, treating Microsoft’s MSRC attestation for Azure Linux as authoritative for Azure Linux is correct — but operators should not assume the attestation implies there are no other Microsoft products to check.
Technical summary of the bug (brief, for engineers)
- The vulnerable function: ip6_finish_output2(), part of the IPv6 network output path.
- Trigger condition: skb_expand_head() returns NULL (an allocation failure path).
- Problem: the code can continue to reference skb, dst and associated idev after they were freed — a classic use‑after‑free.
- Corrective action upstream: hold rcu_read_lock() across the access so dst and idev cannot be freed out from under the code; the upstream stable branches were patched to ensure this protection.
- Impact profile observed in vendor advisories: local attack vector, low privilege required in many scoring variants, with potential for denial‑of‑service and, in worst cases, memory corruption that could lead to control‑flow hijack (subject to exploitability specifics).
Is Azure Linux the only Microsoft product that could be affected?
Short answer: No — not necessarily. Long answer follows.- Microsoft has publicly attested that Azure Linux includes the implicated upstream kernel component for the CVE in question. That statement is authoritative for Azure Linux customers and is the right signal to act on immediately if you run Azure Linux images.
- However, Microsoft maintains multiple Linux kernel artifacts (for WSL2, linux‑azure kernels used in VM images, and other images). Some of those artifacts include the same upstream kernel subtrees (for example, drivers and core networking code). Until Microsoft completes inventory for those separate artifacts and publishes attestations, absence of a product name from the VEX feed is not proof that other Microsoft artifacts are free of the component.
Real‑world scenarios where this matters
- Customers running Azure Linux virtual machines should prioritize kernel updates for those images — Microsoft’s attestation confirms those images contain the component and are potentially affected.
- Enterprises with developer fleets that use WSL2 broadly should check WSL kernel versions and update Windows hosts (or instruct developers to run wsl --update) — WSL kernels are Microsoft‑maintained and can include upstream kernel code.
- Organizations running Marketplace images, third‑party appliances, or other Microsoft‑distributed images must inventory and verify each artifact: Microsoft’s product‑level attestation may not cover those images.
- Multi‑tenant hosts and platforms where local privilege separation is imperfect (e.g., shared build hosts, CI runners, or poorly segmented cloud instances) should treat any vulnerable kernel as a substantial risk because a local exploit could be chained to larger privilege escalations.
Practical checklist: How to confirm whether your systems are affected
Below are concise, actionable steps you can hand to your Linux/Cloud engineering teams. The list covers both Linux hosts and Windows machines running WSL.- Inventory Microsoft artifacts in your environment
- Prioritize: Azure Linux VM images, WSL2 clients in developer fleets, Azure Marketplace images, and any Microsoft‑supplied kernel packages used by guest images.
- Remember: containers generally share the host kernel; container images themselves do not protect you from a vulnerable host kernel.
- On each Linux host or VM, determine the running kernel:
- Command: uname -r
- Also collect: cat /proc/version and the distro kernel package name (e.g., rpm -q kernel or dpkg -l 'linux-image*').
- Check whether IPv6 kernel support was compiled in (the vulnerable code is in the kernel network stack):
- Command (if /proc/config.gz available): zcat /proc/config.gz | grep IPV6
- Or: grep IPV6 /boot/config-$(uname -r)
- If IPv6 is not compiled in and relevant networking paths are disabled, exposure can be reduced — but do not assume absence of risk without cross‑checking.
- Look for the symbol (fast check):
- Command: sudo cat /proc/kallsyms | grep ip6_finish_output2
- If the symbol is present in /proc/kallsyms, the running kernel exposes that code path. Note: kallsyms may be restricted on some systems; you may need appropriate privileges.
- If you run WSL on Windows machines:
- Command from a Windows shell: wsl uname -r
- Use: wsl --update to get the latest Microsoft WSL kernel. For managed fleets, include WSL updates in your patch cycle.
- For VMs and images in Azure:
- Record the exact image SKU and kernel package details. Compare the kernel package version with your vendor’s advisory for the CVE to determine whether your kernel version predates the fix or contains the backport.
- For Marketplace images and appliances:
- Extract the kernel version the image ships (boot a maintenance instance or examine image metadata). Treat each image as a separate artifact; don’t rely on product‑level statements for Azure Linux to cover Marketplace images.
- If you find an exposed, vulnerable kernel:
- Apply your vendor’s kernel update (package update + reboot). If the vendor has published a backport, that is acceptable; otherwise, apply an updated upstream kernel that contains the fix.
