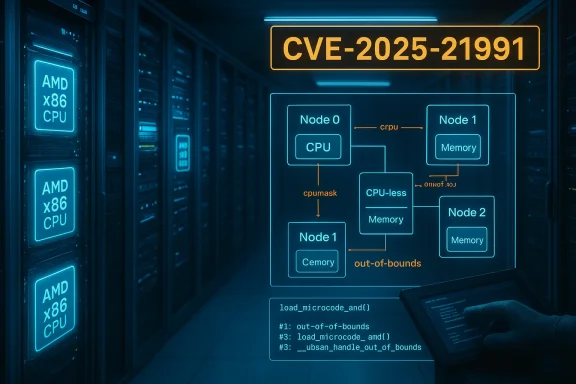
A subtle bounds-checking bug in the Linux kernel’s AMD microcode loader has quietly become a high-priority fix for distributors and administrators: CVE‑2025‑21991 corrects an out‑of‑bounds access in arch/x86’s AMD microcode path that can corrupt memory when microcode is flashed on systems with CPU‑less NUMA nodes, creating a realistic risk of system instability and denial‑of‑service during maintenance windows.
Non‑Uniform Memory Access (NUMA) systems partition memory and CPUs into nodes; most nodes contain both CPUs and memory, but modern deployments — particularly those using far memory or memory‑only regions — can expose nodes that have memory but no CPUs. The Linux kernel routine that handles AMD microcode updates, commonly referenced as load_microcode_amd(), historically iterated over all NUMA nodes and unconditionally accessed per‑CPU structures for the “first” CPU on each node. When a node’s CPU mask is empty, that logic resulted in an invalid index (CONFIG_NR_CPUS) being used to read per‑CPU data — a textbook out‑of‑bounds access.
Vendors and vulnerability trackers assigned this issue a CVSS v3.1 score of 7.8 (High) because while exploitation requires local, privileged access (microcode flashing is a privileged operation), the practical impact—memory corruption while performing microcode updates—can lead to crashes, kernel panics, or persistent service outages that are especially harmful in production environments. Vendor advisories and distribution updates landed quickly across multiple kernels and distributions once the fault was confirmed.
This is a classic robustness error: an unchecked return value from a mask‑querying helper becomes an invalid index and leads to memory corruption during a privileged operation (microcode flashing). While not an elevation‑of‑privilege vector on its own, the consequence—corrupting kernel memory during microcode update—can crash the system or leave it in an undefined state.
For administrators: treat microcode rollouts as high‑risk maintenance operations where the kernel and distribution packages must be trusted and up to date. The paradox here is clear — the procedure meant to improve CPU reliability can cause unreliability if the kernel makes unsafe assumptions about the system layout. Patch promptly, test in topology‑accurate staging, and add checks in automation to avoid repeating this class of outages.
Conclusion: CVE‑2025‑21991 is a practical reminder that hardware diversity and modern memory architectures demand defensive kernel code. Administrators who balance urgent microcode deployment needs against the operational risk of this bug — and who apply vendor fixes and cautious rollout patterns — will navigate this issue with minimal disruption.
Source: MSRC Security Update Guide - Microsoft Security Response Center
 Background / Overview
Background / Overview
Non‑Uniform Memory Access (NUMA) systems partition memory and CPUs into nodes; most nodes contain both CPUs and memory, but modern deployments — particularly those using far memory or memory‑only regions — can expose nodes that have memory but no CPUs. The Linux kernel routine that handles AMD microcode updates, commonly referenced as load_microcode_amd(), historically iterated over all NUMA nodes and unconditionally accessed per‑CPU structures for the “first” CPU on each node. When a node’s CPU mask is empty, that logic resulted in an invalid index (CONFIG_NR_CPUS) being used to read per‑CPU data — a textbook out‑of‑bounds access.Vendors and vulnerability trackers assigned this issue a CVSS v3.1 score of 7.8 (High) because while exploitation requires local, privileged access (microcode flashing is a privileged operation), the practical impact—memory corruption while performing microcode updates—can lead to crashes, kernel panics, or persistent service outages that are especially harmful in production environments. Vendor advisories and distribution updates landed quickly across multiple kernels and distributions once the fault was confirmed.
What exactly went wrong (technical deep dive)
The vulnerable code path
The problem centers on the function often identified in changelogs and advisories as load_microcode_amd() inside arch/x86/kernel/cpu/microcode/amd.c. The function’s job is to enumerate system NUMA nodes, inspect CPU masks, and decide whether the first CPU on a node requires a microcode update. The bug arises when the code assumes every NUMA node has at least one CPU and uses cpumask_first() without checking whether the mask is empty. On CPU‑less nodes cpumask_first() yields CONFIG_NR_CPUS, which is outside the valid per‑CPU array range; the code then dereferences cpu_data(CONFIG_NR_CPUS), producing an out‑of‑bounds access.This is a classic robustness error: an unchecked return value from a mask‑querying helper becomes an invalid index and leads to memory corruption during a privileged operation (microcode flashing). While not an elevation‑of‑privilege vector on its own, the consequence—corrupting kernel memory during microcode update—can crash the system or leave it in an undefined state.
