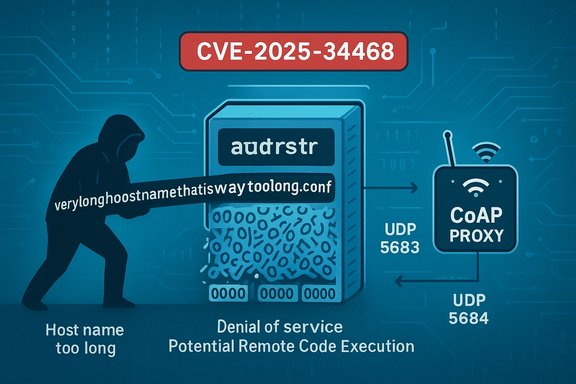
A stack-based buffer overflow affecting libcoap’s address-resolution path has been publicly disclosed as CVE-2025-34468; the defect allows attacker-controlled hostnames to overflow a fixed 256-byte stack buffer in certain code paths, producing reliable Denial‑of‑Service and an environment‑dependent possibility of Remote Code Execution (RCE).
libcoap is a compact open‑source implementation of the Constrained Application Protocol (CoAP), widely used in constrained‑IoT stacks, gateways, and embedded networking services. The newly published CVE‑2025‑34468 affects libcoap releases up to and including 4.3.5, and was fixed upstream by a defensive commit that validates hostname length before copying into a local 256‑byte buffer. The public advisories and vulnerability feeds classify the issue as a stack‑based buffer overflow in the address‑resolution code and assign a high severity score under CVSSv4 (example: CVSS 4.0 = 8.2 by some CNAs). This vulnerability is notable because it touches the part of libcoap that resolves hostnames when applications exercise proxy request handling (the proxy code path). When proxy logic is enabled in an application using libcoap, attacker‑controlled hostnames that exceed the expected length can be copied into a fixed stack buffer without bounds checking—creating an exploitable memory corruption. The upstream fix introduces an explicit length check and logs/returns on oversized hostnames.
Source: MSRC Security Update Guide - Microsoft Security Response Center
 Background / Overview
Background / Overview
libcoap is a compact open‑source implementation of the Constrained Application Protocol (CoAP), widely used in constrained‑IoT stacks, gateways, and embedded networking services. The newly published CVE‑2025‑34468 affects libcoap releases up to and including 4.3.5, and was fixed upstream by a defensive commit that validates hostname length before copying into a local 256‑byte buffer. The public advisories and vulnerability feeds classify the issue as a stack‑based buffer overflow in the address‑resolution code and assign a high severity score under CVSSv4 (example: CVSS 4.0 = 8.2 by some CNAs). This vulnerability is notable because it touches the part of libcoap that resolves hostnames when applications exercise proxy request handling (the proxy code path). When proxy logic is enabled in an application using libcoap, attacker‑controlled hostnames that exceed the expected length can be copied into a fixed stack buffer without bounds checking—creating an exploitable memory corruption. The upstream fix introduces an explicit length check and logs/returns on oversized hostnames. Technical anatomy: what the bug is and why it matters
Where the overflow happens
- The problematic path is in the address resolution routine used when parsing URIs and when proxy logic constructs or validates proxy URIs.
- The vulnerable code copied hostname bytes into a local stack array sized at 256 bytes (addrstr) without validating address->length against the buffer size first.
- An attacker supplying a hostname longer than the buffer (>= 256 bytes) could force an out‑of‑bounds write onto the stack, corrupting adjacent frames, saved registers, or the return address. The upstream commit modifies coap_resolve_address_info to check address->length and bail out with a warning if the hostname is too long.
Practical exploitation model
- Preconditions: The target application must use libcoap’s proxy logic (i.e., accept or construct Proxy‑URI values or otherwise route CoAP proxy requests through the vulnerable code path). Many typical client‑only uses of libcoap do not exercise the proxy path, so not every program that links to libcoap will be vulnerable in practice.
- Attack vector: Network. Because CoAP is a network protocol (default UDP port 5683 for CoAP, 5684 for CoAPS), an attacker that can send or influence proxy requests to a vulnerable application can deliver an oversized hostname value in a URI or proxy header and trigger the code path. Some deployments may also be vulnerable via local inputs (if an application accepts URIs via configuration or IPC).
- Immediate outcome: Denial‑of‑Service (process crash) is the most reliable and predictable effect of a stack overflow in this context.
