The discovery of CVE-2025-23048 — a session-resumption flaw in Apache HTTP Server’s mod_ssl — has sharpened attention on a familiar but persistent reality of modern software security: a vulnerability in a widely used open‑source component can pose ripple effects across diverse products and distributions. Apache’s advisory confirms that certain mod_ssl configurations in Apache HTTP Server versions 2.4.35 through 2.4.63 can allow a client that is trusted on one virtual host to resume a TLS 1.3 session against a different virtual host and bypass certificate-based access controls if strict SNI checks are not enforced. Microsoft’s public attestation today identifies the Azure Linux distribution as a known affected Microsoft product, and the company has said it will update its advisories if further Microsoft products are found to include the vulnerable component. That statement is accurate as a snapshot of Microsoft’s current product mapping — but it is not a technical guarantee that no other Microsoft-distributed products or images could contain an affected Apache/httpd build. This article explains what the vulnerability is, why Microsoft’s attestation should be read narrowly, who else could be affected inside and outside Microsoft’s ecosystem, and what practical steps operators should take now to detect, mitigate and remediate risk.
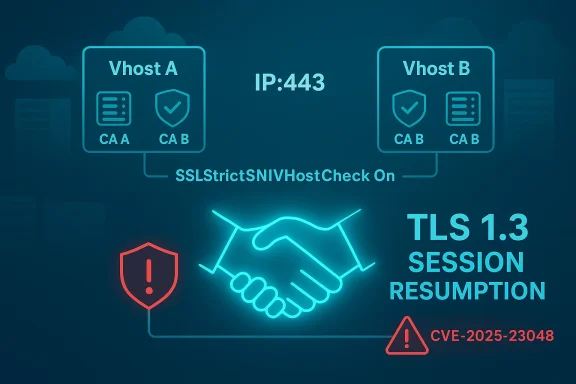
CVE-2025-23048 is an access-control bypass rooted in how mod_ssl handles TLS 1.3 session resumption across name‑based virtual hosts. In typical deployments you can have multiple virtual hosts (vhosts) bound to the same IP ort, each configured with its own TLS certificates and each trusting different client certificate authorities (CA lists). When TLS 1.3 session resumption is allowed, the server and client can resume a previous secure session without performing a full handshake; under certain mod_ssl configurations prior to the fixes, mod_ssl could incorrectly accept a resumed session for a different virtual host than the one that originally authenticated the client certificate. The result: a client authenticated to vhost A (trusted by CA1) might be able to access vhost B (which trusts a different CA2), effectively violating the intended trust boundary.
ort, each configured with its own TLS certificates and each trusting different client certificate authorities (CA lists). When TLS 1.3 session resumption is allowed, the server and client can resume a previous secure session without performing a full handshake; under certain mod_ssl configurations prior to the fixes, mod_ssl could incorrectly accept a resumed session for a different virtual host than the one that originally authenticated the client certificate. The result: a client authenticated to vhost A (trusted by CA1) might be able to access vhost B (which trusts a different CA2), effectively violating the intended trust boundary.
Apache’s security update for the 2.4 branch addressed the problem and the project released fixes in the 2.4.64 line; administrators should treat 2.4.64 or later as the fixed baseline. The issue is configuration-dependent — it is triggered only in deployments that (a) use TLS 1.3 session resumption, (b) host multiple name-based vhosts with differing client-CA trust settings, and (c) do not enable strict SNI host checks — but those conditions are common enough on shared, multi-tenant and appliance-like installations to make this a significant operational concern.
Operational consequences:
Short-term (fast, reversible):
Action plan for operators right now:
Source: MSRC Security Update Guide - Microsoft Security Response Center
 Background / Overview
Background / Overview
CVE-2025-23048 is an access-control bypass rooted in how mod_ssl handles TLS 1.3 session resumption across name‑based virtual hosts. In typical deployments you can have multiple virtual hosts (vhosts) bound to the same IPApache’s security update for the 2.4 branch addressed the problem and the project released fixes in the 2.4.64 line; administrators should treat 2.4.64 or later as the fixed baseline. The issue is configuration-dependent — it is triggered only in deployments that (a) use TLS 1.3 session resumption, (b) host multiple name-based vhosts with differing client-CA trust settings, and (c) do not enable strict SNI host checks — but those conditions are common enough on shared, multi-tenant and appliance-like installations to make this a significant operational concern.
