A recently assigned Linux-kernel vulnerability, CVE-2025-22007, fixes a subtle but consequential Bluetooth error-handling bug in net/bluetooth/6lowpan.c where the function chan_alloc_skb_cb() could return NULL instead of the kernel’s standard error-pointer value; that incorrect return allows a subsequent dereference to trigger a kernel NULL-pointer fault and a reliable denial‑of‑service (DoS) on affected systems.
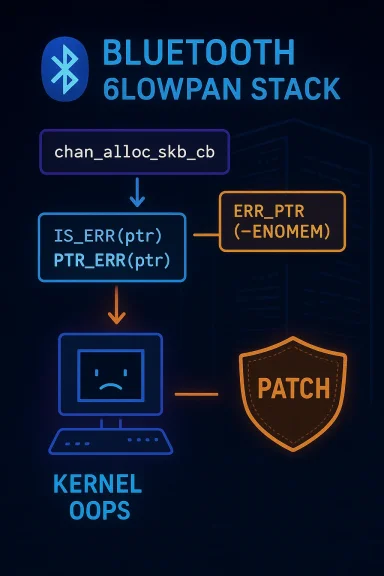
Bluetooth support in the Linux kernel is implemented through a layered subsystem (HCI → L2CAP → higher-level protocols). The 6LoWPAN subsystem adapts IPv6 over low-power Bluetooth links and relies on careful sk_buff (skb) and pointer handling inside net/bluetooth/6lowpan.c. The kernel commonly uses the ERR_PTR/IS_ERR/PTR_ERR idiom to encode error codes into pointer return values so callers can distinguish specific failures from a genuine NULL result; when that convention is broken, callers that expect ERR_PTR-style signals may incorrectly treat NULL as a valid pointer and dereference it, producing a kernel oops or panic.
CVE-2025-22007 was filed to describe exactly this class of mistake: chan_alloc_skb_cb() should return an error pointer (ERR_PTR(-ERRNO)) on failure, but in one error path it returned NULL, which in downstream callsites led to an unconditional dereference and a NULL-pointer fault. Upstream maintainers produced targeted fixes in the Bluetooth net tree and those fixes have been merged and backported across stable kernel series. Public vulnerability catalogs list the change and link to the stable backports.
Affected products and versions vary by downstream packaging, but trackers and advisories show the problem was present across many upstream stable branches (and therefore potentially present in a wide variety of distro kernels and OEM/embedded kernels) until the backported fixes were applied. Distributions and vendors that published advisories include Debian, Ubuntu, SUSE, and others; each has published fixed kernel package versions or guidance to obtain stable backports.
Practical exposure categories:
Multiple vendor advisories list the specific committed patches or the patched kernel package releases you should install. SUSE explicitly lists “Bluetooth: Fix error code in chan_alloc_skb_cb()” among its kernel fixes; Debian and Ubuntu trackers list package updates and the DLA/DSA advisories that map to backported stable patches. Operators should treat those vendor-supplied kernel updates as authoritative for their distribution.
CVE-2025-22007 is not a glamorous remote‑code‑execution story — it is an old-school contract bug with modern implications: a tiny return-value mismatch triggers a kernel‑level crash. The good news is the fix is small and widely available; the hard work for operators is inventory, patching discipline, and closing the long tail of embedded devices that all too often become permanent footholds for availability-focused attackers.
Source: MSRC Security Update Guide - Microsoft Security Response Center
 Background / Overview
Background / Overview
Bluetooth support in the Linux kernel is implemented through a layered subsystem (HCI → L2CAP → higher-level protocols). The 6LoWPAN subsystem adapts IPv6 over low-power Bluetooth links and relies on careful sk_buff (skb) and pointer handling inside net/bluetooth/6lowpan.c. The kernel commonly uses the ERR_PTR/IS_ERR/PTR_ERR idiom to encode error codes into pointer return values so callers can distinguish specific failures from a genuine NULL result; when that convention is broken, callers that expect ERR_PTR-style signals may incorrectly treat NULL as a valid pointer and dereference it, producing a kernel oops or panic.CVE-2025-22007 was filed to describe exactly this class of mistake: chan_alloc_skb_cb() should return an error pointer (ERR_PTR(-ERRNO)) on failure, but in one error path it returned NULL, which in downstream callsites led to an unconditional dereference and a NULL-pointer fault. Upstream maintainers produced targeted fixes in the Bluetooth net tree and those fixes have been merged and backported across stable kernel series. Public vulnerability catalogs list the change and link to the stable backports.
What the bug actually is (technical anatomy)
Where it sits in the stack
- The defect occurs in net/bluetooth/6lowpan.c in the chan_alloc_skb_cb() callback used by the Bluetooth 6LoWPAN virtual network device.
- The function’s job is to allocate and initialize an sk_buff or to signal an allocation/initialization error back to the caller in a pointer-safe way.