- Schedule reboots in line with your availability windows; kernel updates require reboots to take effect.
Quick remediation options and mitigations
- Preferred: apply vendor‑supplied kernel patches (or upstream patched kernels) and reboot. That’s the stable, supported remediation path.
- Temporary mitigation: disable IPv6 as a stopgap only when operationally feasible and after understanding impact:
- sysctl -w net.ipv6.conf.all.disable_ipv6=1
- sysctl -w net.ipv6.conf.default.disable_ipv6=1
- Caveat: disabling IPv6 can break legitimate services and is not a substitute for a patch in production environments.
- For WSL: run wsl --update and reboot Windows hosts. For custom WSL kernels, rebuild with upstream fixes applied.
- For containerized workloads: remember containers use the host kernel; patch the host kernel rather than the container.
Recommended operational playbook (prioritized)
- Immediately patch all Azure Linux images and VMs you control (MSRC attested Azure Linux).
- Inventory other Microsoft artifacts and kernels (WSL2, linux‑azure, Marketplace images) and apply patches where needed.
- For organizations with large fleets, triage hosts by exposure:
- Publicly accessible or multi‑tenant hosts first.
- Developer laptops and WSL in dev fleets next.
- Internal-only test hosts last.
- Run targeted detection:
- Search endpoint inventories for kernel versions older than the fixed releases or running symbols like ip6_finish_output2.
- Communicate to stakeholders: include expected reboot windows, service impact, and rollback plan (boot to previous kernels if needed).
Threat model and exploitation likelihood
Vendor advisories and CVE metadata indicate a local attack vector with low privileges required in many scoring variants. That means:- A remote, unauthenticated attacker is unlikely to exploit this directly over the network without a prior foothold.
- A malicious or compromised local user, or an attacker who can execute code on the host (for example via a container escape, compromised CI job, or an unpatched service giving shell access) could exploit this to cause a kernel crash or trigger memory corruption.
- Denial‑of‑service (kernel panic or OOPS) is the most straightforward impact and is the most commonly observed exploit outcome for UAFs in network code.
- The potential for escalation to arbitrary code execution exists in theory, but exploitability depends on architecture, kernel hardening, KASLR, mitigations, and the particular memory layout — this is an asymmetrical, high‑effort exploit path compared to a DoS.
Strengths and risks of Microsoft’s approach (VEX/CSAF attestations)
Strengths:- Machine‑readable product attestations make triage faster for security teams that rely on SBOMs and automation.
- Attesting Azure Linux first gives customers a deterministic signal: if you run Azure Linux, you know to patch.
- Microsoft’s commitment to expand attestations and update CVE mappings improves long‑term transparency.
- Product‑scoped attestations can create a false sense of exclusivity — customers may incorrectly assume “only Azure Linux” is affected and skip checking WSL or other Microsoft images.
- Attestations are only as useful as the completeness of the vendor’s inventory; artifacts that are not yet inventoried remain blind spots.
- Timelines for expanding attestations and mapping legacy artifacts can be slow; defenders must not defer artifact‑level verification while waiting for vendor mapping updates.
Final recommendations (what you should do this week)
- If you run Azure Linux: apply the vendor kernel update now and schedule reboots.
- If you run WSL at scale in your organization: run wsl --update across Windows hosts and require WSL updates for dev machines as part of your endpoint patching posture.
- If you use Marketplace images or third‑party Microsoft images: inspect image metadata and kernel versions, and treat each image as an independent artifact to verify.
- For all Linux hosts: add the following quick triage to your inventory pipeline:
- Collect uname -r and /boot/config-$(uname -r) for every host.
- Check /proc/kallsyms for ip6_finish_output2 where possible (privileged check).
- Match kernel versions against vendor security advisories or assume vulnerable until vendor indicates fixed/backported versions are present.
- Build automation that consumes vendor VEX/CSAF attestations where available, but don’t let that automation omit any artifact‑level checks for Microsoft images that are not yet attested.
CVE‑2024‑44986 is an important reminder that upstream kernel bugs propagate broadly across the Linux ecosystem — and that vendor attestations are a strong signal but only part of the operational work required to secure heterogeneous environments. Microsoft’s MSRC attestation that “Azure Linux includes the open‑source library” is a clear and useful piece of information; use it to prioritize patching Azure Linux immediately, and then follow the practical inventory and verification steps above to close the remaining blind spots in WSL, Marketplace images, and other Microsoft‑distributed artifacts.
Source: MSRC Security Update Guide - Microsoft Security Response Center