Microsoft’s brief product-mapping for CVE-2025-3416 — that “Azure Linux includes this open‑source library and is therefore potentially affected” — is accurate for the product it names, but it is not a technical guarantee that no other Microsoft product or image could contain the same vulnerable rust-openssl code. Security teams should treat Azure Linux as in‑scope now, act quickly on updates, and simultaneously perform artifact‑level discovery across any Microsoft-supplied images, agent binaries, SDKs, and container workloads until Microsoft’s CSAF/VEX attestations or your own SBOMs confirm otherwise.
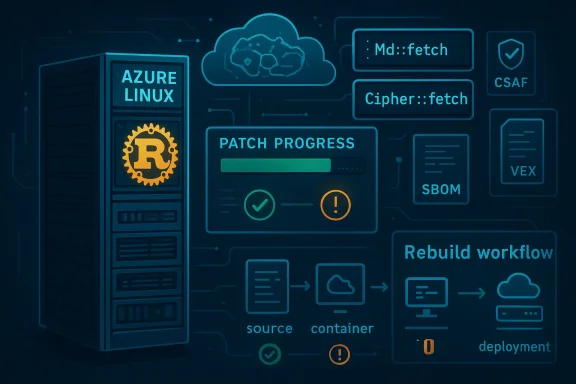
CVE-2025-3416 is a use‑after‑free issue in the Rust bindings to OpenSSL (the rust-openssl crate) that affects the Md::fetch and Cipher::fetch APIs when a non‑empty properties argument is passed. Upstream maintainers addressed the bug in later rust-openssl releases; distribution packages and vendor advisories followed with updates. Independent vulnerability trackers classify the issue as low-to-moderate severity depending on packaging and exploitability conditions, and multiple downstream distributions and vendors produced advisories and fixes.
Microsoft’s Security Response Center (MSRC) published a short, product-scoped advisory that identifies Azure Linux (the Microsoft-maintained Linux distribution formerly known as CBL-Mariner) as including the implicated open‑source library and therefore as “potentially affected.” Microsoft has also publicly committed to publishing machine‑readable CSAF and VEX attestations and began a phased VEX rollout in October zure Linux; MSRC says it will update the CVE/VEX records if additional Microsoft products are identified as carriers of the same upstream component.
This article explains what Microsoft’s wording really means, corroborates the technical facts about the vulnerability, and provides concrete, prioritized guidance for operators and security teams who need to triage risk across Microsoft‑supplied artifacts.
However, the current reality is a phased rollout. An attestation for Azure Linux converts one ambiguous case into a clear finding — but it does not magically attest every Microsoft image or binary. Until Microsoft publishes attestations for additional productsine MSRC VEX files with their own artifact scans and SBOM ingestion to achieve complete coverage. The safest operational stance is to treat un‑attested artifacts as unknown and verify them locally.
The upstream fix is available and distribution vendors have issued updates; the technical remediation is straightforward. The harder work is operational: rebuilding, redeploying, verifying, and — where appropriate — rotating keys. Do that work now for Azure Linux, and do it everywhere else you run Microsoft images or tools until attestations prove otherwise.
Source: MSRC Security Update Guide - Microsoft Security Response Center
 Background / Overview
Background / Overview
CVE-2025-3416 is a use‑after‑free issue in the Rust bindings to OpenSSL (the rust-openssl crate) that affects the Md::fetch and Cipher::fetch APIs when a non‑empty properties argument is passed. Upstream maintainers addressed the bug in later rust-openssl releases; distribution packages and vendor advisories followed with updates. Independent vulnerability trackers classify the issue as low-to-moderate severity depending on packaging and exploitability conditions, and multiple downstream distributions and vendors produced advisories and fixes.Microsoft’s Security Response Center (MSRC) published a short, product-scoped advisory that identifies Azure Linux (the Microsoft-maintained Linux distribution formerly known as CBL-Mariner) as including the implicated open‑source library and therefore as “potentially affected.” Microsoft has also publicly committed to publishing machine‑readable CSAF and VEX attestations and began a phased VEX rollout in October zure Linux; MSRC says it will update the CVE/VEX records if additional Microsoft products are identified as carriers of the same upstream component.
This article explains what Microsoft’s wording really means, corroborates the technical facts about the vulnerability, and provides concrete, prioritized guidance for operators and security teams who need to triage risk across Microsoft‑supplied artifacts.
What the bug actually is
Technical summary
- The vulnerability is a classic use‑after‑free (UAF): the rust-openssl bindings handled the properties argument in certain APIs in a way that allowed memory to be freed while still being referenced, causing undefined behavior. In practice, this could lead to the properties being treated as an empty string or, in pathological cases, to crashes or other memory‑safety failures.
- Affected public releases of the rust-openssl crate extend up through the 0.10.71 line; upstream changelogs show the fix landed in 0.10.72 (and related rust-openssl-sys updates in downstream packaging). Debian and Fedora packaging notes show maintainers pushing the updated crate versions immediately after the fix appeared upstream.