Why CPU‑less NUMA nodes exist
CPU‑less NUMA nodes are not a theoretical oddity. Newer server architectures and experimental or specialized deployments use far memory (memory attached to a node without local CPU), memory expansion fabrics, or memory‑tiering schemes that can produce nodes with memory but no CPU. Containerized or virtualized host topologies, certain high‑density memory servers, and some disaggregated memory prototypes are examples where such topologies appear. Kernel code that iterates over nodes must therefore be defensive against empty CPU masks. Advisories explicitly reference this configuration as the trigger for the issue.Who is affected
- Systems running AMD x86 processors on Linux kernels that include the affected microcode loader path, particularly those with NUMA topologies that include CPU‑less nodes. Distributions issuing security advisories listed kernels across mainstream trees and vendor packages.
- Environments where microcode updates are performed in‑place (for example via initramfs or userland utilities) and where faulty index checks can be hit while the system is live. Flashing microcode is normally a privileged, administrator‑only procedure; therefore the issue requires local authenticated access to trigger.
- Cloud images and appliance kernels that bundle upstream kernel code without the fix — although public advisories from major distributors and livepatch providers were quickly rolled out, heterogeneous clouds and older images can remain vulnerable until explicitly updated.
Impact: availability, reliability, and operational risk
This vulnerability targets reliability and availability rather than confidentiality. The documented consequences include:- Immediate kernel crashes, oopses, or kernel panics during microcode flashing, causing service disruption and potential data loss if the host crashes at an inopportune moment.
- Memory corruption that could be either transient (only while flashing) or persistent if it corrupts kernel structures that survive until reboot, making recovery harder or requiring manual intervention. Advisories emphasize the reliability rather than secret‑leak implications.
- Escalated operational complexity in environments that rely on automated microcode rollouts (e.g., fleet management, cloud host maintenance), because the update itself can become the cause of outages on certain hardware/topologies. Livepatch alternatives and kernel upgrades become tactical choices.
Vendor responses and patches
Distributors and vendors moved quickly to remediate:- Major distributions (Debian, Red Hat, SUSE, Amazon Linux, and others) published advisories and released patched kernel packages and livepatch updates that contain the defensive change: iterate only over NUMA nodes with CPUs or otherwise check cpumask emptiness before accessing per‑CPU data.
- Cloud and enterprise livepatch services released livepatch packages for supported kernels where feasible, giving administrators a way to remediate without full reboots in some cases. Amazon Linux published livepatch advisories for its kernel-livepatch packages.
- Security portals and vulnerability databases cataloged the issue as CVE‑2025‑21991 with a CVSS of 7.8, and published remediation guidance that stresses applying distribution kernel updates promptly.
Practical detection and triage steps
If you manage Linux systems and want to quickly assess exposure and mitigate risk, follow this checklist:- Inventory kernel versions and distribution packages for hosts running AMD x86 processors. Prioritize systems with NUMA topologies or high memory configurations.
- Check whether your distribution has published advisory packages for CVE‑2025‑21991 and whether your host has those packages installed. Use the vendor’s recommended update channels (apt, yum/dnf, zypper, livepatch clients).
- Detect CPU‑less NUMA nodes on candidate hosts:
- Look for nodes with empty CPU masks under /sys/devices/system/node/node*/cpulist or use numactl —hardware to inspect topology.
- If a node has no cpus listed, it’s a candidate for the problematic path to be triggered.
- If you perform microcode updates centrally or via automation, pause those workflows on unpatched hosts until the kernel or livepatch is applied; flashing microcode on a vulnerable system risks causing a crash that could affect production systems.
- If possible, test microcode updates in an isolated lab that mirrors your NUMA topology; enable UBSAN_BOUNDS in a debug build to reproduce out‑of‑bounds triggers safely for testing. Advisory notes reference UBSAN traces in disclosure artifacts.
Remediation and mitigation: recommended steps
- Apply vendor patches immediately. The single most effective action is to install the distribution’s fixed kernel or livepatch that includes the defensive check in load_microcode_amd(). Vendor advisories include package names and update procedures; use those.
- If you cannot patch immediately:
- Avoid flashing microcode updates on susceptible hosts. This is a tactical tradeoff: you delay microcode fixes that may address other CPU-level issues in favor of avoiding immediate crashes. Document the decision and prioritize the patch window.