The kernel convention that was violated
- Kernel APIs that return pointers but also need to signal errors typically return a special pointer encoding produced by ERR_PTR(error_code).
- Callers use IS_ERR(ptr) to test for error returns and PTR_ERR(ptr) to extract the numeric error.
- Returning plain NULL instead of ERR_PTR(-ENOMEM) (or another encoded error) breaks that contract because NULL is not distinguishable from a valid “no-object” case in contexts where NULL is not expected; moreover, many callers do not check for NULL specifically and will dereference the pointer directly.
The consequence
- If the error path is taken during runtime (for example, memory allocation failure, or other recoverable error), the function returned NULL.
- A subsequent caller assumed a non-NULL pointer (or checked only for IS_ERR and not for NULL) and dereferenced it, producing a kernel NULL-pointer dereference—visible in logs as an oops and likely causing a crash or process termination in kernel context.
- The practical result is a deterministic or easily triggered kernel-level crash that yields a full service outage for the host until reboot or until a kernel restart occurs. This is a classic availability-impacting flaw.
Scope: who’s affected and how bad it is
Multiple authoritative trackers categorize CVE-2025-22007 as a medium‑severity flaw (CVSS ~5.5 v3.1) with a high availability impact because the typical outcome is a kernel NULL dereference and host failure. The attack vector is local (an attacker needs local access or Bluetooth radio proximity to trigger the defect), complexity is low, and privilege requirements are low in many threat models that allow untrusted Bluetooth input to reach the kernel stack. Public enrichment databases and distro trackers list the vulnerability against a broad range of upstream kernel versions and show the stable backport commits that resolve the issue.Affected products and versions vary by downstream packaging, but trackers and advisories show the problem was present across many upstream stable branches (and therefore potentially present in a wide variety of distro kernels and OEM/embedded kernels) until the backported fixes were applied. Distributions and vendors that published advisories include Debian, Ubuntu, SUSE, and others; each has published fixed kernel package versions or guidance to obtain stable backports.
Practical exposure categories:
- Standard desktops and servers with Bluetooth enabled and the kernel built with 6LoWPAN support are directly exposed.
- Embedded devices and IoT appliances that include Bluetooth/6LoWPAN stacks are high‑risk because vendor patch cycles for firmware/kernel are often slow or non-existent.
- Cloud VMs are rarely shipped with active Bluetooth stacks, so they are normally lower risk unless Bluetooth passthrough or special hardware is attached.
Evidence, patches and the upstream fix
Upstream kernel maintainers accepted a small, surgical change that ensures chan_alloc_skb_cb() returns proper error pointers on failure paths rather than NULL. The fix is minimal in code but critical in contract correctness; several stable-tree backports were created so distributors could include the repair in their security updates. Public references and commit lists in vulnerability databases link to the stable git commits that implement the change.Multiple vendor advisories list the specific committed patches or the patched kernel package releases you should install. SUSE explicitly lists “Bluetooth: Fix error code in chan_alloc_skb_cb()” among its kernel fixes; Debian and Ubuntu trackers list package updates and the DLA/DSA advisories that map to backported stable patches. Operators should treat those vendor-supplied kernel updates as authoritative for their distribution.
Exploitability and attacker model
- Attack prerequisites: local access to the host or proximity to the Bluetooth radio that the host accepts input from, plus the ability to cause the code path that returns an error (for example, a sequence of malformed or crafted packets that exercise the allocation or initialization error paths).
- Exploit complexity: low for causing a crash; higher and currently speculative for converting this into any information-disclosure or privilege escalation vector. Most public assessments list No Known Exploits in the wild at publication, and EPSS / exploitation trackers record very low exploitation probability. That does not mean the vulnerability is safe—just that so far only denial-of-service is the credible real-world impact.
Practical detection and forensics
What to look for in your logs and telemetry:- Kernel oops or panic messages that mention a NULL dereference in Bluetooth-related call chains. Typical stack traces will show the offending file and function (net/bluetooth/6lowpan.c and chan_alloc_skb_cb or the caller that dereferenced its return).
- KASAN (KernelAddressSanitizer) traces — if you run sanitizer-enabled kernels in lab or development — can pin the allocation/free trace leading to the invalid dereference.
- Repeated or correlated Bluetooth-related crashes across multiple hosts are a strong operational signal of a systematic problem or targeted activity.
- Add rules to your central logging/SEIM platform that alert on kernel oops strings with “net/bluetooth/6lowpan.c”, “chan_alloc_skb_cb”, or Bluetooth oopses.
- For hosts that must remain online, enable enhanced kernel logging and scheduled forensic dump capture around any Bluetooth activity or pairing windows to allow retrospective analysis.
Mitigation and remediation — an actionable checklist
- Identify exposure quickly:
- Run uname -r on Linux hosts and map kernel versions to vendor advisories listed for CVE-2025-22007; consult your distribution's CVE tracker for the exact patched package names.