How the bug works — plain language, then technical detail
What happens in everyday terms
Imagine a server hosting two virtual websites on the same IP and port. One site (secure.example.com) requires client certificates issued by CA-A; the other (internal.example.com) requires client certificates issued by CA-B. A user with a valid client certificate from CA-A should not be able to access internal.example.com. The vulnerability lets that CA-A–authenticated user reuse a previously established TLS 1.3 session (session resumption) to connect to internal.example.com and get access, because mod_ssl can accept the resumed session without confirming that the session’s original certificate-trust context matches the vhost being accessed.The technical mechanics
- TLS 1.3 supports session resumption mechanisms (e.g., tickets or PSKs) that let clients and servers avoid a full handshake on subsequent connections.
- mod_ssl maintains session state and maps sessions to server-side resources. When name‑based virtual hosting and differing per‑vhost trust contexts are used, mod_ssl must ensure resumed sessions are strictly validated against the current virtual host’s trust configuration.
- In the vulnerable code path, mod_ssl’s resumption logic could fail to re-evaluate the client-certificate-to-CA mapping for the resumed session when the SNI-based vhost selection changed between the original session and the resumed connection.
- If SSLStrictSNIVHostCheck is not set to On and TLS 1.3 resumption is used, the mismatch in expected trust boundaries opens the bypass window until a full (non-resumed) handshake occurs and the server re-validates the certificate chain against the correct vhost CA configuration.
Which Apache/httpd installations are affected?
- Affected upstream versions: Apache HTTP Server 2.4.35 through 2.4.63. The upstream fix was applied in the 2.4.64 series.
- Affected configurations: multi‑vhost setups that apply distinct SSLCACertificateFile/SSLCACertificatePath (or equivalent) settings per vhost, with TLS 1.3 resumption enabled and SSLStrictSNIVHostCheck disabled.
- Environments of note:
- Shared hosting and reverse-proxy appliances that host multiple customer sites on a single instance.
- Virtual hosting for intranets where client-certificate authentication is used to gate access to sensitive resources.
- Embedded or packaged appliances that include Apache/httpd as a component (network devices, NMS appliances, NAS web interfaces).
- Container images and cloud images that include the vulnerable httpd package.
What Microsoft said — and what that statement means
Microsoft’s public advisory confirms that the Azure Linux distribution includes the open-source Apache HTTP Server build that contains the vulnerable mod_ssl behavior and that Microsoft is publishing machine-readable attestations (CSAF / VEX) for Azure Linux as part of a transparency program. The important points to read into that statement:- When Microsoft says a product is “attested,” it is explicitly confirming that the Microsoft-managed build or image for that product contains the vulnerable upstream component. For Azure Linux, that attestation is authoritative: customers running Microsoft-published Azure Linux images should assume the vulnerability is in-scope and act accordingly.
- Microsoft’s current attestation list started with Azure Linux as part of a phased rollout. The fact that Azure Linux is currently the only Microsoft product listed is a statement about Microsoft’s inventorying and disclosure cadence — not a definitive technical assurance that no other Microsoft product contains Apache/mod_ssl builds in the vulnerable range.
- Microsoft has committed to updating the CVE/VEX/CSAF entries if additional Microsoft-managed products are discovered to contain the affected component.
Why Azure Linux appears first — and why that matters operationally
Microsoft chose to begin VEX/CSAF publication with Azure Linux because it is a discrete, Microsoft‑managed Linux distribution used widely across Azure images and Azure services. That made it a manageable starting point for automated, machine-readable vulnerability attestations.Operational consequences:
- The attestation provides high‑value, machine‑actionable metadata that customers can use in automated vulnerability triage and patch orchestration for Azure Linux images.
- Other Microsoft products and images (for example, built‑in App Service stacks, platform-managed container images, or custom Marketplace images maintained by third parties) may include Apache/httpd as part of a larger stack. Those artifacts are not yet universally attested, meaning customers must either rely on Microsoft to expand the attestation set or perform direct inventory and scanning.
- Because Microsoft’s VEX program is staged, the safest operational posture is to verify any product or image you consume (especially Microsoft-maintained platform images) rather than assume the attestation set is exhaustive.
Where else inside Microsoft’s ecosystem should you check?
If your organization uses Microsoft services or images, consider checking the following locations for vulnerable Apache/httpd instances:- Azure Linux images (attested — treat as affected unless Microsoft marks fixed).
- Azure Virtual Machine Marketplace images and any Microsoft-curated images for Linux flavors; some Marketplace images include Apache/httpd in the system image.
- Azure App Service built‑in runtime images (the PHP, WordPress and some LAMP/Apache stacks may use Apache as the web server). Built‑in images are maintained by Microsoft, and an affected httpd could exist in those stacks.
