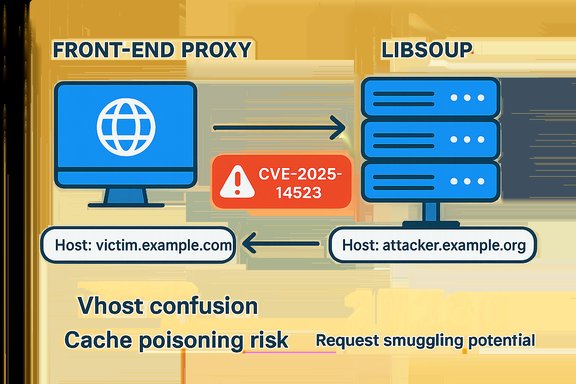
A newly disclosed vulnerability in GNOME’s HTTP library libsoup — tracked as CVE-2025-14523 — exposes a subtle but powerful mismatch in how duplicate Host headers are handled, creating a practical vector for virtual-host confusion, cache poisoning, and request‑smuggling–style bypasses when libsoup‑based servers sit behind proxies that interpret duplicate Host fields differently. The flaw stems from libsoup’s implementation returning the last Host header value when multiple Host headers are present, while many common front proxies and routers use the first Host header for routing; that order mismatch is enough to let an attacker craft requests that are routed to one backend but interpreted as addressed to another, with serious integrity and authorization consequences.
Libsoup is the GNOME HTTP client/server library widely embedded in desktop components, server-side agents, and many Linux distributions’ packages. It provides both synchronous and asynchronous HTTP APIs and is used across a range of upstream projects and downstream products. The project has been the focus of multiple parsing and header-handling fixes over recent years, and this new CVE continues that trend of defensive hardening around header parsing. The vulnerability was made public in December 2025 and appears in public vulnerability feeds and distro advisories, including entries maintained by the NVD and major Linux distributors; CVSS v3.1 scores published by vendors cluster in the High range (example: 8.2), reflecting low attacker complexity and significant integrity impact. At a high level the problem is straightforward: HTTP relies on the Host header as the canonical application-level routing key for virtual hosting. The HTTP/1.1 standard (RFC 7230) requires a single Host header in a request and prescribes that servers must reject messages that contain more than one Host header. Practical implementations, however, vary. When a proxy honors the first Host header but the backend (libsoup in this case) uses the last, an attacker can split the difference and force a proxy-to-backend mismatch that results in the backend believing the request targets a different virtual host than the proxy intended. RFC 7230 explicitly treats multiple Host headers as malformed and directs servers to respond with 400 (Bad Request) when more than one Host header is present.
Source: MSRC Security Update Guide - Microsoft Security Response Center
 Background / Overview
Background / Overview
Libsoup is the GNOME HTTP client/server library widely embedded in desktop components, server-side agents, and many Linux distributions’ packages. It provides both synchronous and asynchronous HTTP APIs and is used across a range of upstream projects and downstream products. The project has been the focus of multiple parsing and header-handling fixes over recent years, and this new CVE continues that trend of defensive hardening around header parsing. The vulnerability was made public in December 2025 and appears in public vulnerability feeds and distro advisories, including entries maintained by the NVD and major Linux distributors; CVSS v3.1 scores published by vendors cluster in the High range (example: 8.2), reflecting low attacker complexity and significant integrity impact. At a high level the problem is straightforward: HTTP relies on the Host header as the canonical application-level routing key for virtual hosting. The HTTP/1.1 standard (RFC 7230) requires a single Host header in a request and prescribes that servers must reject messages that contain more than one Host header. Practical implementations, however, vary. When a proxy honors the first Host header but the backend (libsoup in this case) uses the last, an attacker can split the difference and force a proxy-to-backend mismatch that results in the backend believing the request targets a different virtual host than the proxy intended. RFC 7230 explicitly treats multiple Host headers as malformed and directs servers to respond with 400 (Bad Request) when more than one Host header is present. Technical anatomy: how the mismatch works
What libsoup does (last‑value wins)
The libsoup parsing code path used to construct the request URI via soup_message_headers_get_one[_common] returns the last Host header value when a client supplies multiple Host headers. In other words, if a request contains two Host headers, libsoup’s server-side header accessor will take the later header as authoritative for virtual-host selection. The Red Hat Bugzilla summary and OSIDB import record the exact behavior that enables the mismatch.How proxies commonly behave (first‑value wins)
Many front-end proxies, routers, and load balancers give precedence to the first Host header they see when performing vhost routing or when constructing cache keys. This is a practical norm in certain proxy implementations and deployments (especially in configurations where proxies forward requests with minimal normalization). When the proxy uses the first Host header to decide which backend to route the wire request to, but the backend interprets the last Host header as authoritative, the backend and proxy will effectively disagree about which virtual host the request targets.Real-world exploitation primitive
An attacker who can deliver a crafted HTTP request into the proxy chain (for example, via a public-facing endpoint or by controlling a malicious client) can supply two Host headers in the same request. If the first header contains the legitimate hostname that the proxy uses to route to backend A, and the second header contains an attacker-controlled hostname (or one that triggers different ACLs/caching behavior), the proxy will forward the request to backend A while libsoup on backend A will interpret it as belonging to the second host. That vhost confusion can be weaponized to:- Bypass host-based access controls that assume the proxy’s routing equals server-side target.