Exploitability and impact
- The practical exploitability varies with context. If an application exposes the vulnerable API surface to untrusted input or vendors a copy of the affected crate into a binary or package without rebuilding, then the attack vector exists. Many downstream vendors rated the issue lower where packaging choices or API usage patterns made exploitation unlikely; others flagged a higher practical severity where the vulnerable APIs were commonly used by packaged software.
- The canonical mitigation is to upgrade the rust-openssl crate to the fixed version (0.10.72+) and rebuild any binaries or images that statically link or vendor the crate. Distribution packages that ship a fixed upstream crate or rebuilt binary are also an acceptable remediation path.
What Microsoft’s short advisory does — and what it doesn’t
Exact meaning of the MSRC wording
When MSRC writes that “Azure Linux includes this open‑source library and is therefore potentially affected,” that is a product‑scoped inventory attestation: Microsoft inspected Azure Linux build outputs and identified the implicated upstream component there. For Azure Linux customers, that sentence is an authoritative signal to treat the distro’s images as in‑scope and to apply the publisher’s updates.What the sentence does not assert
- It does not say that Azure Linux is the only Microsoft produlibrary. It’s not an exclusivity declaration. Microsoft deliberately uses scoped attestations in its CSAF/VEX rollout: if and when additional Microsoft products are found to include the same upstream component, Microsoft will publish updated VEX attestations and update the CVE mapping.
- It also does not absolve customers who run other Microsoft artifacts (Marketplace images, platform agents, SDKs, container images published by Microsoft) from re those artifacts. The presence of vulnerable code is fundamentally an artifact‑level property — it depends on which upstream commits were compiled in, which modules were enabled at build time, and whether code was vendored into a binary.
Why many readers misread “Azure Linux includes…” as “only Azure Linux”
The phrasing is concise because it needs to be machine‑readable and easily consumable by automation, but it can be read incorrectly as exclusivity. That is dangerous operationally: treating a single‑line advisory as exhaustive can leave other artifacts unexamined and vulnerable. Microsoft’s own transparency program deliberately starts with one product (Azure Linux) to pilot the VEX/CSAF machinery before scaling to the rest of the product portfolio. Until Microsoft publishes attestations for other products, they remain unattested — not proven safe.Independent verification: cross-checking the key claims
To validate the technical and product statements we cross‑checked multiple independent sources:- Upstream and packaging evidence: the rust-openssl CHANGELOG shows an explicit fix for the Md::fetch and Cipher::fetch use‑after‑free and marks version 0.10.72 as the release that contains the fix. Debian’s package changelog records that update.
- Distribution advisories: Fedora, Ubuntu, Red Hat, SUSE and Amazon Linux trackers produced advisories and updated packages or mitigations. Fedora’s package notes recommend updating to the fixed crate and indicate most dependent packages did not use the affected API in a way that triggered the issue.
- CVE/NVD and vulnerability aggregators: public CVE entries and vulnerability feeds (NVD, CVE aggregators, and regional CERT postings) list CVE‑2025‑3416, describe the UAF class, and link to upstream commits/pull requests and vendor advisories. These independent trackers corroborate both the bug class and the recommended remediations.
- Microsoft policy and practice: the MSRC blog and public announcements describe the CSAF/VEX rollout that started in October 2025 and explicitly say that additional product mappings will be published as discoveries are completed. That explains the observed “Azure Linux only” language and the promise to update mappings later. ([micww.microsoft.com/en-us/msrc/blog/2025/10/toward-greater-transparency-machine-readable-vulnerability-exploitability-xchange-for-azure-linux)
Practical risk analysis for Microsoft customers
If you run Azure Linux images (VMs, AKS node pools, Marketplace images)
- Treat Azure Linux images as potentially affected and apply Microsoft’s security updates for the distribution immediately. Microsoft’s VEX/CSAF attestation is authoritative for Azure Linux; use it to automate triage and patching where you can.
If you run other Microsoft artifacts
- Do not assume they are unaffected just because they are not named in MSRC’s short advisory. The correct posture is assume uncertainty for any un‑attested artifact — unless you can confirm via SBOMs, image scans, or Microsoft’s later VEX attestations that the artifact is not a carrier.
- Candidate places to inspect urgently:
- Microsoft-published container images and base OS images (Marketplace, container registries).
- Agent or telemetry binaries (Azure agents, monitoring collectors) that may statically link Rust crates or vendor OpenSSL bindings.
- SDKs and third‑party partner images that Microsoft distributes or hosts.
- Any marketplace or custom images you inherited from a Microsoft source.
For cloud-native workloads and third‑party products
- Many vendors and cloud services use or embed Rust bindings (or package Rust binaries) as part of their toolchains. If you run third-party software on Azure VMs or AKS and that software vendors rust-openssl, treat it as part of the attack surface and verify with the vendor or by scanning SBOMs. Distribution updates alone will not fix vendor-bundled copies until those vendors rebuild and republish.
- Immediate triage (hours)
- Identify Azure Linux instances and scheduled updates; patch them using Microsoft’s guidance. Use Microsoft’s CSAF/VEX files to automate detection when available.
- Run fast artifact discovery for rust-openssl, OpenSSL, and any Rust binaries in your estate: scan container registries, VM images, and package inventories for the crate name and version.