- Platform-managed base containers used by App Service or Azure Functions on Linux, where the runtime image contains httpd in the platform-provided layers.
- Containers and custom images deployed to Azure Kubernetes Service (AKS) or Web App for Containers — these are customer-controlled but may be based on Microsoft-provided base images or community images that contain vulnerable httpd.
- Local or managed appliances that Microsoft distributes as virtual appliances or VM images in the Azure Marketplace: some vendor appliances package Apache/httpd for web interfaces.
- On‑prem Microsoft products are less likely to include httpd as a mainline component, but third‑party add-ons and management consoles can embed web servers; examine product documentation and installed files.
Immediate mitigation checklist (what to do now)
Treat this as a two-track response: short-term mitigations that reduce immediate risk, and a rapid remediation plan that involves patching and audit.Short-term (fast, reversible):
- Inventory: locate all Apache/httpd installations and record versions. On Linux systems run:
- RPM-based: rpm -q httpd
- Debian/Ubuntu: dpkg -l | grep apache2 ; apt-cache policy apache2
- CBL‑Mariner/Azure Linux: tdnf list installed | grep httpd
- Containers: inspect image layers and run package queries inside running containers.
- Detect vulnerable versions: assume any httpd 2.4.x with 2.4.35 ≤ version ≤ 2.4.63 is potentially vulnerable unless your distro vendor indicates otherwise.
- Configuration mitigation: if you cannot immediately update, enforce stricter SNI checks by adding/ensuring this directive is set in each relevant vhost:
- SSLStrictSNIVHostCheck On
This instructs mod_ssl to reject resumed sessions where the SNI host would not match the expected host-level configuration. - Disable or harden session resumption temporarily (note: performance tradeoffs):
- To disable TLS session tickets (server-side): add SSLSessionTickets Off (per-server or per-vhost as needed).
- Alternatively, limit session resumption by controlling the session cache or rotating session-ticket keys frequently.
Disabling session tickets or resumption reduces the performance benefits of TLS 1.3 resumption but lowers the attack surface. - Isolate multi‑tenant vhosts: if shared vhosting is in use, consider isolating high‑sensitivity vhosts on separate IP
 ort bindings or separate instances until a patch is applied.
ort bindings or separate instances until a patch is applied. - Monitor for PoC/exploit activity: public proof-of-concept code exists; increase logging and monitoring for unusual session-resumption patterns and cross‑vhost access after resumption.
- Apply upstream or vendor-supplied patches: upgrade Apache HTTP Server to a fixed release line (2.4.64 or later) provided by your OS or distribution vendor. For Azure Linux images, apply the Microsoft-released package update when available.
- Rebuild and redeploy any affected containers or VM images with updated httpd packages in the image layers. Do not rely on pulling packages at runtime unless you have a robust image patching pipeline.
- Review and centralize TLS configuration management: enforce consistent SSLCACertificate* settings, SNI enforcement, and session-ticket policies across all vhosts.
- Validate the fix: once updated, verify that a resumed TLS session from a client authenticated to vhost A does not allow access to vhost B using a test harness or controlled PoC.
Practical command snippets and config examples
- Check httpd package version (RHEL/CentOS/Oracle/Azure Linux):
- rpm -q httpd
- tdnf list installed | grep httpd
- Check Apache binary version:
- httpd -v
- apache2ctl -v
- Enable strict SNI checking (add to each SSL vhost):
- In the relevant <VirtualHost *:443> block:
SSLStrictSNIVHostCheck On - Disable TLS session tickets (to block session-ticket resumption):
- In server config or vhost:
SSLSessionTickets Off - Update packages (examples — adapt to your distro):
- Debian/Ubuntu: sudo apt update && sudo apt install --only-upgrade apache2
- RHEL/CentOS/Fedora: sudo dnf update httpd
- CBL‑Mariner / Azure Linux: sudo tdnf -y update httpd
- For containers, rebuild Dockerfile base layers to use updated package sets and publish a new image tag; then redeploy.
Why “only Azure Linux” is not the same as “only Microsoft product affected”
There are three separate facts that often get conflated in threads like this:- Microsoft’s VEX/CSAF attestation status: Microsoft has attested Azure Linux as a known affected product. That attestation is authoritative for Azure Linux and is immediately actionable for customers who run Microsoft-published Azure Linux images.
- Microsoft’s inventory completeness: Microsoft’s public VEX program started with Azure Linux as a deliberate phasing step. Not listing a product today is not the same as an engineering determination that the product cannot possibly contain the vulnerable component. Microsoft has explicitly said it will update the record if more Microsoft products are found affected.