- Poison a shared cache by causing cached responses to be stored or retrieved under inconsistent keys.
- Smuggle requests across vhosts or to internal-only endpoints that the proxy would otherwise block.
Why this is worse than a “trivial parsing bug”
At first glance duplicate header handling may look like an obscure parser quirk. In practice, however, header ordering semantics are fundamental to HTTP message interpretation and to the security assumptions made by middleboxes. Several past high-impact incidents show that tiny parsing discrepancies between proxies and backends can be amplified into full system compromise or large-scale cache poisoning. The libsoup mismatch is particularly dangerous because:- The Host header is the canonical vhost selector — it controls access and routing decisions.
- Proxy-backend desynchronization is easy to trigger if the proxy forwards headers without normalization.
- The attack requires no privileged access and can be initiated across the network.
Evidence, fix status and vendor responses
- NVD and multiple vulnerability aggregators list CVE-2025-14523 with the concise description that libsoup returns the last Host header value while many proxies honor the first, enabling vhost confusion. The NVD entry records the core technical fact and provides the published timestamp.
- Red Hat’s bug tracker and advisory entries document the issue (Bug 2421349) and record that an OSIDB import shows libsoup accepting duplicate Host headers with a last-value-wins policy; the Bugzilla page includes the PoC summary demonstrating routing vs interpretation mismatch.
- Major Linux distributors have published advisories or CVE listings recognizing the issue. For example, SUSE and Ubuntu have public CVE pages and security notices that mirror the description and classify the issue with a high severity vector (CVSS ≈ 8.2). These vendor pages also enumerate the packages and distro versions they consider affected.
- Patches: upstream and distribution packaging activity shows code changes to the libsoup header-parsing routines. Debian’s libsoup3 repository contains commits that adjust soup-message-headers behavior and the logic for soup_message_headers_get_one and related functions — changes that align header-get semantics with the desired behavior for non-list headers (i.e., ignore duplicates or treat duplicates as malformed). Those commits are the practical fix that maintainers are shipping in updated packages.
- Attribution: Red Hat noted that reporters (Ky0toFu and the Sovereign Tech Resilience program) submitted the finding. No widespread exploitation in the wild has been publicly reported at time of disclosure, but the low attacker complexity and the nature of the attack mean administrators should assume the issue can be weaponized quickly.
Practical impact and attack scenarios
- Integrity-first impact: The most likely consequences are integrity violations (unauthorized access to resources, incorrect authorization decisions) and cache poisoning. An attacker who can cause a backend to accept requests under a different Host identity may bypass host-based ACLs or access controls tied to the mistaken Host header.
- Attack prerequisite: The attacker must be able to send HTTP requests that reach the proxy chain (public endpoint or otherwise reachable front-end). They must be able to include duplicate Host headers in the crafted request — something that can be done with custom clients, raw TCP tools (telnet/nc), or certain HTTP libraries that allow header duplication.
- Exploitation example: A publicly reachable frontend proxy routes by the first Host header. The attacker sends:
- Host: victim.internal.example.com
- Host: attacker.example.org
The proxy uses the first value to route to the victim backend. The victim backend (libsoup) uses the last value and therefore applies rules or chooses resources as if the request were for attacker.example.org. If attacker.example.org maps to a page or behavior that causes the backend to disclose data or allows unsafe operations, the attacker gains a bypass. - Environment amplifiers: Shared caches, WAFs that use Host as a key, or multi-tenant backends that rely exclusively on Host for authorization are especially at risk.
Detection and hunting guidance
- Log analysis: Search access logs and proxy logs for requests that contain multiple Host headers. Many web servers log the Host header; comparing proxy logs (which likely store the first Host) to backend logs (which might include the raw headers forwarded) can reveal mismatches.
- Packet captures: Capture TCP streams for suspicious requests and inspect whether duplicate Host headers are present on the wire and whether intermediaries are rewriting or normalizing those headers.
- WAF / IDS rules: Add rules that detect requests with multiple Host headers or that compare the Host used for routing vs the Host used by the backend. Flag or drop requests with duplicate Host headers.
- Behavior alerts: Monitor for anomalous 4xx/5xx rates after enabling stricter checks, and for unusual cache misses or poisoning signs (e.g., cache serving responses for unexpected vhosts).
- CI/build pipeline checks: Inventory software that bundles libsoup (desktop apps, server agents) and ensure packaging includes updated libsoup versions.