- Potential for RCE: Stack corruptions can—under favorable memory layout, runtime options, and absent hardening—lead to control‑flow hijack and arbitrary code execution. Whether a specific build is actually exploitable for RCE depends on the binary’s compile‑time and runtime mitigations (stack canaries, PIE, ASLR, RELRO, compiler optimizations), the presence or absence of non‑executable stack, and whether the application links the vulnerable code in a context where a successful hijack would yield useful privileges and process semantics. Public trackers flag RCE as possible but environment‑dependent; there is no universally deterministic, widely shared public PoC demonstrating reliable RCE at the time of disclosure.
Upstream fix — what changed in the code
The upstream libcoap commit (SHA beginning 30db3ea) adds a simple defensive check:- It validates that address->length is strictly less than sizeof(addrstr) (256).
- If the provided hostname length is too large, the function logs a warning ("Host name too long") and returns NULL instead of copying unbounded data into the local buffer.
- The commit also tightens how URIs are parsed before using proxy logic, preventing the out‑of‑bounds memcpy into the stack buffer.
Verification & cross‑checks
To ensure the description and mitigation are accurate, the public record was cross‑checked across multiple independent sources:- The GitHub commit and pull request contain the exact source‑level changes and the author/credit details for the fix. The commit message explicitly states the bug (host names larger than 255 bytes) and the defensive check added.
- NVD and mainstream vulnerability aggregators list the same affected versions and fix‑commit mapping (libcoap <= 4.3.5; fixed by commit 30db3ea). These trackers echo the technical summary, the fixed commit reference, and the functional impact (DoS, potential RCE depending on environment).
- Several Linux distribution security pages (for example Ubuntu and Debian issue trackers) and commercial scanners have ingested the CVE record and reference the same fix. That provides independent confirmation that the CVE is anchored to the upstream commit and that maintainers will apply packaging updates.
Who is affected — real‑world scope
- Directly affected: Applications and devices that include libcoap versions up to and including 4.3.5 and that exercise the proxy or URI address‑resolution code path. Examples include CoAP gateways, IoT proxies, constrained gateway daemons, and some embedded stacks where libcoap is used for URI parsing and proxy handling.
- Indirectly affected: Any vendor or embedded device that statically links libcoap into its firmware or application binaries and distributes unpatched images. These often have long update cycles, increasing the operational exposure window.
- Not necessarily affected: Applications that use libcoap but never enable proxy handling or do not call the coap_resolve_address_info code path with untrusted hostname data may not be vulnerable in practice. Still, the safe operational assumption is to inventory and confirm. Distribution packagers and OS vendors are marking packages and evaluating backports, so operational exposure will vary by vendor.
Detection, hunting, and triage guidance
Inventory and discovery (first steps)
- Enumerate binaries and packages linking libcoap:
- Package managers: apt/yum/dnf/zypper — check libcoap, libcoap2, libcoap3 package records and versions.
- Container images and firmware bundles — scan images for libcoap library artifacts or symbols.
- Identify processes that expose CoAP network listeners (default UDP 5683/5684) or accept proxy URIs from external clients.
- For statically linked artifacts, use binary inspection tools (strings, readelf, ldd equivalents for static) to detect libcoap symbols and track versions.
Log and behavioral signals to watch
- Repeated crashes of CoAP services or gateway daemons that coincide with malformed or oversized URI or Proxy‑URI inputs.
- Unexpected termination or core dumps from processes that perform URI parsing or proxy routing using libcoap.
- Network flows where CoAP requests include unusually long hostname components in URIs or Proxy‑URI options (monitor payloads for hostname length anomalies).
Example search patterns
- Network IDS/packet capture: search for CoAP messages with URI‑path or Proxy‑URI options containing hostnames > 200 bytes.
- Host‑based: check systemd/journalctl or process crash reports for libcoap‑linked daemons failing with memory errors or SIGSEGV on URI parsing.
Forensics
- Preserve packet captures of any suspicious CoAP traffic that preceded a crash.
- Preserve core dumps and binary build artifacts for analysis — attackers may attempt to craft exploitation chains, and forensic evidence is essential for follow‑up.
Mitigation and remediation
Primary remediation — update libcoap
- Apply the upstream fix: upgrade libcoap to a release that includes commit 30db3ea or apply the commit to your tree and rebuild.
- For OS packages: install vendor/OS security updates as they become available; distribution trackers (Ubuntu, Debian) are evaluating and mapping the CVE to package releases — follow vendor advisories and update package repositories.
Interim mitigations if you cannot patch immediately
- Disable CoAP proxy features in affected applications or gateways until patched. The bug is only triggered when the proxy/address‑resolution path is exercised.
- Network segmentation/firewalling: restrict access to CoAP listeners (UDP 5683/5684) to trusted networks and management hosts only.
- Input validation and filtering: use an upstream proxy or front‑end to reject URIs with hostname components exceeding reasonable lengths (e.g., > 255 characters) before they reach the vulnerable library.
