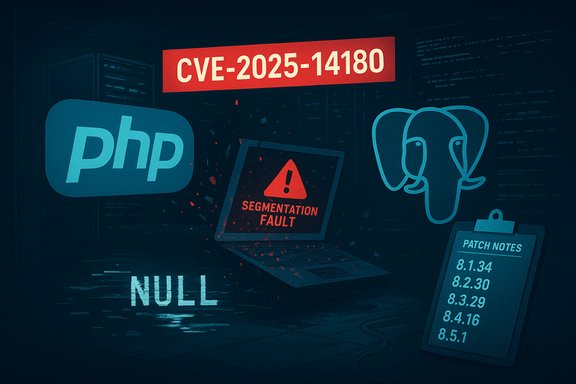
PHP’s PDO PostgreSQL stack contains a newly disclosed null-pointer dereference that can crash PHP processes and knock applications offline when emulated prepares are enabled — CVE-2025-14180 affects multiple PHP 8.x branches and was patched in the late‑December security release cycle; operators running pdo_pgsql with PDO::ATTR_EMULATE_PREPARES set to true should treat this as a high‑priority stability and availability risk and apply vendor fixes or mitigations immediately.
The vulnerability tracked as CVE-2025-14180 is a NULL pointer dereference in PHP’s PDO quoting path when using the PostgreSQL driver. Under certain inputs — notably an invalid byte sequence such as \x99 inside a parameter — the libpq helper PQescapeStringConn can return NULL. That NULL is subsequently assigned into an internal structure used by the PDO parser, and pdo_parse_params dereferences the field without checking for NULL, causing a segmentation fault and crashing the PHP process. The issue is triggered only when PDO::ATTR_EMULATE_PREPARES is enabled (the default behavior in many deployments). The PHP Project assigned patched releases across all supported 8.x lines: the fix is present in 8.1.34, 8.2.30, 8.3.29, 8.4.16, and 8.5.1. Public vulnerability databases and tracking services list the vulnerability with a high CVSS v4.0 vector (CNA-supplied score ~8.2) because the defect is reachable via networked inputs in web contexts and causes a high availability impact when exploited at scale.
Important verification note: the vendor advisory and technical details published by the PHP project (GitHub security advisory GHSA-8xr5-qppj-gvwj) and database records in NVD/CVE trackers contain the authoritative patched version numbers and reproduction guidance cited above; operators should cross‑check their distro/package changelogs and use vendor packages where available before rolling changes to production.
Source: MSRC Security Update Guide - Microsoft Security Response Center
 Background / Overview
Background / Overview
The vulnerability tracked as CVE-2025-14180 is a NULL pointer dereference in PHP’s PDO quoting path when using the PostgreSQL driver. Under certain inputs — notably an invalid byte sequence such as \x99 inside a parameter — the libpq helper PQescapeStringConn can return NULL. That NULL is subsequently assigned into an internal structure used by the PDO parser, and pdo_parse_params dereferences the field without checking for NULL, causing a segmentation fault and crashing the PHP process. The issue is triggered only when PDO::ATTR_EMULATE_PREPARES is enabled (the default behavior in many deployments). The PHP Project assigned patched releases across all supported 8.x lines: the fix is present in 8.1.34, 8.2.30, 8.3.29, 8.4.16, and 8.5.1. Public vulnerability databases and tracking services list the vulnerability with a high CVSS v4.0 vector (CNA-supplied score ~8.2) because the defect is reachable via networked inputs in web contexts and causes a high availability impact when exploited at scale. Technical anatomy: what exactly goes wrong
Where the null appears
- The PostgreSQL libpq function PQescapeStringConn is used by PDO’s PostgreSQL quoter (
pgsql_handle_quoter) to escape parameter values when emulated prepared statements are in use. - For certain invalid or non‑portable byte sequences, PQescapeStringConn can fail and return a NULL pointer (an error condition from libpq). The PDO code then assigns that returned pointer into the internal
plc->quotedfield.
The missing check and crash path
- Later inside pdo_parse_params, the code calls the
ZSTR_LEN(plc->quoted)macro (which dereferences thequotedpointer) without first confirming thatplc->quotedis non‑NULL. - If
plc->quotedis NULL the dereference triggers a segmentation fault in the PHP process, which for typical Apache/mod_php, FPM, or long‑lived worker processes results in immediate request failure and, depending on configuration, a process restart or broader service outage.
Reproduction (concise)
The original report includes a minimal reproduction pattern: compile PHP with pdo_pgsql, enable emulate prepares, and execute a prepared statement where the parameter contains a non‑existent/invalid byte sequence (for example, "alice\x99"). The sample code demonstrates a segfault when the vulnerable path is hit. Administrators and security teams should use the reproduction steps only in isolated test environments.Affected versions and scope
- Affected: PHP 8.1.x (before 8.1.34), 8.2.x (before 8.2.30), 8.3.x (before 8.3.29), 8.4.x (before 8.4.16), and 8.5.x (before 8.5.1).
- Fixed: 8.1.34, 8.2.30, 8.3.29, 8.4.16, 8.5.1.
