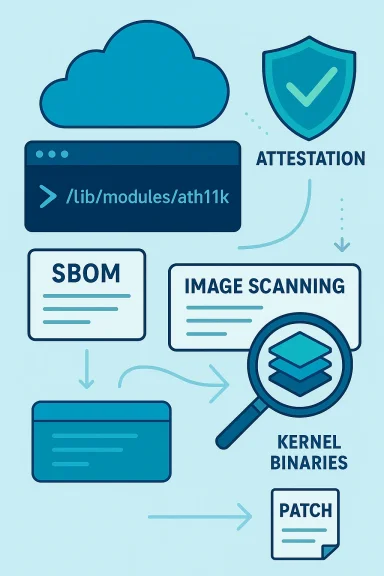
Microsoft’s public advisory for CVE‑2025‑23133 names the Azure Linux distribution as a product that “includes this open‑source library and is therefore potentially affected,” but that statement is a product‑scoped inventory attestation, not a categorical guarantee that no other Microsoft product can contain the same vulnerable Linux kernel code. Security teams should treat Azure Linux images as confirmed in‑scope, prioritize patching them, and at the same time run artifact‑level discovery and SBOM/scan checks across all Microsoft‑supplied images, agents and compiled binaries in their environment because absence of a published MSRC attestation does not prove absence of exposure. erview
CVE‑2025‑23133 is a Linux kernel vulnerability in the ath11k Wi‑Fi driver that was publicly disclosed in April 2025. The bug is a race in the ath11k regulatory‑domain handling path: the driver queues a cfg80211 reg_work and then proceeds to update the firmware’s channel list before cfg80211 has completed processing, which can lead to a slab out‑of‑bounds write observed by KASAN in ath11k_reg_update_chan_list(). Upstream patches fix the sequence by ensuring cfg80211 notifies the driver only after it has completed handling the new channel list (for example, by setting NL80211_REGDOM_SET_BY_DRIVER or similar synchronization). The issue has been cataloged by multiple vulnerability trackers and distro advisories and is considered a medium‑to‑high risk for local exploit and memory‑corruption outcomes. ntry for this CVE includes the question and answer the user quoted: in effect, Microsoft says Azure Linux includes the implicated upstream code and is therefore potentially affected, and Microsoft will update the CVE product mapping if additional Microsoft products are later identified as carriers. That is consistent with Microsoft’s programmatic rollout of CSAF/VEX attestations that began in October 2025; these machine‑readableended to make product‑level inventory claims explicit and automatable.
soft’s wording actually means — precise interpretation
Longer explanation:
Source: MSRC Security Update Guide - Microsoft Security Response Center
CVE‑2025‑23133 is a Linux kernel vulnerability in the ath11k Wi‑Fi driver that was publicly disclosed in April 2025. The bug is a race in the ath11k regulatory‑domain handling path: the driver queues a cfg80211 reg_work and then proceeds to update the firmware’s channel list before cfg80211 has completed processing, which can lead to a slab out‑of‑bounds write observed by KASAN in ath11k_reg_update_chan_list(). Upstream patches fix the sequence by ensuring cfg80211 notifies the driver only after it has completed handling the new channel list (for example, by setting NL80211_REGDOM_SET_BY_DRIVER or similar synchronization). The issue has been cataloged by multiple vulnerability trackers and distro advisories and is considered a medium‑to‑high risk for local exploit and memory‑corruption outcomes. ntry for this CVE includes the question and answer the user quoted: in effect, Microsoft says Azure Linux includes the implicated upstream code and is therefore potentially affected, and Microsoft will update the CVE product mapping if additional Microsoft products are later identified as carriers. That is consistent with Microsoft’s programmatic rollout of CSAF/VEX attestations that began in October 2025; these machine‑readableended to make product‑level inventory claims explicit and automatable.