- Use configuration management and access controls to restrict who can perform microcode flashing (ensure only trusted administrators have the ability).
- If your environment supports kernel livepatching, apply the livepatch to avoid reboots where possible. Amazon Linux and some vendors provided livepatch packages for supported kernels.
- Test: after applying a vendor update, run your standard maintenance microcode update process in a staging environment that mirrors NUMA layout and observe for crashes or UBSAN warnings.
- Long term: add NUMA topology checks to any automated microcode deployment scripts so they can skip or handle nodes where cpumask_of_node() yields an empty result — this prevents similar logic errors in management tooling.
Detection and forensic guidance
A crash triggered by this bug typically appears during or immediately after a microcode update. Look for:- Kernel oopses or panics with call traces referencing load_microcode_amd or microcode flashing operations. UBSAN instrumentation (if present) will show array-index-out-of-bounds messages pointing to amd.c.
- Service outages coincident with scheduled microcode rollout windows. If multiple hosts with similar NUMA topologies fail during a coordinated rollout, suspect this class of defect.
- Absence of remote exploitation indicators; this bug is local and privileged in nature. Forensics should focus on who performed microcode flashing and whether that operator or automation was authenticated and authorized.
Risk analysis: why a privileged local bug matters
It’s tempting to deprioritize bugs that require privileged access, but operational realities make CVE‑2025‑21991 notable:- In managed environments, maintenance tasks are automated and executed widely (e.g., fleet microcode rollout). A single logic flaw in the kernel can turn a routine update into a mass outage. That operational amplification is the central risk vector.
- Supply‑chain and guest/host interactions: some cloud images and vendor appliances bundle kernels that may lag vendor mainline trees. If those images are used broadly in a private or public cloud, the local requirement for exploitation does not prevent widespread impact.
- Microcode is the last‑mile firmware fix for many CPU bugs. Administrators juggling firmware, microcode, and kernel patching must balance the need to deploy CPU fixes against the risk that the act of flashing locks up hosts — a non‑trivial operational problem when hosts are stateful and critical.
Longer‑term implications and hardening recommendations
- Kernel robustness: This CVE is a reminder that kernel code must assume non‑ideal topologies. NUMA awareness and defensive programming (check cpumask emptiness, validate indices) are essential in code handling hardware heterogeneity.
- Test suites: operators should add NUMA edge cases — memory‑only nodes, asymmetric topologies — to their regression test suites for kernel and system management tooling. Enabling sanitizer builds (UBSAN_BOUNDS) in controlled environments can reveal similar out‑of‑bounds issues before they hit production.
- Update orchestration: change microcode deployment practices to include topology discovery and per‑host gating. Tools that blindly flash microcode across a fleet can inadvertently trigger systemic failures when kernel or hardware corner cases exist. Adopt phased rollouts with safe‑stop conditions and canary hosts that mimic production topology.
How to prioritize this fix in your environment (practical playbook)
- Inventory: identify all hosts with AMD x86 CPUs and NUMA topologies. Use automated discovery to flag nodes with empty cpumasks.
- Triage: check whether your distribution has a CVE‑2025‑21991 advisory and whether you’re running the fixed kernel or livepatch package. Prioritize production hosts that run microcode update workflows.
- Patch: apply vendor kernel updates or livepatches as soon as practical; schedule reboots only when necessary and coordinate microcode updates after kernel fixes are in place.
- Test: in staging, run a microcode update and monitor for oopses; if UBSAN_BOUNDS is available on debug builds, use it to validate correctness.
- Harden: implement gating in deployment automation to skip microcode flashing on hosts that report empty node cpumasks until they have the patched kernel.
Final assessment and takeaways
CVE‑2025‑21991 is not an exploit that allows an unprivileged attacker to steal secrets or remotely compromise hosts, but it is an important operational bug with a high real‑world impact profile: a privileged, routine maintenance step (microcode flashing) can become a source of memory corruption and disruption on certain hardware topologies. The Linux community and major distributions responded with targeted fixes and livepatches; the right mitigation for most operators is to install vendor kernels or livepatches and to add topology checks to microcode deployment processes.For administrators: treat microcode rollouts as high‑risk maintenance operations where the kernel and distribution packages must be trusted and up to date. The paradox here is clear — the procedure meant to improve CPU reliability can cause unreliability if the kernel makes unsafe assumptions about the system layout. Patch promptly, test in topology‑accurate staging, and add checks in automation to avoid repeating this class of outages.
Conclusion: CVE‑2025‑21991 is a practical reminder that hardware diversity and modern memory architectures demand defensive kernel code. Administrators who balance urgent microcode deployment needs against the operational risk of this bug — and who apply vendor fixes and cautious rollout patterns — will navigate this issue with minimal disruption.
Source: MSRC Security Update Guide - Microsoft Security Response Center