- Trigger conditions:
- The pdo_pgsql driver is enabled and used by the application.
- PDO::ATTR_EMULATE_PREPARES is set to true (emulated prepares).
- A prepared statement parameter contains an invalid character sequence that causes PQescapeStringConn to return NULL.
Exploitability, attack surface and real‑world risk
Network reachability and attacker model
Because web applications commonly accept string inputs over the network and send them into prepared statements, the attack vector is logically network — an attacker can submit values that reach the vulnerable code path without local access. However, exploitability depends on the following practical realities:- Many frameworks default to server‑side/native prepares (PDO may or may not be configured to emulate prepares); exploitation requires that the affected application is using emulated prepares.
- The presence of byte sequences that trigger PQescapeStringConn to error is required; an attacker must inject or supply such sequences in user parameters.
- Because the result is a crash/segfault (denial of service), a successful exploitation yields availability impact rather than arbitrary code execution — the primary gain for an attacker is DoS.
Severity and scoring
- The PHP Project / CNA provided metrics placing the issue at a high contextual severity (CVSS v4.0 ~8.2), driven by network attack vector and high availability impact. Public trackers have reflected similar scoring.
- Independent trackers vary in per‑metric details (some list “Moderate” or give slightly different base scores) but the operational advice is consistent: treat this as a high‑priority patch for internet‑facing PHP services that use pdo_pgsql with emulated prepares.
Is remote code execution (RCE) possible?
- The public advisory and technical analysis classify this as a NULL pointer dereference causing a crash (CWE‑476). There is no authoritative evidence that CVE‑2025‑14180 directly enables RCE; the dominant risk is denial of service. Treat claims of RCE from this single defect as unverified unless additional, chained vulnerabilities are demonstrated.
What to do now: patches, mitigations and operational steps
Apply the vendor patches as the definitive fix: update PHP to one of the patched releases for your major branch.- Upgrade strategy (recommended):
- Inventory servers and containers for PHP versions: use php -v, phpinfo, or your configuration management tool to enumerate installed PHP branches.
- Identify whether applications use pdo_pgsql and whether PDO::ATTR_EMULATE_PREPARES is enabled (code review, php.ini, framework database adapters).
- Plan updates to one of the fixed releases: 8.1.34, 8.2.30, 8.3.29, 8.4.16, or 8.5.1 depending on your branch. Prefer vendor/distribution packages where possible to retain backport/packaging stability.
- Short‑term mitigations (if immediate upgrade is not possible):
- Disable emulate prepares where feasible (set PDO::ATTR_EMULATE_PREPARES to false) so PDO uses native server‑side prepared statements and avoids the quoting code path that calls PQescapeStringConn. This is an effective behavioral mitigation because the vulnerability arises only when emulated prepares are in use. Note: changing emulate prepares can affect SQL emulation semantics for some applications — test thoroughly.
- Input validation / sanitization: reject or normalize unexpected byte sequences at application boundaries (strip or validate strings to a known encoding such as UTF‑8 with strict validation) before passing them to PDO. This reduces the chance of sending sequences that force libpq to error. However, input filtering is a compensating control and not a replacement for patching.
- Container and image remediation:
- Rebuild container images that bundle vulnerable PHP binaries and push updated images through CI to production gates.
- Ensure base images used in automated builds are updated to include patched PHP packages.
- Distribution package notes:
- Where possible prefer vendor/distribution packages (Debian/Ubuntu/SUSE/RHEL packs). Many distribution trackers have already mapped the CVE into their security advisories and released updated packages; operators using packaged PHP should follow distro advisories for backports and security builds.
Detection, monitoring and forensic guidance
- Detection signals to watch:
- Unexplained PHP process crashes or segfaults appearing in syslog, journalctl, web server error logs, or PHP-FPM logs.
- Application logs that show PDO exceptions interleaved with abrupt worker restarts.
- Spike in 5xx/503 responses coincident with specific inputs or particular endpoints that accept freeform string input.
- Audit queries:
- Check PHP version: php -v or phpinfo for production PHP builds.
- Inspect application code or configuration for PDO::ATTR_EMULATE_PREPARES usage and for places where emulate prepares is enabled by default.
- Review recent crash dumps, core files, or backtraces. The advisory indicates the crash occurs during parameter parsing/quoting — look for stack traces pointing into ext/pdo/pdo_sql_parser.re or pdo_parse_params.
- Forensics and containment:
- If you suspect an active exploitation attempt (repeated crash triggers), temporarily disable verbose inputs from untrusted sources, rate‑limit suspicious endpoints, and apply mitigations (disable emulate prepares or isolate services).
- Collect core dumps and enable debug logging in non‑production environments for reproducible analysis; do not enable debug in production without appropriate safeguards.
Why this class of bug matters — practical perspective for WindowsForum readers
- Many PHP stacks are long‑lived processes (FPM pools, worker pools). A single segmentation fault in a worker process can escalate to application downtime, cascading restarts, and degraded capacity if crash loops occur. Even if only availability is affected, the operational impact on high‑traffic web APIs can be material.