soft’s wording actually means — precise interpretation
- “Includes this open‑source library and is therefore potentially affected” is an authoritative, product‑level confirmation: it means Microsoft inspected the Azure Linux images and found the upstream component referenced by the CVE in those images. For operators running Azure Linux, that statement is actionable: assume the produply patches. xclusivity or universal negation. Vendors frequently publish attestations per product or per artifact as their inventory mapping completes; absence of an attestation for Product B does not prove Product B is free of the same upstream code. Microsoft explicitly commits to updating CVE entries and VEX attestations if additional products are identified, which is industry practice for large vendors who ship many artifacts and images. iven oper like ath11k can appear in many places: Linux distributions, custom cloud images, appliance kernels, compiled binaries that bundle modules, or vendor‑maintained kernel packages used across services. Whether a specific Microsoft product is affected depends on whether that product ships a kernel build or image that includes the wireless stack and the ath11k driver. Microsoft’s Azure Linux attestation is a starting point for remediation — not a finish line. t verification of the vulnerability and patch stechnical claim in independent references:
- The upstream kernel announcement list and Linux CVE roster include CVE‑2025‑23133 and describe the ath11k reg notifier/reg_worker race and the KASAN slab‑out‑of‑bounds symptom. The Linux kernel mailing archives and the public CVE announce list are the canonical places to confirm the exact fix commit(s).ution security advisories and trackers list the CVE and provide fixed package versions or backports: Debian (DSA/Tracker entries), Ubuntu (USN entries), SUSE advisories and OpenSUSE patches, and other distro trackers have cataloged the issue and rolled fixes into kernel packages and images. These packages are the practical remediation units for deployed systems.gregator services and cloud provider advisories (for example Amazon Linux ALAS and third‑party vulnerability databases) also catalog the CVE, rate its severity and list the kernel versions or distro packages where the fix was applied. Cross‑referencing at least two independent trackers (upstream kernel mailing list + distro advisory) is the recommended verification approach for ops teams. Azure Linux the only Microsoft product that includes the library and is therefore potentially affected?
Longer explanation:
- Microsoft’s public statement that “Azure Linux includes this open‑source library and is therefore potentially affected”e attestation for Azure Linux*. If you run Azure Linux images (VM images, AKS node images built from those images, marketplace images), treat them as in‑scope and apply Microsoft/Ubuntu/SUSE kernel updates as appropriate. n does not logically prove exclusivity. Microsoft ships many artifacts (cloud images, appliance kernels, WSL kernels, container base images, agent packages, orchestration tooling) and any of those could contain the same upstream kernel driver code either because they include a kernel build that enables wireless modules or because a binary/component vendored a copy of the driver. Until Microsoft completshes VEX/CSAF statements listing those products as affected or not affected, outside observers cannot rely on the single attestation as a guarantee that there are no other carriers. ommitted to expanding product mappings and publishing machine‑readable VEX/CSAF attestations; if Microsoft later discovers the component in other product artifacts it apping. In the meantime, defenders should assume other Microsoft artifacts could be affected until verified* — i.e., verify, do not assume. l guidance — what to do if you run Microsoft products in your estate
- Immediate triage: inventory any running images that use Azure Linux and check their kernel versions and applied updates. Apply the Microsoft updates for Azure Linux or the distro kernel updates as soon as they areted. Microsoft’s attestation means these images are confirmed carriers and should be patched first. ng: run SBOM and binary/component scanning across:
- All container base images and build images you pull from Microsoft or your registries.
- VM images you run (Azure Marketplace images, custom images derived from Microsoft images).
- Any Microsoft agent packages (log/telemetry agents, security agents) or SDKs that ship native Linux components or kernel modules.
- Internal build artifacts that may vendor or statically link a kernel module or wireless driver.
- If the hardware in question is not using ath11k (no Qualcomm chips/wireless hardware present), consider blacklisting the module to remove the code path until you can patch. That’s a blunt but sometimes effective mitigation: it prevents the driver from loading at runtime.
- Where possible, avoid exposing local, untrusted users or processes to the kernel path that would trigger regulatory updates — e.g., limit who can change regulatory state or plug in device firmware. This is operationally specific and not a long‑term fix.
- For cloud images, consider replacing node pools with patched image versions or using livepatch systems where supported in your distro/vendor ecosystem.dation: after upgrading kernels, validate at runtime that the problematic path no longer triggers KASAN or OOPS on representative hardware. If you have reproducible tests (for example, a test harness that simulates regulatory domain updates), re‑run them in a staging environment before redeployment to reduce risk of regressions.