- Technical feasibility: many Microsoft-delivered or Microsoft‑maintained images and platform stacks could, in principle, include Apache/httpd — e.g., App Service Linux runtime images for PHP/WordPress, platform-provided container images or Marketplace appliances. Whether any of those particular artifacts actually contain the vulnerable httpd depends on the package versions the image was built with. That is why you must either rely on vendor attestations or perform your own inventory to know for sure.
Risk analysis — strengths, weaknesses, and practical risk to customers
Notable strengths in the vendor response
- Upstream patch availability: Apache published fixes in a subsequent 2.4.x release, allowing vendors and packagers to remediate quickly.
- Public disclosure and proof‑of‑concept circulation have made detection and patching priorities clear.
- Microsoft’s VEX/CSAF transparency program gives customers a machine-readable path to automate patch triage for Azure Linux and will help reduce uncertainty for the products it covers.
Remaining risks and pain points
- Inventory friction: many enterprises run dozens or hundreds of images, containers and platform services; absent vendor attestations, discovering whether any of them include vulnerable httpd builds requires active scanning of images and instances.
- Configuration complexity: the vulnerability is configuration‑dependent, which means naive scanning for package versions alone is necessary but not sufficient — you must also confirm TLS 1.3 resumption settings, per‑vhost SSLCACertificate configuration, and SNI handling.
- Patch rollout coordination: in cloud or platform environments, patching a base image may require coordinated redeployments across many services — and operators must follow the correct rebuild-and-redeploy workflow for containers and images to ensure the fixed binary is actually used.
- Performance tradeoffs for mitigations: disabling session resumption or session tickets can be an effective stopgap, but it carries real latency and CPU costs for high-traffic sites. Teams must weigh risk and cost when applying those mitigations.
Recommended detective controls and monitoring
- Image and package scanning: run automated scanners over container registries, VM images and OS package lists to identify any httpd instances in the vulnerable version range.
- Configuration checks: scan Apache configurations for:
- Presence of multiple name-based SSL vhosts with differing SSLCACertificate settings.
- SSLStrictSNIVHostCheck set to the default off.
- TLS 1.3 enabled with session tickets active.
- Traffic anomaly detection: look for requests that successfully access protected vhosts immediately after session-resumption sequences; log TLS handshake and session ID/ticket lifecycles for correlation.
- Incident readiness: prepare a test harness to reproduce the resumption scenario in a controlled environment to validate whether a given deployment is exploitable and to verify remediations.
How to prioritize remediation across diverse estates
- Identify critical assets that use client-certificate authentication or host sensitive multi-tenant workloads on Apache; make those highest priority.
- For high-risk hosts, apply either the upstream vendor patch or the configuration mitigations (SSLStrictSNIVHostCheck On; disable session tickets) as a temporary control.
- For platform images (App Service built-in stacks, Marketplace appliances) under Microsoft management, monitor Microsoft’s VEX/CSAF entries and vendor advisories; for customer-managed images, rebuild with patched packages immediately.
- For containerized environments, rebuild images from updated base images and redeploy via CI/CD pipelines; do not rely on in-container runtime updates alone for reproducible security posture.
Closing analysis and pragmatic advice
CVE-2025-23048 is a textbook example of how a narrow, protocol-level flaw in a ubiquitous open-source component can turn into a broad operational problem. Microsoft’s public attestation of Azure Linux is valuable — it gives a trusted and machine-readable signal that customers can use to automate remediation for that product — but it is an early-stage signal and not an exhaustive inventory. Operators should treat the attestation as authoritative for Azure Linux, and simultaneously assume that other Microsoft-managed artifacts might still be unverified.Action plan for operators right now:
- Inventory: find every Apache/httpd instance across your cloud images, containers and appliances.
- Patch: apply vendor-supplied httpd updates to reach a patched baseline (2.4.64+ or vendor-equivalent).
- Mitigate: if you cannot patch immediately, enable SSLStrictSNIVHostCheck and consider disabling TLS session tickets for the affected virtual hosts.
- Rebuild images: for containers and images, rebuild and redeploy with patched httpd binaries rather than relying on runtime fixes.
- Monitor Microsoft’s VEX/CSAF disclosures and vendor advisories for new attestations, and treat any newly-attested Microsoft product as in-scope.
- Verify: test that resumed sessions cannot cross vhost trust boundaries after remediation.
Source: MSRC Security Update Guide - Microsoft Security Response Center