- Emulated prepares are a commonly used abstraction because they simplify driver behavior and sometimes help with database compatibility. That convenience is why this bug matters: a widely used configuration pattern opened an exposure window. Knowing and controlling runtime driver settings is part of modern application hardening.
- The vulnerability exemplifies how dependencies into C libraries (libpq) can surface subtle error conditions that higher‑level languages must guard against. Defensive checks for NULL and robust error propagation are essential defensive coding patterns in bindings and driver code.
Risk assessment matrix (quick reference)
- Impact: High (availability — process crash / DoS).
- Exploitability: Realistic where conditions match (network‑exposed app using pdo_pgsql + emulate prepares + ability to submit crafted byte sequences). Complexity: Medium–High depending on the need to deliver triggering sequences.
- Likelihood: Higher for public‑facing PHP apps and microservices that accept arbitrary string input; lower for well‑hardened internal services that validate encoding and use native prepares.
- Immediate priority: Patch or mitigate within your next maintenance window if you meet any of the high‑risk criteria above.
Recommended checklist for operators (actionable)
- Inventory: List all hosts, containers and functions running PHP >= 8.1 and pdo_pgsql. Use automation to capture php -v, installed extensions, and container images.
- Detect usage: Search code and framework DB adapters for PDO::ATTR_EMULATE_PREPARES or configuration defaults enabling emulation.
- Patch: Upgrade PHP to the fixed release for your branch (8.1.34 / 8.2.30 / 8.3.29 / 8.4.16 / 8.5.1). Use vendor packages when possible.
- Temporary mitigation: If you cannot immediately patch, set PDO::ATTR_EMULATE_PREPARES = false for affected apps and test behavior in staging.
- Harden inputs: Enforce strict encoding (for example, validate UTF‑8 and reject unexpected 8‑bit sequences) at the application boundary.
- Monitor: Watch for segfaults, core dumps, and sudden spikes in worker restarts on web servers and FPM pools.
- Rebuild images: Update Docker/OCI images that contain vulnerable PHP using patched base images, and redeploy via CI/CD pipelines.
- Communicate: Notify teams that operate dependent services (API clients, frontends) about the change in prepare semantics if you toggle emulate_prepares.
Critical analysis: strengths, limitations and open questions
Strengths of the response and fixes
- The upstream PHP team made a clear, versioned set of fixes across branches and merged targeted defensive checks and fixes into stable releases; patched versions are available for all supported 8.x lines. That allows operators to patch within existing maintenance processes.
- The vulnerability report includes a clear proof‑of‑concept reproduction and a succinct explanation of the root cause (PQescapeStringConn returning NULL with insufficient NULL checking). That transparency accelerates triage and remediation planning.
Potential risks and caveats
- Some supply‑chain and packaging timelines lag: distribution packages and embedded appliance images will take longer to receive fixes. Operators of container images, PaaS platforms, and vendor appliances must confirm the fixed PHP package version in their vendor’s advisory before assuming protection.
- Flipping emulate prepares to false might change application behavior in edge cases — SQL composition, type casting and driver semantics can differ between client‑side emulation and server‑side prepares. Test application flows thoroughly before applying the mitigation in production.
- The advisory and trackers emphasize DoS as the primary effect; however, memory‑corruption classes can sometimes be chained with other bugs. Operators should not assume that DoS is the only possible outcome in every environment — aggressive threat actors may seek to combine faults. Flag that possibility and treat the immediate priority as patching.
Unverifiable or emerging points (flagged)
- Public exploit code availability: at the time of disclosure there is reproduction code in the advisory demonstrating a crash, but broad, weaponized exploit scripts aimed at mass exploitation had not been widely observed. This may change quickly after disclosure; defenders should assume PoCs and exploit tooling can appear within hours to days. Treat lack of public exploit reports as temporary and not a reason to delay remediation.
Conclusion
CVE‑2025‑14180 is a practical and actionable vulnerability in PHP’s PDO PostgreSQL quoting path that manifests as a NULL pointer dereference and process crash when emulated prepares are enabled and certain invalid byte sequences are supplied. The PHP project has published patches across the 8.x series; immediate remediation is straightforward: inventory affected assets, apply the patched PHP builds (8.1.34 / 8.2.30 / 8.3.29 / 8.4.16 / 8.5.1), and — where patching cannot be immediate — consider disabling PDO::ATTR_EMULATE_PREPARES and tighten input validation. Monitor for segfaults, and rebuild/redeliver container images and packaged artifacts with patched PHP builds. Rapid action will close the window of opportunity for DoS attempts against PHP applications that connect to PostgreSQL via PDO.Important verification note: the vendor advisory and technical details published by the PHP project (GitHub security advisory GHSA-8xr5-qppj-gvwj) and database records in NVD/CVE trackers contain the authoritative patched version numbers and reproduction guidance cited above; operators should cross‑check their distro/package changelogs and use vendor packages where available before rolling changes to production.
Source: MSRC Security Update Guide - Microsoft Security Response Center