- For any discovered artifact that includes rust-openssl ≤ 0.10.71
- Upgrade the crate to 0.10.72+ or apply the fixed package supplied by your distribution.
- Rebuild and redeploy any statically linked binaries or container images; simply updating a system package is insufficient if the vulnerable crate is vendored into a binary.
- Apply mitigations where you cannot immediately rebuild
- Limit ingestion of untrusted inputs into services that process cryptographic properties or accept constructed properties arguments.
- Add runtime isolation and sandboxing for components that perform archive or crypto operations.
- If feasible, block untrusted uploads at the web or API layer until rebuilt images are deployed.
- Secrets and validation (after patching)
- Where the vulnerable API was used for transporting secrets or configuration material, review whis warranted. The vulnerability is not a symmetric-key leak in all cases, but where confidentiality could plausibly have been compromised, rotate credentials and audit logs.
- Long-term hygiene
- Ingest SBOMs for all images and libraries. Use automated VEX/CSAF processing to suppress false positives for attested products and to flag un‑attested artifacts for manual inspection.
- Ensure CI/CD enforces pinned dependency versions and fails builds that vendor known-vulnerable code.
- Maintain a rebuild and redeploy checklist for supply‑chain vulnerabilities: update upstream dependency → rebuild → run deterministic tests → redeploy.
Why Microsoft’s CSAF/VEX rollout matters (and its current limits)
Microsoft’s decision to publish CSAF and VEX attestations (starting with Azure Linux in October 2025) is a major operational improvement: machine‑readable attestations let defenders reduce noisy triage, automate patch prioritization, anelevant alerts for products that are provably Not Affected or Fixed. That works when the vendor publishes the attestations broadly and covers each artifact you actually run.However, the current reality is a phased rollout. An attestation for Azure Linux converts one ambiguous case into a clear finding — but it does not magically attest every Microsoft image or binary. Until Microsoft publishes attestations for additional productsine MSRC VEX files with their own artifact scans and SBOM ingestion to achieve complete coverage. The safest operational stance is to treat un‑attested artifacts as unknown and verify them locally.
Critical analysis — strengths, gaps, and residual risks
Strengths
- The bug is fixed upstream and downstream packages have updated promptly; multiple distributions and vendors issued patches or rebuilds quickly. This demonstrates a functioning upstream-to-distro remediation pipeline. (sources.debian.org)
- Microsoft’s adoption of CSAF and VEX improves long-term transparency and automation for customers, reducing human triage burden when fully populated.
Gaps and risks
- Inventory uncertainty remains the largest practical risk. Public product attestations are valuable for the products they cover but do not absolve customers from performing artifact-level verification. Large vendors ship many distinct artifacts (images, SDKs, appliance bundles) that may or may not include the same upstream code. Treat the MSRC attestation as authoritative for Azure Linux only until more attestations appear.
- Vendor-bundling and static linking mean that patched system packages alone are insufficient: binaries that were compiled with vulnerable crate versions remain vulnerable until rebuilt. This increases operational work — patching often becomes a rebuild-and-redeploy task.
- Silent failures: When cryptographic helpers silently reduced properties to an empty string or otherwise changed semantics without breaking higher-level behavior (signatures, RPC success), detection is difficult. Operators should assume the worst for any sensitive secret-handling paths until verification completes.
Quick reference checklist (actionable)
- If you run Azure Linux images: apply MSRC/patch updates now.
- Hunt for rust-openssl versions ≤ 0.10.71 in:
- Container images and registries
- VM images and Marketplace images
- Quine binaries and vendor-statically-linked Rust tools
- SDKs and agent packages
- Upgrade crates to 0.10.72+ and rebuild artifacts; update distro packages where provided.
- Rotate credentials only where exposure is plausible, and collect forensic evidence where compromise is suspected.
- Ingest Microsoft’s CSAF/VEX files and integrate them into your vulnerability‑management pipeline; treat un‑attested Microsoft artifacts as “unknown” until proven otherwise.
Conclusion
Microsoft’s MSRC wording that “Azure Linux includes this open‑source library and is therefore potentially affected” is a correct, product‑scoped attestation: Azure Linux images are in‑scope and should be patched using Microsoft’s guidance. However, the statement does not prove that Azure Linux is the only Microsoft product that could include the rust‑openssl code implicated by CVE‑2025‑3416. The prudent operational posture — and the one that will close real attack windows — is twofold: (1) prioritize and patch Azure Linux images immediately, and (2) run artifact‑level discovery (SBOMs, image scans, binary analysis) across all Microsoft‑supplied images and binaries you run until Microsoft’s VEX/CSAF attestations or your own inventories demonstrate those artifacts are not carriers.The upstream fix is available and distribution vendors have issued updates; the technical remediation is straightforward. The harder work is operational: rebuilding, redeploying, verifying, and — where appropriate — rotating keys. Do that work now for Azure Linux, and do it everywhere else you run Microsoft images or tools until attestations prove otherwise.
Source: MSRC Security Update Guide - Microsoft Security Response Center