- Run vulnerable components under least privilege and containment: sandbox the process, restrict network and filesystem capabilities, enable process hardening mitigations if recompilation is possible.
Hardening and compile‑time mitigations (recommended for rebuilds)
- Recompile libcoap and your application with:
- Stack canaries enabled (-fstack-protector-strong or similar).
- PIE and ASLR enabled for the executable.
- Full RELRO and modern hardened linker flags.
- Build with hardened toolchain options where available (e.g., -fstack-clash-protection).
- Use AddressSanitizer (ASan) in test builds to validate that patches eliminate out‑of‑bounds writes during fuzzing and regression tests.
Patch deployment checklist (operational playbook)
- Identify all hosts and images that ship libcoap (static and shared).
- Determine whether each integration uses proxy logic/URI parsing code paths.
- For package‑managed systems: update OS packages to vendor‑released patched libcoap packages and reboot/restart services where required.
- For static or custom builds:
- Pull upstream changes (commit 30db3ea or later) or apply the patch from the libcoap PR.
- Rebuild the library and all dependent binaries.
- Run unit and integration tests, including fuzzed URI parser tests and ASan-enabled runs.
- Deploy to staging, then to production following change control.
- Monitor after deployment for stability regressions and anomalous CoAP traffic.
Exploitability and risk assessment — practical considerations
- The immediate and guaranteed impact is Denial‑of‑Service: an attacker can cause crashes by sending oversized hostnames to a proxied request handler. That is operationally serious for gateways, constrained devices, and monitoring/management infrastructure.
- Achieving reliable RCE from this stack overflow is non‑trivial in many modern builds because mitigations like ASLR, stack canaries, PIE, NX, and compiler hardening increase the exploitation difficulty. Nevertheless, stack overflows historically have been turned into reliable code‑execution in targeted contexts where attackers can control memory layout or bypass protections.
- Because the vulnerability involves URI parsing and proxy logic, the exposure depends heavily on how libcoap is used. Devices that serve as CoAP proxies, gateways or accept untrusted URIs from the network are highest risk.
- Public advisories responsibly mark RCE as possible rather than confirmed; operators should treat the presence of a stack overflow as high priority for patching because the progression from crash to code execution is context dependent and attackers often have time to craft exploitation chains once a primitive is known.
Communication & vendor coordination
- Device vendors and firmware maintainers should be notified if they ship products with libcoap ≤ 4.3.5 and proxy functionality enabled. Many embedded vendors include libcoap in custom stacks and may not have upstream automated updates; they must backport the fix and issue new firmware.
- Operators should expect distribution advisories and CVE mapping over the next maintenance cycles; watch vendor security trackers and published package changelogs to confirm the patched commit ID is included. Debian and Ubuntu trackers are already mapping the CVE to the upstream commit and planning package updates.
Detection signatures and IDS guidance (examples)
- Network signature: CoAP request packets (UDP 5683) containing Proxy‑URI options where the hostname component exceeds 200 bytes. Alert and capture full payload.
- Host signature: Repeated termination of CoAP gateway processes coinciding with unusual CoAP payloads; sudden segmentation faults in libraries handling coap_split_uri/coap_resolve_address_info.
- Endpoint checks: On systems with package managers, queries like:
- Debian/Ubuntu: dpkg -l | grep libcoap
- RPM: rpm -qa | grep libcoap
- Container scanning: grep for libcoap libraries or referenced package versions within images.
Final recommendations (prioritized)
- Patch immediately where practical: update libcoap to a build that includes commit 30db3ea or install vendor packages that incorporate the fix.
- If patching is delayed, disable proxy functionality or block access to CoAP ports from untrusted networks.
- Rebuild custom images and statically linked binaries with modern compile‑time hardening and test with ASan/fuzzers before redeploying.
- Inventory and track assets that incorporate libcoap (including firmware and containers). Maintain an authoritative list to accelerate future patches.
- Monitor for anomalous CoAP traffic and process crashes; collect PCAPs and core dumps for forensic review.
Conclusion
CVE‑2025‑34468 is a classic, high‑impact memory‑safety defect rooted in a missing length check when copying hostname data into a fixed stack buffer. The vulnerability is fixed upstream by a bounded check commit (30db3ea) and has been widely ingested by vulnerability databases and vendor trackers; operators should treat the issue as actionable. The most reliable remediation is to update libcoap or apply the upstream patch and to ensure that any application using libcoap’s proxy code path is rebuilt and redeployed with hardened compiler/runtime settings. While Denial‑of‑Service is the immediate and reproducible outcome, a prudent defender will assume the potential for escalation to code execution until every affected artifact is validated and patched.Source: MSRC Security Update Guide - Microsoft Security Response Center