- Patch as the primary remediation:
- Install vendor-supplied kernel updates that include the upstream backports (they are the authoritative fixes). Reboot hosts to load the updated kernel. Many distributions already published packages containing the fix—apply those via your normal patch-management pipelines.
- Temporary mitigations if immediate patching is not possible:
- Disable Bluetooth system-wide or blacklist the Bluetooth kernel modules on hosts that do not require wireless connections. Disabling the Bluetooth service entirely is the simplest, most reliable stopgap.
- Restrict physical or wireless access to hosts (reduce attacker proximity) and limit pairing to known devices only.
- On embedded devices with vendor-managed firmware, contact the OEM and insist on a kernel/firmware update; if no update is available, consider isolating the device network or replacing the unit where service continuity and security are critical.
- Validate remediation:
- After patch and reboot, confirm that kernel versions match the patched releases and that Bluetooth functionality works as expected.
- Reproduce safe tests in a controlled lab to ensure the previous crash path no longer triggers; do not attempt destructive tests in production.
- Hardening and long-term controls:
- For high-risk environments (POS, kiosks, medical devices), consider turning off 6LoWPAN features if not required by business function.
- Maintain CMDB/asset inventory of devices that include Bluetooth and track vendor firmware support windows carefully; the “long tail” of embedded/unpatched devices is the largest operational risk.
Why this matters — the operational risk picture
- The vulnerability is a textbook example of contract mismatch between a function’s intended return convention and an implementation detail; the fix is small but the operational consequences for unpatched fleets can be large.
- The most realistic attacker objective here is service disruption—an adversary within Bluetooth range or with local access can repeatedly trigger the NULL dereference to deny service on a host until it is rebooted or patched.
- The larger problem for defenders is distribution and OEM patching lag: while upstream and many major distros published fixes quickly, many devices (embedded appliances, industrial controllers, IoT) never receive timely kernel backports, creating a long tail of vulnerable hosts. That long tail is where attackers focusing on availability can derive real value.
Developer and maintainer notes (what the patch did and why it’s safe)
The upstream patch follows a conservative safety-first approach: it corrects the return path(s) in chan_alloc_skb_cb() so that ERR_PTR() is used for all error returns, and callers (where necessary) are expected to test using IS_ERR() or IS_ERR_OR_NULL() where appropriate. This is a mechanical, contract-repair change — it does not alter the higher-level design or APIs, and it is therefore straightforward to backport to stable kernel releases without introducing functional regressions. Upstream maintainers and stable-tree maintainers accepted those backports and released them in the usual stable branches.Recommended timeline for operators
- Within 24–72 hours: Identify all systems that run kernels or vendor images with Bluetooth/6LoWPAN support; if any are reachable by untrusted users or located in public/shared spaces, schedule them for priority patching.
- Within 7 days: Apply vendor-supplied kernel updates and reboot, or implement temporary mitigations (disable Bluetooth) until the update is possible.
- Within 30 days: Remediate long-tail devices (contact OEMs, plan device replacements if vendors do not provide updates) and add the vulnerability to your patch-and-asset program so future kernel CVEs in device-facing subsystems get higher operational priority.
Final assessment — strengths and remaining risks
Strengths- The bug was discovered and fixed upstream in a narrow, reviewable way; the fix is small, well-scoped, and suitable for stable backporting.
- Major vendors and distributions produced advisories and patched packages, enabling straightforward remediation for the majority of mainstream Linux deployments.
- The long tail: embedded systems, vendor kernels, and appliances often lag in receiving kernel patches; these devices may remain vulnerable for months or years and are difficult to inventory and patch.
- Detection sensitivity: unless you are actively monitoring kernel oopses or KASAN traces, a localized exploitation (or accidental trigger) may be written off as intermittent instability unless correlated properly.
- Attack surface assumptions: environments that allow untrusted Bluetooth inputs (guest networks, public kiosks, BYOD zones) should assume an adversary with proximity can cause widespread availability disruption.
Quick checklist for WindowsForum readers (operational summary)
- Immediately determine which hosts have Bluetooth enabled and which kernels they run; use uname -r and your patch-management inventory.
- Apply vendor-supplied kernel updates that include the stable backports for CVE-2025-22007 and reboot.
- If you cannot patch quickly, disable Bluetooth or blacklist Bluetooth kernel modules until you can update.
- Add SIEM rules to detect kernel oops/panic messages referencing net/bluetooth or chan_alloc_skb_cb and correlate those with Bluetooth activity windows.
- For embedded/OEM devices, contact the vendor for firmware/security advisories; where updates are not available, consider device isolation or replacement for critical services.
CVE-2025-22007 is not a glamorous remote‑code‑execution story — it is an old-school contract bug with modern implications: a tiny return-value mismatch triggers a kernel‑level crash. The good news is the fix is small and widely available; the hard work for operators is inventory, patching discipline, and closing the long tail of embedded devices that all too often become permanent footholds for availability-focused attackers.
Source: MSRC Security Update Guide - Microsoft Security Response Center