 Why the single‑product attestation matters — and why it is not sufficient
Why the single‑product attestation matters — and why it is not sufficient
- The MSRC attestation is highly valuable because it gives a single, authoritative signal operators can automate: if you run Azure Linux images, Microsoft has verified that those images include the vulnerable o remediation is straightforward to prioritize. This is important for large cloud fleets where a single product mapping can materially accelerate risk reduction. endors publish product‑scoped mappings as they complete inventories. The same upstream driver can show up in ancillary products (marketplace images, SDK containers, orchestration tooling) via reuse, rebuilds, or third‑party packaging. Outside security teams cannot exhaustively confirm Microsoft’s internal product inventory; therefoperative is to combine vendor attestations with artifact‑level discovery (SBOMs, image scans, module presence checks). crosoft’s attestation as a positive signal to prioritize Azure Linux images, but do not use it as a negative signal Assume unverified Microsoft artifacts could be affected until proven otherwise. deep dive (what the fix changes and why that prevents the bug)
- Root cause: the ath11k driver enqueues a cfg80211 reg_work and then proceeds to call ath11k_reg_update_chan_list() immediately. Because cfg80211 processes the new channel list asynchronously in reg_work, the driver can attempt to update firmware state before cfg80211 has finished modifying kernel data structures; that timing window produced a slab out‑of‑bounds write observable under KASAN. The bug is a classic race between asynchronous callbacks.sure the driver waits for cfg80211’s handling to complete (for example, by relying on cfg80211 to notify the driver once processing finishes — NL80211_REGDOM_SET_BY_DRIVER is one mechanism that changes ordering so cfg80211 issues a notification after step 2 is fully done). The fix synchronizes the steps so the driver’s update function only runs once the canonical channel list is stable. This removes the out‑of‑bounds window.: memory corruption in kernel drivers can lead to instability, local privilege escalation, or kernel panic. The practical exploitability varies with hardware, kernel configuration and whether the system has local unprivileged paths to trigger the timing window, but the class of bug is severe enough to require prompt remediation via distro kernel updates or vendor patches.d detection and hunting checklist (for SOCs and platform teams)
- Search images and nodes for the ath11k module:
- On hosts: check /lib/modules/$(uname -r)/kernel/drivers/net/wireless/ath/ath11k or run modinfo ath11k.
- In container images: scan layers for the same module path or for kernel module tarballs.
- Inspect dmesg and kernel logs for KASAN or OOPS traces referencing ath11k_reg_update_chan_list or ath11k_regd_update_work — these traces are the exact symptom reported in the public commit.M inventories for kernels built from vulnerable series (upstream versions noted in distro adny matching builds as in‑scope until patched. inventory marketplace images and nodepools that were built from Azure Linux base images; identify out‑of‑date nodepools and schedule rolling updates to patched images. offs and enterprise impact
- For most cloud and datacenter deployments, the risk surface is constrained: the bug requires local interactions (i.e., it is not a simple internet‑facing remote exploit for most configurations) and depends on specific wireless hardware and module loading. Many server‑class cloud instances do not load wireless drivers in normal configurations, which reduces the blast radius. However, any host that runs an image or appliance with wireless modules enabled — for example, developer laptops, IoT/edge appliances, specialized VM images, or edge devices — should be treated as potentially exploitable until validated.sk for large enterprises is supply chain and image drift: if you consume Micros or components and those images are the source for downstream images or CI pipelines, a single vulnerable kernel can propagate widely. That is why vendor attestations, SBOMs,lines matter. Microsoft’s public attestation helps customers prioritize, but operators must couple it with their own artifact scanning. mmendations (concrete next steps)
- Patch Azure Linux images immediat use; follow Microsoft’s update guidance for the distribution. mage scans across all Microsoft‑provided images, base containers, and marketplace artifacts in your environment; search for ath11k module files or kernel builds that include that driver. rnel packages from your distribution vendor (Debian, Ubuntu, SUSE, etc.) where applicable; if you depend on distro packages rather than vendor images, apply the distro advisories.patch immediately, temporarily blacklist the module on hosts that do not need wirelelocal user privileges to reduce the attack surface./CSAF attestations for updates to the product impact mapping and update your remediation priority if Microsoft adds other products to the affected list. Microsoft has said it will update the CVE mapping if impact to additional products is identified.
Source: MSRC Security Update Guide - Microsoft Security Response Center