Immediate mitigations and recommended fixes
The single best mitigation is to apply vendor-supplied security updates for libsoup as soon as they are available and tested in your environment. Distributors are already publishing updated packages; operators should prioritize public-facing systems and any services that sit behind proxies where Host header routing is used. If patching cannot be done immediately, deploy the following compensating controls in order of priority:- Front‑end normalization and strict rejection
- Configure front-end proxies and load balancers to reject requests that contain more than one Host header, or to normalize by canonicalizing the Host header before routing.
- Alternatively, configure the proxy to always rewrite the Host header to the exact value used for routing (derived from the request-target), ensuring the backend sees the same Host the proxy used.
- WAF rules and ingress validators
- Implement WAF signatures that block requests with duplicate Host headers or that normalize headers at the edge.
- Drop or 400 responses for requests with multiple Host headers (this aligns with RFC 7230 guidance).
- Backend hardening and defense-in-depth
- Where possible, make backend logic verify that the downstream-processed Host header matches any upstream-provided routing information (for example, using a trusted header injection pattern or mutual configuration).
- Add server-side checks to refuse requests where Host header semantics are ambiguous.
- Cache key hardening
- Ensure caches use both the full URL and other trustable attributes (TLS server name, connection metadata) when computing cache keys, not just the raw Host header forwarded from proxies.
- Operational controls
- Restrict access to admin endpoints by network controls and authentication such that even if Host confusion occurs, the attacker cannot reach sensitive internal resources.
Recommended remediation checklist (practical steps)
- Inventory
- Identify all systems running libsoup (server or client) via package management queries and configuration management databases.
- Patch
- Apply vendor-supplied updates for libsoup as published by your distribution vendor (Debian/Ubuntu/SUSE/Red Hat packages that include the upstream fix). Confirm package changelogs reference the relevant commit or CVE before wide deployment.
- Test
- In a staging environment, test proxy-backend flows with crafted duplicate Host header requests to ensure behavior is corrected and that services don’t regress.
- Normalize
- Configure front-line proxies/load balancers to normalize or reject duplicate Host headers before forwarding requests.
- Monitor & rotate
- Increase monitoring on web logs and WAF events for several weeks after the patch, and rotate any secrets or tokens if you detect suspicious activity that could indicate past exposure.
- Vendor coordination
- If you embed libsoup into a product or rely on a third-party vendor (appliance, ISV), request their timeline for patches and whether they normalized Host handling in their stack.
Why RFC compliance matters here
RFC 7230 clearly states a server MUST respond with 400 (Bad Request) to any HTTP/1.1 request message that contains more than one Host header field. That standard exists precisely to avoid the kind of ambiguity exploited by CVE-2025-14523. Aligning proxies and backends with the RFC — either by rejecting malformed requests or by canonicalizing header values at the edge — removes the predicate that makes this class of attack possible.Broader context and precedents
This libsoup CVE is another example in a string of parsing/normalization issues across different HTTP stacks in recent years. Industry hardening efforts in 2024–2025 hardened chunked-encoding parsing, Content-Length parsing, and other header semantics precisely because differences between middleboxes and backends enable request-smuggling and desynchronization attacks. Companies and platform vendors have repeatedly introduced toggles and registry keys to let administrators pilot stricter parsing without breaking fragile legacy integrations — a recognition that compatibility and security trade-offs are often operationally painful but necessary. The pattern is clear: put normalization at the ingress, and enforce RFC semantics to reduce the attack surface.Risk assessment and operational priorities
- Immediate priority: Patch internet‑facing services that embed libsoup and that sit behind proxies or shared caches.
- Medium priority: Audit proxy configurations and WAFs to ensure Host header normalization is performed and that duplicate Host headers are refused.
- Lower priority, but important: Audit internal tooling and third-party products that may vendor libsoup and coordinate patching timelines.
Cautionary notes and unverifiable claims
- There are no widely confirmed public exploit campaigns (as of publication) known to the public advisories; absence of public exploit telemetry does not imply the vulnerability is not being probed or targeted. Treat the CVE as high-risk given the low bar to invention and the commonality of proxy-backend topologies.
- Specific product impact (which downstream appliances or embedded products include affected libsoup versions) varies by vendor and build; administrators must consult their vendor advisories and package changelogs to confirm whether a given product is affected before assuming safety. Red Hat, Ubuntu, SUSE and downstream packagers have begun mapping affected packages; use those vendor-specific advisories to identify the exact fixed package versions for your platform.
Final verdict — what WindowsForum readers need to do now
- Prioritize patching: Apply updated libsoup packages from your distribution vendor or upstream project promptly for servers that are publicly reachable or that process requests from untrusted clients.
- Normalize at the edge: Ensure proxies and WAFs reject or normalize duplicate Host headers and that backend services refuse requests that deviate from RFC 7230 (i.e., more than one Host header).
- Hunt and monitor: Check logs, capture suspicious requests, and implement IDS/WAF rules to detect duplicate Host headers and proxy-backend host mismatches.
- Test and coordinate: Where you rely on third-party appliances or vendor binaries that embed libsoup, require a patch schedule and test upgrades before wide rollout.
Source: MSRC Security Update Guide - Microsoft Security Response Center